|
Dropper (malware)
A dropper is a Trojan horse that has been designed to install malware (such as viruses and backdoors) onto a computer. The malware within the dropper can be packaged to evade detection by antivirus software. Alternatively, the dropper may download malware to the target computer once activated. Droppers can be categorized into two types: persistent and non-persistent. Persistent droppers conceal themselves on the device and alter system registry keys. Concealment allows them to reinstall the malware during a reboot, even if previously removed. Non-persistent droppers are considered less dangerous as they remove themselves from the system after executing their payload. Thus, once the malware is removed, it cannot reinstall itself. Trojan horses operate by masquerading as legitimate programs, requiring user interaction to execute. They unpack and load malicious code into the computer's memory, then install malicious software (malware). Precautions can be taken to prevent infection ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Broadcom
Broadcom Inc. is an American multinational corporation, multinational designer, developer, manufacturer, and global supplier of a wide range of semiconductor and infrastructure software products. Broadcom's product offerings serve the data center, networking, software, broadband, wireless, storage, and industrial markets. As of 2024, some 58 percent of Broadcom's revenue came from its semiconductor-based products and 42 percent from its infrastructure software products and services. Tan Hock Eng is the company's president and chief executive officer, CEO. The company is headquartered in Palo Alto, California. Avago Technologies Limited was changing its name to ''Broadcom'' to acquire Broadcom Corporation in January 2016. Avago's ticker symbol AVGO now represents the merged entity. The Broadcom Corporation ticker symbol BRCM was retired. Initially the merged entity was known as ''Broadcom Limited'', before assuming the current name in November 2017. In October 2019, the Europe ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Trojan Horse (computing)
In computing, a trojan horse (or simply trojan; often capitalized, but see below) is a kind of malware that misleads users as to its true intent by disguising itself as a normal program. Trojans are generally spread by some form of social engineering (security), social engineering. For example, a user may be duped into executing an email attachment disguised to appear innocuous (e.g., a routine form to be filled in), or into clicking on a fake advertisement on the Internet. Although their payload can be anything, many modern forms act as a backdoor (computing), backdoor, contacting a controller who can then have unauthorized access to the affected device. Ransomware attacks are often carried out using a trojan. Unlike computer viruses and Computer worm, worms, trojans generally do not attempt to inject themselves into other files or otherwise propagate themselves. Origins of the term The term is derived from the Ancient Greece, ancient Greek story of the deceptive Trojan Horse ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Malware
Malware (a portmanteau of ''malicious software'')Tahir, R. (2018)A study on malware and malware detection techniques . ''International Journal of Education and Management Engineering'', ''8''(2), 20. is any software intentionally designed to cause disruption to a computer, server (computing), server, Client (computing), client, or computer network, leak private information, gain unauthorized access to information or systems, deprive access to information, or which unknowingly interferes with the user's computer security and privacy. Researchers tend to classify malware into one or more sub-types (i.e. computer viruses, Computer worm, worms, Trojan horse (computing), Trojan horses, logic bombs, ransomware, spyware, adware, rogue software, Wiper (malware), wipers and keyloggers). Malware poses serious problems to individuals and businesses on the Internet. According to NortonLifeLock, Symantec's 2018 Internet Security Threat Report (ISTR), malware variants number has increased to 66 ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Computer Virus
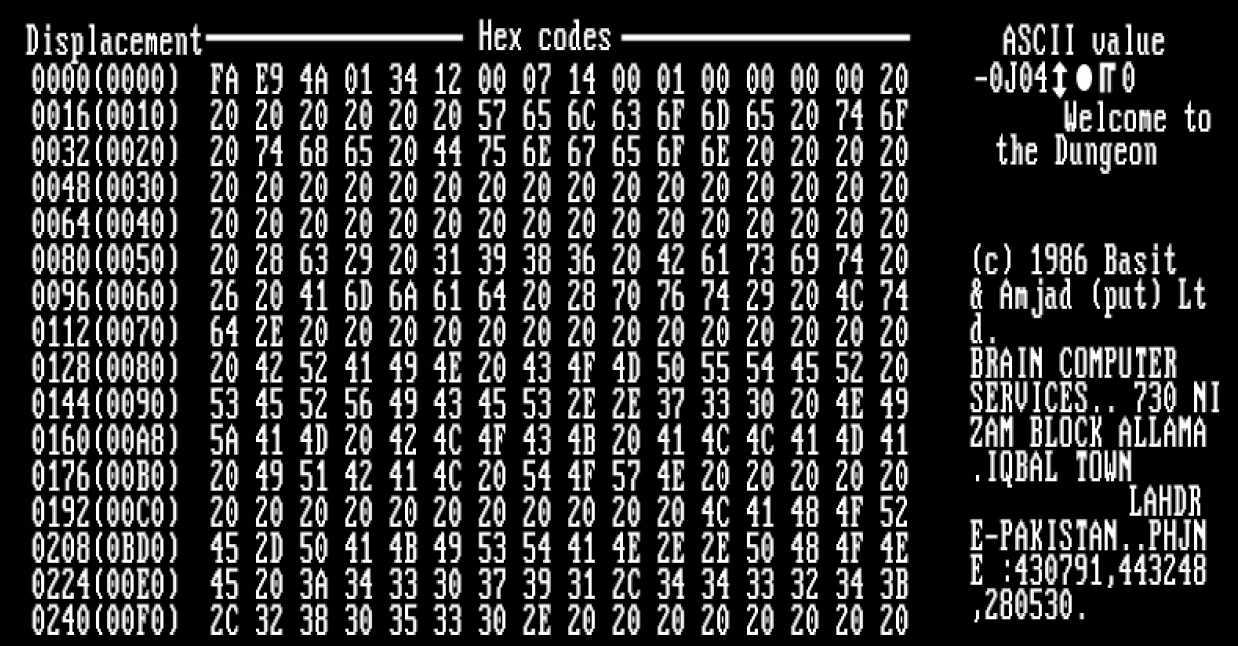
A computer virus is a type of malware that, when executed, replicates itself by modifying other computer programs and Code injection, inserting its own Computer language, code into those programs. If this replication succeeds, the affected areas are then said to be "infected" with a computer virus, a metaphor derived from biological viruses. Computer viruses generally require a Computer program, host program. The virus writes its own code into the host program. When the program runs, the written virus program is executed first, causing infection and damage. By contrast, a computer worm does not need a host program, as it is an independent program or code chunk. Therefore, it is not restricted by the Computer program, host program, but can run independently and actively carry out attacks. Virus writers use social engineering (security), social engineering deceptions and exploit detailed knowledge of vulnerability (computing), security vulnerabilities to initially infect systems an ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Backdoor (computing)
A backdoor is a typically covert method of bypassing normal authentication or encryption in a computer, product, embedded device (e.g. a home router), or its embodiment (e.g. part of a cryptosystem, algorithm, chipset, or even a "homunculus computer"—a tiny computer-within-a-computer such as that found in Intel's AMT technology). Backdoors are most often used for securing remote access to a computer, or obtaining access to plaintext in cryptosystems. From there it may be used to gain access to privileged information like passwords, corrupt or delete data on hard drives, or transfer information within autoschediastic networks. In the United States, the 1994 Communications Assistance for Law Enforcement Act forces internet providers to provide backdoors for government authorities. In 2024, the U.S. government realized that China had been tapping communications in the U.S. using that infrastructure for months, or perhaps longer; China recorded presidential candidate campaign offi ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Antivirus Software
Antivirus software (abbreviated to AV software), also known as anti-malware, is a computer program used to prevent, detect, and remove malware. Antivirus software was originally developed to detect and remove computer viruses, hence the name. However, with the proliferation of other malware, antivirus software started to protect against other computer threats. Some products also include protection from malicious URLs, spam, and phishing. History 1971–1980 period (pre-antivirus days) The first known computer virus appeared in 1971 and was dubbed the " Creeper virus". This computer virus infected Digital Equipment Corporation's ( DEC) PDP-10 mainframe computers running the TENEX operating system.From the first email to the first YouTube video: a d ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Download
In computer networks, download means to ''receive'' data from a remote system, typically a server such as a web server, an FTP server, an email server, or other similar systems. This contrasts with uploading, where data is ''sent to'' a remote server. A ''download'' is a file offered for downloading or that has been downloaded, or the process of receiving such a file. Definition Downloading generally transfers entire files for local storage and later use, as contrasted with streaming, where the data is used nearly immediately while the transmission is still in progress and may not be stored long-term. Websites that offer streaming media or media displayed in-browser, such as YouTube, increasingly place restrictions on the ability of users to save these materials to their computers after they have been received. Downloading on computer networks involves retrieving data from a remote system, like a web server, FTP server, or email server, unlike uploading, where data is sent ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
System Registry
The Windows Registry is a hierarchical database A hierarchical database model is a data model in which the data is organized into a tree-like structure. The data are stored as records which is a collection of one or more fields. Each field contains a single value, and the collection of fields i ... that stores High- and low-level, low-level settings for the Microsoft Windows operating system and for applications that opt to use the registry. The kernel (operating system), kernel, device drivers, Windows service, services, Security Accounts Manager, and Graphical user interface, user interfaces can all use the registry. The registry also allows access to Instrumentation (computer programming), counters for profiling system performance. In other words, the registry or Windows Registry contains information, settings, options, and other values for programs and hardware installed on all versions of Microsoft Windows operating systems. For example, when a program is installed, a new s ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Microsoft Store
The Microsoft Store (formerly known as the Windows Store) is a digital distribution platform operated by Microsoft. It was created as an app store for Windows 8 as the primary means of distributing Universal Windows Platform apps. With Windows 10 1803, Microsoft merged its other distribution platforms ( Windows Marketplace, Windows Phone Store, Xbox Music, Xbox Video, Xbox Store, and a web storefront also known as "Microsoft Store") into Microsoft Store, making it a unified distribution point for apps, console games, and digital videos. Digital music was included until the end of 2017, and E-books were included until 2019. As with other similar platforms, such as the Google Play and Mac App Store, Microsoft Store is curated, and apps must be certified for compatibility and content. In addition to the user-facing Microsoft Store client, the store has a developer portal with which developers can interact. Microsoft takes 5–15% of the sale price for apps and 30 ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Apple App Store
The App Store is an app marketplace developed and maintained by Apple, for mobile apps on its iOS and iPadOS operating systems. The store allows users to browse and download approved apps developed within Apple's iOS SDK. Apps can be downloaded on the iPhone, iPod Touch, or iPad, and some can be transferred to the Apple Watch smartwatch or 4th-generation or newer Apple TVs as extensions of iPhone apps. The App Store opened on July 10, 2008, with an initial 500 applications available. The number of apps peaked at around 2.2 million in 2017, but declined slightly over the next few years as Apple began a process to remove old or 32-bit apps. , the store features more than 1.8 million apps. While Apple touts the role of the App Store in creating new jobs in the "app economy" and claims to have paid over $155 billion to developers, the App Store has also attracted criticism from developers and government regulators that it operates a monopoly and that Apple's 30% cut of revenues f ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Sideloading
Sideloading describes the process of transferring files between two local devices, in particular between a personal computer and a mobile device such as a mobile phone, smartphone, PDA, tablet, portable media player or e-reader. Sideloading typically refers to media file transfer to a mobile device via USB, Bluetooth, WiFi or by writing to a memory card for insertion into the mobile device, but also applies to the transfer of apps from web sources that are not vendor-approved. When referring to Android apps, "sideloading" typically means installing an application package in APK format onto an Android device. Such packages are usually downloaded from websites other than the official app store Google Play. For Android users sideloading of apps is only possible if the user has allowed "Unknown Sources" in their Security Settings. When referring to iOS apps, "sideloading" means installing an app in IPA format onto an Apple device, usually through the use of a computer program ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Drive-by Download
In computer security, a drive-by download is the unintended download of software, typically Malware, malicious software. The term "drive-by download" usually refers to a download which was authorized by a user without understanding what is being downloaded, such as in the case of a Trojan horse (computing), Trojan horse. In other cases, the term may simply refer to a download which occurs without a user's knowledge. Common types of files distributed in drive-by download attacks include Computer virus, computer viruses, spyware, or crimeware. Drive-by downloads may happen when visiting a website, opening an Email attachment, e-mail attachment, clicking a link in an email, or clicking on a deceptive pop-up window. Users often click on a pop-up window in the mistaken belief that, for example, an error message from the computer's operating system is being acknowledged or a seemingly innocuous advertisement pop-up is being dismissed. In such cases, the "supplier" may claim that the us ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |