|
DoublePulsar
DoublePulsar is a backdoor implant tool developed by the U.S. National Security Agency's (NSA) Equation Group that was leaked by The Shadow Brokers in early 2017. The tool infected more than 200,000 Microsoft Windows computers in only a few weeks, and was used alongside EternalBlue in the May 2017 WannaCry ransomware attack. A variant of DoublePulsar was first seen in the wild in March 2016, as discovered by Symantec. Sean Dillon, senior analyst of security company RiskSense Inc., first dissected and inspected DoublePulsar. He said that the NSA exploits are "10 times worse" than the Heartbleed security bug, and use DoublePulsar as the primary payload. DoublePulsar runs in kernel mode, which grants cybercriminals a high level of control over the computer system. Once installed, it uses three commands: ping, kill, and exec Exec or EXEC may refer to: * Executive officer, a person responsible for running an organization * Executive producer, provides finance and guidance ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
WannaCry Ransomware Attack
The WannaCry ransomware attack was a worldwide cyberattack in May 2017 by the WannaCry ransomware cryptoworm, which targeted computers running the Microsoft Windows operating system by encrypting data and demanding ransom payments in the Bitcoin cryptocurrency. It propagated by using EternalBlue, an exploit developed by the United States National Security Agency (NSA) for Windows systems. EternalBlue was stolen and leaked by a group called The Shadow Brokers a month prior to the attack. While Microsoft had released patches previously to close the exploit, much of WannaCry's spread was from organizations that had not applied these, or were using older Windows systems that were past their end-of-life. These patches were imperative to organizations' cyber security but many were not implemented due to ignorance of their importance. Some have claimed a need for 24/7 operation, aversion to risking having formerly working applications breaking because of patch changes, lack of person ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
The Shadow Brokers
The Shadow Brokers (TSB) is a hacker group who first appeared in the summer of 2016. They published several leaks containing hacking tools, including several zero-day exploits, from the "Equation Group" who are widely suspected to be a branch of the National Security Agency (NSA) of the United States. Specifically, these exploits and vulnerabilities targeted enterprise firewalls, antivirus software, and Microsoft products. The Shadow Brokers originally attributed the leaks to the Equation Group threat actor, who have been tied to the NSA's Tailored Access Operations unit. Name and alias Several news sources noted that the group's name was likely in reference to a character from the ''Mass Effect'' video game series. Matt Suiche quoted the following description of that character: "The Shadow Broker is an individual at the head of an expansive organization which trades in information, always selling to the highest bidder. The Shadow Broker appears to be highly competent at its t ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
EternalBlue
EternalBlue is a computer exploit developed by the U.S. National Security Agency (NSA). It was leaked by the Shadow Brokers hacker group on April 14, 2017, one month after Microsoft released patches for the vulnerability. On May 12, 2017, the worldwide WannaCry ransomware used this exploit to attack unpatched computers. On June 27, 2017, the exploit was again used to help carry out the 2017 NotPetya cyberattack on more unpatched computers. The exploit was also reported to have been used since March 2016 by the Chinese hacking group Buckeye (APT3), after they likely found and re-purposed the tool, as well as reported to have been used as part of the Retefe banking trojan since at least September 5, 2017. EternalBlue was among the several exploits used, in conjunction with the DoublePulsar backdoor implant tool, in executing the 2017 WannaCry attacks. Details EternalBlue exploits a vulnerability in Microsoft's implementation of the Server Message Block (SMB) protocol. This ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Backdoor (computing)
A backdoor is a typically covert method of bypassing normal authentication or encryption in a computer, product, embedded device (e.g. a home router), or its embodiment (e.g. part of a cryptosystem, algorithm, chipset, or even a "homunculus computer" —a tiny computer-within-a-computer such as that found in Intel's AMT technology). Backdoors are most often used for securing remote access to a computer, or obtaining access to plaintext in cryptographic systems. From there it may be used to gain access to privileged information like passwords, corrupt or delete data on hard drives, or transfer information within autoschediastic networks. A backdoor may take the form of a hidden part of a program, a separate program (e.g. Back Orifice may subvert the system through a rootkit), code in the firmware of the hardware, or parts of an operating system such as Windows. Trojan horses can be used to create vulnerabilities in a device. A Trojan horse may appear to be an entirely legitim ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Heartbleed
Heartbleed was a security bug in the OpenSSL cryptography library, which is a widely used implementation of the Transport Layer Security (TLS) protocol. It was introduced into the software in 2012 and publicly disclosed in April 2014. Heartbleed could be exploited regardless of whether the vulnerable OpenSSL instance is running as a TLS server or client. It resulted from improper input validation (due to a missing bounds check) in the implementation of the TLS heartbeat extension. Thus, the bug's name derived from ''heartbeat''. The vulnerability was classified as a buffer over-read, a situation where more data can be read than should be allowed. Heartbleed was registered in the Common Vulnerabilities and Exposures database as . The federal Canadian Cyber Incident Response Centre issued a security bulletin advising system administrators about the bug. A fixed version of OpenSSL was released on 7 April 2014, on the same day Heartbleed was publicly disclosed. System administr ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Windows Trojans
Windows is a group of several proprietary graphical operating system families developed and marketed by Microsoft. Each family caters to a certain sector of the computing industry. For example, Windows NT for consumers, Windows Server for servers, and Windows IoT for embedded systems. Defunct Windows families include Windows 9x, Windows Mobile, and Windows Phone. The first version of Windows was released on November 20, 1985, as a graphical operating system shell for MS-DOS in response to the growing interest in graphical user interfaces (GUIs). Windows is the most popular desktop operating system in the world, with 75% market share , according to StatCounter. However, Windows is not the most used operating system when including both mobile and desktop OSes, due to Android's massive growth. , the most recent version of Windows is Windows 11 for consumer PCs and tablets, Windows 11 Enterprise for corporations, and Windows Server 2022 for servers. Genealogy By marketing ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Malware
Malware (a portmanteau for ''malicious software'') is any software intentionally designed to cause disruption to a computer, server, client, or computer network, leak private information, gain unauthorized access to information or systems, deprive access to information, or which unknowingly interferes with the user's computer security and privacy. By contrast, software that causes harm due to some deficiency is typically described as a software bug. Malware poses serious problems to individuals and businesses on the Internet. According to Symantec's 2018 Internet Security Threat Report (ISTR), malware variants number has increased to 669,947,865 in 2017, which is twice as many malware variants as in 2016. Cybercrime, which includes malware attacks as well as other crimes committed by computer, was predicted to cost the world economy $6 trillion USD in 2021, and is increasing at a rate of 15% per year. Many types of malware exist, including computer viruses, worms, Trojan horse ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Exec (system Call)
In computing, exec is a functionality of an operating system that runs an executable file in the context of an already existing process, replacing the previous executable. This act is also referred to as an overlay. It is especially important in Unix-like systems, although it exists elsewhere. As no new process is created, the process identifier (PID) does not change, but the machine code, data, heap, and stack of the process are replaced by those of the new program. The ''exec'' call is available for many programming languages including compilable languages and some scripting languages. In OS command interpreters, the built-in command replaces the shell process with the specified program. Nomenclature Interfaces to ''exec'' and its implementations vary. Depending on programming language it may be accessible via one or more functions, and depending on operating system it may be represented with one or more actual system calls. For this reason ''exec'' is sometimes descri ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Exit (system Call)
On many computer operating systems, a computer process terminates its execution by making an exit system call. More generally, an exit in a multithreading environment means that a thread of execution has stopped running. For resource management, the operating system reclaims resources (memory, files, etc.) that were used by the process. The process is said to be a '' dead process'' after it terminates. How it works Under Unix and Unix-like operating systems, a process is started when its parent process executes a ''fork'' system call. The parent process may then wait for the child process to terminate, or may continue execution (possibly forking off other child processes). When the child process terminates ("dies"), either normally by calling ''exit'', or abnormally due to a fatal exception or signal (e.g., SIGTERM, SIGINT, SIGKILL), an exit status is returned to the operating system and a SIGCHLD signal is sent to the parent process. The exit status can then be retrieve ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
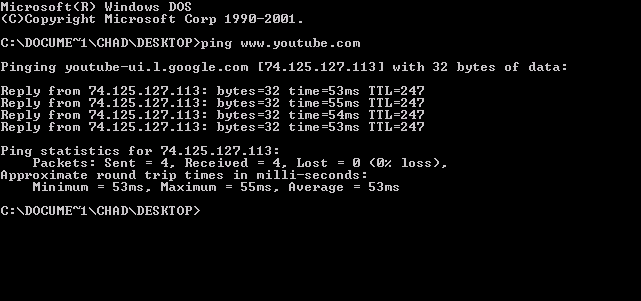
Ping (networking Utility)
ping is a computer network administration software utility used to test the reachability of a host on an Internet Protocol (IP) network. It is available for virtually all operating systems that have networking capability, including most embedded network administration software. Ping measures the round-trip time for messages sent from the originating host to a destination computer that are echoed back to the source. The name comes from active sonar terminology that sends a pulse of sound and listens for the echo to detect objects under water. Ping operates by means of Internet Control Message Protocol (ICMP) packets. ''Pinging'' involves sending an ICMP echo request to the target host and waiting for an ICMP echo reply. The program reports errors, packet loss, and a statistical summary of the results, typically including the minimum, maximum, the mean round-trip times, and standard deviation of the mean. The command-line options of the ping utility and its output vary bet ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Kernel Mode
In computer science, hierarchical protection domains, often called protection rings, are mechanisms to protect data and functionality from faults (by improving fault tolerance) and malicious behavior (by providing computer security). Computer operating systems provide different levels of access to resources. A protection ring is one of two or more hierarchical ''levels'' or ''layers'' of privilege within the architecture of a computer system. This is generally hardware-enforced by some CPU architectures that provide different CPU modes at the hardware or microcode level. Rings are arranged in a hierarchy from most privileged (most trusted, usually numbered zero) to least privileged (least trusted, usually with the highest ring number). Ring 0 is the level with the most privileges and allows direct interaction with the physical hardware such as certain CPU functionality and chips on the motherboard. Special call gates between rings are provided to allow an outer ring to ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Payload (computing)
In computing and telecommunications, the payload is the part of transmitted data that is the actual intended message. Headers and metadata are sent only to enable payload delivery. In the context of a computer virus or worm, the payload is the portion of the malware which performs malicious action. The term is borrowed from transportation, where '' payload'' refers to the part of the load that ''pays'' for transportation. Networking In computer networking, data to be transmitted is the payload. It is almost always encapsulated in some type of frame format, composed of framing bits and a frame check sequence. Examples are Ethernet frames, Point-to-Point Protocol (PPP) frames, Fibre Channel frames, and V.42 modem frames. Programming In computer programming, the most common usage of the term is in the context of message protocols, to differentiate the protocol overhead from the actual data. For example, a JSON web service response might be: The string ''Hello, ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |