|
Hardware Obfuscation
Hardware obfuscation is a technique by which the description or the structure of electronic hardware is modified to intentionally conceal its functionality, which makes it significantly more difficult to reverse-engineer. In other words, hardware obfuscation modifies the design in such a away that the resulting architecture becomes un-obvious to an adversary. Hardware Obfuscation can be of two types depending on the hardware platform targeted: (a) DSP Core Hardware Obfuscation - this type of obfuscation performs certain high level transformation on the data flow graph representation of DSP core to convert it into an unknown form that reflects an un-obvious architecture at RTL or gate level. This type of obfuscation is also called 'Structural Obfuscation'. Another type of DSP Core Obfuscation method is called 'Functional Obfuscation' - It uses a combination of AES and IP core locking blocks (ILBs) to lock the functionality of the DSP core using key-bits. Without application of corre ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Obfuscation
Obfuscation is the obscuring of the intended meaning of communication by making the message difficult to understand, usually with confusing and ambiguous language. The obfuscation might be either unintentional or intentional (although intent usually is connoted), and is accomplished with circumlocution (talking around the subject), the use of jargon (technical language of a profession), and the use of an argot ( ingroup language) of limited communicative value to outsiders. In expository writing, unintentional obfuscation usually occurs in draft documents, at the beginning of composition; such obfuscation is illuminated with critical thinking and editorial revision, either by the writer or by an editor. Etymologically, the word ''obfuscation'' derives from the Latin , from ''obfuscāre'' (to darken); synonyms include the words beclouding and abstrusity. Medical Doctors are faulted for using jargon to conceal unpleasant facts from a patient; the American author and phys ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Failure
Failure is the state or condition of not meeting a desirable or intended objective, and may be viewed as the opposite of success. The criteria for failure depends on context, and may be relative to a particular observer or belief system. One person might consider a failure what another person considers a success, particularly in cases of direct competition or a zero-sum game. Similarly, the degree of success or failure in a situation may be differently viewed by distinct observers or participants, such that a situation that one considers to be a failure, another might consider to be a success, a qualified success or a neutral situation. It may also be difficult or impossible to ascertain whether a situation meets criteria for failure or success due to ambiguous or ill-defined definition of those criteria. Finding useful and effective criteria, or heuristics, to judge the success or failure of a situation may itself be a significant task. In American history Cultural hist ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Mainframe Computer
A mainframe computer, informally called a mainframe or big iron, is a computer used primarily by large organizations for critical applications like bulk data processing for tasks such as censuses, industry and consumer statistics, enterprise resource planning, and large-scale transaction processing. A mainframe computer is large but not as large as a supercomputer and has more processing power than some other classes of computers, such as minicomputers, servers, workstations, and personal computers. Most large-scale computer-system architectures were established in the 1960s, but they continue to evolve. Mainframe computers are often used as servers. The term ''mainframe'' was derived from the large cabinet, called a ''main frame'', that housed the central processing unit and main memory of early computers. Later, the term ''mainframe'' was used to distinguish high-end commercial computers from less powerful machines. Design Modern mainframe design is characterized less ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Hardware Watermarking
Hardware watermarking, also known as IP core watermarking is the process of embedding covert marks as design attributes inside a hardware or IP core design itself. Hardware Watermarking can represent watermarking of either DSP Cores (widely used in consumer electronics devices) or combinational/sequential circuits. Both forms of Hardware Watermarking are very popular. In DSP Core Watermarking a secret mark is embedded within the logic elements of the DSP Core itself. DSP Core Watermark usually implants this secret mark in the form of a robust signature either in the RTL design or during High Level Synthesis (HLS) design. The watermarking process of a DSP Core leverages on the High Level Synthesis framework and implants a secret mark in one (or more) of the high level synthesis phases such as scheduling, allocation and binding. DSP Core Watermarking is performed to protect a DSP core from hardware threats such as IP piracy, forgery and false claim of ownership.Anirban Sengupta, Dipanj ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Function (mathematics)
In mathematics, a function from a set to a set assigns to each element of exactly one element of .; the words map, mapping, transformation, correspondence, and operator are often used synonymously. The set is called the domain of the function and the set is called the codomain of the function.Codomain ''Encyclopedia of Mathematics'Codomain. ''Encyclopedia of Mathematics''/ref> The earliest known approach to the notion of function can be traced back to works of Persian mathematicians Al-Biruni and Sharaf al-Din al-Tusi. Functions were originally the idealization of how a varying quantity depends on another quantity. For example, the position of a planet is a ''function'' of time. Historically, the concept was elaborated with the infinitesimal calculus at the end of the 17th century, and, until the 19th century, the functions that were considered were differentiable (that is, they had a high degree of regularity). The concept of a function was formalized at the end of ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
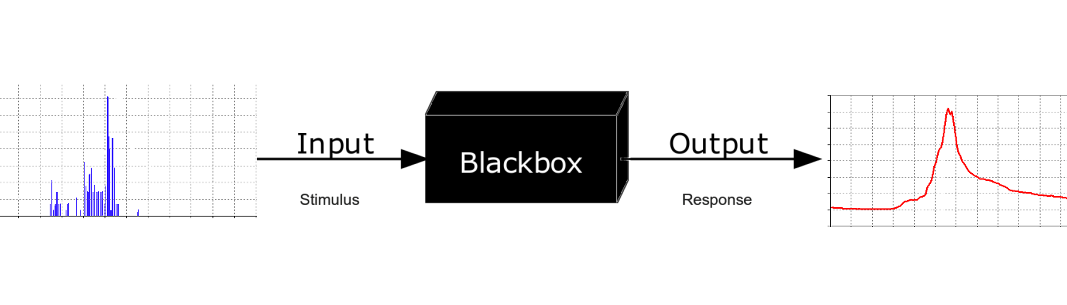
Black Box
In science, computing, and engineering, a black box is a system which can be viewed in terms of its inputs and outputs (or transfer characteristics), without any knowledge of its internal workings. Its implementation is "opaque" (black). The term can be used to refer to many inner workings, such as those of a transistor, an engine, an algorithm, the human brain, or an institution or government. To analyse an open system with a typical "black box approach", only the behavior of the stimulus/response will be accounted for, to infer the (unknown) ''box''. The usual representation of this ''black box system'' is a data flow diagram centered in the box. The opposite of a black box is a system where the inner components or logic are available for inspection, which is most commonly referred to as a white box (sometimes also known as a "clear box" or a "glass box"). History The modern meaning of the term "black box" seems to have entered the English language around 1945. In elect ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Register Renaming
In computer architecture, register renaming is a technique that abstracts logical registers from physical registers. Every logical register has a set of physical registers associated with it. When a machine language instruction refers to a particular logical register, the processor transposes this name to one specific physical register on the fly. The physical registers are opaque and cannot be referenced directly but only via the canonical names. This technique is used to eliminate false data dependencies arising from the reuse of registers by successive instructions that do not have any real data dependencies between them. The elimination of these false data dependencies reveals more instruction-level parallelism in an instruction stream, which can be exploited by various and complementary techniques such as superscalar and out-of-order execution for better performance. Problem approach In a register machine, programs are composed of instructions which operate on values. ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Loop Unwinding
Loop unrolling, also known as loop unwinding, is a loop transformation technique that attempts to optimize a program's execution speed at the expense of its binary size, which is an approach known as space–time tradeoff. The transformation can be undertaken manually by the programmer or by an optimizing compiler. On modern processors, loop unrolling is often counterproductive, as the increased code size can cause more cache misses; ''cf.'' Duff's device. The goal of loop unwinding is to increase a program's speed by reducing or eliminating instructions that control the loop, such as pointer arithmetic and "end of loop" tests on each iteration; reducing branch penalties; as well as hiding latencies, including the delay in reading data from memory. To eliminate this computational overhead, loops can be re-written as a repeated sequence of similar independent statements. Loop unrolling is also part of certain formal verification techniques, in particular bounded model checki ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Hardware Description Language
In computer engineering, a hardware description language (HDL) is a specialized computer language used to describe the structure and behavior of electronic circuits, and most commonly, digital logic circuits. A hardware description language enables a precise, formal description of an electronic circuit that allows for the automated analysis and simulation of an electronic circuit. It also allows for the synthesis of an HDL description into a netlist (a specification of physical electronic components and how they are connected together), which can then be placed and routed to produce the set of masks used to create an integrated circuit. A hardware description language looks much like a programming language such as C or ALGOL; it is a textual description consisting of expressions, statements and control structures. One important difference between most programming languages and HDLs is that HDLs explicitly include the notion of time. HDLs form an integral part of electr ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Information
Information is an abstract concept that refers to that which has the power to inform. At the most fundamental level information pertains to the interpretation of that which may be sensed. Any natural process that is not completely random, and any observable pattern in any medium can be said to convey some amount of information. Whereas digital signals and other data use discrete signs to convey information, other phenomena and artifacts such as analog signals, poems, pictures, music or other sounds, and currents convey information in a more continuous form. Information is not knowledge itself, but the meaning that may be derived from a representation through interpretation. Information is often processed iteratively: Data available at one step are processed into information to be interpreted and processed at the next step. For example, in written text each symbol or letter conveys information relevant to the word it is part of, each word conveys information relev ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Symmetric-key Algorithm
Symmetric-key algorithms are algorithms for cryptography that use the same cryptographic keys for both the encryption of plaintext and the decryption of ciphertext. The keys may be identical, or there may be a simple transformation to go between the two keys. The keys, in practice, represent a shared secret between two or more parties that can be used to maintain a private information link. The requirement that both parties have access to the secret key is one of the main drawbacks of symmetric-key encryption, in comparison to public-key encryption (also known as asymmetric-key encryption). However, symmetric-key encryption algorithms are usually better for bulk encryption. They have a smaller key size, which means less storage space and faster transmission. Due to this, asymmetric-key encryption is often used to exchange the secret key for symmetric-key encryption. Types Symmetric-key encryption can use either stream ciphers or block ciphers. * Stream ciphers encrypt the digi ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Finite State Machine
A finite-state machine (FSM) or finite-state automaton (FSA, plural: ''automata''), finite automaton, or simply a state machine, is a mathematical model of computation. It is an abstract machine that can be in exactly one of a finite number of '' states'' at any given time. The FSM can change from one state to another in response to some inputs; the change from one state to another is called a ''transition''. An FSM is defined by a list of its states, its initial state, and the inputs that trigger each transition. Finite-state machines are of two types— deterministic finite-state machines and non-deterministic finite-state machines. A deterministic finite-state machine can be constructed equivalent to any non-deterministic one. The behavior of state machines can be observed in many devices in modern society that perform a predetermined sequence of actions depending on a sequence of events with which they are presented. Simple examples are vending machines, which dispense ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |