|
Extendable-output Function
Extendable-output function (XOF) is an extension of the cryptographic hash that allows its output to be arbitrarily long. In particular, the sponge construction makes any sponge hash a natural XOF: the squeeze operation can be repeated, and the regular hash functions with a fixed-size result are obtained from a sponge mechanism by stopping the squeezing phase after obtaining the fixed number of bits). The genesis of a XOF makes it Collision resistance, collision, Preimage resistance, preimage and second preimage resistant. Technically, any XOF can be turned into a cryptographic hash by truncating the result to a fixed length (in practice, hashes and XOFs are defined differently for Domain separation (cryptography), domain separation). The examples of XOF include the algorithms from the Keccak family: SHAKE128, SHAKE256, and a variant with higher efficiency, KangarooTwelve. XOFs are used as key derivation functions (KDFs), stream ciphers, mask generation functions. Related-output ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Cryptographic Hash
A cryptographic hash function (CHF) is a hash algorithm (a map of an arbitrary binary string to a binary string with a fixed size of n bits) that has special properties desirable for a cryptographic application: * the probability of a particular n-bit output result (hash value) for a random input string ("message") is 2^ (as for any good hash), so the hash value can be used as a representative of the message; * finding an input string that matches a given hash value (a ''pre-image'') is infeasible, ''assuming all input strings are equally likely.'' The ''resistance'' to such search is quantified as security strength: a cryptographic hash with n bits of hash value is expected to have a ''preimage resistance'' strength of n bits, unless the space of possible input values is significantly smaller than 2^ (a practical example can be found in ); * a ''second preimage'' resistance strength, with the same expectations, refers to a similar problem of finding a second message that m ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
SHAKE256
SHA-3 (Secure Hash Algorithm 3) is the latest member of the Secure Hash Algorithm family of standards, released by NIST on August 5, 2015. Although part of the same series of standards, SHA-3 is internally different from the MD5-like structure of SHA-1 and SHA-2. SHA-3 is a subset of the broader cryptographic primitive family Keccak ( or ), designed by Guido Bertoni, Joan Daemen, Michaël Peeters, and Gilles Van Assche, building upon RadioGatún. Keccak's authors have proposed additional uses for the function, not (yet) standardized by NIST, including a stream cipher, an authenticated encryption system, a "tree" hashing scheme for faster hashing on certain architectures, and AEAD ciphers Keyak and Ketje. Keccak is based on a novel approach called sponge construction. Sponge construction is based on a wide random function or random permutation, and allows inputting ("absorbing" in sponge terminology) any amount of data, and outputting ("squeezing") any amount of da ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
SP 800-108
Sp or SP may refer to: Arts and entertainment * /sp/, the sports board on the Internet forum 4chan * ''SP'' (TV series), a Japanese TV series * Game Boy Advance SP, an upgraded version of the Game Boy Advance handheld video game system, released in 2003 * Standard Play, a magnetic tape speed used for VHS * Story Pirates, a podcast * Subdominant parallel, a type of musical chord * SP, producer stage name of Mumzy Stranger (born 1984), British rapper * SP, stage name of Krisztián Éder (born 1988), Hungarian rapper * ''South Park'', an animated American television series * The Smashing Pumpkins, an American alternative rock band * The SP line of digital samplers marketed by Roland Corporation under its own name and the Boss brand, most notably the Boss SP-303 (2001) and Roland SP-404 (2005) Businesses and organizations * ''SP'' (magazine), illustrated news magazine in Spain between 1957 and 1972 * SP Technical Research Institute of Sweden * ScottishPower, Scottish energy compa ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Triple DES
In cryptography, Triple DES (3DES or TDES), officially the Triple Data Encryption Algorithm (TDEA or Triple DEA), is a symmetric-key block cipher, which applies the DES cipher algorithm three times to each data block. The 56-bit key of the Data Encryption Standard (DES) is no longer considered adequate in the face of modern cryptanalytic techniques and supercomputing power; Triple DES increases the effective security to 112 bits. A CVE released in 2016, CVE-2016-2183', disclosed a major security vulnerability in the DES and 3DES encryption algorithms. This CVE, combined with the inadequate key size of 3DES, led to NIST deprecating 3DES in 2019 and disallowing all uses (except processing already encrypted data) by the end of 2023. It has been replaced with the more secure, more robust AES. While US government and industry standards abbreviate the algorithm's name as TDES (Triple DES) and TDEA (Triple Data Encryption Algorithm), RFC 1851 referred to it as 3DES from the tim ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Mask Generation Function
A mask generation function (MGF) is a cryptographic primitive similar to a cryptographic hash function except that while a hash function's output has a fixed size, a MGF supports output of a variable length. In this respect, a MGF can be viewed as a extendable-output function (XOF): it can accept input of any length and process it to produce output of any length. Mask generation functions are completely deterministic: for any given input and any desired output length the output is always the same. Definition A mask generation function takes an octet string of variable length and a desired output length as input, and outputs an octet string of the desired length. There may be restrictions on the length of the input and output octet strings, but such bounds are generally very large. Mask generation functions are deterministic; the octet string output is completely determined by the input octet string. The output of a mask generation function should be pseudorandom, that is, if th ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Stream Cipher
stream cipher is a symmetric key cipher where plaintext digits are combined with a pseudorandom cipher digit stream ( keystream). In a stream cipher, each plaintext digit is encrypted one at a time with the corresponding digit of the keystream, to give a digit of the ciphertext stream. Since encryption of each digit is dependent on the current state of the cipher, it is also known as ''state cipher''. In practice, a digit is typically a bit and the combining operation is an exclusive-or (XOR). The pseudorandom keystream is typically generated serially from a random seed value using digital shift registers. The seed value serves as the cryptographic key for decrypting the ciphertext stream. Stream ciphers represent a different approach to symmetric encryption from block ciphers. Block ciphers operate on large blocks of digits with a fixed, unvarying transformation. This distinction is not always clear-cut: in some modes of operation, a block cipher primitive is used in such ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Key Derivation Function
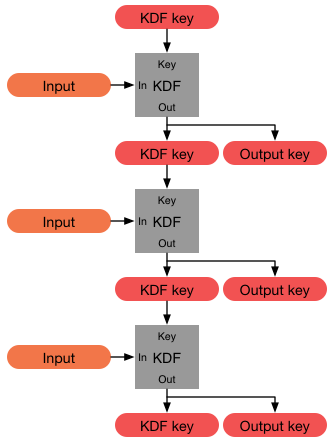
In cryptography, a key derivation function (KDF) is a cryptographic algorithm that derives one or more secret keys from a secret value such as a master key, a password, or a passphrase using a pseudorandom function (which typically uses a cryptographic hash function or block cipher). KDFs can be used to stretch keys into longer keys or to obtain keys of a required format, such as converting a group element that is the result of a Diffie–Hellman key exchange into a symmetric key for use with AES. Keyed cryptographic hash functions are popular examples of pseudorandom functions used for key derivation. History The first deliberately slow (key stretching) password-based key derivation function was called "crypt" (or "crypt(3)" after its man page), and was invented by Robert Morris in 1978. It would encrypt a constant (zero), using the first 8 characters of the user's password as the key, by performing 25 iterations of a modified DES encryption algorithm (in which a 12-b ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
KangarooTwelve
SHA-3 (Secure Hash Algorithm 3) is the latest member of the Secure Hash Algorithm family of standards, released by NIST on August 5, 2015. Although part of the same series of standards, SHA-3 is internally different from the MD5-like structure of SHA-1 and SHA-2. SHA-3 is a subset of the broader cryptographic primitive family Keccak ( or ), designed by Guido Bertoni, Joan Daemen, Michaël Peeters, and Gilles Van Assche, building upon RadioGatún. Keccak's authors have proposed additional uses for the function, not (yet) standardized by NIST, including a stream cipher, an authenticated encryption system, a "tree" hashing scheme for faster hashing on certain architectures, and AEAD ciphers Keyak and Ketje. Keccak is based on a novel approach called sponge construction. Sponge construction is based on a wide random function or random permutation, and allows inputting ("absorbing" in sponge terminology) any amount of data, and outputting ("squeezing") any amount of data, w ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Sponge Construction
Sponges or sea sponges are primarily marine invertebrates of the animal phylum Porifera (; meaning 'pore bearer'), a basal clade and a sister taxon of the diploblasts. They are sessile filter feeders that are bound to the seabed, and are one of the most ancient members of macrobenthos, with many historical species being important reef-building organisms. Sponges are multicellular organisms consisting of jelly-like mesohyl sandwiched between two thin layers of cells, and usually have tube-like bodies full of pores and channels that allow water to circulate through them. They have unspecialized cells that can transform into other types and that often migrate between the main cell layers and the mesohyl in the process. They do not have complex nervous, digestive or circulatory systems. Instead, most rely on maintaining a constant water flow through their bodies to obtain food and oxygen and to remove wastes, usually via flagella movements of the so-called "collar cells". S ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Keccak
SHA-3 (Secure Hash Algorithm 3) is the latest member of the Secure Hash Algorithm family of standards, released by NIST on August 5, 2015. Although part of the same series of standards, SHA-3 is internally different from the MD5-like structure of SHA-1 and SHA-2. SHA-3 is a subset of the broader cryptographic primitive family Keccak ( or ), designed by Guido Bertoni, Joan Daemen, Michaël Peeters, and Gilles Van Assche, building upon RadioGatún. Keccak's authors have proposed additional uses for the function, not (yet) standardized by NIST, including a stream cipher, an authenticated encryption system, a "tree" hashing scheme for faster hashing on certain architectures, and AEAD ciphers Keyak and Ketje. Keccak is based on a novel approach called sponge construction. Sponge construction is based on a wide random function or random permutation, and allows inputting ("absorbing" in sponge terminology) any amount of data, and outputting ("squeezing") any amount of data, ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Domain Separation (cryptography)
In cryptography, domain separation is a construct used to implement multiple different functions using only one underlying template in an efficient way. The domain separation can be defined as partitioning of the domain of a function to assign separate subdomains to different applications of the same function. For example, cryptographic protocols typically rely on random oracles (ROs, functions that return a value fully determined by their input yet otherwise random). The security proofs for these protocols are based on the assumption that the random oracle is unique to the protocol: if two protocols share the same RO, the assumptions of the proof are not met anymore. Since creating a new cryptographic primitive from scratch each time an RO is needed is impractical, multiple ROs (say, RO1 and RO2) are produced by prepending unique domain separation tags (DSTs, also known as ''domain separators'') to the input of a base oracle RO: :RO1(x) := RO("RO1" , , x) :RO2(x) := RO("RO2" , , ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |