|
X-Originating-IP
The X-Originating-IP (not to be confused with X-Forwarded-For) email header field is a de facto standard for identifying the originating IP address of a client connecting to a mail service's HTTP frontend. When clients connect directly to a mail server, its address is already known to the server, but web frontends act as a proxy which internally connect to the mail server. This header can therefore serve to identify the original sender address despite the frontend. Format The general format of the field is: X-Originating-IP: 98.51.100.1/code> Origins In 1999 Hotmail included an ''X-Originating-IP'' email header field that shows the IP address of the sender. As of December 2012, Hotmail removed this header field, replacing it with X-EIP (meaning encoded IP) with the stated goal of protecting users' privacy. See also * Internet privacy Internet privacy involves the right or mandate of personal privacy concerning the storing, re-purposing, provision to third parties, an ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
X-Forwarded-For
The X-Forwarded-For (XFF) HTTP header field is a common method for identifying the originating IP address of a client connecting to a web server through an HTTP proxy or load balancer. The X-Forwarded-For HTTP request header was introduced by the Squid caching proxy server's developers. X-Forwarded-For is also an email-header indicating that an email-message was forwarded from one or more other accounts (probably automatically). Without the use of XFF or another similar technique, any connection through the proxy would reveal only the originating IP address of the proxy server, effectively turning the proxy server into an anonymizing service, thus making the detection and prevention of abusive accesses significantly harder than if the originating IP address were available. The usefulness of XFF depends on the proxy server truthfully reporting the original host's IP address; for this reason, effective use of XFF requires knowledge of which proxies are trustworthy, for insta ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Email Header Fields
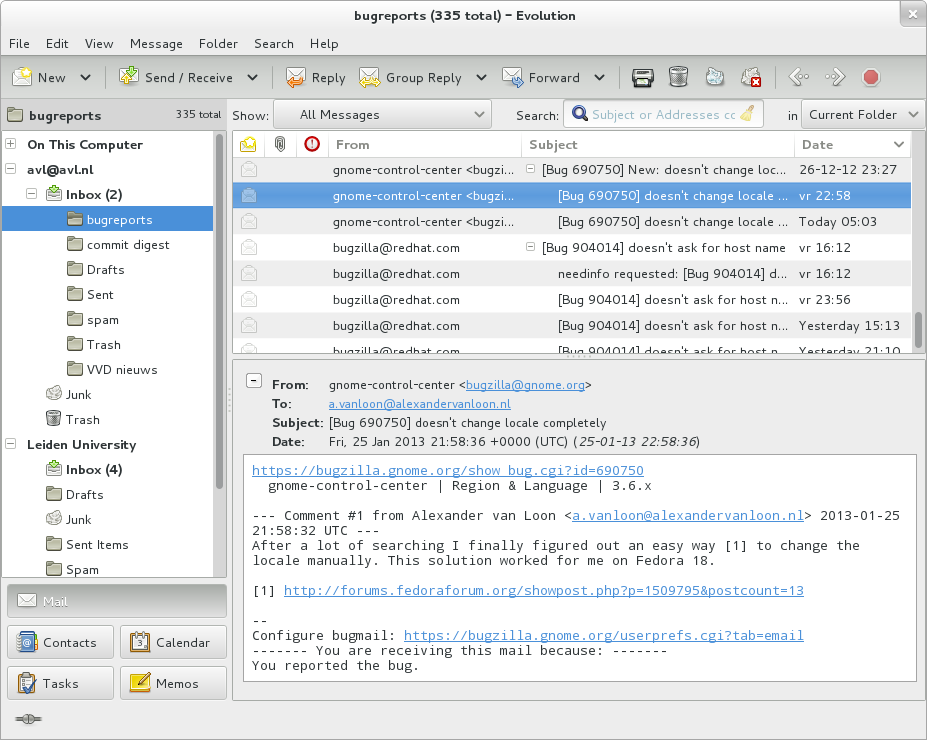
Electronic mail (email or e-mail) is a method of exchanging messages ("mail") between people using electronic devices. Email was thus conceived as the electronic (digital) version of, or counterpart to, mail, at a time when "mail" meant only physical mail (hence '' e- + mail''). Email later became a ubiquitous (very widely used) communication medium, to the point that in current use, an email address is often treated as a basic and necessary part of many processes in business, commerce, government, education, entertainment, and other spheres of daily life in most countries. ''Email'' is the medium, and each message sent therewith is also called an ''email.'' The term is a mass noun. Email operates across computer networks, primarily the Internet, and also local area networks. Today's email systems are based on a store-and-forward model. Email servers accept, forward, deliver, and store messages. Neither the users nor their computers are required to be online simult ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Email
Electronic mail (email or e-mail) is a method of exchanging messages ("mail") between people using electronic devices. Email was thus conceived as the electronic ( digital) version of, or counterpart to, mail, at a time when "mail" meant only physical mail (hence '' e- + mail''). Email later became a ubiquitous (very widely used) communication medium, to the point that in current use, an email address is often treated as a basic and necessary part of many processes in business, commerce, government, education, entertainment, and other spheres of daily life in most countries. ''Email'' is the medium, and each message sent therewith is also called an ''email.'' The term is a mass noun. Email operates across computer networks, primarily the Internet, and also local area networks. Today's email systems are based on a store-and-forward model. Email servers accept, forward, deliver, and store messages. Neither the users nor their computers are required to be online simu ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
De Facto
''De facto'' ( ; , "in fact") describes practices that exist in reality, whether or not they are officially recognized by laws or other formal norms. It is commonly used to refer to what happens in practice, in contrast with '' de jure'' ("by law"), which refers to things that happen according to official law, regardless of whether the practice exists in reality. History In jurisprudence, it mainly means "practiced, but not necessarily defined by law" or "practiced or is valid, but not officially established". Basically, this expression is opposed to the concept of "de jure" (which means "as defined by law") when it comes to law, management or technology (such as standards) in the case of creation, development or application of "without" or "against" instructions, but in accordance with "with practice". When legal situations are discussed, "de jure" means "expressed by law", while "de facto" means action or what is practiced. Similar expressions: "essentially", "unofficial", " ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
IP Address
An Internet Protocol address (IP address) is a numerical label such as that is connected to a computer network that uses the Internet Protocol for communication.. Updated by . An IP address serves two main functions: network interface identification and location addressing. Internet Protocol version 4 (IPv4) defines an IP address as a 32-bit number. However, because of the growth of the Internet and the depletion of available IPv4 addresses, a new version of IP (IPv6), using 128 bits for the IP address, was standardized in 1998. IPv6 deployment has been ongoing since the mid-2000s. IP addresses are written and displayed in human-readable notations, such as in IPv4, and in IPv6. The size of the routing prefix of the address is designated in CIDR notation by suffixing the address with the number of significant bits, e.g., , which is equivalent to the historically used subnet mask . The IP address space is managed globally by the Internet Assigned Numbers Authority ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Mail Server
Within the Internet email system, a message transfer agent (MTA), or mail transfer agent, or mail relay is software Software is a set of computer programs and associated software documentation, documentation and data (computing), data. This is in contrast to Computer hardware, hardware, from which the system is built and which actually performs the work. ... that transfers electronic mail messages from one computer to another using SMTP. The terms mail server, mail exchanger, and MX host are also used in some contexts. Messages exchanged across networks are passed between mail servers, including any attached data files (such as images, multimedia or documents). These servers also often keep mailboxes for email. Access to this email by end users is typically either via webmail or an email client. Operation A message transfer agent receives mail from either another MTA, a mail submission agent (MSA), or a mail user agent (MUA). The transmission details are specified ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Hotmail
Outlook.com is a webmail service that is part of the Microsoft 365 product family. It offers mail, calendaring, contacts, and tasks services. Founded in 1996 by Sabeer Bhatia and Jack Smith as Hotmail, it was acquired by Microsoft in 1997 for an estimated $400 million and relaunched as ''MSN Hotmail'', later rebranded to ''Windows Live Hotmail'' as part of the Windows Live suite of products. Microsoft phased out Hotmail in October 2011, relaunching the service as Outlook.com in 2012. History Launch of Hotmail Hotmail service was founded by Sabeer Bhatia and Jack Smith, and was one of the first webmail services on the Internet along with Four11's RocketMail (later Yahoo! Mail). It was commercially launched on July 4, 1996, symbolizing "freedom" from ISP-based email and the ability to access a user's inbox from anywhere in the world. The name "Hotmail" was chosen out of many possibilities ending in "-mail" as it included the letters HTML, the markup language used to ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Internet Privacy
Internet privacy involves the right or mandate of personal privacy concerning the storing, re-purposing, provision to third parties, and displaying of information pertaining to oneself via Internet. Internet privacy is a subset of data privacy. Privacy concerns have been articulated from the beginnings of large-scale computer sharing. Privacy can entail either personally identifiable information (PII) or non-PII information such as a site visitor's behavior on a website. PII refers to any information that can be used to identify an individual. For example, age and physical address alone could identify who an individual is without explicitly disclosing their name, as these two factors are unique enough to identify a specific person typically. Other forms of PII may soon include GPS tracking data used by apps, as the daily commute and routine information can be enough to identify an individual. It has been suggested that the "appeal of online services is to broadcast personal inf ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Proxy Server
In computer networking, a proxy server is a server application that acts as an intermediary between a client requesting a resource and the server providing that resource. Instead of connecting directly to a server that can fulfill a request for a resource, such as a file or web page, the client directs the request to the proxy server, which evaluates the request and performs the required network transactions. This serves as a method to simplify or control the complexity of the request, or provide additional benefits such as load balancing, privacy, or security. Proxies were devised to add structure and encapsulation to distributed systems. A proxy server thus functions on behalf of the client when requesting service, potentially masking the true origin of the request to the resource server. Types A proxy server may reside on the user's local computer, or at any point between the user's computer and destination servers on the Internet. A proxy server that passes unmodifi ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Anonymity
Anonymity describes situations where the acting person's identity is unknown. Some writers have argued that namelessness, though technically correct, does not capture what is more centrally at stake in contexts of anonymity. The important idea here is that a person be non-identifiable, unreachable, or untrackable. Anonymity is seen as a technique, or a way of realizing, a certain other values, such as privacy, or liberty. Over the past few years, anonymity tools used on the dark web by criminals and malicious users have drastically altered the ability of law enforcement to use conventional surveillance techniques. An important example for anonymity being not only protected, but enforced by law is the vote in free elections. In many other situations (like conversation between strangers, buying some product or service in a shop), anonymity is traditionally accepted as natural. There are also various situations in which a person might choose to withhold their identity. Acts of char ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |


.jpg)