|
Time-of-check-to-time-of-use
In software development, time-of-check to time-of-use (TOCTOU, TOCTTOU or TOC/TOU) is a class of software bugs caused by a race condition involving the ''checking'' of the state of a part of a system (such as a security credential) and the ''use'' of the results of that check. TOCTOU race conditions are common in Unix between operations on the file system, but can occur in other contexts, including local sockets and improper use of database transactions. In the early 1990s, the mail utility of BSD 4.3 UNIX had an exploitable race condition for temporary files because it used the mktemp() function. Early versions of OpenSSH had an exploitable race condition for Unix domain sockets. They remain a problem in modern systems; as of 2019, a TOCTOU race condition in Docker allows root access to the filesystem of the host platform. In the 2023 Pwn2Own competition in Vancouver, a team of hackers were able to compromise the gateway in an updated Tesla Model 3 using this bug. E ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |
File Descriptor
In Unix and Unix-like computer operating systems, a file descriptor (FD, less frequently fildes) is a process-unique identifier (handle) for a file or other input/output resource, such as a pipe or network socket. File descriptors typically have non-negative integer values, with negative values being reserved to indicate "no value" or error conditions. File descriptors are a part of the POSIX API. Each Unix process (except perhaps daemons) should have three standard POSIX file descriptors, corresponding to the three standard streams: Overview In the traditional implementation of Unix, file descriptors index into a per-process maintained by the kernel, that in turn indexes into a system-wide table of files opened by all processes, called the . This table records the ''mode'' with which the file (or other resource) has been opened: for reading, writing, appending, and possibly other modes. It also indexes into a third table called the inode table that describes the ac ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |
Software Bug
A software bug is a design defect ( bug) in computer software. A computer program with many or serious bugs may be described as ''buggy''. The effects of a software bug range from minor (such as a misspelled word in the user interface) to severe (such as frequent crashing). In 2002, a study commissioned by the US Department of Commerce's National Institute of Standards and Technology concluded that "software bugs, or errors, are so prevalent and so detrimental that they cost the US economy an estimated $59 billion annually, or about 0.6 percent of the gross domestic product". Since the 1950s, some computer systems have been designed to detect or auto-correct various software errors during operations. History Terminology ''Mistake metamorphism'' (from Greek ''meta'' = "change", ''morph'' = "form") refers to the evolution of a defect in the final stage of software deployment. Transformation of a ''mistake'' committed by an analyst in the early stages of the softw ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |
Software Development
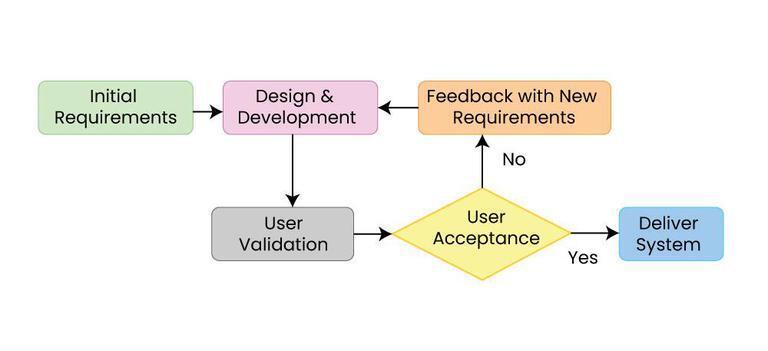
Software development is the process of designing and Implementation, implementing a software solution to Computer user satisfaction, satisfy a User (computing), user. The process is more encompassing than Computer programming, programming, writing source code, code, in that it includes conceiving the goal, evaluating feasibility, analyzing software requirements, requirements, software design, design, software testing, testing and software release life cycle, release. The process is part of software engineering which also includes management, organizational management, Software project management, project management, configuration management and other aspects. Software development involves many skills and job specializations including software programmer, programming, software test, testing, Technical writing, documentation, graphic design, user support, marketing, and fundraising. Software development involves many software tools, tools including: compiler, integrated develo ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |
Microsoft Developer Network
Microsoft Developer Network (MSDN) was the division of Microsoft responsible for managing the firm's relationship with developers and testers, such as hardware developers interested in the operating system (OS), and software developers developing on the various OS platforms or using the API or scripting languages of Microsoft's applications. The relationship management was situated in assorted media: web sites, newsletters, developer conferences, trade media, blogs and DVD distribution. Starting in January 2020, the website was fully integrated with Microsoft Docs (itself integrated into Microsoft Learn in 2022). Websites MSDN's primary web presence at ''msdn.microsoft.com'' was a collection of sites for the developer community that provided information, documentation, and discussion that was authored both by Microsoft and by the community at large. Microsoft later began placing emphasis on incorporation of forums, blogs, library annotations and social bookmarking to make MSD ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |
Microsoft Press
Microsoft Press is the publishing arm of Microsoft, usually releasing books dealing with various current Microsoft technologies. Microsoft Press' introduced books were ''The Apple Macintosh Book'' by Cary Lu and ''Exploring the IBM PCjr Home Computer'' by Peter Norton in 1984 at the West Coast Computer Faire. The publisher has gone on to release books by other recognizable authors such as Charles Petzold, Steve McConnell, Mark Russinovich and Jeffrey Richter. Following a deal signed in 2009, O'Reilly Media became the official distributor of Microsoft Press books. In 2014, the distributor was changed to Pearson PLC, Pearson. In July 2016, Microsoft Press editorial staff was laid off. References External links * Microsoft divisions Computer book publishing companies Publishing companies established in 1984 {{microsoft-stub ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |
NTFS
NT File System (NTFS) (commonly called ''New Technology File System'') is a proprietary journaling file system developed by Microsoft in the 1990s. It was developed to overcome scalability, security and other limitations with File Allocation Table, FAT. NTFS adds several features that File Allocation Table, FAT and HPFS (file system), HPFS lack, including: access control lists (ACLs); filesystem encryption; transparent compression; sparse files; Journaling file system, file system journaling and shadow copy, volume shadow copy, a feature that allows backups of a system while in use. Starting with Windows NT 3.1, it is the default file system of the Windows NT family superseding the File Allocation Table (FAT) file system. NTFS read/write support is available on Linux and Berkeley Software Distribution, BSD using NTFS3 in Linux kernel, Linux and NTFS-3G in BSD. NTFS uses several files hidden from the user to store metadata about other files stored on the drive which can help impr ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |
Microsoft Windows
Windows is a Product lining, product line of Proprietary software, proprietary graphical user interface, graphical operating systems developed and marketed by Microsoft. It is grouped into families and subfamilies that cater to particular sectors of the computing industry – Windows (unqualified) for a consumer or corporate workstation, Windows Server for a Server (computing), server and Windows IoT for an embedded system. Windows is sold as either a consumer retail product or licensed to Original equipment manufacturer, third-party hardware manufacturers who sell products Software bundles, bundled with Windows. The first version of Windows, Windows 1.0, was released on November 20, 1985, as a graphical operating system shell for MS-DOS in response to the growing interest in graphical user interfaces (GUIs). The name "Windows" is a reference to the windowing system in GUIs. The 1990 release of Windows 3.0 catapulted its market success and led to various other product families ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |
Association For Computing Machinery
The Association for Computing Machinery (ACM) is a US-based international learned society for computing. It was founded in 1947 and is the world's largest scientific and educational computing society. The ACM is a non-profit professional membership group, reporting nearly 110,000 student and professional members . Its headquarters are in New York City. The ACM is an umbrella organization for academic and scholarly interests in computer science (informatics). Its motto is "Advancing Computing as a Science & Profession". History In 1947, a notice was sent to various people: On January 10, 1947, at the Symposium on Large-Scale Digital Calculating Machinery at the Harvard computation Laboratory, Professor Samuel H. Caldwell of Massachusetts Institute of Technology spoke of the need for an association of those interested in computing machinery, and of the need for communication between them. ..After making some inquiries during May and June, we believe there is ample interest to ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |
Concurrency Control
In information technology and computer science, especially in the fields of computer programming, operating systems, multiprocessors, and databases, concurrency control ensures that correct results for concurrent operations are generated, while getting those results as quickly as possible. Computer systems, both software and hardware, consist of modules, or components. Each component is designed to operate correctly, i.e., to obey or to meet certain consistency rules. When components that operate concurrently interact by messaging or by sharing accessed data (in memory or storage), a certain component's consistency may be violated by another component. The general area of concurrency control provides rules, methods, design methodologies, and theories to maintain the consistency of components operating concurrently while interacting, and thus the consistency and correctness of the whole system. Introducing concurrency control into a system means applying operation constraints ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |
Transaction Processing
In computer science, transaction processing is information processing that is divided into individual, indivisible operations called ''transactions''. Each transaction must succeed or fail as a complete unit; it can never be only partially complete. For example, when you purchase a book from an online bookstore, you exchange money (in the form of credit) for a book. If your credit is good, a series of related operations ensures that you get the book and the bookstore gets your money. However, if a single operation in the series fails during the exchange, the entire exchange fails. You do not get the book and the bookstore does not get your money. The technology responsible for making the exchange balanced and predictable is called ''transaction processing''. Transactions ensure that data-oriented resources are not permanently updated unless all operations within the transactional unit complete successfully. By combining a set of related operations into a unit that either com ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |
Thomas J
Clarence Thomas (born June 23, 1948) is an American lawyer and jurist who has served since 1991 as an associate justice of the Supreme Court of the United States. President George H. W. Bush Clarence Thomas Supreme Court nomination, nominated him to succeed Thurgood Marshall. After Marshall, Thomas is the second African Americans, African American to serve on the U.S. Supreme Court and has been its List of United States Supreme Court justices by time in office, longest-serving member since Anthony Kennedy's retirement in 2018. He has also been the Court's oldest member since Stephen Breyer retired in 2022. Thomas was born in Pin Point, Georgia. After his father abandoned the family, he was raised by his grandfather in a poor Gullah community near Savannah, Georgia. Growing up as a devout Catholic, Thomas originally intended to be a priest in the Catholic Church but became dissatisfied with its efforts to combat racism and abandoned his aspiration to join the clergy. He gradua ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |
O'Reilly Media
O'Reilly Media, Inc. (formerly O'Reilly & Associates) is an American learning company established by Tim O'Reilly that provides technical and professional skills development courses via an online learning platform. O'Reilly also publishes books about programming and other technical content. Its distinctive brand features a woodcut of an animal on many of its book covers. The company was known as a popular tech conference organizer for more than 20 years before closing the live conferences arm of its business. Company Early days The company began in 1978 as a private consulting firm doing technical writing, based in the Cambridge, Massachusetts area. In 1984, it began to retain publishing rights on manuals created for Unix vendors. A few 70-page "Nutshell Handbooks" were well-received, but the focus remained on the consulting business until 1988. After a conference displaying O'Reilly's preliminary Xlib manuals attracted significant attention, the company began increas ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |