|
Elliptic-curve Diffie–Hellman
Elliptic-curve Diffie–Hellman (ECDH) is a key agreement protocol that allows two parties, each having an Elliptic curve, elliptic-curve public–private key pair, to establish a shared secret over an insecure channel. This shared secret may be directly used as a key, or to Key derivation function, derive another key. The key, or the derived key, can then be used to encrypt subsequent communications using a Symmetric-key algorithm, symmetric-key cipher. It is a variant of the Diffie–Hellman key exchange, Diffie–Hellman protocol using elliptic-curve cryptography. Key establishment protocol The following example illustrates how a shared key is established. Suppose Alice and Bob, Alice wants to establish a shared key with Alice and Bob, Bob, but the only channel available for them may be eavesdropped by a third party. Initially, the Elliptic curve cryptography#Domain parameters, domain parameters (that is, (p, a, b, G, n, h) in the prime case or (m, f(x), a, b, G, n, h) in the bi ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
|
|
Key Agreement
In cryptography, a key-agreement protocol is a protocol whereby two (or more) parties generate a cryptographic Key (cryptography), key as a function of information provided by each honest party so that no party can predetermine the resulting value. In particular, all honest participants influence the outcome. A key-agreement protocol is a specialisation of a key-exchange protocol. At the completion of the protocol, all parties share the same key. A key-agreement protocol precludes undesired third parties from forcing a key choice on the agreeing parties. A secure key agreement can ensure confidentiality and data integrity in communications systems, ranging from simple messaging applications to complex banking transactions. Secure agreement is defined relative to a security model, for example the Universal Model. More generally, when evaluating protocols, it is important to state security goals and the security model. For example, it may be required for the session key to be Authen ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
|
|
Transport Layer Security
Transport Layer Security (TLS) is a cryptographic protocol designed to provide communications security over a computer network, such as the Internet. The protocol is widely used in applications such as email, instant messaging, and voice over IP, but its use in securing HTTPS remains the most publicly visible. The TLS protocol aims primarily to provide security, including privacy (confidentiality), integrity, and authenticity through the use of cryptography, such as the use of certificates, between two or more communicating computer applications. It runs in the presentation layer and is itself composed of two layers: the TLS record and the TLS handshake protocols. The closely related Datagram Transport Layer Security (DTLS) is a communications protocol that provides security to datagram-based applications. In technical writing, references to "(D)TLS" are often seen when it applies to both versions. TLS is a proposed Internet Engineering Task Force (IETF) standard, fir ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
|
 |
Facebook Messenger
Messenger, formerly known as Facebook Messenger, is an American proprietary instant messaging service developed by Meta Platforms. Originally developed as Facebook Chat in 2008, the client application of Messenger is currently available on iOS and Android mobile platforms, Windows and macOS desktop platforms, through the Messenger.com web application, and on the standalone Facebook Portal hardware. Messenger is used to send messages and exchange photos, videos, stickers, audio, and files, and also react to other users' messages and interact with bots. The service also supports voice and video calling. The standalone apps support using multiple accounts, conversations with end-to-end encryption, and playing games. With a monthly userbase of over 1 billion people it is among the largest social media platforms. History Following tests of a new instant messaging platform on Facebook in March 2008, the feature, then-titled "Facebook Chat", was gradually released to ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
|
WhatsApp
WhatsApp (officially WhatsApp Messenger) is an American social media, instant messaging (IM), and voice-over-IP (VoIP) service owned by technology conglomerate Meta. It allows users to send text, voice messages and video messages, make voice and video calls, and share images, documents, user locations, and other content. WhatsApp's client application runs on mobile devices, and can be accessed from computers. The service requires a cellular mobile telephone number to sign up. WhatsApp was launched in February 2009. In January 2018, WhatsApp released a standalone business app called WhatsApp Business which can communicate with the standard WhatsApp client. The service was created by WhatsApp Inc. of Mountain View, California, which was acquired by Facebook in February 2014 for approximately US$19.3 billion. It became the world's most popular messaging application by 2015, and had more than 2billion users worldwide by February 2020, with WhatsApp Business having approxi ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
|
|
Signal (messaging App)
Signal is an American open-source, encrypted messaging service for instant messaging, voice calls, and video calls. The instant messaging function includes sending text, voice notes, images, videos, and other files. Communication may be one-to-one between users or may involve group messaging. The application uses a centralized computing architecture and is cross-platform software. It is developed by the non-profit Signal Foundation and its subsidiary Signal Messenger LLC. Signal's software is free and open-source. Its mobile clients, desktop client, and server are all published under the AGPL-3.0-only license. The official Android app generally uses the proprietary Google Play Services, although it is designed to be able to work without them. Signal is also distributed for iOS and desktop programs for Windows, macOS, and Linux. Registration for desktop use requires an iOS or Android device. Signal uses mobile telephone numbers to register and manage user accounts, thoug ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
|
|
Signal Protocol
The Signal Protocol (formerly known as the TextSecure Protocol) is a non- federated cryptographic protocol that provides end-to-end encryption for voice and instant messaging conversations. The protocol was developed by Open Whisper Systems in 2013 and was introduced in the open-source TextSecure app, which later became Signal. Several closed-source applications have implemented the protocol, such as WhatsApp, which is said to encrypt the conversations of "more than a billion people worldwide" or Google who provides end-to-end encryption by default to all RCS-based conversations between users of their Google Messages app for one-to-one conversations. Facebook Messenger also say they offer the protocol for optional "Secret Conversations", as did Skype for its "Private Conversations". The protocol combines the Double Ratchet Algorithm, prekeys (i.e., one-time ephemeral public keys that have been uploaded in advance to a central server), and a triple elliptic-curve Diffie–Hellm ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
|
 |
End-to-end Encryption
End-to-end encryption (E2EE) is a method of implementing a secure communication system where only communicating users can participate. No one else, including the system provider, telecom providers, Internet providers or malicious actors, can access the cryptographic keys needed to read or send messages. End-to-end encryption prevents data from being read or secretly modified, except by the true sender and intended recipients. Frequently, the messages are relayed from the sender to the recipients by a service provider. However, messages are encrypted by the sender and no third party, including the service provider, has the means to decrypt them. The recipients retrieve the encrypted messages and decrypt them independently. Since third parties cannot decrypt the data being communicated or stored, services that provide end-to-end encryption are better at protecting user data when they are affected by data breaches. Such services are also unable to share user data with governm ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
 |
Line (software)
Line is a freeware app and service for instant messaging and Social networking service, social networking, operated by the Korean-Japanese company LY Corporation, co-owned by SoftBank Group and Naver. Line was launched in Japan in June 2011 by NHN Japan, a subsidiary of Naver. Initially designed for text messaging and Voice over IP, VoIP voice and video calling, it has gradually expanded to become a super-app providing services including a digital wallet (Line Pay), news stream (Line Today), video on demand (Line TV) and digital comic distribution (Line Manga and Line Webtoon). Line became Japan's largest social network in 2013 and is used by over 70% of the population as of 2023; it is also popular mainly in Indonesia, Taiwan and Thailand. History Launch Naver Corporation, Naver launched a messaging app called Naver Talk for the South Korean market in February 2011. However, rival Korean company Kakao dominated the market with its KakaoTalk app, launched in March 2010 Na ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
|
Rambus
Rambus Inc. is an American technology company that designs, develops and licenses chip interface technologies and architectures that are used in digital electronics products. The company, founded in 1990, is well known for inventing RDRAM and for its intellectual property-based litigation following the introduction of DDR-SDRAM memory. History Rambus was founded in March 1990 by electrical and computer engineers, Mike Farmwald and Mark Horowitz. The company's early investors included premier venture capital and investment banking firms such as Kleiner Perkins Caufield and Byers, Merrill Lynch, Mohr Davidow Ventures, and Goldman Sachs. Rambus was incorporated and founded as California company in 1990 and then re-incorporated in the state of Delaware before the company went public in 1997 on the NASDAQ stock exchange under the symbol RMBS. In the 1990s, Rambus was a high-speed interface technology development and marketing company that invented 600 MHz inte ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
|
|
Language Binding
In programming and software design, a binding is an application programming interface (API) that provides glue code specifically made to allow a programming language to use a foreign library or operating system service (one that is not native to that language). Characteristics Binding generally refers to a mapping of one thing to another. In the context of software libraries, bindings are wrapper libraries that bridge two programming languages, so that a library written for one language can be used in another language. Many software libraries are written in system programming languages such as C or C++. To use such libraries from another language, usually of higher-level, such as Java, Common Lisp, Scheme, Python, or Lua, a binding to the library must be created in that language, possibly requiring recompiling the language's code, depending on the amount of modification needed. However, most languages offer a foreign function interface, such as Python's and OCaml's cty ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
|
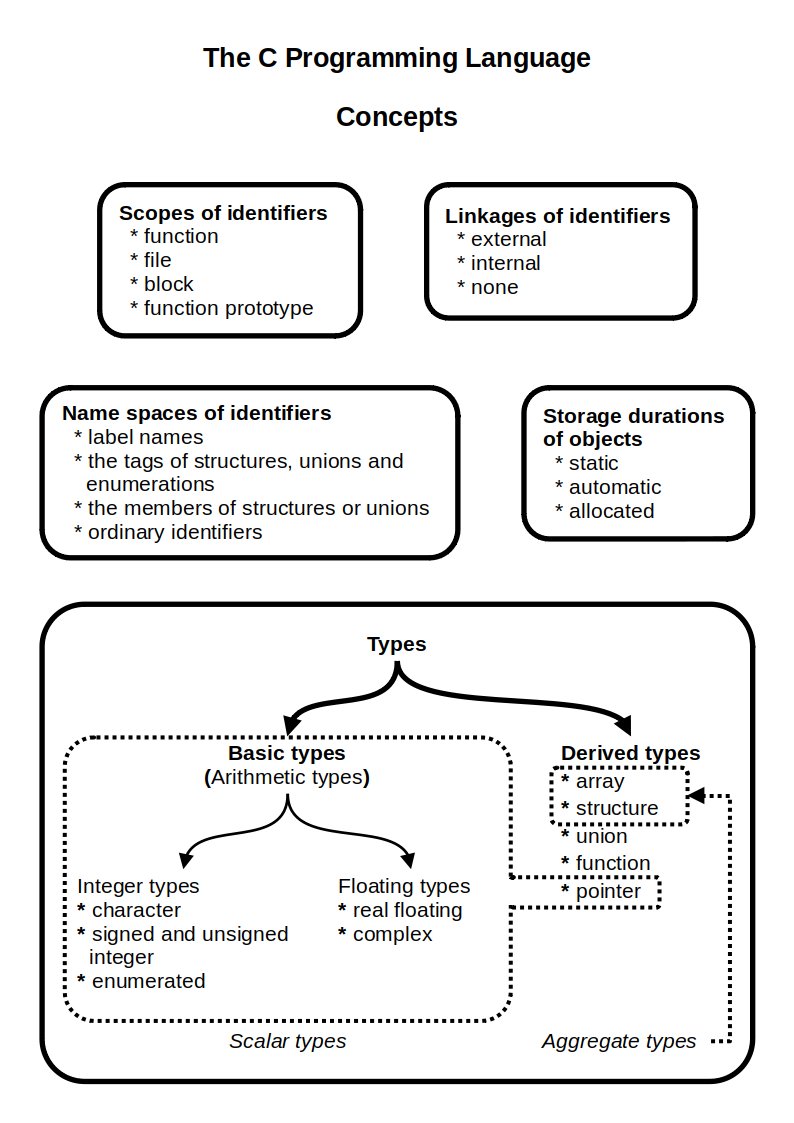 |
C Language
C (''pronounced'' '' – like the letter c'') is a general-purpose programming language. It was created in the 1970s by Dennis Ritchie and remains very widely used and influential. By design, C's features cleanly reflect the capabilities of the targeted CPUs. It has found lasting use in operating systems code (especially in kernels), device drivers, and protocol stacks, but its use in application software has been decreasing. C is commonly used on computer architectures that range from the largest supercomputers to the smallest microcontrollers and embedded systems. A successor to the programming language B, C was originally developed at Bell Labs by Ritchie between 1972 and 1973 to construct utilities running on Unix. It was applied to re-implementing the kernel of the Unix operating system. During the 1980s, C gradually gained popularity. It has become one of the most widely used programming languages, with C compilers available for practically all modern computer arc ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
|
Curve448
In cryptography, Curve448 or Curve448-Goldilocks is an elliptic curve potentially offering 224 bits of security and designed for use with the elliptic-curve Diffie–Hellman (ECDH) key agreement scheme. History Developed by Mike Hamburg of Rambus Cryptography Research, Curve448 allows fast performance compared with other proposed curves with comparable security. The reference implementation is available under an MIT license. The curve was favored by the Internet Research Task Force Crypto Forum Research Group (IRTF CFRG) for inclusion in Transport Layer Security (TLS) standards along with Curve25519. In 2017, NIST announced that Curve25519 and Curve448 would be added to "Special Publication 800-186", which specifies approved elliptic curves for use by the US Federal Government, and in 2023 it was approved for use in FIPS 186-5. Both are described in . The name X448 is used for the DH function. X448 support was added to OpenSSL in version 1.1.1 (released on 11 September 2018). Ma ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |