|
Kerberized
Kerberos () is a computer-network authentication protocol that works on the basis of ''tickets'' to allow nodes communicating over a non-secure network to prove their identity to one another in a secure manner. Its designers aimed it primarily at a client–server model, and it provides mutual authentication—both the user and the server verify each other's identity. Kerberos protocol messages are protected against eavesdropping and replay attacks. Kerberos builds on symmetric-key cryptography and requires a trusted third party, and optionally may use public-key cryptography during certain phases of authentication.RFC 4556, abstract. Kerberos uses UDP port 88 by default. The protocol was named after the character '' Kerberos'' (or ''Cerberus'') from Greek mythology, the ferocious three-headed guard dog of Hades. History and development The Massachusetts Institute of Technology (MIT) developed Kerberos in 1988 to protect network services provided by Project Athena. Its first ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Massachusetts Institute Of Technology
The Massachusetts Institute of Technology (MIT) is a Private university, private research university in Cambridge, Massachusetts, United States. Established in 1861, MIT has played a significant role in the development of many areas of modern technology and science. In response to the increasing Technological and industrial history of the United States, industrialization of the United States, William Barton Rogers organized a school in Boston to create "useful knowledge." Initially funded by a land-grant universities, federal land grant, the institute adopted a Polytechnic, polytechnic model that stressed laboratory instruction in applied science and engineering. MIT moved from Boston to Cambridge in 1916 and grew rapidly through collaboration with private industry, military branches, and new federal basic research agencies, the formation of which was influenced by MIT faculty like Vannevar Bush. In the late twentieth century, MIT became a leading center for research in compu ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Cerberus
In Greek mythology, Cerberus ( or ; ''Kérberos'' ), often referred to as the hound of Hades, is a polycephaly, multi-headed dog that guards the gates of the Greek underworld, underworld to prevent the dead from leaving. He was the offspring of the monsters Echidna (mythology), Echidna and Typhon, and was usually described as having three heads, a serpent for a tail, and snakes protruding from his body. Cerberus is primarily known for his capture by Heracles, the last of Heracles' Labours of Heracles, twelve labours. Etymology The etymology of Cerberus' name is uncertain. Ogden refers to attempts to establish an Indo-European etymology as "not yet successful". It has been claimed to be related to the Sanskrit word सर्वरा ''sarvarā'', used as an epithet of one of the Sharvara and Shyama, dogs of Yama, from a Proto-Indo-European language, Proto-Indo-European word *''k̑érberos'', meaning "spotted". Lincoln (1991), among others, critiques this etymology. This ety ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
BSD Licenses
BSD licenses are a family of permissive free software licenses, imposing minimal restrictions on the use and distribution of covered software. This is in contrast to copyleft licenses, which have share-alike requirements. The original BSD license was used for its namesake, the Berkeley Software Distribution (BSD), a Unix-like operating system. The original version has since been revised, and its descendants are referred to as modified BSD licenses. BSD is both a license and a class of license (generally referred to as BSD-like). The modified BSD license (in wide use today) is very similar to the license originally used for the BSD version of Unix. The BSD license is a simple license that merely requires that all code retain the BSD license notice if redistributed in source code format, or reproduce the notice if redistributed in binary format. The BSD license (unlike some other licenses e.g. GPL) does not require that source code be distributed at all. Terms In addition to ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Generic Security Services Application Program Interface
The Generic Security Service Application Programming Interface (GSSAPI, also GSS-API) is an application programming interface for programs to access security services. The GSSAPI is an IETF standard that addresses the problem of many similar but incompatible security services in use . Operation The GSSAPI, by itself, does not provide any security. Instead, security-service vendors provide GSSAPI ''implementations'' - usually in the form of libraries installed with their security software. These libraries present a GSSAPI-compatible interface to application writers who can write their application to use only the vendor-independent GSSAPI. If the security implementation ever needs replacing, the application need not be rewritten. The definitive feature of GSSAPI applications is the exchange of opaque messages (''tokens'') which hide the implementation detail from the higher-level application. The client and server sides of the application are written to convey the tokens given t ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Advanced Encryption Standard
The Advanced Encryption Standard (AES), also known by its original name Rijndael (), is a specification for the encryption of electronic data established by the U.S. National Institute of Standards and Technology (NIST) in 2001. AES is a variant of the Rijndael block cipher developed by two Belgium, Belgian cryptographers, Joan Daemen and Vincent Rijmen, who submitted a proposal to NIST during the Advanced Encryption Standard process, AES selection process. Rijndael is a family of ciphers with different key size, key and Block size (cryptography), block sizes. For AES, NIST selected three members of the Rijndael family, each with a block size of 128 bits, but three different key lengths: 128, 192 and 256 bits. AES has been adopted by the Federal government of the United States, U.S. government. It supersedes the Data Encryption Standard (DES), which was published in 1977. The algorithm described by AES is a symmetric-key algorithm, meaning the same key is used for both encrypting ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
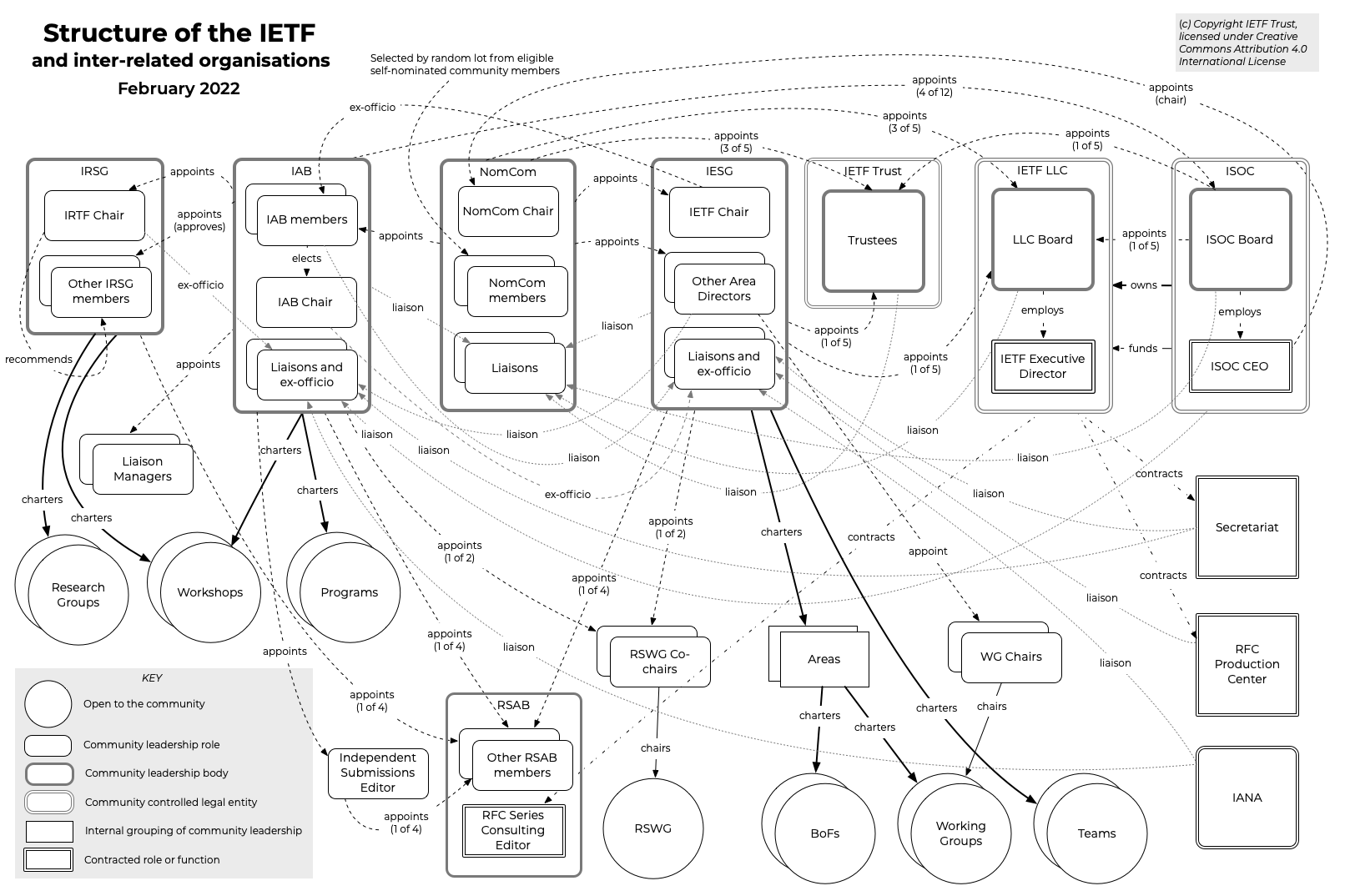
Internet Engineering Task Force
The Internet Engineering Task Force (IETF) is a standards organization for the Internet standard, Internet and is responsible for the technical standards that make up the Internet protocol suite (TCP/IP). It has no formal membership roster or requirements and all its participants are volunteers. Their work is usually funded by employers or other sponsors. The IETF was initially supported by the federal government of the United States but since 1993 has operated under the auspices of the Internet Society, a non-profit organization with local chapters around the world. Organization There is no membership in the IETF. Anyone can participate by signing up to a working group mailing list, or registering for an IETF meeting. The IETF operates in a bottom-up task creation mode, largely driven by working groups. Each working group normally has appointed two co-chairs (occasionally three); a charter that describes its focus; and what it is expected to produce, and when. It is open ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Royal Institute Of Technology
KTH Royal Institute of Technology (), abbreviated KTH, is a public research university in Stockholm, Sweden. KTH conducts research and education in engineering and technology and is Sweden's largest technical university. Since 2018, KTH consists of five schools with four campuses in and around Stockholm. KTH was established in 1827 as the ''Teknologiska institutet'' (Institute of Technology) and had its roots in the ''Mekaniska skolan'' (School of Mechanics) that was established in 1798 in Stockholm. But the origin of KTH dates back to the predecessor of the ''Mekaniska skolan'', the ''Laboratorium mechanicum'', which was established in 1697 by the Swedish scientist and innovator Christopher Polhem. The ''Laboratorium mechanicum'' combined education technology, a laboratory, and an exhibition space for innovations. In 1877, KTH received its current name, ''Kungliga Tekniska högskolan'' (KTH Royal Institute of Technology). The Swedish king, His Majesty Carl XVI Gustaf, is the pa ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Bond University
Bond University is Australia's first private university, private not-for-profit university and is located in Robina, Queensland, Robina on the Gold Coast, Queensland. Since its opening on 15 May 1989, Bond University has primarily been a teaching-focused higher education institution featuring a three-semester-per-year timetable. Bond comprises four main university schools and academic faculties, through which it offers a range of accelerated undergraduate and postgraduate degrees and programs, diplomas, and non-award programs. History Bond University was established and funded in 1987 by the chairman of Bond Corporation, Alan Bond, the president of the Japanese-based Electronics and Industrial Enterprises International (EIE), Harunori Takahashi and Dr Taro Tanioka, in a joint venture to manage the land and construction of the buildings of the university. The university's buildings and surrounding land initially covered approximately 212 hectares and encompassed what was p ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Export Of Cryptography From The United States
The export of cryptography from the United States to other countries has experienced various levels of restrictions over time. World War II illustrated that code-breaking and cryptography can play an integral part in national security and the ability to prosecute war. Changes in technology and the preservation of free speech have been competing factors in the regulation and constraint of cryptographic technologies for export. History Cold War era In the early days of the Cold War, the U.S. and its allies developed an elaborate series of export control regulations designed to prevent a wide range of Western technology from falling into the hands of others, particularly the Eastern bloc. All export of technology classed as 'critical' required a license. CoCom was organized to coordinate Western export controls. Two types of technology were protected: technology associated only with weapons of war ("munitions") and dual use technology, which also had commercial applications. In t ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Encryption Algorithm
In cryptography, encryption (more specifically, encoding) is the process of transforming information in a way that, ideally, only authorized parties can decode. This process converts the original representation of the information, known as plaintext, into an alternative form known as ciphertext. Despite its goal, encryption does not itself prevent interference but denies the intelligible content to a would-be interceptor. For technical reasons, an encryption scheme usually uses a pseudo-random encryption key generated by an algorithm. It is possible to decrypt the message without possessing the key but, for a well-designed encryption scheme, considerable computational resources and skills are required. An authorized recipient can easily decrypt the message with the key provided by the originator to recipients but not to unauthorized users. Historically, various forms of encryption have been used to aid in cryptography. Early encryption techniques were often used in military mes ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Data Encryption Standard
The Data Encryption Standard (DES ) is a symmetric-key algorithm for the encryption of digital data. Although its short key length of 56 bits makes it too insecure for modern applications, it has been highly influential in the advancement of cryptography. Developed in the early 1970s at IBM and based on an earlier design by Horst Feistel, the algorithm was submitted to the National Bureau of Standards (NBS) following the agency's invitation to propose a candidate for the protection of sensitive, unclassified electronic government data. In 1976, after consultation with the National Security Agency (NSA), the NBS selected a slightly modified version (strengthened against differential cryptanalysis, but weakened against brute-force attacks), which was published as an official Federal Information Processing Standard (FIPS) for the United States in 1977. The publication of an NSA-approved encryption standard led to its quick international adoption and widespread academic scrutiny. C ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Needham–Schroeder Protocol
The Needham–Schroeder protocol is one of the two key transport protocols intended for use over an insecure network, both proposed by Roger Needham and Michael Schroeder. These are: * The ''Needham–Schroeder Symmetric Key Protocol'', based on a Symmetric-key algorithm, symmetric encryption algorithm. It forms the basis for the Kerberos (protocol), Kerberos protocol. This protocol aims to establish a session key between two parties on a network, typically to protect further communication. * The ''Needham–Schroeder Public-Key Protocol'', based on public-key cryptography. This protocol is intended to provide mutual authentication between two parties communicating on a network, but in its proposed form is insecure. Symmetric protocol Here, Alice and Bob, Alice (A) initiates the communication to Bob . S is a server trusted by both parties. In the communication: * A and B are identities of Alice and Bob respectively * is a symmetric key known only to A and S * is a symmetric k ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |