Introduction to SAML metadata
To securely interoperate, partners share metadata in whatever form and by whatever means possible. In any case, at least the following metadata must be shared: * Entity ID * Cryptographic keys * Protocol endpoints (bindings and locations) Every SAML system entity has an entity ID, a globally-unique identifier used in software configurations, relying-party databases, and client-side cookies. On the wire, every SAML protocol message contains the entity ID of the issuer. For authentication purposes, a SAML message may be digitally signed by the issuer. To verify the signature on the message, the message receiver uses a public key known to belong to the issuer. Similarly, to encrypt a message, a public encryption key belonging to the ultimate receiver must be known to the issuer. In both situations—signing and encryption—trusted public keys must be shared in advance. Once the message is signed and encrypted, the issuer sends the message to a trusted protocol endpoint, the location of which must be known in advance. Upon receipt, the message receiver decrypts the message (using its own private decryption key) and verifies the signature (using a trusted public key in metadata) before mapping the entity ID in the message to a trusted partner. The previous scenario requires each party to know the other in advance. To establish a baseline of trust, parties share metadata with each other. Initially, this may be as simple as sharing information via email. Over time, as the number of SAML partners grows, the natural tendency is to automate the metadata sharing process. To fully automate the metadata sharing process, a standard file format is needed. To this end, the SAML V2.0 Metadata specification defines a standard representation for SAML metadata that simplifies the configuration of SAML software and makes it possible to create secure, automated processes for metadata sharing.Metadata-driven interoperability
As SAML technology has matured, the importance of SAML metadata has steadily increased. Today an implementation that supports SAML web browser requires a schema-valid SAML metadata file for each SAML partner. (See the SAML V2.0 Profiles specification for more information about SAML web browser SSO.)
Static metadata configuration
The term ''static metadata'' refers to a metadata file that is configured directly into the SAML application by an administrator. In doing so, the administrator becomes responsible for the maintenance of the metadata regardless of how the metadata was obtained in the first place. Thus static metadata contributes to the overall static configuration of the SAML application. Unfortunately, SAML metadata is inherently non-static as illustrated by the following typical scenario between a SAML identity provider (IdP) and a SAML service provider (SP). Suppose an IdP owner obtains SAML metadata from an SP partner. Perhaps the SP metadata is transmitted to the IdP owner via email, or maybe the IdP owner logs into a protected web app and downloads the SP metadata via a browser. Regardless of how the metadata is obtained, the end result is the same: The IdP owner configures the SP metadata directly into the IdP software. Now suppose the SP metadata contains a public encryption key. Presumably, the corresponding private decryption key is configured into the SP software. If the private decryption key is compromised (or otherwise needs to be replaced), the public encryption key in the SP metadata is no longer trustworthy and must be replaced as well. Since the SP metadata is statically configured in the IdP software, only the IdP owner can replace the public encryption key in the SP metadata. In this sense, ''the IdP owner is responsible for the SP metadata.'' This mismatch leads to interoperability issues. The same is true on the SP side. By statically configuring IdP metadata into the SP software, the SP owner implicitly accepts the responsibility to maintain the IdP metadata when something changes. Since an IdP (or SP) typically has many partners, static metadata configuration clearly does not scale, and moreover, change management associated with static metadata is difficult at best.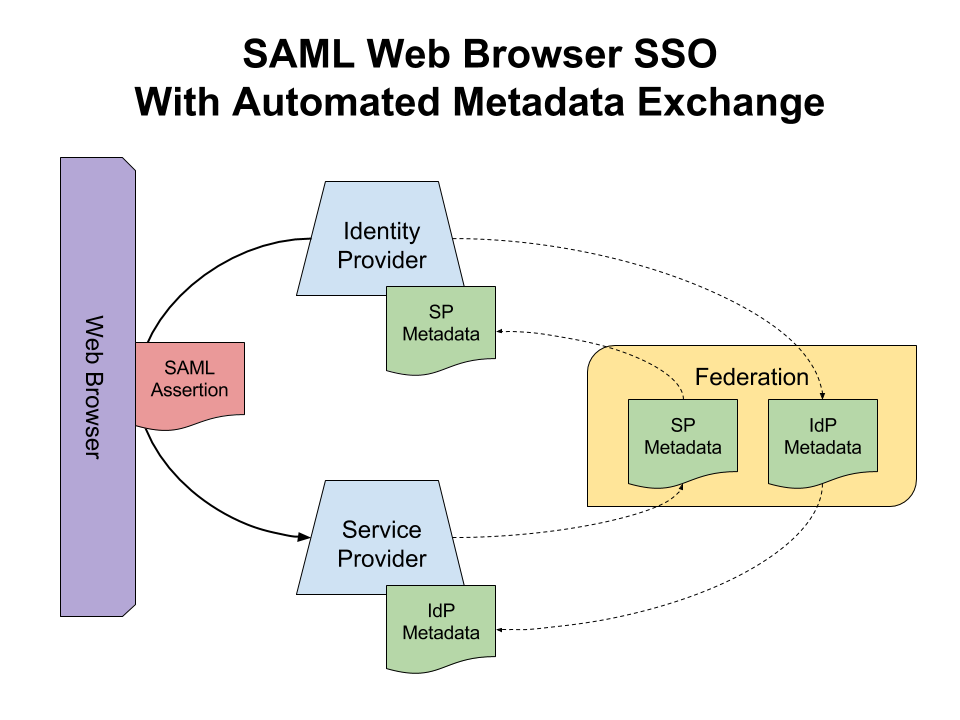
Dynamic metadata exchange
Not surprisingly, metadata sharing processes yearn to be automated. Every metadata file that is statically configured into the SAML application by an administrator incurs technical debt. The accumulation of this debt prevents the SAML deployment from scaling to its potential. To avoid excessive technical debt, the metadata sharing process must be automated. One approach is to enlist the help of a trusted third party whose responsibility it is to collect, curate, and distribute metadata across the network. Curated metadata is consistently formatted, more likely to be free of vulnerabilities (intentional or otherwise), and therefore safe to use. In the case of SAML metadata, this trusted third party is called a ''SAML federation.'' The community of SAML deployers comprising the federation willingly conform to one or more profiles of SAML to promote interoperability and trust. To that end, federation participants often share a central infrastructure for metadata sharing, which allows the federation to scale to thousands of interoperable SAML deployments.A history of SAML metadata
Now let's retrace some of the steps that led to the publication of the SAML V2.0 Metadata specification in March 2005. A turning point occurred on 14 November 2003—our story starts there.Historical origins
In response toLiberty contributed ID-FF 1.2 to OASIS
The contribution included a document entitled ''Liberty Metadata Description and Discovery Specification Version 1.0,'' which included the following design goals: # "whois for SAML federations" (based on the
Organization and ContactPerson elements in metadata)
# dynamic discovery of metadata (with resolution via DNS and Well-Known Location)
# document-level security using XML Signature
As it turns out, all of those goals were preserved in the OASIS SAML V2.0 Metadata Standard described later in this article.
The schema document included with thlegacy Liberty ID-FF 1.2 archive
is identified as Liberty Metadata Version 1.1 whereas Liberty Metadata Version 1.0 was contributed to OASIS. The apparent contradiction was explained by the schema's author. (Peter Davis, Personal Communication) Between November 2003 (when Version 1.0 was contributed to OASIS) and December 2004 (when Version 1.1 was completed by Liberty), development of the Liberty metadata specification continued in parallel with the OASIS work stream. See the chart below for a visual representation. The arrows in the chart indicate dependencies while the dashed lines indicate equivalencies. Relevant
Version 1.0 schema
and th
Version 1.1 schema
are linked here courtesy of the Internet Archive's Wayback Machine.
Post-November 2003
Over the next thirteen months, from November 2003 to December 2004, the OASIS Security Services (SAML) Technical Committee (SSTC) molded the Liberty metadata specification into what eventually became known as SAML Metadata. During that time, the SSTC generalized the metadata specification to include support for multiple protocols (including non-SAML protocols) but more importantly, the Liberty metadata schema was retrofitted with numerous extension points. Historically, the extensibility of SAML Metadata has had important consequences, as we shall see. By March 2004, most of the Liberty contribution was incorporated into the OASIS work stream. From that point onward, the Liberty and OASIS work streams progressed concurrently (but not independently since the same people were working on both specifications). Between March and July 2004, the fledgling SAML Metadata specification underwent significant churn. In July 2004, the SSTC issuedcovering a complete set of SAML V2.0 draft specifications. Included in that specification set was a working draft of a newly forged SAML V2.0 Metadata specification. In retrospect, it appears as though the bulk of the SAML V2.0 Metadata specification was developed between March and July 2004, but clearly the SAML V2.0 Metadata Standard sprung from the loins of the Liberty Alliance, specifically Liberty Metadata Version 1.0. Consequently, to understand the origins of SAML Metadata, one must study the provenance of Liberty metadata. The remaining history of SAML Metadata is mostly OASIS administrative process. After the final Committee Draft was published in November 2004, the SSTC began the standardization process in January 2005. Finally, on 5 March 2005, OASIS announced the newly ratified SAML V2.0 Standard. The V2.0 specification set (see the
Pre-November 2003
As it turns out, the influence of the Liberty Identity Federation Framework on SAML Metadata predates the contribution of ID-FF 1.2 in November 2003. Apparently the SSTC was dabbling in metadata in parallel with the Liberty Alliance. An excerpt from a draft metadata specification published in September 2003 bears this out:This document defines metadata that describe the elements and attributes required to use the SAML Web Browser SSO Profiles. Since the Liberty Alliance Web SSO Profiles are directly based on the SAML Web SSO Profiles, the metadata defined in this document borrows extensively from the metadata definitions in the draft Liberty Alliance 1.2 specifications. (Excerpted from "Metadata for SAML 2.0 Web Browser SSO Profiles")The revision history at the end of that draft document gives the following characterization of itself: "Initial draft based on Draft 07 of SAML 1.1 Metadata specification." In other words, earlier draft documents were published. Indeed, the revision history at the end of the previous draft shows a trail of metadata specifications dating back to November 2002. Following the document trail, the influence of Liberty ID-FF on SAML metadata can be traced to a draft specification published in April 2003. This is the first known OASIS document that references Liberty ID-FF, specifically, Liberty Metadata Version 1.0-06, an early version of the Liberty Metadata specification about which little is known. It is, however, clear that "Metadata for SAML 1.1 Web Browser Profiles" was intended to be a companion to the SAML V1.1 Standard but of course we know that V1.1 does not specify the use of metadata. See the next section for relevant conjecture. Two early metadata schema may be of interest: # In June 2002, barely a month after the SSTC completed its work on what was to become the SAML V1.0 Standard, the
metadata schema
consisting of
Historical summary
We know that metadata standards for SAML V1.0 or SAML V1.1 were never published. We also know that the necessary IPR for Liberty Metadata was not in place until November 2003. With that, we offer the following summary and conjecture: # A draft specification entitled "Metadata for SAML 1.0 Web Browser Profiles" was the first known SAML metadata specification. The document is dated 12 November 2002, which is one week after the SAML V1.0 Standard was announced, which is curious. In any case, the metadata syntax used in that document is completely different from what we now know as SAML Metadata. That document was never published and its origins remain a mystery. # A draft specification entitled "Metadata for SAML 1.1 Web Browser Profiles" was the first known SAML metadata specification based on Liberty ID-FF. It was completed in April 2003. The title of the draft specification makes it clear that the SSTC knew that SAML V1.1 was coming and moreover SAML metadata was to be included in the SAML V1.1 Standard. # Unfortunately that did not happen since the necessary IPR was not in place when the SAML V1.1 Standard was announced. Indeed, thoccurred two months after the announcement of the SAML V1.1 Standard in September 2003. # In September 2003, less than two weeks after the announcement of the SAML V1.1 Standard, the SSTC set its sights on SAML V2.0 by forking the document stream and renaming the draft document: "Metadata for SAML 2.0 Web Browser Profiles." # SAML Metadata came to life between March and July 2004. The SSTC issued
that included a candidate SAML Metadata specification. # The final SAML Metadata specification was included in the SAML V2.0 Standard specification set announced in March 2005. # For the next 10 years, the specification documents evolved (but the schema remained stable). A specification for SAML V2.0 Metadata with Errata (SAMLMeta20Errata) was published in September 2015.
Post-V2.0 specifications
As mentioned earlier, the SAML V2.0 Metadata Schema has numerous extension points. This feature led to a proliferation of "Post-V2.0" specifications that extended the standard in several directions. The more popular metadata extensions are listed below for convenience (see theSAML metadata examples
In this section we give concrete examples of the SAML ''entity descriptor,'' the basic unit of policy and interoperability in SAML metadata. Each of the examples includes the following metadata bits: * Entity ID and entity attributes * Role descriptor (describing either a SAML identity provider or a SAML service provider) ** User interface elements ** Signing keys or encryption keys ** Single sign-on protocol endpoints * Registration and publication info * Organization and contact info (for human readers) In the examples below, a particular URI in metadata (such as anentityID or an endpoint location) maps to a responsible party via the URI's domain component:
* The organization that owns domain example.info is responsible for an unspecified SAML entity (such as an identity provider or a service provider)
* The organization that owns domain example.org is responsible for a SAML identity provider
* The organization that owns domain example.com is responsible for a SAML service provider
* The organization that owns domain example.net is a trusted 3rd party responsible for metadata registration and publication
Note that SAML metadata describes all parties involved in metadata-driven SAML Web Browser SSO except the browser user. (See the SAML V2.0 Profiles specification for more information about SAML web browser SSO.)
Entity metadata
The following code sample illustrates the common technical features of a SAMLentityID attribute is the unique identifier of the entity. Note well that the entityID is an immutable name for the entity, not a location.
* The validUntil attribute gives the expiration date of the metadata.
* The creationInstant attribute gives the precise instant the metadata was created. Comparing the value of the creationInstant attribute to the value of the validUntil attribute, we see that the metadata is valid for two weeks.
* The Identity provider metadata
A SAML identity provider manages a Single Sign-On Service endpoint that receives authentication requests from service providers. The entity descriptor for an identity provider in that role contains anBinding attributes of the md:SingleSignOnService/@Location attributes in identity provider metadata are used by a service provider to route SAML messages, which minimizes the possibility of a rogue identity provider orchestrating a Service provider metadata
A SAML service provider manages an Assertion Consumer Service endpoint that receives authentication assertions from identity providers. The entity descriptor for a service provider in that role contains anWantAssertionsSigned attribute on the index attribute of an AssertionConsumerServiceIndex attribute in a Binding attribute of the index attribute of the AttributeConsumingServiceIndex attribute in a md:AssertionConsumerService/@Location attribute in service provider metadata is used by an identity provider to route SAML messages, which minimizes the possibility of a rogue service provider orchestrating a Metadata-driven SAML web browser
The following SAML protocol flow is intended to illustrate the use of metadata at various stages of SAML web browser SSO. (See the SAML V2.0 Profiles specification for more information about SAML web browser SSO.) Trusted SAML metadata ensures a secure transaction between a SAML identity provider (IdP) and a SAML service provider (SP). Before metadata, trust information was encoded into the implementation in a proprietary manner. Now the sharing of trust information is facilitated by standard metadata. The SAML 2.0 Metadata Standard provides a well-defined, interoperable metadata format that entities can use to bootstrap the trust process.
The following sequence illustrates the use of SAML metadata to drive the SAML protocol flow.
Trusted SAML metadata ensures a secure transaction between a SAML identity provider (IdP) and a SAML service provider (SP). Before metadata, trust information was encoded into the implementation in a proprietary manner. Now the sharing of trust information is facilitated by standard metadata. The SAML 2.0 Metadata Standard provides a well-defined, interoperable metadata format that entities can use to bootstrap the trust process.
The following sequence illustrates the use of SAML metadata to drive the SAML protocol flow.
1. Request the target resource at the SP
A browser user requests a web application resource protected by a SAML service provider:2. Redirect to the Discovery Service
Before the service provider can initiate the SAML protocol flow at step 6, the browser user's preferred identity provider must be known. There are numerous ways to do this. For illustration purposes, the service provider will use a local Discovery Service that conforms to the ''Identity Provider Discovery Service Protocol and Profile.'' The service provider redirects the browser user to the Discovery Service:entityID is included in the redirect URL as specified by the discovery protocol.
3. Request the Discovery Service
The browser user requests the Discovery Service by virtue of the redirect:4. Redirect to the Discovery Response endpoint at the SP
The Discovery Service now redirects the browser user to a Discovery Response endpoint at the service provider:entityID is included in the redirect URL as specified by the discovery protocol.
5. Request the Discovery Response endpoint at the SP
The browser user requests the Discovery Response endpoint at the service provider by virtue of the redirect:6. Redirect to SSO Service at the IdP
The service provider generates a relevant7. Request the SSO Service at the IdP
The browser user requests the Single Sign-On Service endpoint at the identity provider by virtue of the redirect:8. Respond with the login page
The identity provider returns a login page to the user's browser. The login page contains an HTML form similar to the following:9. Submit the login form
The browser user submits the HTML form to the identity provider:eduPersonUniqueId and mail.
Operationally, the identity provider digitally signs and encrypts the SAML Assertion, wraps the Assertion in a SAML Response, and then signs the Response object as well. Typically the identity provider signs the Response alone but in this case both the Assertion and the Response are digitally signed.
10. Respond with the SAML Response page
The identity provider returns an XHTML document to the user's browser. The document contains a SAML Response encoded in an XHTML form as follows:11. Request the Assertion Consumer Service at the SP
The XHTML form is automatically submitted by the browser (due to a small bit of JavaScript on the page):12. Redirect to the target resource
The service provider creates a security context for the user principal and redirects the browser user to the original web application resource:13. Request the target resource at the SP again
Finally the browser user requests the target resource at the service provider by virtue of the redirect:14. Respond with requested resource
Since a security context exists, the service provider returns the resource to the browser user agent as requested.See also
*References
Liberty metadata specifications
Note: The Liberty metadata schema are listed verbatim in the specification documents listed below. Since the direct link to the Version 1.1 XSD document on the Liberty web site is broken, a copy of thXSD document for Liberty Metadata Version 1.1
has been uploaded to the web. That document is also included in th
legacy Liberty ID-FF 1.2 archive
SAML metadata specifications pre-2005
SAML standards
The original SAML V2.0 standards published in March 2005 have been deprecated in favor of the revised specifications with errata listed further below. * S. Cantor et al. ''Assertions and Protocols for the OASIS Security Assertion Markup Language (SAML) V2.0.'' OASIS Standard, March 2005. Document ID saml-core-2.0-os http://docs.oasis-open.org/security/saml/v2.0/saml-core-2.0-os.pdf * S. Cantor et al. ''Bindings for the OASIS Security Assertion Markup Language (SAML) V2.0.'' OASIS Standard, March 2005. Document ID saml-bindings-2.0-os http://docs.oasis-open.org/security/saml/v2.0/saml-bindings-2.0-os.pdf * J. Hughes et al. ''Profiles for the OASIS Security Assertion Markup Language (SAML) V2.0.'' OASIS Standard, March 2005. Document ID saml-profiles-2.0-os http://docs.oasis-open.org/security/saml/v2.0/saml-profiles-2.0-os.pdf * S. Cantor et al. ''Metadata for the OASIS Security Assertion Markup Language (SAML) V2.0.'' OASIS Standard, March 2005. Document ID saml-metadata-2.0-os http://docs.oasis-open.org/security/saml/v2.0/saml-metadata-2.0-os.pdf Except for historical references to the original SAML V2.0 Metadata Standard, the following footnotes point to SAML V2.0 specifications with errata. The latter specifications are fully inclusive of all errata approved by the OASIS Security Services (SAML) Technical Committee since the SAML V2.0 standards were published in March 2005. Please refer to thOASIS SAML Wiki
for the most recent version of any SAML specification.
Committee specifications post-2005
This is a small subset of the "Post-V2.0" committee specifications published by the OASIS Security Services (SAML) Technical Committee. Please refer to thOASIS SAML Wiki
for the most recent version of any SAML specification.
Miscellaneous
{{OASIS Standards XML-based standards Metadata standards