|
Risk-based Authentication
In authentication Authentication (from ''authentikos'', "real, genuine", from αὐθέντης ''authentes'', "author") is the act of proving an Logical assertion, assertion, such as the Digital identity, identity of a computer system user. In contrast with iden ..., risk-based authentication is a non-static authentication system which takes into account the profile (IP address, User-Agent HTTP header, time of access, and so on) of the agent requesting access to the system to determine the risk profile associated with that transaction. The risk profile is then used to determine the complexity of the challenge. Higher risk profiles leads to stronger challenges, whereas a static username/password may suffice for lower-risk profiles. Risk-based implementation allows the application to challenge the user for additional credentials only when the risk level is appropriate. The point is that user validation accuracy is improved without inconveniencing a user, and risk-based authenticat ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
|
 |
Authentication
Authentication (from ''authentikos'', "real, genuine", from αὐθέντης ''authentes'', "author") is the act of proving an Logical assertion, assertion, such as the Digital identity, identity of a computer system user. In contrast with identification, the act of indicating a person or thing's identity, authentication is the process of verifying that identity. Authentication is relevant to multiple fields. In art, antiques, and anthropology, a common problem is verifying that a given artifact was produced by a certain person, or in a certain place (i.e. to assert that it is not counterfeit), or in a given period of history (e.g. by determining the age via carbon dating). In computer science, verifying a user's identity is often required to allow access to confidential data or systems. It might involve validating personal identity documents. In art, antiques and anthropology Authentication can be considered to be of three types: The ''first'' type of authentication is accep ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
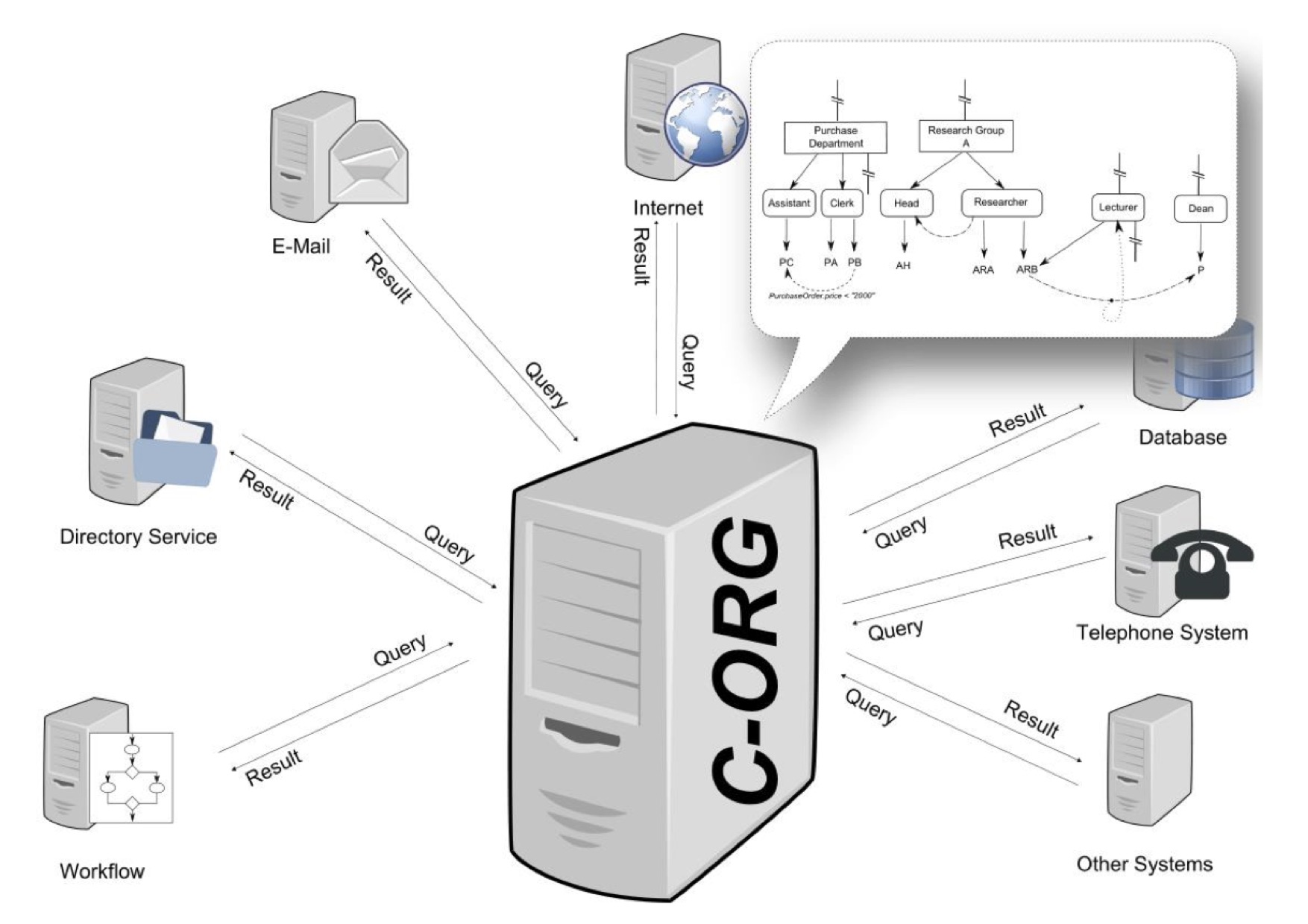 |
Graph-based Access Control
Graph-based access control (GBAC) is a declarative way to define access rights, task assignments, recipients and content in information systems. Access rights are granted to objects like files or documents, but also business objects such as an account. GBAC can also be used for the assignment of agents to tasks in workflow environments. Organizations are modeled as a specific kind of semantic graph comprising the organizational units, the roles and functions as well as the human and automatic agents (i.a. persons, machines). The main difference with other approaches such as role-based access control or attribute-based access control is that in GBAC access rights are defined using an organizational query language instead of total enumeration. History The foundations of GBAC go back to a research project named CoCoSOrg (Configurable Cooperation System) ">ref name="DISS">(in English language please see) at Bamberg University. In CoCoSOrg an organization is represented as a semant ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
|
Applications Of Cryptography
Application may refer to: Mathematics and computing * Application software, computer software designed to help the user to perform specific tasks ** Application layer, an abstraction layer that specifies protocols and interface methods used in a communications network * Function application, in mathematics and computer science Processes and documents * Application for employment, a form or forms that an individual seeking employment must fill out * College application, the process by which prospective students apply for entry into a college or university * Patent application A patent application is a request pending at a patent office for the grant of a patent for an invention described in the patent specification and a set of one or more claim (patent), claims stated in a formal document, including necessary officia ..., a document filed at a patent office to support the grant of a patent Other uses * Application (virtue), a characteristic encapsulated in diligence * Topica ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
|
|
RSBAC
Rule-set-based access control (RSBAC) is an open source access control framework for current Linux kernels, which has been in stable production use since January 2000 (version 1.0.9a). Features * Free open source GNU General Public License ( GPL) Linux kernel security extension * Independent of governments and big companies * Several well-known and new security models, e.g. mandatory access control ( MAC), access control list ( ACL), and role compatibility (RC) * On-access virus scanning with Dazuko interface * Detailed control over individual user and program network accesses * Fully access controlled kernel level user management * Any combination of security models possible * Easily extensible: write your own model for runtime registration * Support for latest kernels * Stable for production use * Easily portable to other operating systems The RSBAC system architecture has been derived and extended from the Generalized Framework for Access Control ( GFAC) by Marshall Abrams and ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
|
|
Role-based Access Control
In computer systems security, role-based access control (RBAC) or role-based security is an approach to restricting system access to authorized users, and to implementing mandatory access control (MAC) or discretionary access control, discretionary access control (DAC). Role-based access control is a policy-neutral access control mechanism defined around roles and privileges. The components of RBAC such as role-permissions, user-role and role-role relationships make it simple to perform user assignments. A study by NIST has demonstrated that RBAC addresses many needs of commercial and government organizations. RBAC can be used to facilitate administration of security in large organizations with hundreds of users and thousands of permissions. Although RBAC is different from MAC and DAC access control frameworks, it can enforce these policies without any complication. Design Within an organization, role (computer science), roles are created for various job functions. The permiss ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
|
|
Organisation-based Access Control
In computer security, organization-based access control (OrBAC) is an access control model first presented in 2003. The current approaches of the access control In physical security and information security, access control (AC) is the action of deciding whether a subject should be granted or denied access to an object (for example, a place or a resource). The act of ''accessing'' may mean consuming ... rest on the three entities (''subject'', ''action'', ''object'') to control the access the policy specifies that some subject has the permission to realize some action on some object. OrBAC allows the policy designer to define a security policy independently of the implementation. The chosen method to fulfill this goal is the introduction of an abstract level. * Subjects are abstracted into roles. A role is a set of subjects to which the same security rule apply. * Similarly, an activity is a set of actions to which the same security rule apply. * And, a view is a set of ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
|
|
Mandatory Access Control
In computer security, mandatory access control (MAC) refers to a type of access control by which a secured environment (e.g., an operating system or a database) constrains the ability of a ''subject'' or ''initiator'' to access or modify on an ''object'' or ''target''. In the case of operating systems, the subject is a process or thread, while objects are files, directories, TCP/ UDP ports, shared memory segments, or IO devices. Subjects and objects each have a set of security attributes. Whenever a subject attempts to access an object, the operating system kernel examines these security attributes, examines the authorization rules (aka ''policy'') in place, and decides whether to grant access. A database management system, in its access control mechanism, can also apply mandatory access control; in this case, the objects are tables, views, procedures, etc. In mandatory access control, the security policy is centrally controlled by a policy administrator and is guaranteed (in p ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
|
|
Lattice-based Access Control
In computer security, lattice-based access control (LBAC) is a complex access control model based on the interaction between any combination of objects (such as resources, computers, and applications) and subjects (such as individuals, groups or organizations). In this type of label-based mandatory access control model, a lattice (order), lattice is used to define the levels of security that an object may have and that a subject may have access to. The subject is only allowed to access an object if the security level of the subject is greater than or equal to that of the object. Mathematically, the security level access may also be expressed in terms of the lattice (a partial order set) where each object and subject have a greatest lower bound (meet) and least upper bound (join) of access rights. For example, if two subjects ''A'' and ''B'' need access to an object, the security level is defined as the meet of the levels of ''A'' and ''B''. In another example, if two object ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
|
|
Discretionary Access Control
In computer security, discretionary access control (DAC) is a type of access control defined by the Trusted Computer System Evaluation Criteria (TCSEC) as a means of restricting access to objects based on the identity of subjects and/or groups to which they belong. The controls are discretionary in the sense that a subject with a certain access permission is capable of passing that permission (perhaps indirectly) on to any other subject (unless restrained by mandatory access control). Discretionary access control is commonly discussed in contrast to mandatory access control (MAC). Occasionally, a system as a whole is said to have "discretionary" or "purely discretionary" access control when that system lacks mandatory access control. On the other hand, systems can implement both MAC and DAC simultaneously, where DAC refers to one category of access controls that subjects can transfer among each other, and MAC refers to a second category of access controls that imposes constr ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
|
|
Computer Configuration
In communications or computer systems, a configuration of a system refers to the arrangement of each of its functional units, according to their nature, number and chief characteristics. Often, configuration pertains to the choice of hardware, software, firmware, and documentation. Along with its architecture, the configuration of a computer system affects both its function and performance. The configuration of a computer is typically recorded in a configuration file. In modern computer systems, this is created and updated automatically as physical components are added or removed. Applications may assume that the configuration file is an accurate representation of the physical configuration and act accordingly. Most modern computer systems provide a mechanism called the system settings (or "control panel") that permits users to set their preferences. These include system accessibility options (such as the default size of the system font), brightness and contrast; security ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
|
|
Context-based Access Control
Context-based access control (CBAC) is a feature of firewall software, which intelligently filters TCP and UDP packets based on application layer protocol session information. It can be used for intranets, extranets and internets. CBAC can be configured to permit specified TCP and UDP traffic through a firewall only when the connection is initiated from within the network needing protection. (In other words, CBAC can inspect traffic for sessions that originate from the external network.) However, while this example discusses inspecting traffic for sessions that originate from the external network, CBAC can inspect traffic for sessions that originate from either side of the firewall. This is the basic function of a stateful inspection firewall. Without CBAC, traffic filtering is limited to access list implementations that examine packets at the network layer, or at most, the transport layer. However, CBAC examines not only network layer and transport layer information but ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
|
|
Capability-based Security
Capability-based security is a concept in the design of secure computing systems, one of the existing security models. A capability (known in some systems as a key) is a communicable, unforgeable token of authority. It refers to a value that references an object along with an associated set of access rights. A user program on a capability-based operating system must use a capability to access an object. Capability-based security refers to the principle of designing user programs such that they directly share capabilities with each other according to the principle of least privilege, and to the operating system infrastructure necessary to make such transactions efficient and secure. Capability-based security is to be contrasted with an approach that uses traditional UNIX permissions and access control lists. Although most operating systems implement a facility which resembles capabilities, they typically do not provide enough support to allow for the exchange of capabilitie ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |