Parental controls on:
[Wikipedia]
[Google]
[Amazon]
 Parental controls are features which may be included in
Parental controls are features which may be included in
 Parental controls are features which may be included in
Parental controls are features which may be included in digital television
Digital television (DTV) is the transmission of television signals using Digital signal, digital encoding, in contrast to the earlier analog television technology which used analog signals. At the time of its development it was considered an ...
services, computers and video games, mobile devices
A mobile device or handheld device is a computer small enough to hold and operate in hand. Mobile devices are typically battery-powered and possess a flat-panel display and one or more built-in input devices, such as a touchscreen or keypad. Mod ...
and software
Software consists of computer programs that instruct the Execution (computing), execution of a computer. Software also includes design documents and specifications.
The history of software is closely tied to the development of digital comput ...
to assist parents
A parent is either the progenitor of a child or, in humans, it can refer to a caregiver or legal guardian, generally called an adoptive parent or step-parent. Parents who are progenitors are first-degree relatives and have 50% genetic meet. ...
in their ability to restrict certain content viewable by their children
A child () is a human being between the stages of childbirth, birth and puberty, or between the Development of the human body, developmental period of infancy and puberty. The term may also refer to an unborn human being. In English-speaking ...
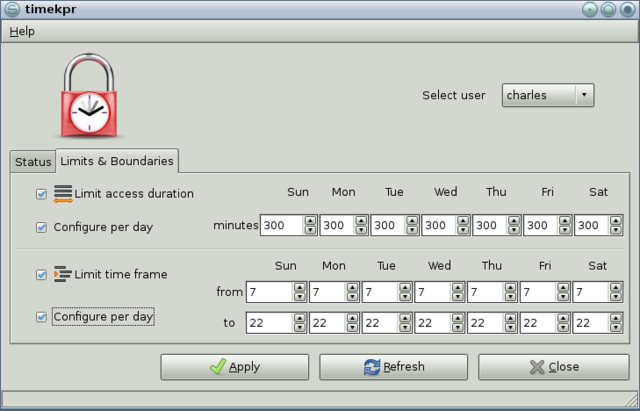
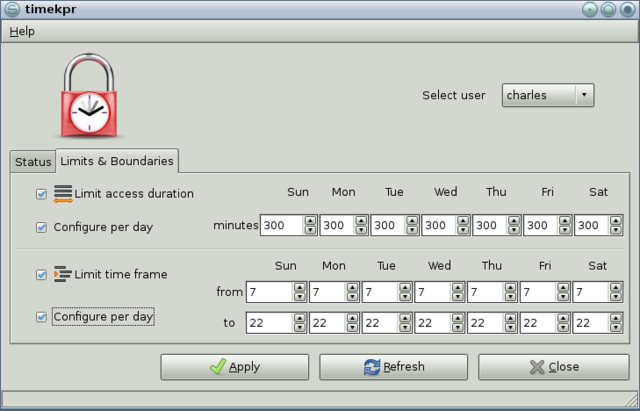
. This may be content they deem inappropriate for their age, maturity level or feel is aimed more at an adult audience. Parental controls fall into roughly four categories: '' content filters'', which limit access to age inappropriate content; ''usage controls'', which constrain the usage of these devices such as placing time-limits on usage or forbidding certain types of usage; ''computer usage management tools'', which enforces the use of certain software; and '' monitoring'', which can track location and activity when using the devices.
Content filters were the first popular type of parental controls to limit access to Internet
The Internet (or internet) is the Global network, global system of interconnected computer networks that uses the Internet protocol suite (TCP/IP) to communicate between networks and devices. It is a internetworking, network of networks ...
content. Television station
A television station is a set of equipment managed by a business, organisation or other entity such as an amateur television (ATV) operator, that transmits video content and audio content via radio waves directly from a transmitter on the earth's s ...
s also began to introduce V-Chip technology to limit access to television content. Modern usage controls are able to restrict a range of explicit content such as explicit songs and movies. They are also able to turn devices off during specific times of the day, limiting the volume output of devices, and with GPS technology becoming affordable, it is now possible to easily locate devices such as mobile phones. UNICEF emphases the responsibility of parents and teachers in this role.
The demand for parental control methods that restrict content has increased over the decades due to the rising availability of the Internet. A 2014 ICM survey showed that almost a quarter of people under the age of 12 had been exposed to online pornography. Restricting especially helps in cases when children are exposed to inappropriate content by accident. Monitoring may be effective for lessening acts of cyberbullying
Cyberbullying (cyberharassment or online bullying) is a form of bullying or harassment using electronic means. Since the 2000s, it has become increasingly common, especially among teenagers and adolescents, due to young people's increased u ...
within the internet. It is unclear whether parental controls will affect online harassment in children, as little is known about the role the family plays in protecting children from undesirable experiences online. Psychologically, cyberbullying could be more harmful to the victim than traditional bullying. Studies done in the past have shown that about 75% of adolescents were subjected to cyberbullying. A lack of parental controls in the household could enable kids to be a part of cyberbullying or be the victim of cyberbullying.
Overview
Behavioral control consists of controlling the amount of time a child spends online, or how much the child can view. Psychological control involves parents trying to influence children's behavior. Several techniques exist for creating parental controls for blocking websites. Add-on parental control software may monitorAPI
An application programming interface (API) is a connection between computers or between computer programs. It is a type of software interface, offering a service to other pieces of software. A document or standard that describes how to build ...
in order to observe applications such as a web browser or Internet chat application and to intervene according to certain criteria, such as a match in a database of banned words. Virtually all parental control software includes a password or other form of authentication
Authentication (from ''authentikos'', "real, genuine", from αὐθέντης ''authentes'', "author") is the act of proving an Logical assertion, assertion, such as the Digital identity, identity of a computer system user. In contrast with iden ...
to prevent unauthorized users from disabling it.
Techniques involving a proxy server are also used. A web browser
A web browser, often shortened to browser, is an application for accessing websites. When a user requests a web page from a particular website, the browser retrieves its files from a web server and then displays the page on the user's scr ...
is set to send requests for web content to the proxy server rather than directly to the web server intended. The proxy server then fetches the web page from the server on the browser's behalf and passes on the content to the browser. Proxy servers can inspect the data being sent and received and intervene depending on various criteria relating to content of the page or the URL being requested, for example, using a database
In computing, a database is an organized collection of data or a type of data store based on the use of a database management system (DBMS), the software that interacts with end users, applications, and the database itself to capture and a ...
of banned words or banned URLs. The proxy method's major disadvantage is that it requires that the client application to be configured to utilize the proxy, and if it is possible for the user to reconfigure applications to access the Internet directly rather than going through the proxy, then this control is easily bypassed. Proxy servers themselves may be used to circumvent parental controls. There are other techniques used to bypass parental controls.
The computer usage management method, unlike content filters, is focused on empowering the parents to balance the computing environment for children by regulating gaming. The main idea of these applications is to allow parents to introduce a learning component into the computing time of children, who must earn gaming time while working through educational contents.
Network-based parental control devices have been develop which work as a firewall router using packet filtering, DNS response policy zone (RPZ) and deep packet inspection
Deep packet inspection (DPI) is a type of data processing that inspects in detail the data (Network packet, packets) being sent over a computer network, and may take actions such as alerting, blocking, re-routing, or logging it accordingly. Deep ...
(DPI) methods to block inappropriate web content. These methods have been used in commercial and governmental communication networks. Another form of these devices made for home networks has been developed. These devices plug into the home router and create a new wireless network, which is specifically designed for kids to connect to.
Parental controls on mobile devices
The increased use of mobile devices with fully featured web browsers and downloadable applications has created a demand for parental controls on these devices. Some examples of mobile devices that contain parental controls include cell phones, tablets, and e-readers. In November 2007, Verizon was the first carrier to offer age-appropriate content filters as well as the first to offer generic content filters, recognizing that mobile devices were used to access all manner of content from movies and music to short-code programs and websites. In June 2009, in iPhone OS 3.0, Apple was the first company to provide a built-in mechanism on mobile devices to create age brackets for users that would block unwanted applications from being downloaded to the device. In the following years, the developers of all major operating systems have presented in-built tools for parental control, including Linux, Android, Windows, and even the more business-oriented platform Blackberry. There are also applications that allow parents to monitor real-time conversations on their children's phone via access to text messages, browser history, and application history. An example of one of these isTrend Micro
is an American-Japanese cyber security software company. The company has globally dispersed R&D in 16 locations across every continent excluding Antarctica. The company develops enterprise security software for servers, containers, and cloud ...
which not only offers protection from viruses, but also offers parental controls to phones and tablets of almost all brands. Most of these offer the ability to add extra features to parental controls. These apps have the features mobile devices already have, but have additional features such as, being able to monitor and filter texts/calls, protection while surfing the web, and denied access to specific websites. Applications of this sort have created a rising competition in their market.
Mobile device software enables parents to restrict which applications their child can access while also allowing parents to monitor text messages, phone logs, MMS pictures, and other transactions occurring on their child's mobile device; to enable parents to set a time limit on the usage of mobile devices; and to track the exact location of their children as well as monitor calls and the content of texts. This software also allows parents to monitor social media accounts. Parents are able to view posts, pictures, and any interactions in real time. Another function of this software is to keep track of bullying
Bullying is the use of force, coercion, Suffering, hurtful teasing, comments, or threats, in order to abuse, aggression, aggressively wikt:domination, dominate, or intimidate one or more others. The behavior is often repeated and habitual. On ...
.
Most internet service providers offer no-cost filtering options to limit internet browsing options and block unsuitable content. Implementing parental controls and discussing internet safety are useful steps to protect children from inappropriate information.
Although parental controls can protect children, they also come with some negative factors. Children's anxiety may increase due to parental controls. In extreme cases, a child may become so angry that they destroy their device, defeating the purpose of parental controls entirely. In that case, it might be a better idea to forgo installing parental controls.
Bypassing parental controls
* If the filtering software is located locally within the computer, all Internet software can be easily bypassed by booting up the computer in question from alternative media, with an alternative operating system or (onWindows
Windows is a Product lining, product line of Proprietary software, proprietary graphical user interface, graphical operating systems developed and marketed by Microsoft. It is grouped into families and subfamilies that cater to particular sec ...
) in Safe Mode
Safe mode is a diagnosis, diagnostic mode of a computer operating system (OS). It can also refer to a mode of operation by application software. ''Safe mode'' is intended to help fix most, if not all, problems within an operating system. It is a ...
. However, if the computer's BIOS
In computing, BIOS (, ; Basic Input/Output System, also known as the System BIOS, ROM BIOS, BIOS ROM or PC BIOS) is a type of firmware used to provide runtime services for operating systems and programs and to perform hardware initialization d ...
is configured to disallow booting from removable media, and if changes to the BIOS are prohibited without proper authentication, then booting into an alternative operating system is not available without circumventing BIOS security by partially disassembling the computer and resetting BIOS configuration using a button or jumper, or removing and replacing the internal button cell battery.
* Using external proxy servers or other servers. The user sends requests to the external server which retrieves content on the user's behalf. Filtering software may then never be able to know which URLs the user is accessing, as all communications are with the one external server and filtering software never sees any communications with the web servers from which content really originated. To counter this, filtering software may also block access to popular proxies. Additionally, filtering systems which only permit access to a set of allowed URLs (whitelisting) will not permit access anything outside this list, including proxy servers.
* Resetting passwords using exploits
* Modifying the software's files
* Brute-force attack
In cryptography, a brute-force attack or exhaustive key search is a cryptanalytic attack that consists of an attacker submitting many possible keys or passwords with the hope of eventually guessing correctly. This strategy can theoretically be ...
s on software passwords
* 'Incognito/InPrivate' modes with the 'image' tab: Users, parental control software, and parental control routers may use 'safe search' (SafeSearch
SafeSearch is a feature in Google Search and Google Images, and later, Bing, that acts as an automated filter of pornography and other potentially offensive and inappropriate content.
History
On November 11th, 2009, Google introduced the abilit ...
) to enforce filtering at most major search engines. However, in most browsers a user may select 'Incognito' or 'InPrivate' browsing, enter search terms for content, and select the 'image' tab to effectively bypass 'safe search' and many parental control filters. See below for router based considerations and solutions.
Filtering that occurs outside of the individuals computer (such as at the router) cannot be bypassed using the above methods (except for 'Incognito/InPrivate' modes). However,
* The major search engines cache and serve content on their own servers. As a result, domain filters such as many third party DNS servers, also fail to filter the 'Incognito/InPrivate' with 'image' tab.
* Most commercially available routers with parental controls do not enforce safe search at the router, and therefore do not filter the 'Incognito/InPrivate' with 'image' tab.
Criticism
While parental controls have been added to various electronic media and have increased in popularity, the question has been raised if they are enough to protect and deter children from exposure to inappropriate material. It has been speculated by researchers that the strict focus on control may hinder a child's ability to learn self-governing skills and restricting the growth of open communication between parent and child.Operating systems with parental controls
Below is a list of popularoperating system
An operating system (OS) is system software that manages computer hardware and software resources, and provides common daemon (computing), services for computer programs.
Time-sharing operating systems scheduler (computing), schedule tasks for ...
s which currently have built-in parental control features:
*Android operating system
Android is an operating system based on a modified version of the Linux kernel and other open-source software, designed primarily for touchscreen-based mobile devices such as smartphones and tablets. Android has historically been developed by ...
*iOS
Ios, Io or Nio (, ; ; locally Nios, Νιός) is a Greek island in the Cyclades group in the Aegean Sea. Ios is a hilly island with cliffs down to the sea on most sides. It is situated halfway between Naxos and Santorini. It is about long an ...
( 12 or later)
*macOS
macOS, previously OS X and originally Mac OS X, is a Unix, Unix-based operating system developed and marketed by Apple Inc., Apple since 2001. It is the current operating system for Apple's Mac (computer), Mac computers. With ...
( 10.3 and later)
* DoudouLinux (built-in web filter)
* sabily (built-in web filter)
*Ubuntu Christian edition (built-in web filter)
*Windows
Windows is a Product lining, product line of Proprietary software, proprietary graphical user interface, graphical operating systems developed and marketed by Microsoft. It is grouped into families and subfamilies that cater to particular sec ...
(Vista
Vista may refer to:
Software
*Windows Vista, the line of Microsoft Windows client operating systems released in 2006 and 2007
* VistA, (Veterans Health Information Systems and Technology Architecture) a medical records system of the United States ...
, 7, 10 and later)
*ChromeOS
ChromeOS, sometimes styled as chromeOS and formerly styled as Chrome OS, is an operating system designed and developed by Google. It is derived from the open-source operating system and uses the Google Chrome web browser as its principal user ...
(65 or later)
See also
*Adultism
Adultism is a bias or prejudice against children or youth. It has been defined as "the power adults have over children", or the abuse thereof, as well as "prejudice and accompanying systematic discrimination against young people", and "bias tow ...
* David Burt David Burt may refer to:
* David Raitt Robertson Burt (1899–1983), Scottish zoologist
* David Burt (cricketer) (1901–?), New Zealand cricketer
* Dave Burt (born 1937), Australian rules footballer
* David Burt (actor) (born 1953), British actor
...
* Internet censorship
Internet censorship is the legal control or suppression of what can be accessed, published, or viewed on the Internet. Censorship is most often applied to specific internet domains (such as ''Wikipedia.org'', for example) but exceptionally may ...
* List of parental control software
* Motion picture rating system
A motion picture content rating system classifies films based on their suitability for audiences due to their treatment of issues such as sex, violence, or substance abuse, their use of profanity, or other matters typically deemed unsuitable for ...
* Television rating system
* Videogame Rating Council
* Retina-X Studios
* Smart Sheriff
* Restricted to Adults
References
{{DEFAULTSORT:Parental Controls Internet safety Parenting Content-control software