Graph-based Access Control on:
[Wikipedia]
[Google]
[Amazon]
Graph-based access control (GBAC) is a declarative way to define access rights, task assignments, recipients and content in
iisys
, the approach was extended by features like separation of duty, access control in virtual organizations and subject-oriented access control.
 GBAC was first implemented in the CoCoS Environment within the organizational server CoCoSOrg.
In the C-Org-Project it was extended with more sophisticated features like separation of duty or access control in distributed environments.
There is also a cloud-based implementation on IBM's Bluemix
GBAC was first implemented in the CoCoS Environment within the organizational server CoCoSOrg.
In the C-Org-Project it was extended with more sophisticated features like separation of duty or access control in distributed environments.
There is also a cloud-based implementation on IBM's BluemixBluemix
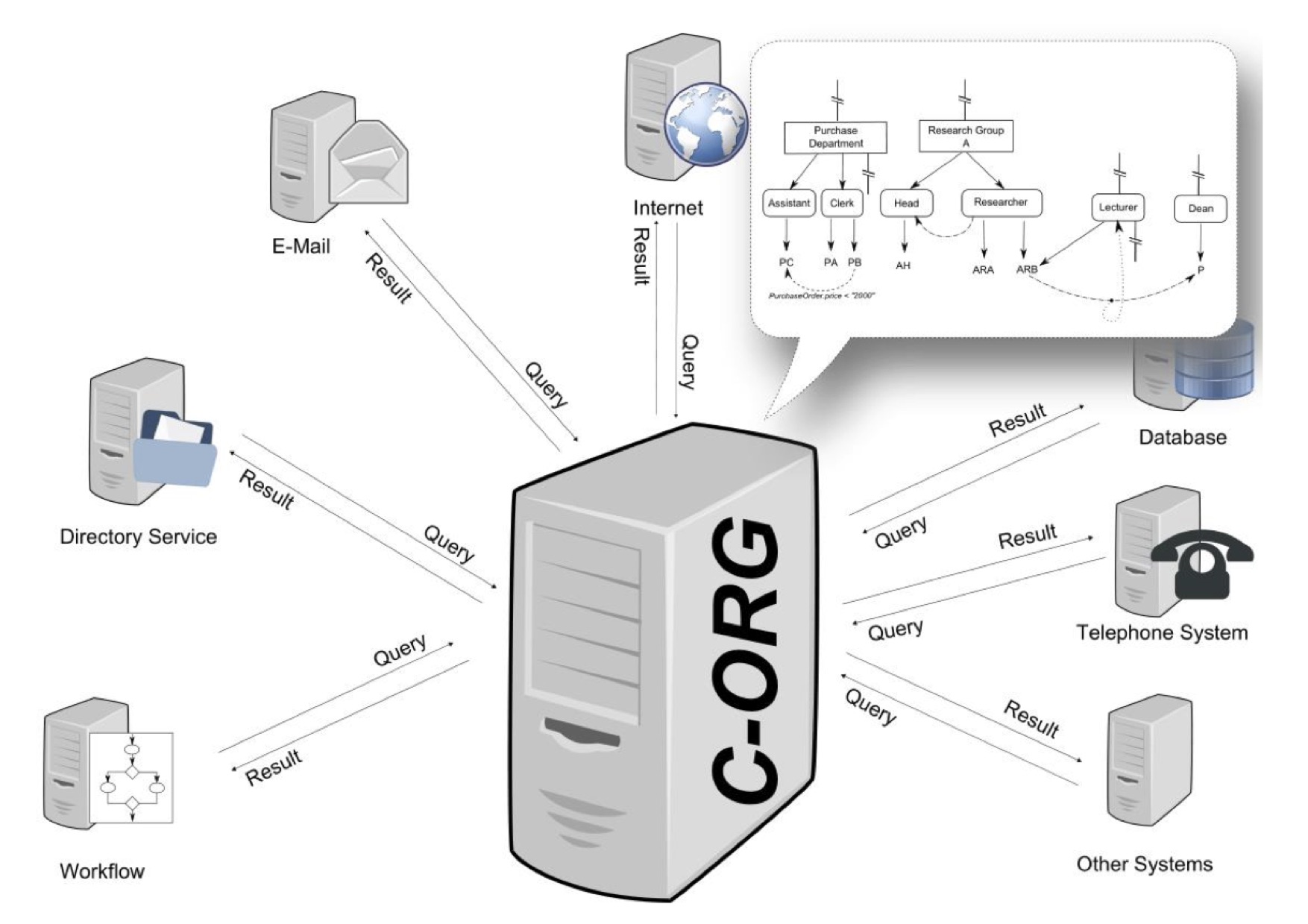
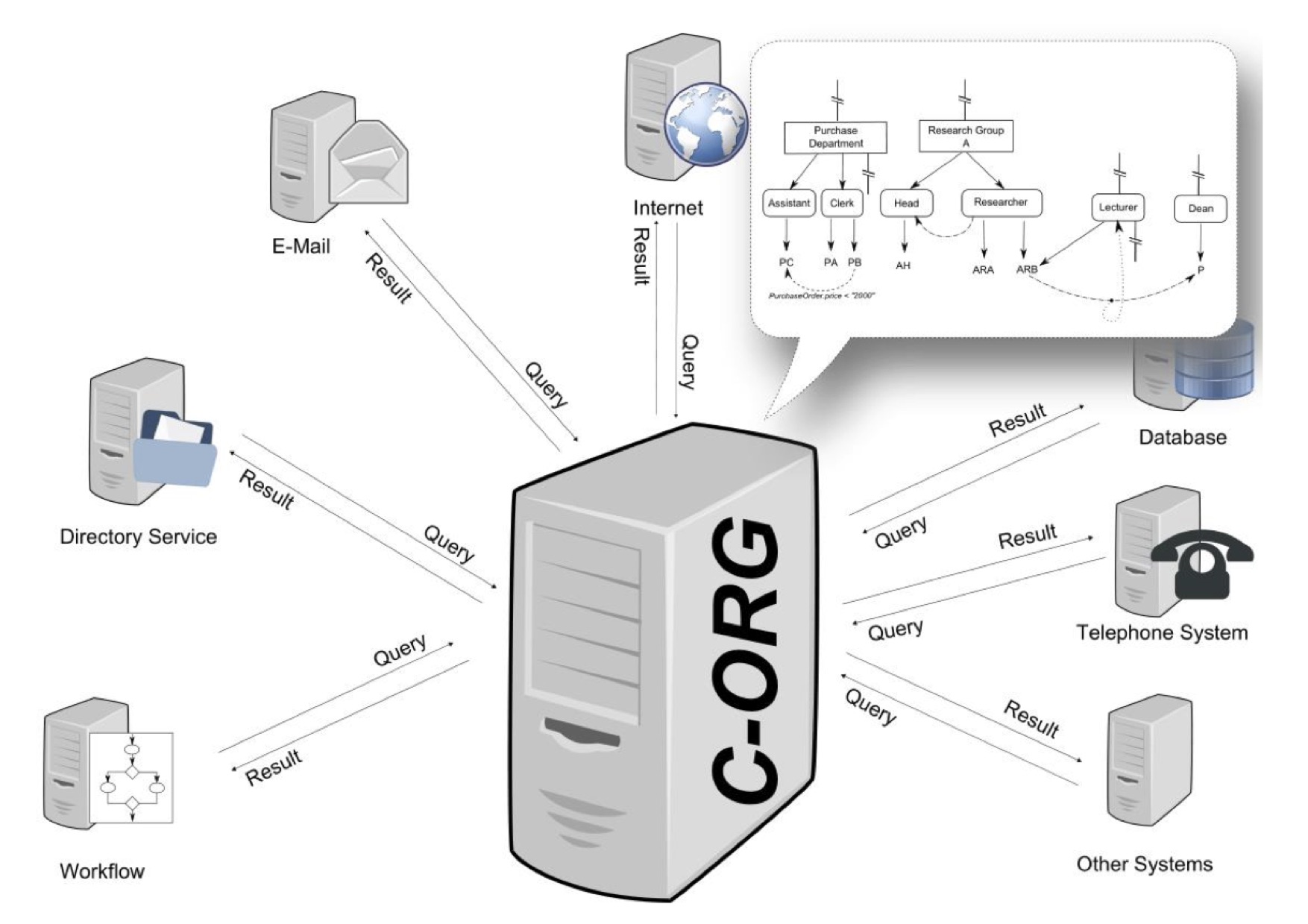
/ref> platform. In all implementations the server takes a query from a client system and resolves it to a set of agents. This set is sent back to the calling client as response. Clients can be file systems, database management systems, workflow management systems, physical security systems or even telephone servers.
information system
An information system (IS) is a formal, sociotechnical, organizational system designed to collect, process, Information Processing and Management, store, and information distribution, distribute information. From a sociotechnical perspective, info ...
s. Access rights are granted to objects like files or documents, but also business objects such as an account. GBAC can also be used for the assignment of agents to tasks in workflow environments. Organizations are modeled as a specific kind of semantic graph comprising the organizational units, the roles and functions as well as the human and automatic agents (i.a. persons, machines). The main difference with other approaches such as role-based access control or attribute-based access control is that in GBAC access rights are defined using an organizational query language instead of total enumeration.
History
The foundations of GBAC go back to a research project named CoCoSOrg (Configurable Cooperation System) ">ref name="DISS">(in English language please see) at Bamberg University. In CoCoSOrg an organization is represented as a semantic graph and a formal language is used to specify agents and their access rights in a workflow environment. Within the C-Org-Project at Hof University's Institute for Information Systemsiisys
, the approach was extended by features like separation of duty, access control in virtual organizations and subject-oriented access control.
Definition
Graph-based access control consists of two building blocks: * A semantic graph modeling an organization * A query language.Organizational graph
The organizational graph is divided into a type and an instance level. On the instance level there are node types for organizational units, functional units and agents. The basic structure of an organization is defined using so called "structural relations". They define the "is part of"- relations between functional units and organizational units as well as the mapping of agents to functional units. Additionally there are specific relationship types like "deputyship" or "informed_by". These types can be extended by the modeler. All relationships can be context sensitive through the usage of predicates. On the type level organizational structures are described in a more general manner. It consists of organizational unit types, functional unit types and the same relationship types as on the instance level. Type definitions can be used to create new instances or reuse organizational knowledge in case of exceptions (for further reading see).Query language
In GBAC a query language is used to define agents having certain characteristics or abilities. The following table shows the usage of the query language in the context of an access control matrix. The first query means that all managers working for the company for more than six months can read the financial report, as well as the managers who are classified by the flag "ReadFinancialReport". The daily financial report can only be written by the manager of the controlling department or clerks of the department that are enabled to do that (WriteFinancialReportTRUE).Implementation
 GBAC was first implemented in the CoCoS Environment within the organizational server CoCoSOrg.
In the C-Org-Project it was extended with more sophisticated features like separation of duty or access control in distributed environments.
There is also a cloud-based implementation on IBM's Bluemix
GBAC was first implemented in the CoCoS Environment within the organizational server CoCoSOrg.
In the C-Org-Project it was extended with more sophisticated features like separation of duty or access control in distributed environments.
There is also a cloud-based implementation on IBM's Bluemix/ref> platform. In all implementations the server takes a query from a client system and resolves it to a set of agents. This set is sent back to the calling client as response. Clients can be file systems, database management systems, workflow management systems, physical security systems or even telephone servers.
See also
{{columns-list, colwidth=30em, *Access control list
In computer security, an access-control list (ACL) is a list of permissions associated with a system resource (object or facility). An ACL specifies which users or system processes are granted access to resources, as well as what operations are ...
* Attribute-based access control (ABAC)
* Capability-based security
* Context-based access control (CBAC)
* Discretionary access control
In computer security, discretionary access control (DAC) is a type of access control defined by the Trusted Computer System Evaluation Criteria (TCSEC) as a means of restricting access to objects based on the identity of subjects and/or groups to ...
(DAC)
* Lattice-based access control
In computer security, lattice-based access control (LBAC) is a complex access control model based on the interaction between any combination of objects (such as resources, computers, and applications) and subjects (such as individuals, groups or o ...
(LBAC)
* Mandatory access control (MAC)
* Organisation-based access control (OrBAC)
* Risk-based authentication
* Role-based access control (RBAC)
* Rule-set-based access control (RSBAC)
References