|
SM3 (hash Function)
ShangMi 3 (SM3) is a cryptographic hash function, standardised for use in commercial cryptography in China. It was published by the National Cryptography Administration ( zh, 国家密码管理局) on 2010-12-17 as "GM/T 0004-2012: SM3 cryptographic hash algorithm". SM3 is used for implementing digital signatures, message authentication codes, and pseudorandom number generators. The algorithm is public and is considered similar to SHA-256 in security and efficiency. SM3 is used with Transport Layer Security. Definitive standards SM3 is defined in each of: *GM/T 0004-2012: SM3 cryptographic hash algorithm *GB/T 32905-2016: Information security techniques—SM3 cryptographic hash algorithmWang Xiaoyun. Journal of Information Security Research, 2016, 2(11): 983-994. *ISO/IEC 10118-3:2018—IT Security techniques—Hash-functions—Part 3: Dedicated hash-functions *IETF RFC draft-sca-cfrg-sm3-02 References See also *SM4 (cipher) ShāngMì 4 (SM4, 商密4) (formerly SMS4) ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Cryptographic Hash Function
A cryptographic hash function (CHF) is a hash algorithm (a map (mathematics), map of an arbitrary binary string to a binary string with a fixed size of n bits) that has special properties desirable for a cryptography, cryptographic application: * the probability of a particular n-bit output result (hash value) for a random input string ("message") is 2^ (as for any good hash), so the hash value can be used as a representative of the message; * finding an input string that matches a given hash value (a ''pre-image'') is infeasible, ''assuming all input strings are equally likely.'' The ''resistance'' to such search is quantified as security strength: a cryptographic hash with n bits of hash value is expected to have a ''preimage resistance'' strength of n bits, unless the space of possible input values is significantly smaller than 2^ (a practical example can be found in ); * a ''second preimage'' resistance strength, with the same expectations, refers to a similar problem of f ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
CNNIC
The China Internet Network Information Center (CNNIC; ) is a public institution affiliated with the Ministry of Industry and Information Technology. Founded on 3 June 1997 and based in Zhongguancun, Beijing, the center manages the Country code top-level domain, country code top-level domain name of the People's Republic of China, namely the .cn domain name. Responsibility areas Domain name registry service CNNIC is responsible for operating and administering China’s domain name registry. CNNIC manages both the ".cn" country code top level domain and the Chinese domain name system (internationalized domain names that contain Chinese characters). As of April 2017, the total number of Chinese domain names was about 21 million. As of January 2017, CNNIC only opened the CN domain to registered businesses, required supporting documentations for domain registration such as business license or personal ID, and suspended overseas registrars even for domestic registrants. CNNIC deni ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Message Authentication Codes
In cryptography, a message authentication code (MAC), sometimes known as an authentication tag, is a short piece of information used for authenticating and integrity-checking a message. In other words, it is used to confirm that the message came from the stated sender (its authenticity) and has not been changed (its integrity). The MAC value allows verifiers (who also possess a secret key) to detect any changes to the message content. Terminology The term message integrity code (MIC) is frequently substituted for the term ''MAC'', especially in communications to distinguish it from the use of the latter as '' media access control address'' (''MAC address''). However, some authors use MIC to refer to a message digest, which aims only to uniquely but opaquely identify a single message. RFC 4949 recommends avoiding the term ''message integrity code'' (MIC), and instead using ''checksum'', ''error detection code'', ''hash'', ''keyed hash'', ''message authentication code'', or ''prote ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Pseudorandom Number Generators
A pseudorandom number generator (PRNG), also known as a deterministic random bit generator (DRBG), is an algorithm for generating a sequence of numbers whose properties approximate the properties of sequences of random numbers. The PRNG-generated sequence is not truly random, because it is completely determined by an initial value, called the PRNG's ''seed'' (which may include truly random values). Although sequences that are closer to truly random can be generated using hardware random number generators, ''pseudorandom number generators'' are important in practice for their speed in number generation and their reproducibility. PRNGs are central in applications such as simulations (e.g. for the Monte Carlo method), electronic games (e.g. for procedural generation), and cryptography. Cryptographic applications require the output not to be predictable from earlier outputs, and more elaborate algorithms, which do not inherit the linearity of simpler PRNGs, are needed. Good statist ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Internet Engineering Task Force
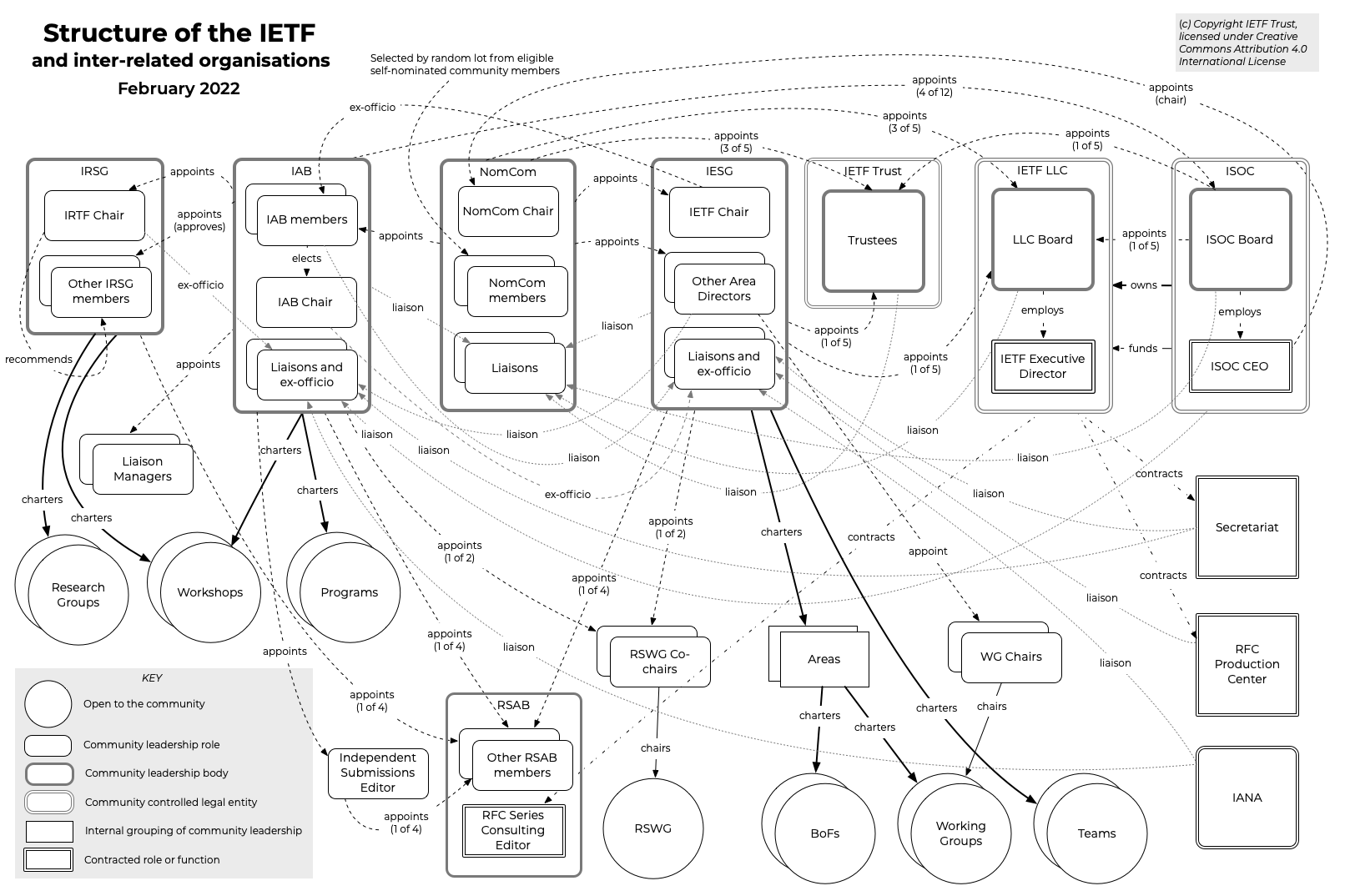
The Internet Engineering Task Force (IETF) is a standards organization for the Internet standard, Internet and is responsible for the technical standards that make up the Internet protocol suite (TCP/IP). It has no formal membership roster or requirements and all its participants are volunteers. Their work is usually funded by employers or other sponsors. The IETF was initially supported by the federal government of the United States but since 1993 has operated under the auspices of the Internet Society, a non-profit organization with local chapters around the world. Organization There is no membership in the IETF. Anyone can participate by signing up to a working group mailing list, or registering for an IETF meeting. The IETF operates in a bottom-up task creation mode, largely driven by working groups. Each working group normally has appointed two co-chairs (occasionally three); a charter that describes its focus; and what it is expected to produce, and when. It is open ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
SHA-256
SHA-2 (Secure Hash Algorithm 2) is a set of cryptographic hash functions designed by the United States National Security Agency (NSA) and first published in 2001. They are built using the Merkle–Damgård construction, from a one-way compression function itself built using the Davies–Meyer structure from a specialized block cipher. SHA-2 includes significant changes from its predecessor, SHA-1. The SHA-2 family consists of six hash functions with digests (hash values) that are 224, 256, 384 or 512 bits: SHA-224, SHA-256, SHA-384, SHA-512, SHA-512/224, SHA-512/256. SHA-256 and SHA-512 are hash functions whose digests are eight 32-bit and 64-bit words, respectively. They use different shift amounts and additive constants, but their structures are otherwise virtually identical, differing only in the number of rounds. SHA-224 and SHA-384 are truncated versions of SHA-256 and SHA-512 respectively, computed with different initial values. SHA-512/224 and SHA-512/256 are also trunc ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Transport Layer Security
Transport Layer Security (TLS) is a cryptographic protocol designed to provide communications security over a computer network, such as the Internet. The protocol is widely used in applications such as email, instant messaging, and voice over IP, but its use in securing HTTPS remains the most publicly visible. The TLS protocol aims primarily to provide security, including privacy (confidentiality), integrity, and authenticity through the use of cryptography, such as the use of certificates, between two or more communicating computer applications. It runs in the presentation layer and is itself composed of two layers: the TLS record and the TLS handshake protocols. The closely related Datagram Transport Layer Security (DTLS) is a communications protocol that provides security to datagram-based applications. In technical writing, references to "(D)TLS" are often seen when it applies to both versions. TLS is a proposed Internet Engineering Task Force (IETF) standard, fir ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Wang Xiaoyun
Wang Xiaoyun (; born 1966) is a Chinese cryptographer, mathematician, and computer scientist. She is a professor in the Department of Mathematics and System Science of Shandong University and an academician of the Chinese Academy of Sciences. Early life and education Wang was born in Zhucheng, Shandong Province. She gained bachelor's (1987), master's (1990) and doctorate (1993) degrees at Shandong University, and subsequently lectured in the mathematics department from 1993. Her doctoral advisor was Pan Chengdong. Wang was appointed assistant professor in 1995, and full professor in 2001. She became the Chen Ning Yang Professor of the Center for Advanced Study, Tsinghua University in 2005. Career and research At the rump session of CRYPTO 2004, she and co-authors demonstrated collision attacks against MD5, SHA-0 and other related hash functions (a collision occurs when two distinct messages result in the same hash function output). They received a standing ovation for their ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
SM4 (cipher)
ShāngMì 4 (SM4, 商密4) (formerly SMS4) is a block cipher, standardised for commercial cryptography in China. It is used in the Chinese National Standard for Wireless LAN WAPI (WLAN Authentication and Privacy Infrastructure), and with Transport Layer Security. SM4 was a cipher proposed for the IEEE 802.11i standard, but it has so far been rejected. One of the reasons for the rejection has been opposition to the WAPI fast-track proposal by the IEEE. SM4 was published as in 2021. The SM4 algorithm was drafted by Data Assurance & Communication Security Center, Chinese Academy of Sciences (CAS), and Commercial Cryptography Testing Center, National Cryptography Administration. It is mainly developed by Lü Shuwang ( zh, 吕述望). The algorithm was declassified in January, 2006, and it became a national standard (GB/T 32907-2016) in August 2016.Lu Shuwang. Journal of Information Security Research, 2016, 2(11): 995-1007. Cipher detail The SM4 cipher has a key size and a blo ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Cryptographic Hash Functions
A cryptographic hash function (CHF) is a hash algorithm (a map of an arbitrary binary string to a binary string with a fixed size of n bits) that has special properties desirable for a cryptographic application: * the probability of a particular n-bit output result (hash value) for a random input string ("message") is 2^ (as for any good hash), so the hash value can be used as a representative of the message; * finding an input string that matches a given hash value (a ''pre-image'') is infeasible, ''assuming all input strings are equally likely.'' The ''resistance'' to such search is quantified as security strength: a cryptographic hash with n bits of hash value is expected to have a ''preimage resistance'' strength of n bits, unless the space of possible input values is significantly smaller than 2^ (a practical example can be found in ); * a ''second preimage'' resistance strength, with the same expectations, refers to a similar problem of finding a second message that mat ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |