|
SUPERAntiSpyware
SUPERAntiSpyware is a software application which can detect and remove spyware, adware, trojan horses, rogue security software, computer worms, rootkits, parasites and other potentially harmful software applications. Although it can detect various types of malware, SUPERAntiSpyware is not designed to replace antivirus software. Details SUPERAntiSpyware's virus definitions are updated several times a week and generally receive a build update once a month. The company claims that it is specifically designed to be compatible with other security applications, such as Kaspersky, and can, therefore, be used even when those other applications are incompatible with other anti-spyware products. The product is available as freeware for personal use with limited functions, such as no automatic update and scheduling and limited repair functions. Reception In 2011, SUPERAntiSpyware received a "DISMAL" rating from ''PC Magazine'', which complained that it had no real-time protection and t ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Support
Support may refer to: Arts, entertainment, and media * Supporting character Business and finance * Support (technical analysis) * Child support * Customer support * Income Support Construction * Support (structure), or lateral support, a type of structural support to help prevent sideways movement * Structural support, architectural components that include arches, beams, columns, balconies, and stretchers Law and politics * Advocacy, in politics, support for constituencies, issues, or legislation * Lateral and subjacent support, a legal term Mathematics Mathematics (generally) * Support (mathematics), subset of the domain of a function where it is non-zero valued * Support (measure theory), a subset of a measurable space * Supporting hyperplane, sometimes referred to as support Statistics * Support, the natural logarithm of the likelihood ratio, as used in phylogenetics * Method of support, in statistics, a technique that is used to make inferences from datase ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Rootkit
A rootkit is a collection of computer software, typically malicious, designed to enable access to a computer or an area of its software that is not otherwise allowed (for example, to an unauthorized user) and often masks its existence or the existence of other software. The term ''rootkit'' is a compound of "root" (the traditional name of the privileged account on Unix-like operating systems) and the word "kit" (which refers to the software components that implement the tool). The term "rootkit" has negative connotations through its association with malware. Rootkit installation can be automated, or an attacker can install it after having obtained root or administrator access. Obtaining this access is a result of direct attack on a system, i.e. exploiting a vulnerability (such as privilege escalation) or a password (obtained by cracking or social engineering tactics like "phishing"). Once installed, it becomes possible to hide the intrusion as well as to maintain privileged ac ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Spyware Removal
Spyware (a portmanteau for spying software) is software with malicious behaviour that aims to gather information about a person or organization and send it to another entity in a way that harms the user—for example, by violating their privacy or endangering their device's security. This behaviour may be present in malware as well as in legitimate software. Websites may engage in spyware behaviours like web tracking. Hardware devices may also be affected. Spyware is frequently associated with advertising and involves many of the same criticism of advertising, issues. Because these behaviors are so common, and can have non-harmful uses, providing a precise definition of spyware is a difficult task.FTC Report (2005)." History The first recorded use of the term :wikt:spyware, spyware occurred on October 16, 1995 in a Usenet post that poked fun at Microsoft's business model.Vossen, Roland (attributed); October 21, 1995Win 95 Source code in c!!posted to rec..programmer; retrieve ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
CNET
''CNET'' (short for "Computer Network") is an American media website that publishes reviews, news, articles, blogs, podcasts, and videos on technology and consumer electronics globally. ''CNET'' originally produced content for radio and television in addition to its website and now uses new media distribution methods through its Internet television network, CNET Video, and its podcast and blog networks. Founded in 1994 by Halsey Minor and Shelby Bonnie, it was the flagship brand of CNET Networks and became a brand of CBS Interactive through that unit's acquisition of CNET Networks in 2008. It has been owned by Red Ventures since October 30, 2020. Other than English, ''CNETs region- and language-specific editions include Chinese, French, German, Japanese, Korean, and Spanish. History Origins After leaving PepsiCo, Halsey Minor and Shelby Bonnie launched ''CNET'' in 1994, after website Yahoo! was launched. With help from Fox Network co-founder Kevin Wendle and fo ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
PC Magazine
''PC Magazine'' (shortened as ''PCMag'') is an American computer magazine published by Ziff Davis. A print edition was published from 1982 to January 2009. Publication of online and offline, online editions started in late 1994 and have continued to the present day. Overview ''PC Magazine'' provides reviews and previews of the latest personal computer hardware, hardware and software for the information technology professional. Articles are written by leading experts including John C. Dvorak, whose regular column and "Inside Track" feature were among the magazine's most popular attractions. Other regular departments include columns by long-time editor-in-chief Michael J. Miller (corporate executive), Michael J. Miller ("Forward Thinking"), Bill Machrone, and Jim Louderback, as well as: * "First Looks" (a collection of reviews of newly released products) * "Pipeline" (a collection of short articles and snippets on computer-industry developments) * "Solutions" (which includes ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Freeware
Freeware is software, most often proprietary, that is distributed at no monetary cost to the end user. There is no agreed-upon set of rights, license, or EULA that defines ''freeware'' unambiguously; every publisher defines its own rules for the freeware it offers. For instance, modification, redistribution by third parties, and reverse engineering are permitted by some publishers but prohibited by others. Unlike with free and open-source software, which are also often distributed free of charge, the source code for freeware is typically not made available. Freeware may be intended to benefit its producer by, for example, encouraging sales of a more capable version, as in the freemium and shareware business models. History The term ''freeware'' was coined in 1982 by Andrew Fluegelman, who wanted to sell PC-Talk, the communications application he had created, outside of commercial distribution channels. Fluegelman distributed the program via a process now termed '' share ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Anti-spyware
Spyware (a portmanteau for spying software) is software with malicious behaviour that aims to gather information about a person or organization and send it to another entity in a way that harms the user—for example, by violating their privacy or endangering their device's security. This behaviour may be present in malware as well as in legitimate software. Websites may engage in spyware behaviours like web tracking. Hardware devices may also be affected. Spyware is frequently associated with advertising and involves many of the same issues. Because these behaviors are so common, and can have non-harmful uses, providing a precise definition of spyware is a difficult task.FTC Report (2005)." History The first recorded use of the term :wikt:spyware, spyware occurred on October 16, 1995 in a Usenet post that poked fun at Microsoft's business model.Vossen, Roland (attributed); October 21, 1995Win 95 Source code in c!!posted to rec..programmer; retrieved from groups.google.com ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Kaspersky Internet Security
Kaspersky Internet Security (often abbreviated to KIS) is an internet security suite developed by Kaspersky Lab compatible with Microsoft Windows and Mac OS X. Kaspersky Internet Security offers protection from malware, as well as email spam, phishing and hacking attempts, and data leaks. Kaspersky Lab Diagnostics results are distributed to relevant developers through the MIT License. Windows edition Version 2007 (6.0) Version 6.0 was the first release of KIS. PC World magazine praised version 6.0's detection of malware. KIS detected 100 percent of threats on a subset of the January 2006 wild-list, a list of prevalent threats. The suite detected almost 100 (99.57%) percent of adware samples. KIS has the ability to scan within compressed or packed files, detecting 83.3 percent of the "hidden" malware. However, version 6.0 was criticized for not completely removing malware by leaving Registry entries and files. PC World also highlighted the suite's false positives — eigh ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Antivirus Software
Antivirus software (abbreviated to AV software), also known as anti-malware, is a computer program used to prevent, detect, and remove malware. Antivirus software was originally developed to detect and remove computer viruses, hence the name. However, with the proliferation of other malware, antivirus software started to protect from other computer threats. In particular, modern antivirus software can protect users from malicious browser helper objects (BHOs), browser hijackers, ransomware, keyloggers, backdoors, rootkits, trojan horses, worms, malicious LSPs, dialers, fraud tools, adware, and spyware. Some products also include protection from other computer threats, such as infected and malicious URLs, spam, scam and phishing attacks, online identity (privacy), online banking attacks, social engineering techniques, advanced persistent threat (APT), and botnet DDoS attacks. History 1949–1980 period (pre-antivirus days) Although the roots of the c ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Malware
Malware (a portmanteau for ''malicious software'') is any software intentionally designed to cause disruption to a computer, server, client, or computer network, leak private information, gain unauthorized access to information or systems, deprive access to information, or which unknowingly interferes with the user's computer security and privacy. By contrast, software that causes harm due to some deficiency is typically described as a software bug. Malware poses serious problems to individuals and businesses on the Internet. According to Symantec's 2018 Internet Security Threat Report (ISTR), malware variants number has increased to 669,947,865 in 2017, which is twice as many malware variants as in 2016. Cybercrime, which includes malware attacks as well as other crimes committed by computer, was predicted to cost the world economy $6 trillion USD in 2021, and is increasing at a rate of 15% per year. Many types of malware exist, including computer viruses, worms, Trojan ho ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
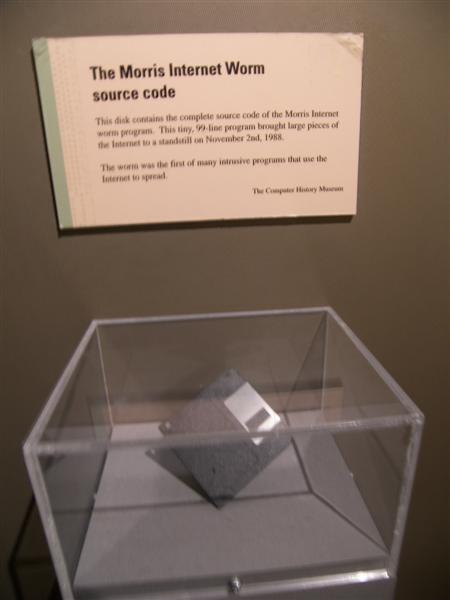
Computer Worm
A computer worm is a standalone malware computer program that replicates itself in order to spread to other computers. It often uses a computer network to spread itself, relying on security failures on the target computer to access it. It will use this machine as a host to scan and infect other computers. When these new worm-invaded computers are controlled, the worm will continue to scan and infect other computers using these computers as hosts, and this behaviour will continue. Computer worms use recursive methods to copy themselves without host programs and distribute themselves based on the law of exponential growth, thus controlling and infecting more and more computers in a short time. Worms almost always cause at least some harm to the network, even if only by consuming bandwidth, whereas viruses almost always corrupt or modify files on a targeted computer. Many worms are designed only to spread, and do not attempt to change the systems they pass through. However, as ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Mebibyte
The byte is a unit of digital information that most commonly consists of eight bits. Historically, the byte was the number of bits used to encode a single character of text in a computer and for this reason it is the smallest addressable unit of memory in many computer architectures. To disambiguate arbitrarily sized bytes from the common 8-bit definition, network protocol documents such as The Internet Protocol () refer to an 8-bit byte as an octet. Those bits in an octet are usually counted with numbering from 0 to 7 or 7 to 0 depending on the bit endianness. The first bit is number 0, making the eighth bit number 7. The size of the byte has historically been hardware-dependent and no definitive standards existed that mandated the size. Sizes from 1 to 48 bits have been used. The six-bit character code was an often-used implementation in early encoding systems, and computers using six-bit and nine-bit bytes were common in the 1960s. These systems often had memory words ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |