Maze Generation on:
[Wikipedia]
[Google]
[Amazon]
Maze generation algorithms are automated methods for the creation of
 A maze can be generated by starting with a predetermined arrangement of cells (most commonly a rectangular grid but other arrangements are possible) with wall sites between them. This predetermined arrangement can be considered as a
A maze can be generated by starting with a predetermined arrangement of cells (most commonly a rectangular grid but other arrangements are possible) with wall sites between them. This predetermined arrangement can be considered as a
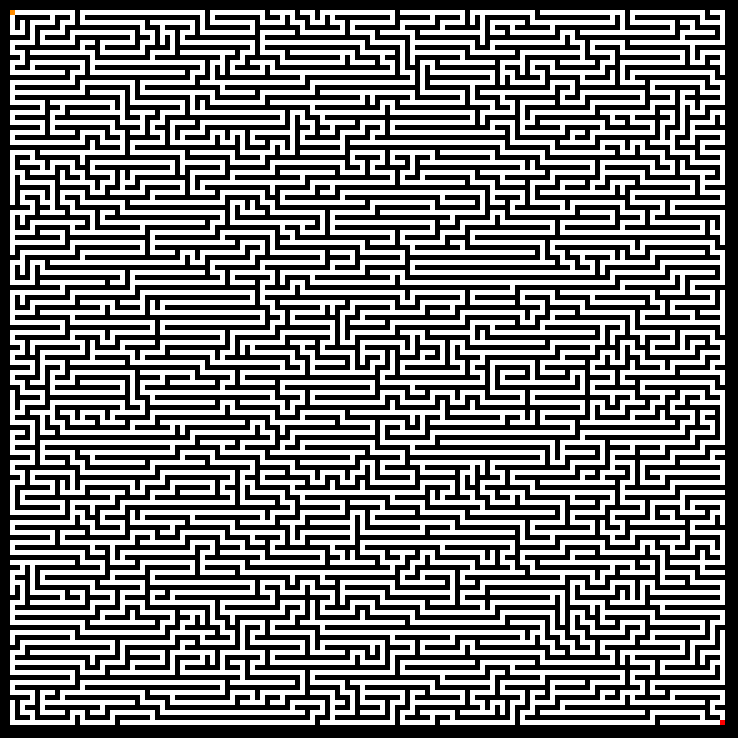 Mazes generated with a depth-first search have a low branching factor and contain many long corridors, because the algorithm explores as far as possible along each branch before backtracking.
Mazes generated with a depth-first search have a low branching factor and contain many long corridors, because the algorithm explores as far as possible along each branch before backtracking.
 All the above algorithms have biases of various sorts: depth-first search is biased toward long corridors, while Kruskal's/Prim's algorithms are biased toward many short dead ends. Wilson's algorithm, on the other hand, generates an ''unbiased'' sample from the uniform distribution over all mazes, using
All the above algorithms have biases of various sorts: depth-first search is biased toward long corridors, while Kruskal's/Prim's algorithms are biased toward many short dead ends. Wilson's algorithm, on the other hand, generates an ''unbiased'' sample from the uniform distribution over all mazes, using
 This is a simple and fast way to generate a maze.
On each iteration, this algorithm creates a maze twice the size by copying itself 3 times. At the end of each iteration, 3 paths are opened between the 4 smaller mazes.
The advantage of this method is that it is very fast. The downside is that it is not possible to get a maze of a chosen size - but various tricks can be used to get around this problem.
This is a simple and fast way to generate a maze.
On each iteration, this algorithm creates a maze twice the size by copying itself 3 times. At the end of each iteration, 3 paths are opened between the 4 smaller mazes.
The advantage of this method is that it is very fast. The downside is that it is not possible to get a maze of a chosen size - but various tricks can be used to get around this problem.
 Other algorithms exist that require only enough memory to store one line of a 2D maze or one plane of a 3D maze. Eller's algorithm prevents loops by storing which cells in the current line are connected through cells in the previous lines, and never removes walls between any two cells already connected. The Sidewinder algorithm starts with an open passage along the entire top row, and subsequent rows consist of shorter horizontal passages with one connection to the passage above. The Sidewinder algorithm is trivial to solve from the bottom up because it has no upward dead ends. Given a starting width, both algorithms create perfect mazes of unlimited height.
Most maze generation algorithms require maintaining relationships between cells within it, to ensure the result will be solvable. Valid simply connected mazes can however be generated by focusing on each cell independently. A binary tree maze is a standard orthogonal maze where each cell always has a passage leading up or leading left, but never both. To create a binary tree maze, for each cell flip a coin to decide whether to add a passage leading up or left. Always pick the same direction for cells on the boundary, and the result will be a valid simply connected maze that looks like a
Other algorithms exist that require only enough memory to store one line of a 2D maze or one plane of a 3D maze. Eller's algorithm prevents loops by storing which cells in the current line are connected through cells in the previous lines, and never removes walls between any two cells already connected. The Sidewinder algorithm starts with an open passage along the entire top row, and subsequent rows consist of shorter horizontal passages with one connection to the passage above. The Sidewinder algorithm is trivial to solve from the bottom up because it has no upward dead ends. Given a starting width, both algorithms create perfect mazes of unlimited height.
Most maze generation algorithms require maintaining relationships between cells within it, to ensure the result will be solvable. Valid simply connected mazes can however be generated by focusing on each cell independently. A binary tree maze is a standard orthogonal maze where each cell always has a passage leading up or leading left, but never both. To create a binary tree maze, for each cell flip a coin to decide whether to add a passage leading up or left. Always pick the same direction for cells on the boundary, and the result will be a valid simply connected maze that looks like a  A related form of flipping a coin for each cell is to create an image using a random mix of forward slash and backslash characters. This doesn't generate a valid simply connected maze, but rather a selection of closed loops and unicursal passages. The manual for the
A related form of flipping a coin for each cell is to create an image using a random mix of forward slash and backslash characters. This doesn't generate a valid simply connected maze, but rather a selection of closed loops and unicursal passages. The manual for the
Think Labyrinth: Maze algorithms
(details on these and other maze generation algorithms)
* ttps://franciscouzo.github.io/maze/ Maze generation visualization
Java implementation of Prim's algorithm
Implementations of DFS maze creation algorithm
in multiple languages at Rosetta Code
Armin Reichert: 34 maze algorithms in Java 8, with demo application
Coding Challenge #10.1: Maze Generator with p5.js - Part 1: Maze generation algorithm in JavaScript with p5
Maze Generator by Charles Bond, COMPUTE! Magazine, December 1981
Mazes Algorithms Random graphs Articles containing video clips
maze
A maze is a path or collection of paths, typically from an entrance to a goal. The word is used to refer both to branching tour puzzles through which the solver must find a route, and to simpler non-branching ("unicursal") patterns that lead ...
s.
Graph theory based methods
 A maze can be generated by starting with a predetermined arrangement of cells (most commonly a rectangular grid but other arrangements are possible) with wall sites between them. This predetermined arrangement can be considered as a
A maze can be generated by starting with a predetermined arrangement of cells (most commonly a rectangular grid but other arrangements are possible) with wall sites between them. This predetermined arrangement can be considered as a connected graph
In mathematics and computer science, connectivity is one of the basic concepts of graph theory: it asks for the minimum number of elements (nodes or edges) that need to be removed to separate the remaining nodes into two or more isolated subgrap ...
with the edges representing possible wall sites and the nodes representing cells. The purpose of the maze generation algorithm can then be considered to be making a subgraph in which it is challenging to find a route between two particular nodes.
If the subgraph is not connected
Connected may refer to:
Film and television
* ''Connected'' (2008 film), a Hong Kong remake of the American movie ''Cellular''
* '' Connected: An Autoblogography About Love, Death & Technology'', a 2011 documentary film
* ''Connected'' (2015 TV ...
, then there are regions of the graph that are wasted because they do not contribute to the search space. If the graph contains loops, then there may be multiple paths between the chosen nodes. Because of this, maze generation is often approached as generating a random spanning tree
In the mathematical field of graph theory, a spanning tree ''T'' of an undirected graph ''G'' is a subgraph that is a tree which includes all of the vertices of ''G''. In general, a graph may have several spanning trees, but a graph that is no ...
. Loops, which can confound naive maze solvers, may be introduced by adding random edges to the result during the course of the algorithm.
The animation shows the maze generation steps for a
graph that is not on a rectangular grid.
First, the computer creates a random planar graph
In graph theory, a planar graph is a graph (discrete mathematics), graph that can be graph embedding, embedded in the plane (geometry), plane, i.e., it can be drawn on the plane in such a way that its edges intersect only at their endpoints. ...
G
shown in blue, and its dual
Dual or Duals may refer to:
Paired/two things
* Dual (mathematics), a notion of paired concepts that mirror one another
** Dual (category theory), a formalization of mathematical duality
*** see more cases in :Duality theories
* Dual number, a nu ...
F
shown in yellow. Second, the computer traverses F using a chosen
algorithm, such as a depth-first search, coloring the path red.
During the traversal, whenever a red edge crosses over a blue edge,
the blue edge is removed.
Finally, when all vertices of F have been visited, F is erased
and two edges from G, one for the entrance and one for the exit, are removed.
Randomized depth-first search
This algorithm, also known as the "recursive backtracker" algorithm, is a randomized version of thedepth-first search
Depth-first search (DFS) is an algorithm for traversing or searching tree or graph data structures. The algorithm starts at the root node (selecting some arbitrary node as the root node in the case of a graph) and explores as far as possible al ...
algorithm.
Frequently implemented with a stack
Stack may refer to:
Places
* Stack Island, an island game reserve in Bass Strait, south-eastern Australia, in Tasmania’s Hunter Island Group
* Blue Stack Mountains, in Co. Donegal, Ireland
People
* Stack (surname) (including a list of people ...
, this approach is one of the simplest ways to generate a maze using a computer. Consider the space for a maze being a large grid of cells (like a large chess board), each cell starting with four walls. Starting from a random cell, the computer then selects a random neighbouring cell that has not yet been visited. The computer removes the wall between the two cells and marks the new cell as visited, and adds it to the stack to facilitate backtracking. The computer continues this process, with a cell that has no unvisited neighbours being considered a dead-end. When at a dead-end it backtracks through the path until it reaches a cell with an unvisited neighbour, continuing the path generation by visiting this new, unvisited cell (creating a new junction). This process continues until every cell has been visited, causing the computer to backtrack all the way back to the beginning cell. We can be sure every cell is visited.
As given above this algorithm involves deep recursion which may cause stack overflow issues on some computer architectures. The algorithm can be rearranged into a loop by storing backtracking information in the maze itself. This also provides a quick way to display a solution, by starting at any given point and backtracking to the beginning.
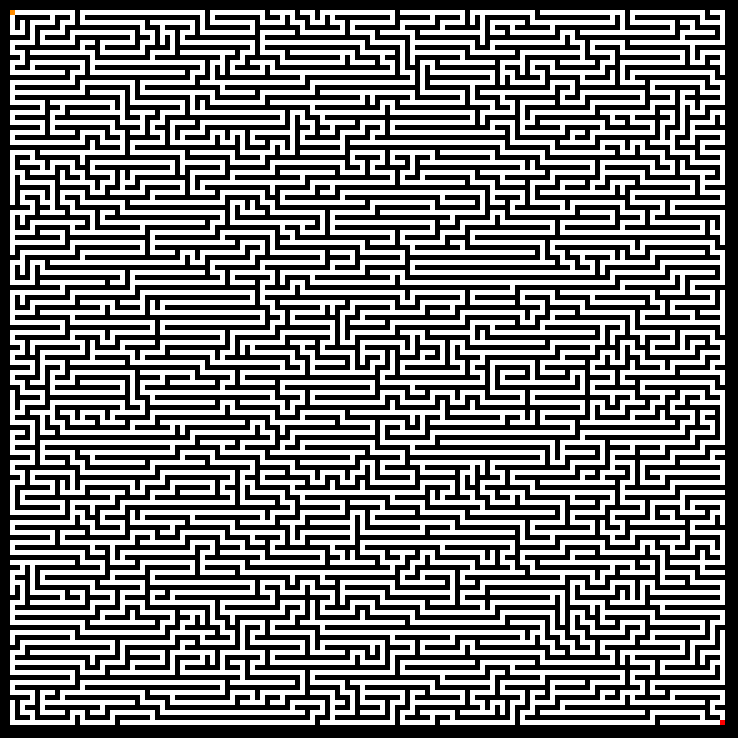 Mazes generated with a depth-first search have a low branching factor and contain many long corridors, because the algorithm explores as far as possible along each branch before backtracking.
Mazes generated with a depth-first search have a low branching factor and contain many long corridors, because the algorithm explores as far as possible along each branch before backtracking.
Recursive implementation
Thedepth-first search
Depth-first search (DFS) is an algorithm for traversing or searching tree or graph data structures. The algorithm starts at the root node (selecting some arbitrary node as the root node in the case of a graph) and explores as far as possible al ...
algorithm of maze generation is frequently implemented using backtracking
Backtracking is a class of algorithms for finding solutions to some computational problems, notably constraint satisfaction problems, that incrementally builds candidates to the solutions, and abandons a candidate ("backtracks") as soon as it de ...
. This can be described with a following recursive
Recursion occurs when the definition of a concept or process depends on a simpler or previous version of itself. Recursion is used in a variety of disciplines ranging from linguistics to logic. The most common application of recursion is in m ...
routine:
# Given a current cell as a parameter
# Mark the current cell as visited
# While the current cell has any unvisited neighbour cells
## Choose one of the unvisited neighbours
## Remove the wall between the current cell and the chosen cell
## Invoke the routine recursively for the chosen cell
which is invoked once for any initial cell in the area.
Iterative implementation (with stack)
A disadvantage of the first approach is a large depth ofrecursion
Recursion occurs when the definition of a concept or process depends on a simpler or previous version of itself. Recursion is used in a variety of disciplines ranging from linguistics to logic. The most common application of recursion is in m ...
– in the worst case, the routine may need to recur on every cell of the area being processed, which may exceed the maximum recursion stack depth in many environments. As a solution, the same backtracking method can be implemented with an explicit stack
Stack may refer to:
Places
* Stack Island, an island game reserve in Bass Strait, south-eastern Australia, in Tasmania’s Hunter Island Group
* Blue Stack Mountains, in Co. Donegal, Ireland
People
* Stack (surname) (including a list of people ...
, which is usually allowed to grow much bigger with no harm.
# Choose the initial cell, mark it as visited and push it to the stack
# While the stack is not empty
## Pop a cell from the stack and make it a current cell
## If the current cell has any neighbours which have not been visited
### Push the current cell to the stack
### Choose one of the unvisited neighbours
### Remove the wall between the current cell and the chosen cell
### Mark the chosen cell as visited and push it to the stack
Iterative randomized Kruskal's algorithm (with sets)
This algorithm is a randomized version ofKruskal's algorithm
Kruskal's algorithm finds a minimum spanning forest of an undirected edge-weighted graph. If the graph is connected, it finds a minimum spanning tree. It is a greedy algorithm that in each step adds to the forest the lowest-weight edge that ...
.
# Create a list of all walls, and create a set for each cell, each containing just that one cell.
# For each wall, in some random order:
## If the cells divided by this wall belong to distinct sets:
### Remove the current wall.
### Join the sets of the formerly divided cells.
There are several data structures that can be used to model the sets of cells. An efficient implementation using a disjoint-set data structure
In computer science, a disjoint-set data structure, also called a union–find data structure or merge–find set, is a data structure that stores a collection of Disjoint sets, disjoint (non-overlapping) Set (mathematics), sets. Equivalently, it ...
can perform each union and find operation on two sets in nearly constant amortized time
In computer science, amortized analysis is a method for analyzing a given algorithm's complexity, or how much of a resource, especially time or memory, it takes to execute. The motivation for amortized analysis is that looking at the worst-case ...
(specifically, time; for any plausible value of ), so the running time of this algorithm is essentially proportional to the number of walls available to the maze.
It matters little whether the list of walls is initially randomized or if a wall is randomly chosen from a nonrandom list, either way is just as easy to code.
Because the effect of this algorithm is to produce a minimal spanning tree from a graph with equally weighted edges, it tends to produce regular patterns which are fairly easy to solve.
Iterative randomized Prim's algorithm (without stack, without sets)
This algorithm is a randomized version ofPrim's algorithm
In computer science, Prim's algorithm is a greedy algorithm that finds a minimum spanning tree for a Weighted graph, weighted undirected graph. This means it finds a subset of the edge (graph theory), edges that forms a Tree (graph theory), tree ...
.
# Start with a grid full of walls.
# Pick a cell, mark it as part of the maze. Add the walls of the cell to the wall list.
# While there are walls in the list:
## Pick a random wall from the list. If only one of the cells that the wall divides is visited, then:
### Make the wall a passage and mark the unvisited cell as part of the maze.
### Add the neighboring walls of the cell to the wall list.
## Remove the wall from the list.
Note that simply running classical Prim's on a graph with random edge weights would create mazes stylistically identical to Kruskal's, because they are both minimal spanning tree algorithms. Instead, this algorithm introduces stylistic variation because the edges closer to the starting point have a lower effective weight.
Modified version
Although the classical Prim's algorithm keeps a list of edges, for maze generation we could instead maintain a list of adjacent cells. If the randomly chosen cell has multiple edges that connect it to the existing maze, select one of these edges at random. This will tend to branch slightly more than the edge-based version above.Simplified version
The algorithm can be simplified even further by randomly selecting cells that neighbour already-visited cells, rather than keeping track of the weights of all cells or edges. It will usually be relatively easy to find the way to the starting cell, but hard to find the way anywhere else.Wilson's algorithm
 All the above algorithms have biases of various sorts: depth-first search is biased toward long corridors, while Kruskal's/Prim's algorithms are biased toward many short dead ends. Wilson's algorithm, on the other hand, generates an ''unbiased'' sample from the uniform distribution over all mazes, using
All the above algorithms have biases of various sorts: depth-first search is biased toward long corridors, while Kruskal's/Prim's algorithms are biased toward many short dead ends. Wilson's algorithm, on the other hand, generates an ''unbiased'' sample from the uniform distribution over all mazes, using loop-erased random walk
In mathematics, loop-erased random walk is a model for a random simple path with important applications in combinatorics, physics and quantum field theory. It is intimately connected to the uniform spanning tree, a model for a random tree. See al ...
s.
We begin the algorithm by initializing the maze with one cell chosen arbitrarily. Then we start at a new cell chosen arbitrarily, and perform a random walk until we reach a cell already in the maze—however, if at any point the random walk reaches its own path, forming a loop, we erase the loop from the path before proceeding. When the path reaches the maze, we add it to the maze. Then we perform another loop-erased random walk from another arbitrary starting cell, repeating until all cells have been filled.
This procedure remains unbiased no matter which method we use to arbitrarily choose starting cells. So we could always choose the first unfilled cell in (say) left-to-right, top-to-bottom order for simplicity.
Aldous-Broder algorithm
The Aldous-Broder algorithm also produces uniform spanning trees. However, it is one of the least efficient maze algorithms. # Pick a random cell as the current cell and mark it as visited. # While there are unvisited cells: ## Pick a random neighbour. ## If the chosen neighbour has not been visited: ### Remove the wall between the current cell and the chosen neighbour. ### Mark the chosen neighbour as visited. ## Make the chosen neighbour the current cell.Recursive division method
Mazes can be created with ''recursive division'', an algorithm which works as follows: Begin with the maze's space with no walls. Call this a chamber. Divide the chamber with a randomly positioned wall (or multiple walls) where each wall contains a randomly positioned passage opening within it. Then recursively repeat the process on the subchambers until all chambers are minimum sized. This method results in mazes with long straight walls crossing their space, making it easier to see which areas to avoid. For example, in a rectangular maze, build at random points two walls that are perpendicular to each other. These two walls divide the large chamber into four smaller chambers separated by four walls. Choose three of the four walls at random, and open a one cell-wide hole at a random point in each of the three. Continue in this manner recursively, until every chamber has a width of one cell in either of the two directions.Fractal Tessellation algorithm
 This is a simple and fast way to generate a maze.
On each iteration, this algorithm creates a maze twice the size by copying itself 3 times. At the end of each iteration, 3 paths are opened between the 4 smaller mazes.
The advantage of this method is that it is very fast. The downside is that it is not possible to get a maze of a chosen size - but various tricks can be used to get around this problem.
This is a simple and fast way to generate a maze.
On each iteration, this algorithm creates a maze twice the size by copying itself 3 times. At the end of each iteration, 3 paths are opened between the 4 smaller mazes.
The advantage of this method is that it is very fast. The downside is that it is not possible to get a maze of a chosen size - but various tricks can be used to get around this problem.
Simple algorithms
binary tree
In computer science, a binary tree is a tree data structure in which each node has at most two children, referred to as the ''left child'' and the ''right child''. That is, it is a ''k''-ary tree with . A recursive definition using set theor ...
, with the upper left corner its root. As with Sidewinder, the binary tree maze has no dead ends in the directions of bias.
 A related form of flipping a coin for each cell is to create an image using a random mix of forward slash and backslash characters. This doesn't generate a valid simply connected maze, but rather a selection of closed loops and unicursal passages. The manual for the
A related form of flipping a coin for each cell is to create an image using a random mix of forward slash and backslash characters. This doesn't generate a valid simply connected maze, but rather a selection of closed loops and unicursal passages. The manual for the Commodore 64
The Commodore 64, also known as the C64, is an 8-bit computing, 8-bit home computer introduced in January 1982 by Commodore International (first shown at the Consumer Electronics Show, January 7–10, 1982, in Las Vegas). It has been listed in ...
presents a BASIC program using this algorithm, using PETSCII
PETSCII (PET Standard Code of Information Interchange), also known as CBM ASCII, is the character set used in Commodore Business Machines' 8-bit home computers.
This character set was first used by the PET from 1977, and was subsequently use ...
diagonal line graphic characters instead for a smoother graphic appearance.
Cellular automaton algorithms
Certain types ofcellular automata
A cellular automaton (pl. cellular automata, abbrev. CA) is a discrete model of computation studied in automata theory. Cellular automata are also called cellular spaces, tessellation automata, homogeneous structures, cellular structures, tessel ...
can be used to generate mazes. Two well-known such cellular automata, Maze and Mazectric, have rulestrings B3/S12345 and B3/S1234. In the former, this means that cells survive from one generation to the next if they have at least one and at most five neighbours
''Neighbours'' is an Australian television soap opera that has aired since 18 March 1985. It was created by television executive Reg Watson. The Seven Network commissioned the show following the success of Watson's earlier soap '' Sons and ...
. In the latter, this means that cells survive if they have one to four neighbours. If a cell has exactly three neighbours, it is born. It is similar to Conway's Game of Life
The Game of Life, also known as Conway's Game of Life or simply Life, is a cellular automaton devised by the British mathematician John Horton Conway in 1970. It is a zero-player game, meaning that its evolution is determined by its initial ...
in that patterns that do not have a living cell adjacent to 1, 4, or 5 other living cells in any generation will behave identically to it. However, for large patterns, it behaves very differently from Life.
For a random starting pattern, these maze-generating cellular automata will evolve into complex mazes with well-defined walls outlining corridors. Mazecetric, which has the rule B3/S1234 has a tendency to generate longer and straighter corridors compared with Maze, with the rule B3/S12345. Since these cellular automaton rules are deterministic
Determinism is the metaphysical view that all events within the universe (or multiverse) can occur only in one possible way. Deterministic theories throughout the history of philosophy have developed from diverse and sometimes overlapping mo ...
, each maze generated is uniquely determined by its random starting pattern. This is a significant drawback since the mazes tend to be relatively predictable.
Like some of the graph-theory based methods described above, these cellular automata typically generate mazes from a single starting pattern; hence it will usually be relatively easy to find the way to the starting cell, but harder to find the way anywhere else.
See also
*Maze solving algorithm
A maze-solving algorithm is an algorithm, automated method for solving a maze. The random mouse, wall follower, Pledge, and Trémaux's algorithms are designed to be used inside the maze by a traveler with no prior knowledge of the maze, whereas th ...
* Self-avoiding walk
In mathematics, a self-avoiding walk (SAW) is a sequence of moves on a lattice (group), lattice (a lattice path) that does not visit the same point more than once. This is a special case of the graph theory, graph theoretical notion of a Path ( ...
* Brute-force search
In computer science, brute-force search or exhaustive search, also known as generate and test, is a very general problem-solving technique and algorithmic paradigm that consists of Iteration#Computing, systematically checking all possible candida ...
References
{{reflistExternal links
Think Labyrinth: Maze algorithms
(details on these and other maze generation algorithms)
* ttps://franciscouzo.github.io/maze/ Maze generation visualization
Java implementation of Prim's algorithm
Implementations of DFS maze creation algorithm
in multiple languages at Rosetta Code
Armin Reichert: 34 maze algorithms in Java 8, with demo application
Coding Challenge #10.1: Maze Generator with p5.js - Part 1: Maze generation algorithm in JavaScript with p5
Maze Generator by Charles Bond, COMPUTE! Magazine, December 1981
Mazes Algorithms Random graphs Articles containing video clips