Bomba (cryptography) on:
[Wikipedia]
[Google]
[Amazon]
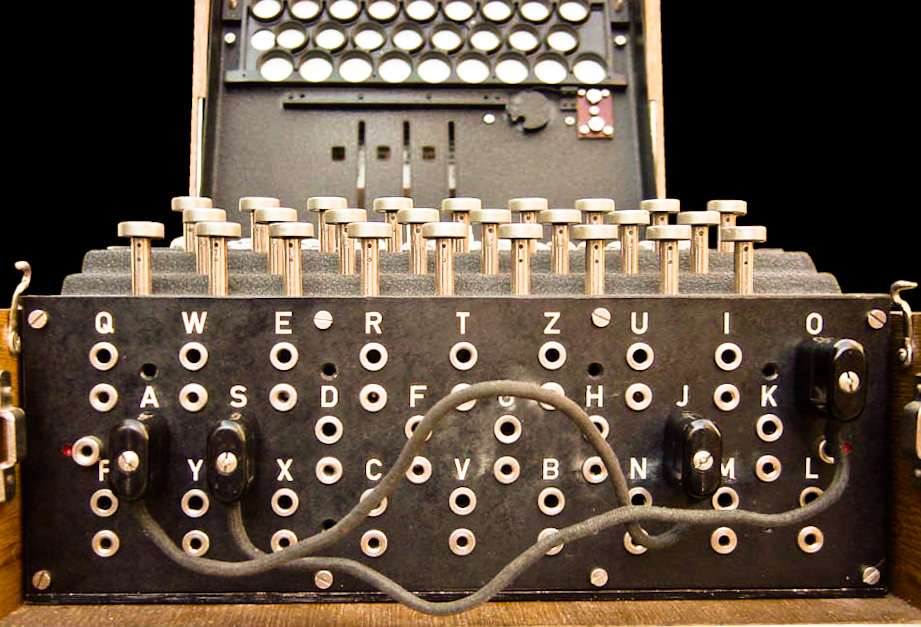
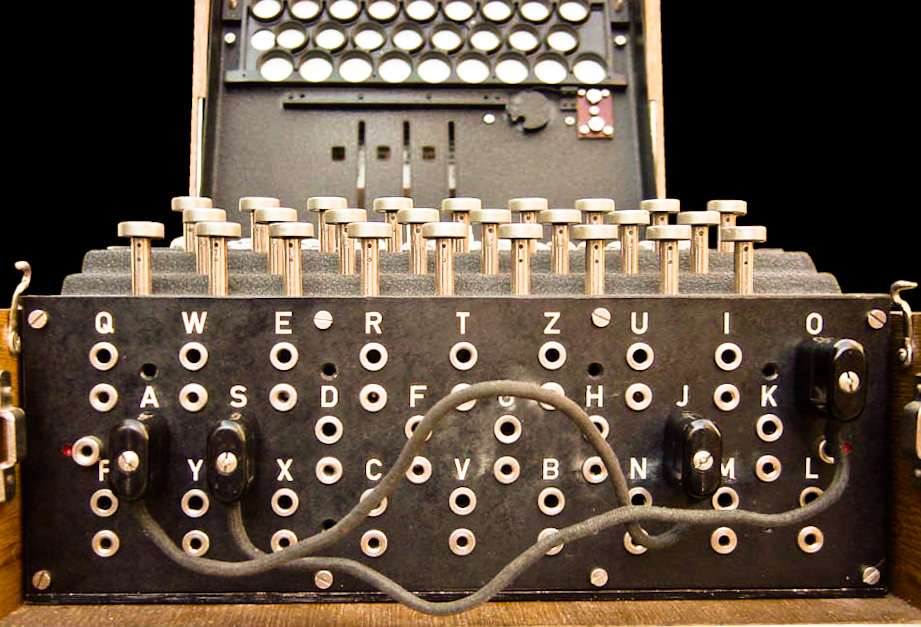
 The ''bomba'', or ''bomba kryptologiczna'' (Polish for "bomb" or "cryptologic bomb"), was a special-purpose machine designed around October 1938 by Polish Cipher Bureau cryptologist Marian Rejewski to break German Enigma-machine ciphers.
The ''bomba'', or ''bomba kryptologiczna'' (Polish for "bomb" or "cryptologic bomb"), was a special-purpose machine designed around October 1938 by Polish Cipher Bureau cryptologist Marian Rejewski to break German Enigma-machine ciphers.
 Using the knowledge that the first three letters of a message were the same as the second three, Polish mathematician– cryptologist Marian Rejewski was able to determine the internal wiring of the Enigma machine and thus to reconstruct the logical structure of the device. Only general traits of the machine were suspected, from the example of the commercial Enigma variant, which the Germans were known to have been using for diplomatic communications. The military versions were sufficiently different to present an entirely new problem. Having done that much, it was still necessary to check each of the potential daily keys to break an encrypted message (i.e., a "ciphertext"). With many thousands of such possible keys, and with the growing complexity of the Enigma machine and its keying procedures, this was becoming an increasingly daunting task.
In order to mechanize and speed up the process, Rejewski, a civilian mathematician working at the Polish General Staff's Cipher Bureau in
Using the knowledge that the first three letters of a message were the same as the second three, Polish mathematician– cryptologist Marian Rejewski was able to determine the internal wiring of the Enigma machine and thus to reconstruct the logical structure of the device. Only general traits of the machine were suspected, from the example of the commercial Enigma variant, which the Germans were known to have been using for diplomatic communications. The military versions were sufficiently different to present an entirely new problem. Having done that much, it was still necessary to check each of the potential daily keys to break an encrypted message (i.e., a "ciphertext"). With many thousands of such possible keys, and with the growing complexity of the Enigma machine and its keying procedures, this was becoming an increasingly daunting task.
In order to mechanize and speed up the process, Rejewski, a civilian mathematician working at the Polish General Staff's Cipher Bureau in
Bomba Kryptologiczna Simulator
David Link {{DISPLAYTITLE:''Bomba'' (cryptography) 1930s computers Computer-related introductions in 1938 Cryptanalytic devices One-of-a-kind computers Science and technology in Poland Cipher Bureau (Poland) Polish inventions
 The ''bomba'', or ''bomba kryptologiczna'' (Polish for "bomb" or "cryptologic bomb"), was a special-purpose machine designed around October 1938 by Polish Cipher Bureau cryptologist Marian Rejewski to break German Enigma-machine ciphers.
The ''bomba'', or ''bomba kryptologiczna'' (Polish for "bomb" or "cryptologic bomb"), was a special-purpose machine designed around October 1938 by Polish Cipher Bureau cryptologist Marian Rejewski to break German Enigma-machine ciphers.
Etymology
How the machine came to be called a "bomb" has been an object of fascination and speculation. One theory, most likely apocryphal, originated with Polish engineer and army officer Tadeusz Lisicki (who knew Rejewski and his colleague Henryk Zygalski in wartime Britain but was never associated with the Cipher Bureau). He claimed that Jerzy Różycki (the youngest of the three Enigma cryptologists, and who had died in a Mediterranean passenger-ship sinking in January 1942) named the "bomb" after an ice-cream dessert of that name. This story seems implausible, since Lisicki had not known Różycki. Rejewski himself stated that the device had been dubbed a "bomb" "for lack of a better idea". Perhaps the most credible explanation is given by a Cipher Bureau technician, Czesław Betlewski: workers at B.S.-4, the Cipher Bureau's German section, christened the machine a "bomb
A bomb is an explosive weapon that uses the exothermic reaction of an explosive material to provide an extremely sudden and violent release of energy. Detonations inflict damage principally through ground- and atmosphere-transmitted mechan ...
" (also, alternatively, a "washing machine
A washing machine (laundry machine, clothes washer, washer, or simply wash) is a machine designed to laundry, launder clothing. The term is mostly applied to machines that use water. Other ways of doing laundry include dry cleaning (which uses ...
" or a " mangle") because of the characteristic muffled noise that it produced when operating.
A top-secret U.S. Army report dated 15 June 1945 stated:
The U.S. Army's above description of the Polish ''bomba'' is both vague and inaccurate, as is clear from the device's description at the end of the second paragraph of the "History
History is the systematic study of the past, focusing primarily on the Human history, human past. As an academic discipline, it analyses and interprets evidence to construct narratives about what happened and explain why it happened. Some t ...
" section, below: "Each bomb... essentially constituted an ''electrically powered'' aggregate of ''six'' Enigmas..." Determination of a solution involved no disassembly ("a part... fall ngoff") of the device.
Background
The German Enigma used a combination key to control the operation of the machine: rotor order, which rotors to install, which ring setting for each rotor, which initial setting for each rotor, and the settings of the ''stecker'' plugboard. The rotor settings were trigrams (for example, "NJR") to indicate the way the operator was to set the machine. German Enigma operators were issued lists of these keys, one key for each day. For added security, however, each individual message was encrypted using an additional key modification. The operator randomly selected a trigram rotor setting for eachmessage
A message is a unit of communication that conveys information from a sender to a receiver. It can be transmitted through various forms, such as spoken or written words, signals, or electronic data, and can range from simple instructions to co ...
(for example, "PDN"). This message key would be typed twice ("PDNPDN") and encrypt
In cryptography, encryption (more specifically, encoding) is the process of transforming information in a way that, ideally, only authorized parties can decode. This process converts the original representation of the information, known as plai ...
ed, using the daily key (all the rest of those settings). At this point each operator would reset his machine to the message key, which would then be used for the rest of the message. Because the configuration of the Enigma's rotor set changed with each depression of a key, the repetition would not be obvious in the ciphertext
In cryptography, ciphertext or cyphertext is the result of encryption performed on plaintext using an algorithm, called a cipher. Ciphertext is also known as encrypted or encoded information because it contains a form of the original plaintext ...
since the same plaintext
In cryptography, plaintext usually means unencrypted information pending input into cryptographic algorithms, usually encryption algorithms. This usually refers to data that is transmitted or stored unencrypted.
Overview
With the advent of comp ...
letters would encrypt to different ciphertext letters. (For example, "PDNPDN" might become "ZRSJVL.")
This procedure, which seemed reasonably secure to the Germans, was nonetheless a cryptographic
Cryptography, or cryptology (from "hidden, secret"; and ''graphein'', "to write", or '' -logia'', "study", respectively), is the practice and study of techniques for secure communication in the presence of adversarial behavior. More gen ...
malpractice, since the first insights into Enigma encryption could be inferred from seeing how the same character string was encrypted differently two times in a row.
History
 Using the knowledge that the first three letters of a message were the same as the second three, Polish mathematician– cryptologist Marian Rejewski was able to determine the internal wiring of the Enigma machine and thus to reconstruct the logical structure of the device. Only general traits of the machine were suspected, from the example of the commercial Enigma variant, which the Germans were known to have been using for diplomatic communications. The military versions were sufficiently different to present an entirely new problem. Having done that much, it was still necessary to check each of the potential daily keys to break an encrypted message (i.e., a "ciphertext"). With many thousands of such possible keys, and with the growing complexity of the Enigma machine and its keying procedures, this was becoming an increasingly daunting task.
In order to mechanize and speed up the process, Rejewski, a civilian mathematician working at the Polish General Staff's Cipher Bureau in
Using the knowledge that the first three letters of a message were the same as the second three, Polish mathematician– cryptologist Marian Rejewski was able to determine the internal wiring of the Enigma machine and thus to reconstruct the logical structure of the device. Only general traits of the machine were suspected, from the example of the commercial Enigma variant, which the Germans were known to have been using for diplomatic communications. The military versions were sufficiently different to present an entirely new problem. Having done that much, it was still necessary to check each of the potential daily keys to break an encrypted message (i.e., a "ciphertext"). With many thousands of such possible keys, and with the growing complexity of the Enigma machine and its keying procedures, this was becoming an increasingly daunting task.
In order to mechanize and speed up the process, Rejewski, a civilian mathematician working at the Polish General Staff's Cipher Bureau in Warsaw
Warsaw, officially the Capital City of Warsaw, is the capital and List of cities and towns in Poland, largest city of Poland. The metropolis stands on the Vistula, River Vistula in east-central Poland. Its population is officially estimated at ...
, invented the ''"bomba kryptologiczna"'' (cryptologic bomb), probably in October 1938. Each bomb (six were built in Warsaw for the Cipher Bureau before September 1939) essentially constituted an electrically powered aggregate of six Enigmas and took the place of some one hundred workers.
The bomb method was based, like the Poles' earlier "grill" method, on the fact that the plug connections in the commutator ("plugboard") did not change all the letters. But while the grill method required unchanged ''pairs'' of letters, the bomb method required only unchanged letters. Hence it could be applied even though the number of plug connections in this period was between five and eight. In mid-November 1938, the bombs were ready, and the reconstructing of daily keys now took about two hours.Marian Rejewski, "Appendix C: Summary of Our Methods for Reconstructing ENIGMA and Reconstructing Daily Keys, and of German Efforts to Frustrate Those Methods in .
Up to July 25, 1939, the Poles had been breaking Enigma messages for over six and a half years without telling their French and British
British may refer to:
Peoples, culture, and language
* British people, nationals or natives of the United Kingdom, British Overseas Territories and Crown Dependencies.
* British national identity, the characteristics of British people and culture ...
allies. On December 15, 1938, two new rotors, IV and V, were introduced (three of the now five rotors being selected for use in the machine at a time). As Rejewski wrote in a 1979 critique of appendix 1, volume 1 (1979), of the official history of ''British Intelligence in the Second World War'', "we quickly found the iringswithin the ew rotors but heir
Inheritance is the practice of receiving private property, titles, debts, entitlements, privileges, rights, and obligations upon the death of an individual. The rules of inheritance differ among societies and have changed over time. Offi ...
introduction ..raised the number of possible sequences of drums from 6 to 60 ..and hence also raised tenfold the work of finding the keys. Thus the change was not qualitative but quantitative. We would have had to markedly increase the personnel to operate the bombs, to produce the perforated sheets (60 series of 26 sheets each were now needed, whereas up to the meeting on July 25, 1939, we had only two such series ready) and to manipulate the sheets."
Harry Hinsley suggested in ''British Intelligence in the Second World War'' that the Poles decided to share their Enigma-breaking techniques and equipment with the French and British in July 1939 because they had encountered insuperable technical difficulties. Rejewski rejected this: "No, it was not ryptologicdifficulties ..that prompted us to work with the British and French, but only the deteriorating political situation. If we had had no difficulties at all we would still, or even the more so, have shared our achievements with our allies as our contribution to the struggle against Germany."
See also
* *Notes
Works cited
*Further reading
* *External links
Bomba Kryptologiczna Simulator
David Link {{DISPLAYTITLE:''Bomba'' (cryptography) 1930s computers Computer-related introductions in 1938 Cryptanalytic devices One-of-a-kind computers Science and technology in Poland Cipher Bureau (Poland) Polish inventions