|
NetSpectre
Spectre is one of the speculative execution CPU vulnerabilities which involve side-channel attacks. These affect modern microprocessors that perform branch prediction and other forms of speculative execution. On most processors, the speculative execution resulting from a branch misprediction may leave observable side effects that may reveal private data to attackers. For example, if the pattern of memory accesses performed by such speculative execution depends on private data, the resulting state of the data cache constitutes a side channel through which an attacker may be able to extract information about the private data using a timing attack. In addition to vulnerabilities associated with installed applications, JIT engines used for JavaScript were found to be vulnerable. A website can read data stored in the browser for another website, or the browser's memory itself. Two Common Vulnerabilities and Exposures records related to Spectre, (bounds check bypass, Spectre-V1, ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Microprocessor
A microprocessor is a computer processor (computing), processor for which the data processing logic and control is included on a single integrated circuit (IC), or a small number of ICs. The microprocessor contains the arithmetic, logic, and control circuitry required to perform the functions of a computer's central processing unit (CPU). The IC is capable of interpreting and executing program instructions and performing arithmetic operations. The microprocessor is a multipurpose, Clock signal, clock-driven, Processor register, register-based, digital integrated circuit that accepts binary code, binary data as input, processes it according to instruction (computing), instructions stored in its computer memory, memory, and provides results (also in binary form) as output. Microprocessors contain both combinational logic and sequential logic, sequential digital logic, and operate on numbers and symbols represented in the binary number system. The integration of a whole CPU on ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Intel
Intel Corporation is an American multinational corporation and technology company headquartered in Santa Clara, California, and Delaware General Corporation Law, incorporated in Delaware. Intel designs, manufactures, and sells computer components such as central processing units (CPUs) and related products for business and consumer markets. It is one of the world's List of largest semiconductor chip manufacturers, largest semiconductor chip manufacturers by revenue, and ranked in the Fortune 500, ''Fortune'' 500 list of the List of largest companies in the United States by revenue, largest United States corporations by revenue for nearly a decade, from 2007 to 2016 Fiscal year, fiscal years, until it was removed from the ranking in 2018. In 2020, it was reinstated and ranked 45th, being the List of Fortune 500 computer software and information companies, 7th-largest technology company in the ranking. It was one of the first companies listed on Nasdaq. Intel supplies List of I ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
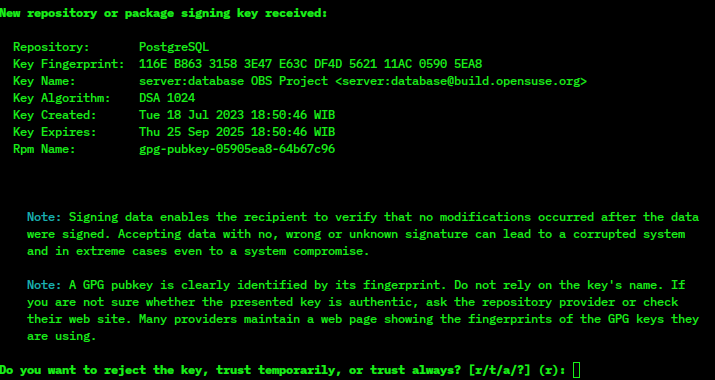
GnuPG
GNU Privacy Guard (GnuPG or GPG) is a free-software replacement for Symantec's cryptographic software suite PGP. The software is compliant with the now obsoleted , the IETF standards-track specification of OpenPGP. Modern versions of PGP are interoperable with GnuPG and other OpenPGP v4-compliant systems. November 2023 saw two drafts aiming to update the 2007 OpenPGP v4 specification (RFC4880), ultimately resulting in thRFC 9580standard in July 2024. The proposal from the GnuPG developers, which is called LibrePGP, was not taken up by the OpenPGP Working Group and future versions of GnuPG will not support the current version of OpenPGP. GnuPG is part of the GNU Project and received major funding from the German government in 1999. Overview GnuPG is a hybrid-encryption software program because it uses a combination of conventional symmetric-key cryptography for speed, and public-key cryptography for ease of secure key exchange, typically by using the recipient's publi ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
University Of Adelaide
The University of Adelaide is a public university, public research university based in Adelaide, South Australia. Established in 1874, it is the third-oldest university in Australia. Its main campus in the Adelaide city centre includes many Sandstone universities, sandstone buildings of historical and architectural significance, such as Bonython Hall. Its royal charter awarded by Queen Victoria in 1881 allowed it to become the University of London, second university in the English-speaking world to confer degrees to women. It Adelaide University, plans to merge with the neighbouring University of South Australia, is adjacent to the Australian Space Agency headquarters on Lot Fourteen and is part of the Adelaide BioMed City research precinct. The university was founded at the former South Australian Society of Arts, Royal South Australian Society of Arts by the Union College and studies were initially conducted at its State Library of South Australia, Institute Building. The soc ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
RSA (cryptosystem)
The RSA (Rivest–Shamir–Adleman) cryptosystem is a public-key cryptosystem, one of the oldest widely used for secure data transmission. The initialism "RSA" comes from the surnames of Ron Rivest, Adi Shamir and Leonard Adleman, who publicly described the algorithm in 1977. An equivalent system was developed secretly in 1973 at Government Communications Headquarters (GCHQ), the British signals intelligence agency, by the English mathematician Clifford Cocks. That system was declassified in 1997. In a public-key cryptosystem, the encryption key is public and distinct from the decryption key, which is kept secret (private). An RSA user creates and publishes a public key based on two large prime numbers, along with an auxiliary value. The prime numbers are kept secret. Messages can be encrypted by anyone via the public key, but can only be decrypted by someone who knows the private key. The security of RSA relies on the practical difficulty of factoring the product o ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Colin Percival
Colin A. Percival (born 1980) is a Canadian computer scientist and computer security researcher. He completed his undergraduate education at Simon Fraser University and a doctorate at the University of Oxford. While at university he joined the FreeBSD project, and achieved some notoriety for discovering a security weakness in Intel's hyper-threading technology. Besides his work in delta compression and the introduction of memory-hard functions, he is also known for developing the Tarsnap online backup service, which became his full-time job. Education Percival began taking mathematics courses at Simon Fraser University (SFU) at age 13, as a student at Burnaby Central Secondary School. He graduated from Burnaby Central and officially enrolled at SFU in 1998. At SFU he studied number theory under Peter Borwein, and competed in the William Lowell Putnam Mathematical Competition, placing in the top 15 in 1998 and as a Putnam Fellow (in the top six) in 1999. From 1998 to 2000 he ran t ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Advanced Encryption Standard
The Advanced Encryption Standard (AES), also known by its original name Rijndael (), is a specification for the encryption of electronic data established by the U.S. National Institute of Standards and Technology (NIST) in 2001. AES is a variant of the Rijndael block cipher developed by two Belgium, Belgian cryptographers, Joan Daemen and Vincent Rijmen, who submitted a proposal to NIST during the Advanced Encryption Standard process, AES selection process. Rijndael is a family of ciphers with different key size, key and Block size (cryptography), block sizes. For AES, NIST selected three members of the Rijndael family, each with a block size of 128 bits, but three different key lengths: 128, 192 and 256 bits. AES has been adopted by the Federal government of the United States, U.S. government. It supersedes the Data Encryption Standard (DES), which was published in 1977. The algorithm described by AES is a symmetric-key algorithm, meaning the same key is used for both encrypting ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |