|
SSPI
Security Support Provider Interface (SSPI) is a component of Windows API that performs security-related operations such as authentication. SSPI functions as a common interface to several Security Support Providers (SSPs): A Security Support Provider is a dynamic-link library (DLL) that makes one or more security packages available to apps. Providers The following SSPs are included in Windows: * NTLMSSP (msv1_0.dll) – Introduced in Windows NT 3.51. Provides NTLM challenge/response authentication for Windows domains prior to Windows 2000 and for systems that are not part of a domain. * Kerberos (kerberos.dll) – Introduced in Windows 2000 and updated in Windows Vista to support AES. Performs authentication for Windows domains in Windows 2000 and later. * NegotiateSSP (secur32.dll) – Introduced in Windows 2000. Provides single sign-on capability, sometimes referred to as Integrated Windows Authentication (especially in the context of IIS). Prior to Windows 7, it tries ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
|
|
Generic Security Services Application Program Interface
The Generic Security Service Application Programming Interface (GSSAPI, also GSS-API) is an application programming interface for programs to access security services. The GSSAPI is an IETF standard that addresses the problem of many similar but incompatible security services in use . Operation The GSSAPI, by itself, does not provide any security. Instead, security-service vendors provide GSSAPI ''implementations'' - usually in the form of libraries installed with their security software. These libraries present a GSSAPI-compatible interface to application writers who can write their application to use only the vendor-independent GSSAPI. If the security implementation ever needs replacing, the application need not be rewritten. The definitive feature of GSSAPI applications is the exchange of opaque messages (''tokens'') which hide the implementation detail from the higher-level application. The client and server sides of the application are written to convey the tokens given t ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
|
|
Integrated Windows Authentication
Integrated Windows Authentication (IWA) is a term associated with Microsoft products that refers to the SPNEGO, Kerberos, and NTLMSSP authentication protocols with respect to SSPI functionality introduced with Microsoft Windows 2000 and included with later Windows NT-based operating systems. The term is used more commonly for the automatically authenticated connections between Microsoft Internet Information Services, Internet Explorer, and other Active Directory aware applications. IWA is also known by several names like ''HTTP Negotiate authentication'', ''NT Authentication'', ''NTLM Authentication'', ''Domain authentication'', ''Windows Integrated Authentication'', ''Windows NT Challenge/Response authentication'', or simply ''Windows Authentication''. Overview Integrated Windows Authentication uses the security features of Windows clients and servers. Unlike Basic Authentication or Digest Authentication, initially, it does not prompt users for a user name and password. The ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
|
|
NTLMSSP
NTLMSSP (NT LAN Manager (NTLM) Security Support Provider) is a binary messaging protocol used by the Microsoft Security Support Provider Interface (SSPI) to facilitate NTLM challenge-response authentication and to negotiate integrity and confidentiality options. NTLMSSP is used wherever SSPI authentication is used including Server Message Block / CIFS extended security authentication, HTTP HTTP (Hypertext Transfer Protocol) is an application layer protocol in the Internet protocol suite model for distributed, collaborative, hypermedia information systems. HTTP is the foundation of data communication for the World Wide Web, wher ... Negotiate authentication (e.g. IIS with IWA turned on) and MSRPC services. The NTLMSSP and NTLM challenge-response protocol have been documented in Microsoft's Open Protocol Specification. [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
|
|
Network Level Authentication
Remote Desktop Services (RDS), known as Terminal Services in Windows Server 2008 and earlier, is one of the components of Microsoft Windows that allow a user to initiate and control an interactive session on a remote computer or virtual machine over a network connection. RDS is Microsoft's implementation of thin client architecture, where Windows software, and the entire desktop of the computer running RDS, are made accessible to any remote client machine that supports Remote Desktop Protocol (RDP). User interfaces are displayed from the server onto the client system and input from the client system is transmitted to the server - where software execution takes place. This is in contrast to application streaming systems, like Microsoft App-V, in which computer programs are streamed to the client on-demand and executed on the client machine. RDS was first released in 1998 as ''Terminal Server'' in Windows NT 4.0 Terminal Server Edition, a stand-alone edition of Windows NT 4.0 ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
|
|
NTLM
In a Windows network, NT (New Technology) LAN Manager (NTLM) is a suite of Microsoft security protocols intended to provide authentication, integrity, and confidentiality to users. NTLM is the successor to the authentication protocol in Microsoft LAN Manager (LANMAN), an older Microsoft product. The NTLM protocol suite is implemented in a Security Support Provider, which combines the LAN Manager authentication protocol, NTLMv1, NTLMv2 and NTLM2 Session protocols in a single package. Whether these protocols are used or can be used on a system, which is governed by Group Policy settings, for which different versions of Windows have different default settings. NTLM passwords are considered weak because they can be brute-forced very easily with modern hardware. Protocol NTLM is a challenge–response authentication protocol which uses three messages to authenticate a client in a connection-oriented environment (connectionless is similar), and a fourth additional message if integr ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
|
|
Windows 2000
Windows 2000 is a major release of the Windows NT operating system developed by Microsoft, targeting the server and business markets. It is the direct successor to Windows NT 4.0, and was Software release life cycle#Release to manufacturing (RTM), released to manufacturing on December 15, 1999, and then to retail on February 17, 2000 for all versions, with Windows 2000 Datacenter Server being released to retail on September 26, 2000. Windows 2000 introduces NTFS 3.0, Encrypting File System, and basic and dynamic disk storage. Support for people with disabilities is improved over Windows NT 4.0 with a number of new Assistive technology, assistive technologies, and Microsoft increased support for different languages and Locale (computer software), locale information. The Windows 2000 Server family has additional features, most notably the introduction of Active Directory, which in the years following became a widely used directory service in business environments. Although not pre ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
|
|
Kerberos (protocol)
Kerberos () is a computer-network authentication protocol that works on the basis of ''tickets'' to allow nodes communicating over a non-secure network to prove their identity to one another in a secure manner. Its designers aimed it primarily at a client–server model, and it provides mutual authentication—both the user and the server verify each other's identity. Kerberos protocol messages are protected against eavesdropping and replay attacks. Kerberos builds on symmetric-key cryptography and requires a trusted third party, and optionally may use public-key cryptography during certain phases of authentication.RFC 4556, abstract. Kerberos uses UDP port 88 by default. The protocol was named after the character '' Kerberos'' (or ''Cerberus'') from Greek mythology, the ferocious three-headed guard dog of Hades. History and development The Massachusetts Institute of Technology (MIT) developed Kerberos in 1988 to protect network services provided by Project Athena. Its ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
|
 |
Windows API
The Windows API, informally WinAPI, is the foundational application programming interface (API) that allows a computer program to access the features of the Microsoft Windows operating system in which the program is running. Programs can access API functionality via shared-library technologies or via system-file access. Each major version of the Windows API has a distinct name that identifies a compatibility aspect of that version. For example, Win32 is the major version of Windows API that runs on 32-bit systems. The name, Windows API, collectively refers to all versions of this capability of Windows. Microsoft provides developer support via a software development kit, Microsoft Windows SDK, which includes documentation and tools for building software based on the Windows API. Services This section lists notable services provided by the Windows API. Base Services Base services include features such as the file system, devices, processes, threads, and error handl ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
|
Public Key Certificate
In cryptography, a public key certificate, also known as a digital certificate or identity certificate, is an electronic document used to prove the validity of a Key authentication, public key. The certificate includes the public key and information about it, information about the identity of its owner (called the subject), and the digital signature of an entity that has verified the certificate's contents (called the issuer). If the device examining the certificate trusts the issuer and finds the signature to be a valid signature of that issuer, then it can use the included public key to communicate securely with the certificate's subject. In email encryption, code signing, and Electronic signature, e-signature systems, a certificate's subject is typically a person or organization. However, in Transport Layer Security (TLS) a certificate's subject is typically a computer or other device, though TLS certificates may identify organizations or individuals in addition to their core rol ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
|
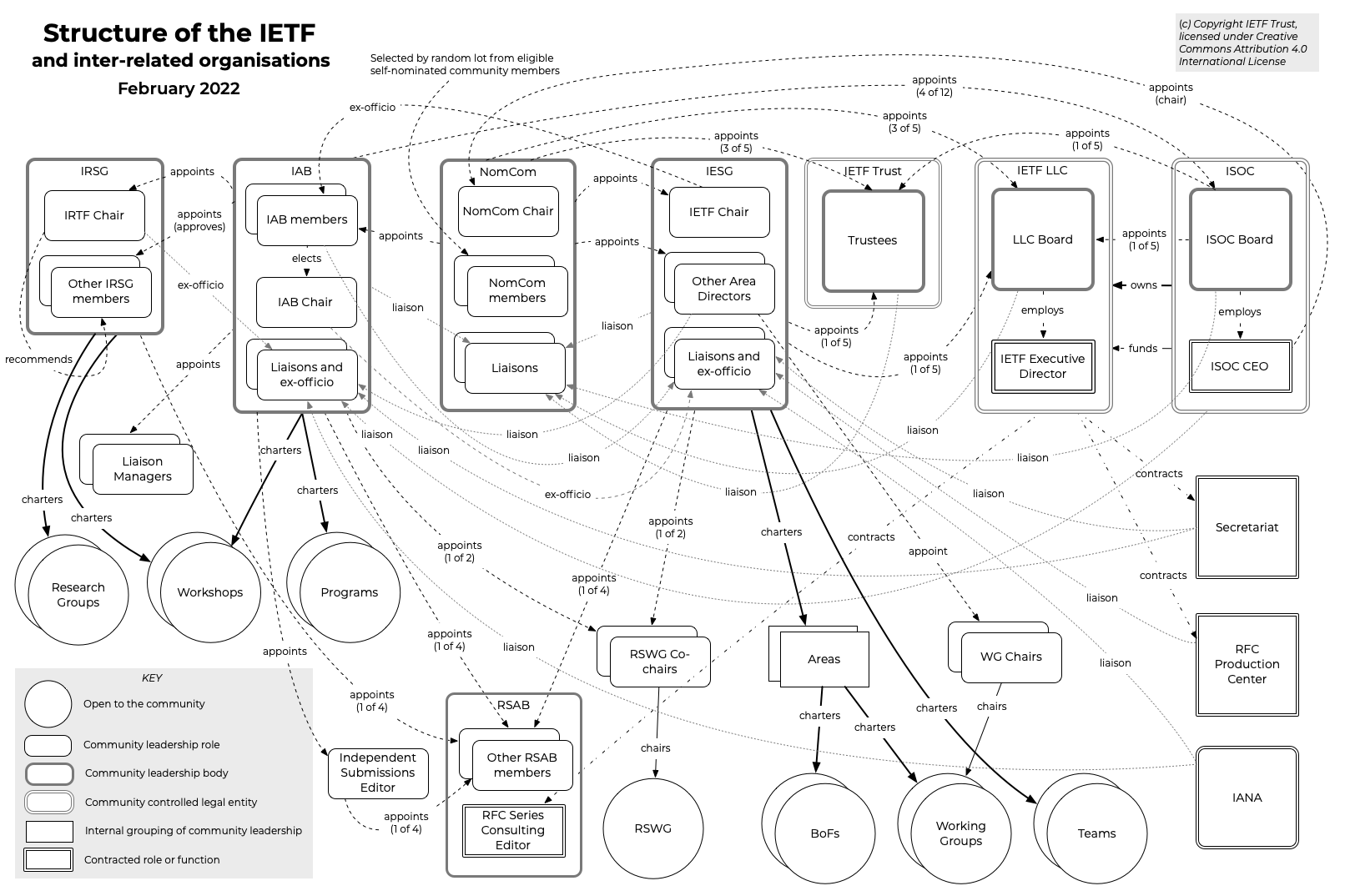 |
Internet Engineering Task Force
The Internet Engineering Task Force (IETF) is a standards organization for the Internet standard, Internet and is responsible for the technical standards that make up the Internet protocol suite (TCP/IP). It has no formal membership roster or requirements and all its participants are volunteers. Their work is usually funded by employers or other sponsors. The IETF was initially supported by the federal government of the United States but since 1993 has operated under the auspices of the Internet Society, a non-profit organization with local chapters around the world. Organization There is no membership in the IETF. Anyone can participate by signing up to a working group mailing list, or registering for an IETF meeting. The IETF operates in a bottom-up task creation mode, largely driven by working groups. Each working group normally has appointed two co-chairs (occasionally three); a charter that describes its focus; and what it is expected to produce, and when. It is open ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
|
Windows 95
Windows 95 is a consumer-oriented operating system developed by Microsoft and the first of its Windows 9x family of operating systems, released to manufacturing on July 14, 1995, and generally to retail on August 24, 1995. Windows 95 merged Microsoft's formerly separate MS-DOS and Microsoft Windows products into a single product and featured significant improvements over its predecessor, most notably in the graphical user interface (GUI) and in its simplified " plug-and-play" features. There were also major changes made to the core components of the operating system, such as moving from a mainly cooperatively multitasked 16-bit architecture of its predecessor Windows 3.1 to a 32-bit preemptive multitasking architecture. Windows 95 introduced numerous functions and features that were featured in later Windows versions, and continue in modern variations to this day, such as the taskbar, the notification area, file shortcuts on the desktop, plug and play driver integration, ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |