|
Aircrack
Aircrack-ng is a network software suite consisting of a detector, packet sniffer, WEP and WPA/WPA2-PSK cracker and analysis tool for 802.11 wireless LANs. It works with any wireless network interface controller whose driver supports raw monitoring mode and can sniff 802.11a, 802.11b and 802.11g traffic. The program runs under Linux, FreeBSD, macOS, OpenBSD, and Windows; the Linux version is packaged for OpenWrt and has also been ported to the Android, Zaurus PDA and Maemo platforms; and a proof of concept port has been made to the iPhone. In April 2007 a team at the Darmstadt University of Technology in Germany developed a new attack method based on a paper released on the RC4 cipher by Adi Shamir. This new attack, named 'PTW', decreases the number of initialization vectors or IVs needed to decrypt a WEP key and has been included in the aircrack-ng suite since the 0.9 release. Aircrack-ng is a fork of the original Aircrack project. It can be found as a preinstalled tool i ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Wi-Fi Protected Access
Wi-Fi Protected Access (WPA), Wi-Fi Protected Access II (WPA2), and Wi-Fi Protected Access 3 (WPA3) are the three security and security certification programs developed after 2000 by the Wi-Fi Alliance to secure wireless computer networks. The Alliance defined these in response to serious weaknesses researchers had found in the previous system, Wired Equivalent Privacy (WEP). WPA (sometimes referred to TKIP standard) became available in 2003. The Wi-Fi Alliance intended it as an intermediate measure in anticipation of the availability of the more secure and complex WPA2, which became available in 2004 and is a common shorthand for the full IEEE 802.11i (or IEEE 802.11i-2004) standard. In January 2018, Wi-Fi Alliance announced the release of WPA3 with several security improvements over WPA2. Versions WPA The Wi-Fi Alliance intended WPA as an intermediate measure to take the place of WEP pending the availability of the full IEEE 802.11i standard. WPA could be implemented throug ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
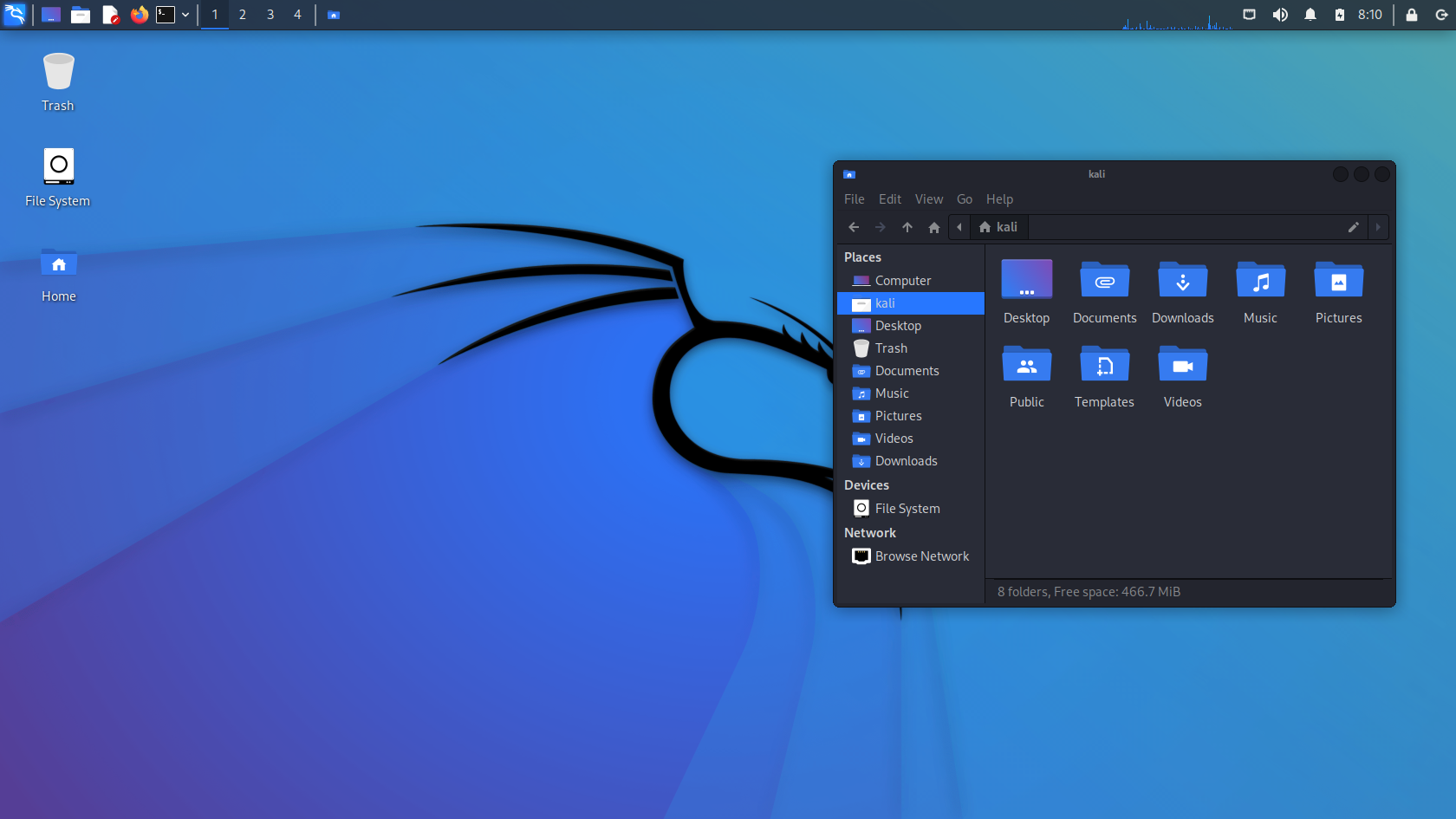
Kali Linux
Kali Linux is a Debian-derived Linux distribution designed for digital forensics and penetration testing. It is maintained and funded by Offensive Security. Kali Linux has around 600 penetration-testing programs (tools), including Armitage (a graphical cyber attack management tool), Nmap (a port scanner), Wireshark (a packet analyzer), metasploit (penetration testing framework), John the Ripper (a password cracker), sqlmap (automatic SQL injection and database takeover tool), Aircrack-ng (a software suite for penetration-testing wireless LANs), Burp suite and OWASP ZAP web application security scanners, etc. It was developed by Mati Aharoni and Devon Kearns of Offensive Security through the rewrite of BackTrack, their previous information security testing Linux distribution based on Knoppix. The name was inspired by the Hindu goddess Kali. Kali Linux is based on the Debian ''Testing'' branch. Most packages Kali uses are imported from the Debian repositories. Kali Linux's po ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Cracking Of Wireless Networks
Wireless security is the prevention of unauthorized access or damage to computers or data using wireless networks, which include Wi-Fi networks. The term may also refer to the protection of the wireless network itself from adversaries seeking to damage the confidentiality, integrity, or availability of the network. The most common type is Wi-Fi security, which includes Wired Equivalent Privacy (WEP) and Wi-Fi Protected Access (WPA). WEP is an old IEEE 802.11 standard from 1997. It is a notoriously weak security standard: the password it uses can often be cracked in a few minutes with a basic laptop computer and widely available software tools. WEP was superseded in 2003 by WPA, a quick alternative at the time to improve security over WEP. The current standard is WPA2; some hardware cannot support WPA2 without firmware upgrade or replacement. WPA2 uses an encryption device that encrypts the network with a 256-bit key; the longer key length improves security over WEP. Enterprises of ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Wired Equivalent Privacy
Wired Equivalent Privacy (WEP) was a security algorithm for 802.11 wireless networks. Introduced as part of the original IEEE 802.11 standard ratified in 1997, its intention was to provide data confidentiality comparable to that of a traditional wired network. WEP, recognizable by its key of 10 or 26 hexadecimal digits (40 or 104 bits), was at one time widely used, and was often the first security choice presented to users by router configuration tools. In 2003, the Wi-Fi Alliance announced that WEP had been superseded by Wi-Fi Protected Access (WPA). In 2004, with the ratification of the full 802.11i standard (i.e. WPA2), the IEEE declared that both WEP-40 and WEP-104 have been deprecated. WEP was the only encryption protocol available to 802.11a and 802.11b devices built before the WPA standard, which was available for 802.11g devices. However, some 802.11b devices were later provided with firmware or software updates to enable WPA, and newer devices had it built in. Hi ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
OpenWrt
OpenWrt (from ''open wireless router'') is an open-source project for embedded operating systems based on Linux, primarily used on embedded devices to route network traffic. The main components are Linux, util-linux, musl, and BusyBox. All components have been optimized to be small enough to fit into the limited storage and memory available in home routers. OpenWrt is configured using a command-line interface (ash shell) or a web interface (LuCI). There are about 8000 optional software packages available for installation via the opkg package management system. OpenWrt can run on various types of devices, including CPE routers, residential gateways, smartphones, pocket computers (e.g. Ben NanoNote). It is also possible to run OpenWrt on personal computers and laptops. History The OpenWrt project was started in 2004 after Linksys had built the firmware for their WRT54G series of wireless routers with code licensed under the GNU General Public License. Under the terms ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Parrot Security OS
Parrot OS is a Linux distribution based on Debian with a focus on security, privacy, and development. Core Parrot is based on Debian's "testing" branch, with a Linux 5.10 kernel. It follows a rolling release development model. The desktop environments is MATE, and the default display manager is LightDM. The system is certified to run on devices which have a minimum of 256MB of RAM, and it is suitable for both 32-bit (i386) and 64-bit (amd64) processor architectures. Moreover, the project is available for ARMv7 (armhf) architectures. In June 2017, the Parrot Team announced they were considering to change from Debian to Devuan, mainly because of problems with systemd. As of January 21st, 2019, the Parrot team has begun to phase out the development of their 32-bit (i386) ISO. In August 2020, the Parrot OS officially supports Lightweight Xfce Desktop. Editions Parrot has multiple editions that are based upon Debian, with various desktop environments available. Parro ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Fork (software Development)
In software engineering, a project fork happens when developers take a copy of source code from one software package and start independent development on it, creating a distinct and separate piece of software. The term often implies not merely a development branch, but also a split in the developer community; as such, it is a form of schism. Grounds for forking are varying user preferences and stagnated or discontinued development of the original software. Free and open-source software is that which, by definition, may be forked from the original development team without prior permission, and without violating copyright law. However, licensed forks of proprietary software (''e.g.'' Unix) also happen. Etymology The word "fork" has been used to mean "to divide in branches, go separate ways" as early as the 14th century. In the software environment, the word evokes the fork system call, which causes a running process to split itself into two (almost) identical copies that ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Initialization Vector
In cryptography, an initialization vector (IV) or starting variable (SV) is an input to a cryptographic primitive being used to provide the initial state. The IV is typically required to be random or pseudorandom, but sometimes an IV only needs to be unpredictable or unique. Randomization is crucial for some encryption schemes to achieve semantic security, a property whereby repeated usage of the scheme under the same key does not allow an attacker to infer relationships between (potentially similar) segments of the encrypted message. For block ciphers, the use of an IV is described by the modes of operation. Some cryptographic primitives require the IV only to be non-repeating, and the required randomness is derived internally. In this case, the IV is commonly called a nonce (a number used only once), and the primitives (e.g. CBC) are considered ''stateful'' rather than ''randomized''. This is because an IV need not be explicitly forwarded to a recipient but may be derived from ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Adi Shamir
Adi Shamir ( he, עדי שמיר; born July 6, 1952) is an Israeli cryptographer. He is a co-inventor of the Rivest–Shamir–Adleman (RSA) algorithm (along with Ron Rivest and Len Adleman), a co-inventor of the Feige–Fiat–Shamir identification scheme (along with Uriel Feige and Amos Fiat), one of the inventors of differential cryptanalysis and has made numerous contributions to the fields of cryptography and computer science. Education Born in Tel Aviv, Shamir received a Bachelor of Science (BSc) degree in mathematics from Tel Aviv University in 1973 and obtained his Master of Science (MSc) and Doctor of Philosophy (PhD) degrees in Computer Science from the Weizmann Institute in 1975 and 1977 respectively. Career and research After a year as a postdoctoral researcher at the University of Warwick, he did research at Massachusetts Institute of Technology (MIT) from 1977 to 1980 before returning to be a member of the faculty of Mathematics and Computer Science at the Weizma ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Germany
Germany,, officially the Federal Republic of Germany, is a country in Central Europe. It is the second most populous country in Europe after Russia, and the most populous member state of the European Union. Germany is situated between the Baltic and North seas to the north, and the Alps to the south; it covers an area of , with a population of almost 84 million within its 16 constituent states. Germany borders Denmark to the north, Poland and the Czech Republic to the east, Austria and Switzerland to the south, and France, Luxembourg, Belgium, and the Netherlands to the west. The nation's capital and most populous city is Berlin and its financial centre is Frankfurt; the largest urban area is the Ruhr. Various Germanic tribes have inhabited the northern parts of modern Germany since classical antiquity. A region named Germania was documented before AD 100. In 962, the Kingdom of Germany formed the bulk of the Holy Roman Empire. During the 16th ce ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Technische Universität Darmstadt
The Technische Universität Darmstadt (official English name Technical University of Darmstadt, sometimes also referred to as Darmstadt University of Technology), commonly known as TU Darmstadt, is a research university in the city of Darmstadt, Germany. It was founded in 1877 and received the right to award doctorates in 1899. In 1882, it was the first university in the world to set up a chair in electrical engineering. In 1883, the university founded the first faculty of electrical engineering and introduced the world's first degree course in electrical engineering.History of the department of Electrical Engineering: (German) In 2004, it became the first German university to be declared as an autonomous university. TU Darmstadt has assumed a pioneering role in Germany. Computer science, electrical engineering, artificial intelligence, mechatronics, business informatics, political science and many more courses were introduced as scientific disciplines in Germany by Darmstadt ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
.jpg)
.jpg)