|
Lightweight Cipher
Cryptography, or cryptology (from "hidden, secret"; and ''graphein'', "to write", or ''-logia'', "study", respectively), is the practice and study of techniques for secure communication in the presence of adversarial behavior. More generally, cryptography is about constructing and analyzing protocols that prevent third parties or the public from reading private messages. Modern cryptography exists at the intersection of the disciplines of mathematics, computer science, information security, electrical engineering, digital signal processing, physics, and others. Core concepts related to information security ( data confidentiality, data integrity, authentication, and non-repudiation) are also central to cryptography. Practical applications of cryptography include electronic commerce, chip-based payment cards, digital currencies, computer passwords, and military communications. Cryptography prior to the modern age was effectively synonymous with encryption, converting r ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Password
A password, sometimes called a passcode, is secret data, typically a string of characters, usually used to confirm a user's identity. Traditionally, passwords were expected to be memorized, but the large number of password-protected services that a typical individual accesses can make memorization of unique passwords for each service impractical. Using the terminology of the NIST Digital Identity Guidelines, the secret is held by a party called the ''claimant'' while the party verifying the identity of the claimant is called the ''verifier''. When the claimant successfully demonstrates knowledge of the password to the verifier through an established authentication protocol, the verifier is able to infer the claimant's identity. In general, a password is an arbitrary String (computer science), string of character (computing), characters including letters, digits, or other symbols. If the permissible characters are constrained to be numeric, the corresponding secret is sometimes ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Algorithm
In mathematics and computer science, an algorithm () is a finite sequence of Rigour#Mathematics, mathematically rigorous instructions, typically used to solve a class of specific Computational problem, problems or to perform a computation. Algorithms are used as specifications for performing calculations and data processing. More advanced algorithms can use Conditional (computer programming), conditionals to divert the code execution through various routes (referred to as automated decision-making) and deduce valid inferences (referred to as automated reasoning). In contrast, a Heuristic (computer science), heuristic is an approach to solving problems without well-defined correct or optimal results.David A. Grossman, Ophir Frieder, ''Information Retrieval: Algorithms and Heuristics'', 2nd edition, 2004, For example, although social media recommender systems are commonly called "algorithms", they actually rely on heuristics as there is no truly "correct" recommendation. As an e ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Mathematical Theory
A theory is a systematic and rational form of abstract thinking about a phenomenon, or the conclusions derived from such thinking. It involves contemplative and logical reasoning, often supported by processes such as observation, experimentation, and research. Theories can be scientific, falling within the realm of empirical and testable knowledge, or they may belong to non-scientific disciplines, such as philosophy, art, or sociology. In some cases, theories may exist independently of any formal discipline. In modern science, the term "theory" refers to Scientific theory, scientific theories, a well-confirmed type of explanation of nature, made in a way Consistency, consistent with the scientific method, and fulfilling the Scientific theory#Characteristics of theories, criteria required by modern science. Such theories are described in such a way that scientific tests should be able to provide Empirical evidence, empirical support for it, or Empirical evidence, empirical contradi ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
World War II
World War II or the Second World War (1 September 1939 – 2 September 1945) was a World war, global conflict between two coalitions: the Allies of World War II, Allies and the Axis powers. World War II by country, Nearly all of the world's countries participated, with many nations mobilising all resources in pursuit of total war. Tanks in World War II, Tanks and Air warfare of World War II, aircraft played major roles, enabling the strategic bombing of cities and delivery of the Atomic bombings of Hiroshima and Nagasaki, first and only nuclear weapons ever used in war. World War II is the List of wars by death toll, deadliest conflict in history, causing World War II casualties, the death of 70 to 85 million people, more than half of whom were civilians. Millions died in genocides, including the Holocaust, and by massacres, starvation, and disease. After the Allied victory, Allied-occupied Germany, Germany, Allied-occupied Austria, Austria, Occupation of Japan, Japan, a ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
World War I
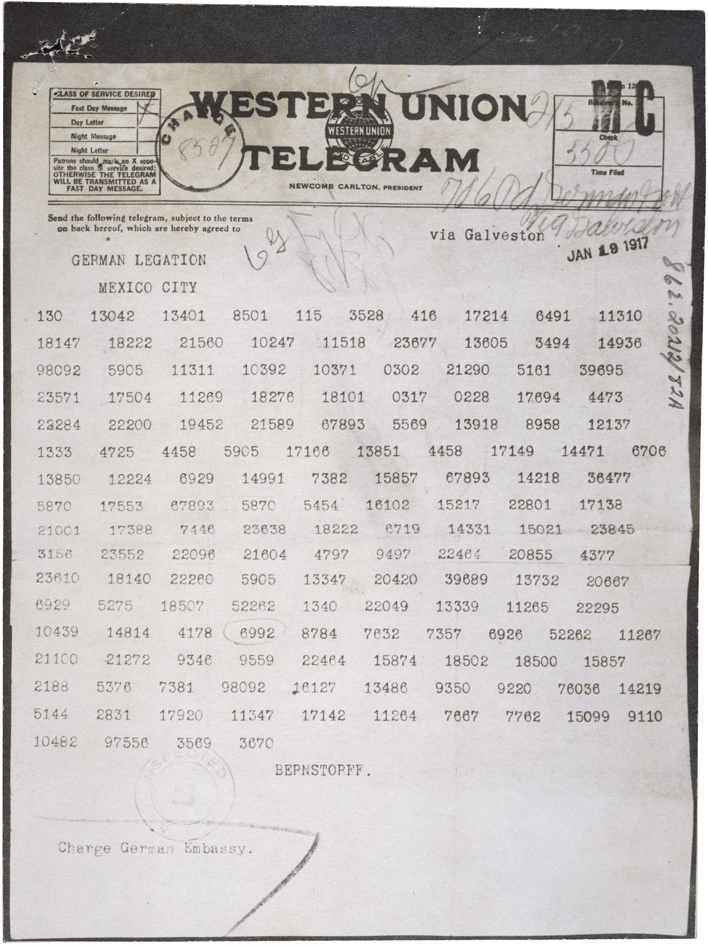
World War I or the First World War (28 July 1914 – 11 November 1918), also known as the Great War, was a World war, global conflict between two coalitions: the Allies of World War I, Allies (or Entente) and the Central Powers. Fighting took place mainly in European theatre of World War I, Europe and the Middle Eastern theatre of World War I, Middle East, as well as in parts of African theatre of World War I, Africa and the Asian and Pacific theatre of World War I, Asia-Pacific, and in Europe was characterised by trench warfare; the widespread use of Artillery of World War I, artillery, machine guns, and Chemical weapons in World War I, chemical weapons (gas); and the introductions of Tanks in World War I, tanks and Aviation in World War I, aircraft. World War I was one of the List of wars by death toll, deadliest conflicts in history, resulting in an estimated World War I casualties, 10 million military dead and more than 20 million wounded, plus some 10 million civilian de ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Rotor Machine
In cryptography, a rotor machine is an electro-mechanical stream cipher device used for encrypting and decrypting messages. Rotor machines were the cryptographic state-of-the-art for much of the 20th century; they were in widespread use from the 1920s to the 1970s. The most famous example is the German Enigma machine, the output of which was deciphered by the Allies during World War II, producing intelligence code-named '' Ultra''. Description The primary component of a rotor machine is a set of ''rotors'', also termed ''wheels'' or ''drums'', which are rotating disks with an array of electrical contacts on either side. The wiring between the contacts implements a fixed substitution of letters, replacing them in some complex fashion. On its own, this would offer little security; however, before or after encrypting each letter, the rotors advance positions, changing the substitution. By this means, a rotor machine produces a complex polyalphabetic substitution cipher, whic ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Eavesdropping
Eavesdropping is the act of secretly or stealthily listening to the private conversation or communications of others without their consent in order to gather information. Etymology The verb ''eavesdrop'' is a back-formation from the noun ''eavesdropper'' ("a person who eavesdrops"), which was formed from the related noun ''eavesdrop'' ("the dripping of water from the eaves of a house; the ground on which such water falls"). An eavesdropper was someone who would hang from the eave of a building so as to hear what is said within. The PBS documentaries ''Inside the Court of Henry VIII'' (April 8, 2015) and ''Secrets of Henry VIII’s Palace'' (June 30, 2013) include segments that display and discuss "eavedrops", carved wooden figures Henry VIII had built into the eaves (overhanging edges of the beams in the ceiling) of Hampton Court to discourage unwanted gossip or dissension from the King's wishes and rule, to foment paranoia and fear, and demonstrate that everything said there wa ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Alice And Bob
Alice and Bob are fictional characters commonly used as placeholders in discussions about cryptography, cryptographic systems and Cryptographic protocol, protocols, and in other science and engineering literature where there are several participants in a thought experiment. The Alice and Bob characters were created by Ron Rivest, Adi Shamir, and Leonard Adleman in their 1978 paper "A Method for Obtaining Digital Signatures and Public-key Cryptosystems". Subsequently, they have become common archetypes in many scientific and engineering fields, such as quantum cryptography, game theory and physics. As the use of Alice and Bob became more widespread, additional characters were added, sometimes each with a particular meaning. These characters do not have to refer to people; they refer to generic agents which might be different computers or even different programs running on a single computer. Overview Alice and Bob are the names of fictional characters used for convenience and ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Decryption
In cryptography, encryption (more specifically, encoding) is the process of transforming information in a way that, ideally, only authorized parties can decode. This process converts the original representation of the information, known as plaintext, into an alternative form known as ciphertext. Despite its goal, encryption does not itself prevent interference but denies the intelligible content to a would-be interceptor. For technical reasons, an encryption scheme usually uses a pseudo-random encryption key generated by an algorithm. It is possible to decrypt the message without possessing the key but, for a well-designed encryption scheme, considerable computational resources and skills are required. An authorized recipient can easily decrypt the message with the key provided by the originator to recipients but not to unauthorized users. Historically, various forms of encryption have been used to aid in cryptography. Early encryption techniques were often used in military m ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Ciphertext
In cryptography, ciphertext or cyphertext is the result of encryption performed on plaintext using an algorithm, called a cipher. Ciphertext is also known as encrypted or encoded information because it contains a form of the original plaintext that is unreadable by a human or computer without the proper cipher to decrypt it. This process prevents the loss of sensitive information via hacking. Decryption, the inverse of encryption, is the process of turning ciphertext into readable plaintext. Ciphertext is not to be confused with codetext because the latter is a result of a code, not a cipher. Conceptual underpinnings Let m\! be the plaintext message that Alice wants to secretly transmit to Bob and let E_k\! be the encryption cipher, where _k\! is a secret key, cryptographic key. Alice must first transform the plaintext into ciphertext, c\!, in order to securely send the message to Bob, as follows: : c = E_k(m). \! In a symmetric-key system, Bob knows Alice's encryption key. ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Nonsense
Nonsense is a form of communication, via speech, writing, or any other formal logic system, that lacks any coherent meaning. In ordinary usage, nonsense is sometimes synonymous with absurdity or the ridiculous. Many poets, novelists and songwriters have used nonsense in their works, often creating entire works using it for reasons ranging from pure comic amusement or satire, to illustrating a point about language or reasoning. In the philosophy of language and philosophy of science, nonsense is distinguished from sense or meaningfulness, and attempts have been made to come up with a coherent and consistent method of distinguishing sense from nonsense. It is also an important field of study in cryptography regarding separating a signal from noise. Literary The phrase " Colorless green ideas sleep furiously" was coined by Noam Chomsky as an example of nonsense. However, this can easily be confused with poetic symbolism. The individual ''words'' make sense and are arranged ac ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |