|
Passkeys (authentication)
Web Authentication (WebAuthn) is a web standard published by the World Wide Web Consortium (W3C). Its primary purpose is to build a system of authentication for web-based applications that solves or mitigates the issues of traditional password-based authentication. Zero-knowledge proofs based on public-key signature schemes are used to register and authenticate users without the need to transmit or store private authenticating information (such as passwords) on servers. Passwords are replaced by the so-called WebAuthn Credentials which are generated client-side and stored in so-called Authenticators. WebAuthn supports both roaming authenticators (such as physical security keys) and platform authenticators (such as smartphones). While different types of credentials are supported, synced discoverable credentials (also known as Passkeys) are the most common ones. WebAuthn is a core component of the FIDO2 Project under the guidance of the FIDO Alliance. On the client side, aut ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
FIDO2 Project
The FIDO ("Fast IDentity Online") Alliance is an open industry association launched in February 2013 whose stated mission is to develop and promote authentication standards that "help reduce the world’s over-reliance on passwords". FIDO addresses the lack of interoperability among devices that use strong authentication and reduces the problems users face creating and remembering multiple usernames and passwords. FIDO supports a full range of authentication technologies, including biometrics such as fingerprint and iris scanners, voice and facial recognition, as well as existing solutions and communications standards, such as Trusted Platform Modules (TPM), USB security tokens, embedded Secure Elements (eSE), smart cards, and near-field communication (NFC). The USB security token device may be used to authenticate using a simple password (e.g. four-digit PIN) or by pressing a button. The specifications emphasize a device-centric model. Authentication over an insecure channel ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Ars Technica
''Ars Technica'' is a website covering news and opinions in technology, science, politics, and society, created by Ken Fisher and Jon Stokes in 1998. It publishes news, reviews, and guides on issues such as computer hardware and software, science, technology policy, and video games. ''Ars Technica'' was privately owned until May 2008, when it was sold to Condé Nast Digital, the online division of Condé Nast Publications. Condé Nast purchased the site, along with two others, for $25 million and added it to the company's ''Wired'' Digital group, which also includes '' Wired'' and, formerly, Reddit. The staff mostly works from home and has offices in Boston, Chicago, London, New York City, and San Francisco. The operations of ''Ars Technica'' are funded primarily by advertising, and it has offered a paid subscription service since 2001. History Ken Fisher, who serves as the website's current editor-in-chief, and Jon Stokes created ''Ars Technica'' in 1998. Its purpose was t ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
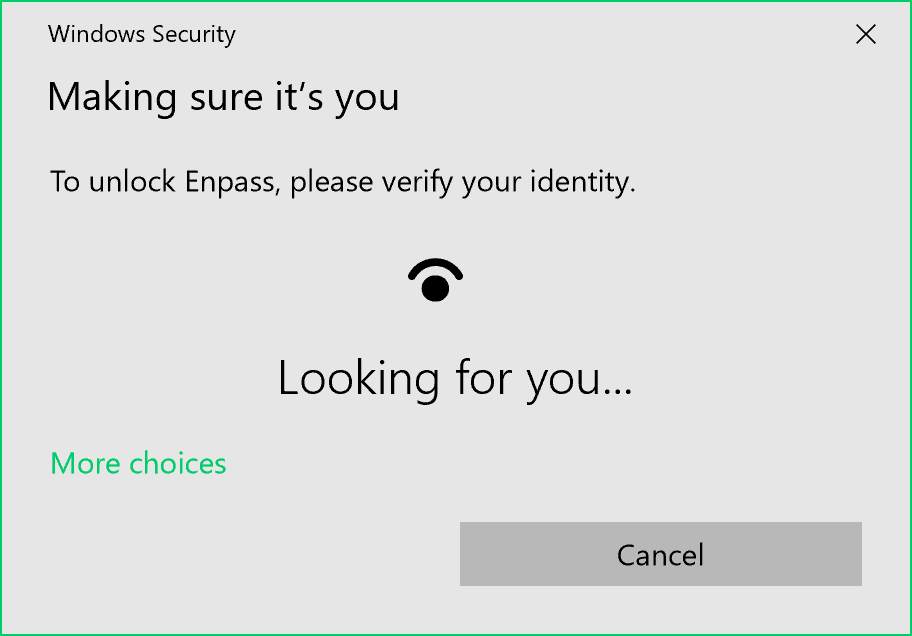
Windows Hello
Windows 10 is a major release of Microsoft's Windows NT operating system. The successor to Windows 8.1, it was released to manufacturing on July 15, 2015, and later to retail on July 29, 2015. Windows 10 was made available for download via MSDN and TechNet, as a free upgrade for retail copies of Windows 8 and Windows 8.1 users via the Microsoft Store, and to Windows 7 users via Windows Update. Unlike previous Windows NT releases, Windows 10 receives new builds on an ongoing basis, which are available at no additional cost to users; devices in enterprise environments can alternatively use long-term support milestones that only receive critical updates, such as security patches. It was succeeded by Windows 11, which was released on October 5, 2021. In contrast to the tablet-oriented approach of Windows 8, Microsoft provided the desktop-oriented interface in line with previous versions of Windows in Windows 10. Other features added include Xbox Live integration, Cortan ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
JavaScript
JavaScript (), often abbreviated as JS, is a programming language and core technology of the World Wide Web, alongside HTML and CSS. Ninety-nine percent of websites use JavaScript on the client side for webpage behavior. Web browsers have a dedicated JavaScript engine that executes the client code. These engines are also utilized in some servers and a variety of apps. The most popular runtime system for non-browser usage is Node.js. JavaScript is a high-level, often just-in-time–compiled language that conforms to the ECMAScript standard. It has dynamic typing, prototype-based object-orientation, and first-class functions. It is multi-paradigm, supporting event-driven, functional, and imperative programming styles. It has application programming interfaces (APIs) for working with text, dates, regular expressions, standard data structures, and the Document Object Model (DOM). The ECMAScript standard does not include any input/output (I/O), such as netwo ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Mozilla
Mozilla is a free software community founded in 1998 by members of Netscape. The Mozilla community uses, develops, publishes and supports Mozilla products, thereby promoting free software and open standards. The community is supported institutionally by the Nonprofit organization, non-profit Mozilla Foundation and its tax-paying subsidiary, the Mozilla Corporation. List of Mozilla products, Mozilla's current products include the Firefox web browser, Mozilla Thunderbird, Thunderbird e-mail client (now through a subsidiary), the Bugzilla bug tracking system, the Gecko (software), Gecko layout engine, and the Pocket (service), Pocket "read-it-later-online" service. History On January 23, 1998, Netscape announced that its Netscape Communicator browser software would be free, and that its source code would also be free. One day later, Jamie Zawinski of Netscape registered . The project took its name, "Mozilla", from the original code name of the Netscape Navigator browser—a por ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Cryptography
Cryptography, or cryptology (from "hidden, secret"; and ''graphein'', "to write", or ''-logy, -logia'', "study", respectively), is the practice and study of techniques for secure communication in the presence of Adversary (cryptography), adversarial behavior. More generally, cryptography is about constructing and analyzing Communication protocol, protocols that prevent third parties or the public from reading private messages. Modern cryptography exists at the intersection of the disciplines of mathematics, computer science, information security, electrical engineering, digital signal processing, physics, and others. Core concepts related to information security (confidentiality, data confidentiality, data integrity, authentication, and non-repudiation) are also central to cryptography. Practical applications of cryptography include electronic commerce, Smart card#EMV, chip-based payment cards, digital currencies, password, computer passwords, and military communications. ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Passwordless Web Authentication
Passwordless authentication is an authentication method in which a user can log in to a computer system without entering (and having to remember) a password or any other knowledge-based secret. In most common implementations users are asked to enter their public identifier (username, phone number, email address etc.) and then complete the authentication process by providing a secure proof of identity through a registered device or token. Passwordless authentication methods typically rely on public-key cryptography infrastructure where the public key is provided during registration to the authenticating service (remote server, application or website) while the private key is kept on a user’s device ( PC, smartphone or an external security token) and can be accessed only by providing a biometric signature or another authentication factor which is not knowledge-based. These factors classically fall into two categories: * Ownership factors (“Something the user has”) such as ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Web Browser
A web browser, often shortened to browser, is an application for accessing websites. When a user requests a web page from a particular website, the browser retrieves its files from a web server and then displays the page on the user's screen. Browsers can also display content stored locally on the user's device. Browsers are used on a range of devices, including desktops, laptops, tablets, smartphones, smartwatches and consoles. As of 2024, the most used browsers worldwide are Google Chrome (~66% market share), Safari (~16%), Edge (~6%), Firefox (~3%), Samsung Internet (~2%), and Opera (~2%). As of 2023, an estimated 5.4 billion people had used a browser. Function The purpose of a web browser is to fetch content and display it on the user's device. This process begins when the user inputs a Uniform Resource Locator (URL), such as ''https://en.wikipedia.org/'', into the browser's address bar. Virtually all URLs on the Web start with either ''http:'' or ''h ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Website
A website (also written as a web site) is any web page whose content is identified by a common domain name and is published on at least one web server. Websites are typically dedicated to a particular topic or purpose, such as news, education, commerce, entertainment, or social media. Hyperlinking between web pages guides the navigation of the site, which often starts with a home page. The most-visited sites are Google, YouTube, and Facebook. All publicly-accessible websites collectively constitute the World Wide Web. There are also private websites that can only be accessed on a private network, such as a company's internal website for its employees. Users can access websites on a range of devices, including desktops, laptops, tablets, and smartphones. The app used on these devices is called a web browser. Background The World Wide Web (WWW) was created in 1989 by the British CERN computer scientist Tim Berners-Lee. On 30 April 1993, CERN announced that the ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Smartphone
A smartphone is a mobile phone with advanced computing capabilities. It typically has a touchscreen interface, allowing users to access a wide range of applications and services, such as web browsing, email, and social media, as well as multimedia playback and Streaming media, streaming. Smartphones have built-in cameras, GPS navigation, and support for various communication methods, including voice calls, text messaging, and internet-based messaging apps. Smartphones are distinguished from older-design feature phones by their more advanced hardware capabilities and extensive mobile operating systems, access to the internet, business applications, Mobile payment, mobile payments, and multimedia functionality, including music, video, mobile gaming, gaming, Internet radio, radio, and Mobile television, television. Smartphones typically feature MOSFET, metal–oxide–semiconductor (MOS) integrated circuit (IC) chips, various sensors, and support for multiple wireless communicati ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Public-key Cryptography
Public-key cryptography, or asymmetric cryptography, is the field of cryptographic systems that use pairs of related keys. Each key pair consists of a public key and a corresponding private key. Key pairs are generated with cryptographic algorithms based on mathematical problems termed one-way functions. Security of public-key cryptography depends on keeping the private key secret; the public key can be openly distributed without compromising security. There are many kinds of public-key cryptosystems, with different security goals, including digital signature, Diffie–Hellman key exchange, Key encapsulation mechanism, public-key key encapsulation, and public-key encryption. Public key algorithms are fundamental security primitives in modern cryptosystems, including applications and protocols that offer assurance of the confidentiality and authenticity of electronic communications and data storage. They underpin numerous Internet standards, such as Transport Layer Security, T ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Biometrics
Biometrics are body measurements and calculations related to human characteristics and features. Biometric authentication (or realistic authentication) is used in computer science as a form of identification and access control. It is also used to identify individuals in groups that are under surveillance. Biometric identifiers are the distinctive, measurable characteristics used to label and describe individuals. Biometric identifiers are often categorized as physiological characteristics which are related to the shape of the body. Examples include, but are not limited to fingerprint, palm veins, face recognition, DNA, palm print, hand geometry, iris recognition, retina, odor/scent, voice, shape of ears and gait. Behavioral characteristics are related to the pattern of behavior of a person, including but not limited to mouse movement, typing rhythm, gait, signature, voice, and behavioral profiling. Some researchers have coined the term behaviometrics (behavioral biom ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |