|
Short Authentication String
ZRTP (composed of Z and Real-time Transport Protocol) is a cryptographic key-agreement protocol to negotiate the keys for encryption between two end points in a Voice over IP (VoIP) phone telephony call based on the Real-time Transport Protocol. It uses Diffie–Hellman key exchange and the Secure Real-time Transport Protocol (SRTP) for encryption. ZRTP was developed by Phil Zimmermann, with help from Bryce Wilcox-O'Hearn, Colin Plumb, Jon Callas and Alan Johnston and was submitted to the Internet Engineering Task Force (IETF) by Zimmermann, Callas and Johnston on March 5, 2006 and published on April 11, 2011 as . Overview ZRTP ("Z" is a reference to its inventor, Zimmermann; "RTP" stands for Real-time Transport Protocol) is described in the Internet Draft as a ''"key agreement protocol which performs Diffie–Hellman key exchange during call setup in-band in the Real-time Transport Protocol (RTP) media stream which has been established using some other signaling protocol such as S ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Real-time Transport Protocol
The Real-time Transport Protocol (RTP) is a network protocol for delivering audio and video over IP networks. RTP is used in communication and entertainment systems that involve streaming media, such as telephony, video teleconference applications including WebRTC, television services and web-based push-to-talk features. RTP typically runs over User Datagram Protocol (UDP). RTP is used in conjunction with the RTP Control Protocol (RTCP). While RTP carries the media streams (e.g., audio and video), RTCP is used to monitor transmission statistics and quality of service (QoS) and aids synchronization of multiple streams. RTP is one of the technical foundations of voice over IP and in this context is often used in conjunction with a signaling protocol such as the Session Initiation Protocol (SIP) which establishes connections across the network. RTP was developed by the Audio-Video Transport Working Group of the Internet Engineering Task Force (IETF) and first published i ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Distributed Hash Table
A distributed hash table (DHT) is a Distributed computing, distributed system that provides a lookup service similar to a hash table. Key–value pairs are stored in a DHT, and any participating node (networking), node can efficiently retrieve the value associated with a given key. The main advantage of a DHT is that nodes can be added or removed with minimum work around re-distributing keys. ''Keys'' are unique identifiers which map to particular ''values'', which in turn can be anything from addresses, to Electronic document, documents, to arbitrary Data (computing), data. Responsibility for maintaining the mapping from keys to values is distributed among the nodes, in such a way that a change in the set of participants causes a minimal amount of disruption. This allows a DHT to scale (computing), scale to extremely large numbers of nodes and to handle continual node arrivals, departures, and failures. DHTs form an infrastructure that can be used to build more complex services, su ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
EDGE (telecommunication)
Enhanced Data rates for GSM Evolution (EDGE), also known as 2.75G and under various other names, is a 2G digital mobile phone technology for packet switching, packet switched data transmission. It is a subset of General Packet Radio Service (GPRS) on the GSM network and improves upon it offering speeds close to 3G technology, hence the name 2.75G. EDGE is standardized by the 3GPP as part of the GSM family and as an upgrade to GPRS. EDGE was deployed on GSM networks beginning in 2003 – initially by Cingular (now AT&T) in the United States. It could be readily deployed on existing GSM and GPRS cellular equipment, making it an easier upgrade for Mobile network operator, cellular companies compared to the UMTS 3G technology that required significant changes. Through the introduction of sophisticated methods of coding and transmitting data, EDGE delivers higher bit-rates per radio channel, resulting in a threefold increase in capacity and performance compared with an ordinary G ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
UMTS
The Universal Mobile Telecommunications System (UMTS) is a 3G mobile cellular system for networks based on the GSM standard. UMTS uses Wideband Code Division Multiple Access, wideband code-division multiple access (W-CDMA) radio access technology to offer greater spectral efficiency and bandwidth to mobile network operators compared to previous 2G systems like GPRS and Circuit Switched Data, CSD. UMTS on its provides a peak theoretical data rate of 2 Data-rate units, Mbit/s. Developed and maintained by the 3GPP (3rd Generation Partnership Project), UMTS is a component of the International Telecommunication Union IMT-2000 standard set and compares with the CDMA2000 standard set for networks based on the competing IS-95, cdmaOne technology. The technology described in UMTS is sometimes also referred to as Freedom of Mobile Multimedia Access (FOMA) or 3GSM. UMTS specifies a complete network system, which includes the radio access network (UMTS Terrestrial Radio Access Network, or U ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
WiFi
Wi-Fi () is a family of wireless network protocols based on the IEEE 802.11 family of standards, which are commonly used for Wireless LAN, local area networking of devices and Internet access, allowing nearby digital devices to exchange data by radio waves. These are the most widely used computer networks, used globally in small office/home office, home and small office networks to link devices and to provide Internet access with wireless routers and wireless access points in public places such as coffee shops, restaurants, hotels, libraries, and airports. ''Wi-Fi'' is a trademark of the Wi-Fi Alliance, which restricts the use of the term "''Wi-Fi Certified''" to products that successfully complete Interoperability Solutions for European Public Administrations, interoperability certification testing. Non-compliant hardware is simply referred to as WLAN, and it may or may not work with "''Wi-Fi Certified''" devices. the Wi-Fi Alliance consisted of more than 800 companies from ar ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Java (programming Language)
Java is a High-level programming language, high-level, General-purpose programming language, general-purpose, Memory safety, memory-safe, object-oriented programming, object-oriented programming language. It is intended to let programmers ''write once, run anywhere'' (Write once, run anywhere, WORA), meaning that compiler, compiled Java code can run on all platforms that support Java without the need to recompile. Java applications are typically compiled to Java bytecode, bytecode that can run on any Java virtual machine (JVM) regardless of the underlying computer architecture. The syntax (programming languages), syntax of Java is similar to C (programming language), C and C++, but has fewer low-level programming language, low-level facilities than either of them. The Java runtime provides dynamic capabilities (such as Reflective programming, reflection and runtime code modification) that are typically not available in traditional compiled languages. Java gained popularity sh ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
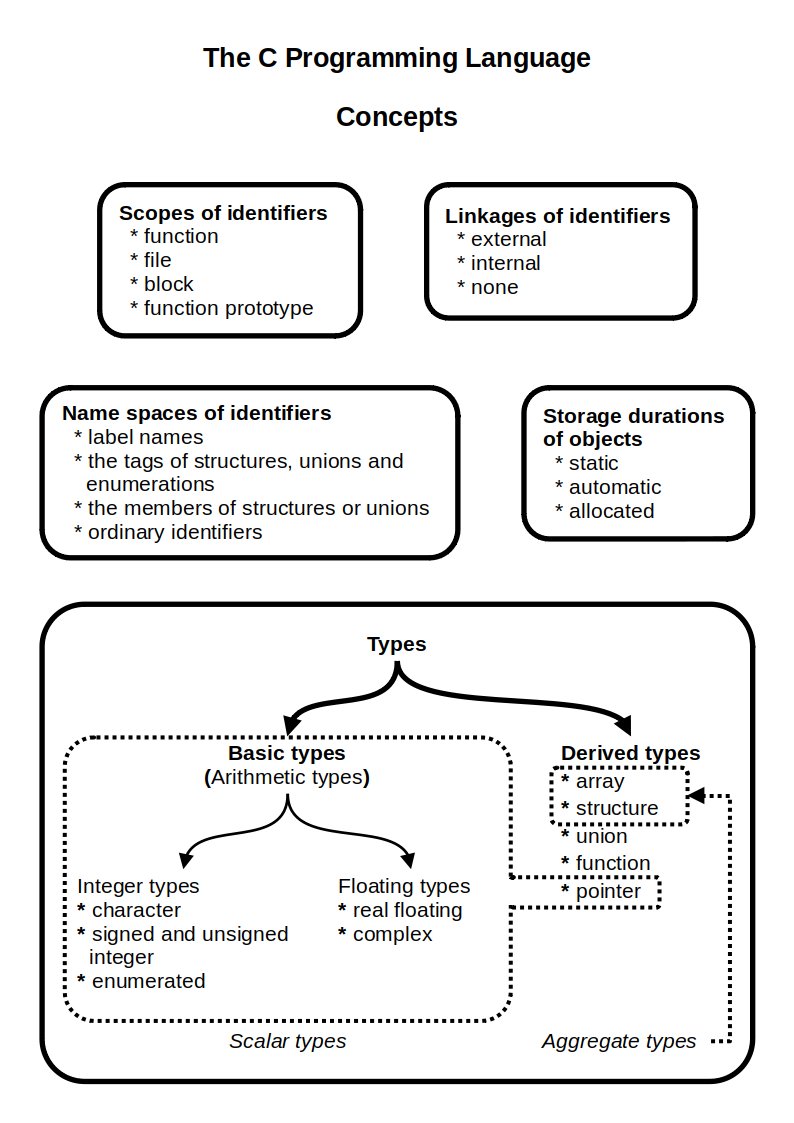
C (programming Language)
C (''pronounced'' '' – like the letter c'') is a general-purpose programming language. It was created in the 1970s by Dennis Ritchie and remains very widely used and influential. By design, C's features cleanly reflect the capabilities of the targeted Central processing unit, CPUs. It has found lasting use in operating systems code (especially in Kernel (operating system), kernels), device drivers, and protocol stacks, but its use in application software has been decreasing. C is commonly used on computer architectures that range from the largest supercomputers to the smallest microcontrollers and embedded systems. A successor to the programming language B (programming language), B, C was originally developed at Bell Labs by Ritchie between 1972 and 1973 to construct utilities running on Unix. It was applied to re-implementing the kernel of the Unix operating system. During the 1980s, C gradually gained popularity. It has become one of the most widely used programming langu ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Android (operating System)
Android is an operating system based on a modified version of the Linux kernel and other open-source software, open-source software, designed primarily for touchscreen-based mobile devices such as smartphones and tablet computer, tablets. Android has historically been developed by a consortium of developers known as the Open Handset Alliance, but its most widely used version is primarily developed by Google. First released in 2008, Android is the world's Usage share of operating systems, most widely used operating system; the latest version, released on June 10, 2025, is Android 16. At its core, the operating system is known as the Android Open Source Project (AOSP) and is free and open-source software (FOSS) primarily licensed under the Apache License. However, most devices run the proprietary software, proprietary Android version developed by Google, which ships with additional proprietary closed-source software pre-installed, most notably Google Mobile Services (GMS), which ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Linux
Linux ( ) is a family of open source Unix-like operating systems based on the Linux kernel, an kernel (operating system), operating system kernel first released on September 17, 1991, by Linus Torvalds. Linux is typically package manager, packaged as a Linux distribution (distro), which includes the kernel and supporting system software and library (computing), libraries—most of which are provided by third parties—to create a complete operating system, designed as a clone of Unix and released under the copyleft GPL license. List of Linux distributions, Thousands of Linux distributions exist, many based directly or indirectly on other distributions; popular Linux distributions include Debian, Fedora Linux, Linux Mint, Arch Linux, and Ubuntu, while commercial distributions include Red Hat Enterprise Linux, SUSE Linux Enterprise, and ChromeOS. Linux distributions are frequently used in server platforms. Many Linux distributions use the word "Linux" in their name, but the Free ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Windows
Windows is a Product lining, product line of Proprietary software, proprietary graphical user interface, graphical operating systems developed and marketed by Microsoft. It is grouped into families and subfamilies that cater to particular sectors of the computing industry – Windows (unqualified) for a consumer or corporate workstation, Windows Server for a Server (computing), server and Windows IoT for an embedded system. Windows is sold as either a consumer retail product or licensed to Original equipment manufacturer, third-party hardware manufacturers who sell products Software bundles, bundled with Windows. The first version of Windows, Windows 1.0, was released on November 20, 1985, as a graphical operating system shell for MS-DOS in response to the growing interest in graphical user interfaces (GUIs). The name "Windows" is a reference to the windowing system in GUIs. The 1990 release of Windows 3.0 catapulted its market success and led to various other product families ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
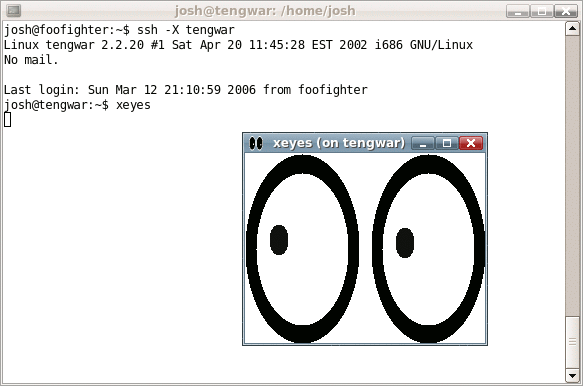
Secure Shell
The Secure Shell Protocol (SSH Protocol) is a cryptographic network protocol for operating network services securely over an unsecured network. Its most notable applications are remote login and command-line execution. SSH was designed for Unix-like operating systems as a replacement for Telnet and unsecured remote Unix shell protocols, such as the Berkeley Remote Shell (rsh) and the related rlogin and rexec protocols, which all use insecure, plaintext methods of authentication, like passwords. Since mechanisms like Telnet and Remote Shell are designed to access and operate remote computers, sending the authentication tokens (e.g. username and password) for this access to these computers across a public network in an unsecured way poses a great risk of 3rd parties obtaining the password and achieving the same level of access to the remote system as the telnet user. Secure Shell mitigates this risk through the use of encryption mechanisms that are intended to hide th ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Cryptographic Hash Function
A cryptographic hash function (CHF) is a hash algorithm (a map (mathematics), map of an arbitrary binary string to a binary string with a fixed size of n bits) that has special properties desirable for a cryptography, cryptographic application: * the probability of a particular n-bit output result (hash value) for a random input string ("message") is 2^ (as for any good hash), so the hash value can be used as a representative of the message; * finding an input string that matches a given hash value (a ''pre-image'') is infeasible, ''assuming all input strings are equally likely.'' The ''resistance'' to such search is quantified as security strength: a cryptographic hash with n bits of hash value is expected to have a ''preimage resistance'' strength of n bits, unless the space of possible input values is significantly smaller than 2^ (a practical example can be found in ); * a ''second preimage'' resistance strength, with the same expectations, refers to a similar problem of f ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |