Wi-Fi () is a family of
wireless network
A wireless network is a computer network that uses wireless data connections between network nodes.
Wireless networking is a method by which homes, telecommunications networks and business installations avoid the costly process of introducing ...
protocols
Protocol may refer to:
Sociology and politics
* Protocol (politics), a formal agreement between nation states
* Protocol (diplomacy), the etiquette of diplomacy and affairs of state
* Etiquette, a code of personal behavior
Science and technology ...
, based on the
IEEE 802.11 family of standards, which are commonly used for
local area networking of devices and
Internet
The Internet (or internet) is the global system of interconnected computer networks that uses the Internet protocol suite (TCP/IP) to communicate between networks and devices. It is a '' network of networks'' that consists of private, p ...
access, allowing nearby digital devices to exchange data by
radio wave
Radio waves are a type of electromagnetic radiation with the longest wavelengths in the electromagnetic spectrum, typically with frequencies of 300 gigahertz ( GHz) and below. At 300 GHz, the corresponding wavelength is 1 mm (sho ...
s. These are the most widely used computer networks in the world, used globally in
home and small office networks to link
desktop
A desktop traditionally refers to:
* The surface of a desk (often to distinguish office appliances that fit on a desk, such as photocopiers and printers, from larger equipment covering its own area on the floor)
Desktop may refer to various compu ...
and
laptop
A laptop, laptop computer, or notebook computer is a small, portable personal computer (PC) with a screen and alphanumeric keyboard. Laptops typically have a clam shell form factor with the screen mounted on the inside of the upper li ...
computers,
tablet computer
A tablet computer, commonly shortened to tablet, is a mobile device, typically with a mobile operating system and touchscreen display processing circuitry, and a rechargeable battery in a single, thin and flat package. Tablets, being com ...
s,
smartphone
A smartphone is a portable computer device that combines mobile telephone and computing functions into one unit. They are distinguished from feature phones by their stronger hardware capabilities and extensive mobile operating systems, whi ...
s,
smart TV
A smart TV, also known as a connected TV (CTV), is a traditional television set with integrated Internet and interactive Web 2.0 features, which allows users to stream music and videos, browse the internet, and view photos. Smart TVs are a techn ...
s,
printers, and
smart speaker
A smart speaker is a type of loudspeaker and voice command device with an integrated virtual assistant that offers interactive actions and hands-free activation with the help of one "hot word" (or several "hot words"). Some smart speakers can a ...
s together and to a
wireless router
A wireless router is a device that performs the functions of a router and also includes the functions of a wireless access point. It is used to provide access to the Internet or a private computer network. Depending on the manufacturer and mode ...
to connect them to the Internet, and in
wireless access point
In computer networking, a wireless access point (WAP), or more generally just access point (AP), is a networking hardware device that allows other Wi-Fi devices to connect to a wired network. As a standalone device, the AP may have a wired ...
s in public places like coffee shops, hotels, libraries and airports to provide visitors with Internet access for their mobile devices.
''Wi-Fi'' is a trademark of the non-profit
Wi-Fi Alliance
The Wi-Fi Alliance is a non-profit organization that owns the Wi-Fi trademark. Manufacturers may use the trademark to brand products certified for Wi-Fi
interoperability.
History
Early 802.11 products suffered from interoperability problems be ...
, which restricts the use of the term ''Wi-Fi Certified'' to products that successfully complete
interoperability
Interoperability is a characteristic of a product or system to work with other products or systems. While the term was initially defined for information technology or systems engineering services to allow for information exchange, a broader defi ...
certification testing. the Wi-Fi Alliance consisted of more than 800 companies from around the world.
over 3.05 billion Wi-Fi enabled devices are shipped globally each year.
Wi-Fi uses multiple parts of the
IEEE 802
IEEE 802 is a family of Institute of Electrical and Electronics Engineers (IEEE) standards for local area networks (LAN), personal area network (PAN), and metropolitan area networks (MAN). The IEEE 802 LAN/MAN Standards Committee (LMSC) maintai ...
protocol
Protocol may refer to:
Sociology and politics
* Protocol (politics), a formal agreement between nation states
* Protocol (diplomacy), the etiquette of diplomacy and affairs of state
* Etiquette, a code of personal behavior
Science and technology
...
family and is designed to interwork seamlessly with its wired sibling,
Ethernet
Ethernet () is a family of wired computer networking technologies commonly used in local area networks (LAN), metropolitan area networks (MAN) and wide area networks (WAN). It was commercially introduced in 1980 and first standardized in 1 ...
. Compatible devices can network through
wireless access point
In computer networking, a wireless access point (WAP), or more generally just access point (AP), is a networking hardware device that allows other Wi-Fi devices to connect to a wired network. As a standalone device, the AP may have a wired ...
s to each other as well as to wired devices and the Internet. The different versions of Wi-Fi are specified by various IEEE 802.11 protocol standards, with the different radio technologies determining radio bands, and the maximum ranges, and speeds that may be achieved. Wi-Fi most commonly uses the
UHF
Ultra high frequency (UHF) is the ITU designation for radio frequencies in the range between 300 megahertz (MHz) and 3 gigahertz (GHz), also known as the decimetre band as the wavelengths range from one meter to one tenth of a meter (on ...
and
SHF radio bands; these bands are subdivided into multiple channels. Channels can be shared between networks but, within range, only one transmitter can transmit on a channel at a time.

Wi-Fi's radio bands have relatively high absorption and work best for
line-of-sight use. Many common obstructions such as walls, pillars, home appliances, etc. may greatly reduce range, but this also helps minimize interference between different networks in crowded environments. An access point range of about indoors while some access points claim up to a range outdoors. Hotspot coverage can be as small as a single room with walls that block radio waves, or as large as many square kilometres using many overlapping access points with
roaming
Roaming is a wireless telecommunication term typically used with mobile devices, such as mobile phones. It refers to a mobile phone being used outside the range of its native network and connecting to another available cell network.
Technical ...
permitted between them. Over time the speed and spectral efficiency of Wi-Fi have increased. some versions of Wi-Fi, running on suitable hardware at close range, can achieve speeds of 9.6 Gbit/s (
gigabit
The bit is the most basic unit of information in computing and digital communications. The name is a portmanteau of binary digit. The bit represents a logical state with one of two possible values. These values are most commonly represented ...
per second).
History
A 1985 ruling by the U.S. Federal Communications Commission released parts of the
ISM band
The ISM radio bands are portions of the radio spectrum reserved internationally for industrial, scientific and medical (ISM) purposes, excluding applications in telecommunications.
Examples of applications for the use of radio frequency (RF) ener ...
s for unlicensed use for communications. These frequency bands include the same 2.4 GHz bands used by equipment such as
microwave oven
A microwave oven (commonly referred to as a microwave) is an electric oven that heats and cooks food by exposing it to electromagnetic radiation in the microwave frequency range. This induces polar molecules in the food to rotate and produce ...
s, and are thus subject to interference.
A prototype
test bed
A testbed (also spelled test bed) is a platform for conducting rigorous, transparent, and replicable testing of scientific theories, computational tools, and new technologies.
The term is used across many disciplines to describe experimental res ...
for a
wireless local area network
A wireless LAN (WLAN) is a wireless computer network that links two or more devices using wireless communication to form a local area network (LAN) within a limited area such as a home, school, computer laboratory, campus, or office buildi ...
(WLAN) was developed in 1992 by researchers from the Radiophysics Division of the
CSIRO
The Commonwealth Scientific and Industrial Research Organisation (CSIRO) is an Australian Government agency responsible for scientific research.
CSIRO works with leading organisations around the world. From its headquarters in Canberra, CSIRO ...
(Commonwealth Scientific and Industrial Research Organisation) in Australia.
About the same time in The Netherlands in 1991,
the
NCR Corporation
NCR Corporation, previously known as National Cash Register, is an American software, consulting and technology company providing several professional services and electronic products. It manufactures self-service kiosks, point-of-sale termin ...
with
AT&T Corporation
AT&T Corporation, originally the American Telephone and Telegraph Company, is the subsidiary of AT&T Inc. that provides voice, video, data, and Internet telecommunications and professional services to businesses, consumers, and government agen ...
invented the precursor to 802.11, intended for use in cashier systems, under the name
WaveLAN
WaveLAN was a brand name for a family of wireless networking technology sold by NCR, AT&T, Lucent Technologies, and Agere Systems as well as being sold by other companies under OEM agreements. The WaveLAN name debuted on the market in 1990 and was ...
. NCR's
Vic Hayes
Victor "Vic" Hayes (born July 31, 1941 Surabaya, Dutch East Indies) is a former Senior Research Fellow at the Delft University of Technology. His role in establishing and chairing the IEEE 802.11 Standards Working Group for Wireless Local Area Ne ...
, who held the chair of IEEE 802.11 for 10 years, along with
Bell Labs
Nokia Bell Labs, originally named Bell Telephone Laboratories (1925–1984),
then AT&T Bell Laboratories (1984–1996)
and Bell Labs Innovations (1996–2007),
is an American industrial research and scientific development company owned by mul ...
engineer Bruce Tuch, approached the
Institute of Electrical and Electronics Engineers
The Institute of Electrical and Electronics Engineers (IEEE) is a 501(c)(3) professional association for electronic engineering and electrical engineering (and associated disciplines) with its corporate office in New York City and its operation ...
(IEEE) to create a standard and were involved in designing the initial 802.11b and 802.11a standards within the IEEE. They have both been subsequently inducted into the Wi-Fi NOW Hall of Fame.
The first version of the 802.11 protocol was released in 1997, and provided up to 2 Mbit/s link speeds. This was updated in 1999 with
802.11b to permit 11 Mbit/s link speeds.
In 1999, the
Wi-Fi Alliance
The Wi-Fi Alliance is a non-profit organization that owns the Wi-Fi trademark. Manufacturers may use the trademark to brand products certified for Wi-Fi
interoperability.
History
Early 802.11 products suffered from interoperability problems be ...
formed as a trade association to hold the Wi-Fi trademark under which most IEEE 802.11 products are sold.
The major commercial breakthrough came with
Apple Inc. adopting Wi-Fi for their
iBook
iBook is a line of laptop computers designed, manufactured, and sold by Apple Computer from 1999 to 2006. The line targeted entry-level, consumer and education markets, with lower specifications and prices than the PowerBook, Apple's higher-end ...
series of laptops in 1999.
It was the first mass consumer product to offer Wi-Fi network connectivity, which was then branded by Apple as
AirPort
An airport is an aerodrome with extended facilities, mostly for commercial air transport. Airports usually consists of a landing area, which comprises an aerially accessible open space including at least one operationally active surfa ...
. This was in collaboration with the same group that helped create the standard:
Vic Hayes
Victor "Vic" Hayes (born July 31, 1941 Surabaya, Dutch East Indies) is a former Senior Research Fellow at the Delft University of Technology. His role in establishing and chairing the IEEE 802.11 Standards Working Group for Wireless Local Area Ne ...
, Bruce Tuch,
Cees Links, Rich McGinn, and others from
Lucent
Lucent Technologies, Inc. was an American multinational telecommunications equipment company headquartered in Murray Hill, New Jersey. It was established on September 30, 1996, through the divestiture of the former AT&T Technologies business u ...
.
Wi-Fi uses a large number of
patent
A patent is a type of intellectual property that gives its owner the legal right to exclude others from making, using, or selling an invention for a limited period of time in exchange for publishing an enabling disclosure of the invention."A ...
s held by many different organizations. Australia claims Wi-Fi is an Australian invention. This claim is controversial. Nevertheless, in April 2009, 14 technology companies agreed to pay the Australian CSIRO $1 billion for infringements on CSIRO patents.
CSIRO won a further $220 million settlement for Wi-Fi patent infringements in 2012, with global firms in the United States required to pay CSIRO licensing rights estimated at an additional $1 billion in royalties.
In 2016, the CSIRO's WLAN prototype test bed was chosen as Australia's contribution to the exhibition ''
A History of the World in 100 Objects
''A History of the World in 100 Objects'' was a joint project of BBC Radio 4 and the British Museum, consisting of a 100-part radio series written and presented by British Museum director Neil MacGregor. In 15-minute presentations broadcast on ...
'' held in the
National Museum of Australia
The National Museum of Australia, in the national capital Canberra, preserves and interprets Australia's social history, exploring the key issues, people and events that have shaped the nation. It was formally established by the ''National Muse ...
.
Etymology and terminology
The name ''Wi-Fi'', commercially used at least as early as August 1999, was coined by the brand-consulting firm Interbrand. The Wi-Fi Alliance had hired Interbrand to create a name that was "a little catchier than 'IEEE 802.11b Direct Sequence'."
According to Phil Belanger, a founding member of the Wi-Fi Alliance, the term ''Wi-Fi'' was chosen from a list of ten names that Interbrand proposed.
The Wi-Fi Alliance used the
advertising slogan
Advertising slogans are short phrases used in advertising campaigns to generate publicity and unify a company's marketing strategy. The phrases may be used to attract attention to a distinctive product feature or reinforce a company's brand.
Etym ...
"The Standard for Wireless Fidelity" for a short time after the brand name was created,
and the Wi-Fi Alliance was also called the "Wireless Fidelity Alliance Inc" in some publications. The name is often written as ''WiFi'', ''Wifi'', or ''wifi'', but these are not approved by the Wi-Fi Alliance.
IEEE
The Institute of Electrical and Electronics Engineers (IEEE) is a 501(c)(3) professional association for electronic engineering and electrical engineering (and associated disciplines) with its corporate office in New York City and its operati ...
is a separate, but related, organization and their website has stated "WiFi is a short name for Wireless Fidelity".
Interbrand also created the Wi-Fi
logo
A logo (abbreviation of logotype; ) is a graphic mark, emblem, or symbol used to aid and promote public identification and recognition. It may be of an abstract or figurative design or include the text of the name it represents as in a wo ...
. The
yin-yang Wi-Fi logo indicates the certification of a product for
interoperability
Interoperability is a characteristic of a product or system to work with other products or systems. While the term was initially defined for information technology or systems engineering services to allow for information exchange, a broader defi ...
.
Other technologies intended for fixed points, including
Motorola Canopy
Cambium Networks is a wireless infrastructure provider that offers fixed wireless and Wi-Fi to broadband service providers and enterprises to provide Internet access. An American telecommunications infrastructure company, it provides wireless tec ...
, are usually called ''
fixed wireless
Fixed wireless is the operation of wireless communication devices or systems used to connect two fixed locations (e.g., building to building or tower to building) with a radio or other wireless link, such as laser bridge. Usually, fixed wireles ...
''. Alternative wireless technologies include
Zigbee
Zigbee is an IEEE 802.15.4-based specification for a suite of high-level communication protocols used to create personal area networks with small, low-power digital radios, such as for home automation, medical device data collection, and oth ...
,
Z-Wave
Z-Wave is a wireless communications protocol used primarily for residential and commercial building automation. It is a mesh network using low-energy radio waves to communicate from device to device, allowing for wireless control of smart home de ...
,
Bluetooth
Bluetooth is a short-range wireless technology standard that is used for exchanging data between fixed and mobile devices over short distances and building personal area networks (PANs). In the most widely used mode, transmission power is limi ...
and mobile phone standards, such as
2G,
3G,
4G,
5G and
LTE.
To connect to a Wi-Fi LAN, a computer must be equipped with a
wireless network interface controller. The combination of a computer and an interface controller is called a ''
station''. Stations are identified by one or more
MAC address
A media access control address (MAC address) is a unique identifier assigned to a network interface controller (NIC) for use as a network address in communications within a network segment. This use is common in most IEEE 802 networking te ...
es.
Wi-Fi nodes often operate in infrastructure mode in which all communications go through a base station. ''
Ad hoc mode
A wireless ad hoc network (WANET) or mobile ad hoc network (MANET) is a decentralized type of wireless network. The network is ad hoc because it does not rely on a pre-existing infrastructure, such as routers in wired networks or access points ...
'' refers to devices communicating directly with each other, without communicating with an access point.
A
service set is the set of all the devices associated with a particular Wi-Fi network. Devices in a service set need not be on the same wavebands or channels. A service set can be local, independent, extended, mesh, or a combination.
Each service set has an associated identifier, a 32-byte service set identifier (SSID), which identifies the network. The SSID is configured within the devices that are part of the network.
A basic service set (BSS) is a group of stations that share the same wireless channel, SSID, and other settings that have wirelessly connected, usually to the same access point.
Each BSS is identified by a MAC address called the ''BSSID''.
Certification

The
IEEE
The Institute of Electrical and Electronics Engineers (IEEE) is a 501(c)(3) professional association for electronic engineering and electrical engineering (and associated disciplines) with its corporate office in New York City and its operati ...
does not test equipment for compliance with their standards. The
non-profit
A nonprofit organization (NPO) or non-profit organisation, also known as a non-business entity, not-for-profit organization, or nonprofit institution, is a legal entity organized and operated for a collective, public or social benefit, in co ...
Wi-Fi Alliance was formed in 1999 to fill this voidto establish and enforce standards for interoperability and
backward compatibility
Backward compatibility (sometimes known as backwards compatibility) is a property of an operating system, product, or technology that allows for interoperability with an older legacy system, or with input designed for such a system, especiall ...
, and to promote
wireless
Wireless communication (or just wireless, when the context allows) is the transfer of information between two or more points without the use of an electrical conductor, optical fiber or other continuous guided medium for the transfer. The most ...
local-area-network technology. , the Wi-Fi Alliance includes more than 800 companies.
It includes
3Com
3Com Corporation was an American digital electronics manufacturer best known for its computer network products. The company was co-founded in 1979 by Robert Metcalfe, Howard Charney and others. Bill Krause joined as President in 1981. Metcalfe e ...
(now owned by
Hewlett Packard Enterprise
The Hewlett Packard Enterprise Company (HPE) is an American multinational information technology company based in Spring, Texas, United States.
HPE was founded on November 1, 2015, in Palo Alto, California, as part of the splitting of the ...
), Aironet (now owned by
Cisco
Cisco Systems, Inc., commonly known as Cisco, is an American-based multinational digital communications technology conglomerate corporation headquartered in San Jose, California. Cisco develops, manufactures, and sells networking hardware, ...
),
Harris Semiconductor
Harris Corporation was an American technology company, defense contractor, and information technology services provider that produced wireless equipment, tactical radios, electronic systems, night vision equipment and both terrestrial and space ...
(now owned by
Intersil),
Lucent
Lucent Technologies, Inc. was an American multinational telecommunications equipment company headquartered in Murray Hill, New Jersey. It was established on September 30, 1996, through the divestiture of the former AT&T Technologies business u ...
(now owned by
Nokia
Nokia Corporation (natively Nokia Oyj, referred to as Nokia) is a Finnish multinational telecommunications, information technology, and consumer electronics corporation, established in 1865. Nokia's main headquarters are in Espoo, Finland, i ...
), Nokia and
Symbol Technologies
Symbol Technologies is an American manufacturer and supplier of mobile data capture and delivery equipment. The company specializes in barcode scanners, mobile computers, RFID systems and Wireless LAN infrastructure. In 2014, Symbol Technolog ...
(now owned by
Zebra Technologies
Zebra Technologies Corporation is an American mobile computing company specializing in technology used to sense, analyze, and act in real time. The company manufactures and sells marking, tracking, and computer printing technologies. Its product ...
). The Wi-Fi Alliance enforces the use of the Wi-Fi brand to technologies based on the
IEEE 802.11 standards from the IEEE. This includes
wireless local area network
A wireless LAN (WLAN) is a wireless computer network that links two or more devices using wireless communication to form a local area network (LAN) within a limited area such as a home, school, computer laboratory, campus, or office buildi ...
(WLAN) connections, a device to device connectivity (such as Wi-Fi Peer to Peer aka
Wi-Fi Direct
Wi-Fi Direct (formerly Wi-Fi Peer-to-Peer) is a Wi-Fi standard for peer-to-peer wireless connections that allows two devices to establish a direct Wi-Fi connection without an intermediary wireless access point, router, or Internet connection. W ...
),
Personal area network
A personal area network (PAN) is a computer network for interconnecting electronic devices within an individual person's workspace. A PAN provides data transmission among devices such as computers, smartphones, tablets and personal digital ...
(PAN),
local area network
A local area network (LAN) is a computer network that interconnects computers within a limited area such as a residence, school, laboratory, university campus or office building. By contrast, a wide area network (WAN) not only covers a large ...
(LAN), and even some limited
wide area network
A wide area network (WAN) is a telecommunications network that extends over a large geographic area. Wide area networks are often established with leased telecommunication circuits.
Businesses, as well as schools and government entities, u ...
(WAN) connections. Manufacturers with membership in the Wi-Fi Alliance, whose products pass the certification process, gain the right to mark those products with the Wi-Fi logo.
Specifically, the certification process requires conformance to the IEEE 802.11 radio standards, the
WPA and WPA2 security standards, and the
EAP authentication standard. Certification may optionally include tests of IEEE 802.11 draft standards, interaction with cellular-phone technology in converged devices, and features relating to security set-up, multimedia, and power-saving.
Not every Wi-Fi device is submitted for certification. The lack of Wi-Fi certification does not necessarily imply that a device is incompatible with other Wi-Fi devices. The Wi-Fi Alliance may or may not sanction derivative terms, such as
Super Wi-Fi Super Wi-Fi refers to IEEE 802.11g/ n/ ac/ ax Wi-Fi implementations over unlicensed 2.4 and 5 GHz Wi-Fi bands but with performance enhancements for antenna control, multiple path beam selection, advance control for best path, and applied intelligen ...
, coined by the US
Federal Communications Commission
The Federal Communications Commission (FCC) is an independent agency of the United States federal government that regulates communications by radio, television, wire, satellite, and cable across the United States. The FCC maintains jurisdicti ...
(FCC) to describe proposed networking in the UHF TV band in the US.
Versions and generations
Equipment frequently supports multiple versions of Wi-Fi. To communicate, devices must use a common Wi-Fi version. The versions differ between the radio wavebands they operate on, the radio bandwidth they occupy, the maximum data rates they can support and other details. Some versions permit the use of multiple antennas, which permits greater speeds as well as reduced interference.
Historically, the equipment has simply listed the versions of Wi-Fi using the name of the IEEE standard that it supports. In 2018, the
Wi-Fi Alliance
The Wi-Fi Alliance is a non-profit organization that owns the Wi-Fi trademark. Manufacturers may use the trademark to brand products certified for Wi-Fi
interoperability.
History
Early 802.11 products suffered from interoperability problems be ...
introduced simplified Wi-Fi generational numbering to indicate equipment that supports Wi-Fi 4 (
802.11n), Wi-Fi 5 (
802.11ac
IEEE 802.11ac-2013 or 802.11ac is a wireless networking standard in the IEEE 802.11 set of protocols (which is part of the Wi-Fi networking family), providing high-throughput wireless local area networks (WLANs) on the 5 GHz band. The stand ...
) and Wi-Fi 6 (
802.11ax). These generations have a high degree of backward compatibility with previous versions. The alliance has stated that the generational level 4, 5, or 6 can be indicated in the user interface when connected, along with the signal strength.
The list of most important versions of Wi-Fi is: 802.11a, 802.11b, 802.11g, 802.11n (Wi-Fi 4),
802.11h, 802.11i, 802.11-2007, 802.11-2012, 802.11ac (Wi-Fi 5),
802.11ad, 802.11af, 802.11-2016, 802.11ah, 802.11ai, 802.11aj,
802.11aq, 802.11ax (Wi-Fi 6),
.
Uses
Internet

Wi-Fi technology may be used to provide local network and
Internet access
Internet access is the ability of individuals and organizations to connect to the Internet using computer terminals, computers, and other devices; and to access services such as email and the World Wide Web. Internet access is sold by Interne ...
to devices that are within Wi-Fi range of one or more routers that are connected to the Internet. The coverage of one or more interconnected access points (''hotspots'') can extend from an area as small as a few rooms to as large as many square kilometres (miles). Coverage in the larger area may require a group of access points with overlapping coverage. For example, public outdoor Wi-Fi technology has been used successfully in
wireless mesh networks in London. An international example is
Fon.
Wi-Fi provides services in private homes, businesses, as well as in public spaces. Wi-Fi hotspots may be set up either free-of-charge or commercially, often using a
captive portal
A captive portal is a web page accessed with a web browser that is displayed to newly connected users of a Wi-Fi or wired network before they are granted broader access to network resources. Captive portals are commonly used to present a landin ...
webpage for access. Organizations, enthusiasts, authorities and
business
Business is the practice of making one's living or making money by producing or buying and selling products (such as goods and services). It is also "any activity or enterprise entered into for profit."
Having a business name does not separ ...
es, such as airports, hotels, and restaurants, often provide free or paid-use hotspots to attract customers, to provide services to promote business in selected areas.
Routers often incorporate a
digital subscriber line
Digital subscriber line (DSL; originally digital subscriber loop) is a family of technologies that are used to transmit digital data over telephone lines. In telecommunications marketing, the term DSL is widely understood to mean asymmetric dig ...
modem or a
cable modem
A cable modem is a type of network bridge that provides bi-directional data communication via radio frequency channels on a hybrid fibre-coaxial (HFC), radio frequency over glass (RFoG) and coaxial cable infrastructure. Cable modems are primar ...
and a Wi-Fi access point, are frequently set up in homes and other buildings, to provide Internet access and
internetworking
Internetworking is the practice of interconnecting multiple computer networks, such that any pair of hosts in the connected networks can exchange messages irrespective of their hardware-level networking technology. The resulting system of interc ...
for the structure.
Similarly, battery-powered routers may include a cellular Internet
radio modem
Radio modems are modems that transfer data wirelessly across a range of up to tens of kilometres.
Using radio modems is a modern way to create Private Radio Networks (PRN). Private radio networks are used in critical industrial applications, when r ...
and a Wi-Fi access point. When subscribed to a cellular data carrier, they allow nearby Wi-Fi stations to access the Internet over 2G, 3G, or 4G networks using the
tethering technique. Many smartphones have a built-in capability of this sort, including those based on
Android,
BlackBerry
The blackberry is an edible fruit produced by many species in the genus ''Rubus'' in the family Rosaceae, hybrids among these species within the subgenus ''Rubus'', and hybrids between the subgenera ''Rubus'' and ''Idaeobatus''. The taxonomy ...
,
Bada
Bada (stylized as bada; Korean: ) is a discontinued mobile operating system developed by Samsung Electronics for devices such as mid- to high-end smartphones and tablet computers. The name is derived from " (bada)", meaning "ocean" or "sea" in ...
,
iOS,
Windows Phone
Windows Phone (WP) is a discontinued family of mobile operating systems developed by Microsoft for smartphones as the replacement successor to Windows Mobile and Zune. Windows Phone featured a new user interface derived from the Metro design lan ...
, and
Symbian
Symbian is a discontinued mobile operating system (OS) and computing platform designed for smartphones. It was originally developed as a proprietary software OS for personal digital assistants in 1998 by the Symbian Ltd. consortium. Symbian OS ...
, though carriers often disable the feature, or charge a separate fee to enable it, especially for customers with unlimited data plans. "Internet packs" provide standalone facilities of this type as well, without the use of a smartphone; examples include the
MiFi- and
WiBro
WiBro (''wireless broadband'') is a wireless broadband Internet technology developed by the South Korean telecoms industry. WiBro is the South Korean service name for IEEE 802.16e (mobile WiMAX) international standard. By the end of 2012, t ...
-branded devices. Some laptops that have a cellular modem card can also act as mobile Internet Wi-Fi access points.
Many traditional university campuses in the developed world provide at least partial Wi-Fi coverage.
Carnegie Mellon University
Carnegie Mellon University (CMU) is a private research university in Pittsburgh, Pennsylvania. One of its predecessors was established in 1900 by Andrew Carnegie as the Carnegie Technical Schools; it became the Carnegie Institute of Technology ...
built the first campus-wide wireless Internet network, called
Wireless Andrew
The Andrew Project was a distributed computing environment developed at Carnegie Mellon University (CMU) beginning in 1982. It was an ambitious project for its time and resulted in an unprecedentedly vast and accessible university computing infrast ...
, at its
Pittsburgh
Pittsburgh ( ) is a city in the Commonwealth (U.S. state), Commonwealth of Pennsylvania, United States, and the county seat of Allegheny County, Pennsylvania, Allegheny County. It is the most populous city in both Allegheny County and Wester ...
campus in 1993 before Wi-Fi branding originated. By February 1997, the CMU Wi-Fi zone was fully operational. Many universities collaborate in providing Wi-Fi access to students and staff through the
Eduroam
eduroam (''edu''cation ''roam''ing) is an international Wi-Fi internet access roaming service for users in research, higher education and further education. It provides researchers, teachers, and students network access when visiting an institu ...
international authentication infrastructure.
City-wide

In the early 2000s, many cities around the world announced plans to construct citywide Wi-Fi networks. There are many successful examples; in 2004,
Mysore
Mysore (), officially Mysuru (), is a city in the southern part of the state of Karnataka, India. Mysore city is geographically located between 12° 18′ 26″ north latitude and 76° 38′ 59″ east longitude. It is located at an altitude o ...
(Mysuru) became India's first Wi-Fi-enabled city. A company called WiFiyNet has set up hotspots in Mysore, covering the whole city and a few nearby villages.
In 2005,
St. Cloud, Florida and
Sunnyvale, California
Sunnyvale () is a city located in the Santa Clara Valley in northwest Santa Clara County in the U.S. state of California.
Sunnyvale lies along the historic El Camino Real and Highway 101 and is bordered by portions of San Jose to the nor ...
, became the first cities in the United States to offer citywide free Wi-Fi (from
MetroFi).
Minneapolis
Minneapolis () is the largest city in Minnesota, United States, and the county seat of Hennepin County. The city is abundant in water, with thirteen lakes, wetlands, the Mississippi River, creeks and waterfalls. Minneapolis has its origin ...
has generated $1.2 million in profit annually for
its provider.
In May 2010, the then
London
London is the capital and List of urban areas in the United Kingdom, largest city of England and the United Kingdom, with a population of just under 9 million. It stands on the River Thames in south-east England at the head of a estuary dow ...
mayor
Boris Johnson
Alexander Boris de Pfeffel Johnson (; born 19 June 1964) is a British politician, writer and journalist who served as Prime Minister of the United Kingdom and Leader of the Conservative Party from 2019 to 2022. He previously served as ...
pledged to have London-wide Wi-Fi by 2012. Several
boroughs
A borough is an administrative division in various English-speaking countries. In principle, the term ''borough'' designates a self-governing walled town, although in practice, official use of the term varies widely.
History
In the Middle A ...
including
Westminster
Westminster is an area of Central London, part of the wider City of Westminster.
The area, which extends from the River Thames to Oxford Street, has many visitor attractions and historic landmarks, including the Palace of Westminster, B ...
and
Islington
Islington () is a district in the north of Greater London, England, and part of the London Borough of Islington. It is a mainly residential district of Inner London, extending from Islington's High Street to Highbury Fields, encompassing the ...
already had extensive outdoor Wi-Fi coverage at that point.
New York City
New York, often called New York City or NYC, is the List of United States cities by population, most populous city in the United States. With a 2020 population of 8,804,190 distributed over , New York City is also the L ...
announced a city-wide campaign to convert old
phone booths into digitized "kiosks" in 2014. The project, titled
LinkNYC
LinkNYC is the New York City branch of an international infrastructure project to create a network covering several cities with free Wi-Fi service. The office of New York City Mayor Bill de Blasio announced the plan on November 17, 2014, and ...
, has created a network of kiosks which serve as public Wi-Fi hotspots, high-definition screens and
landlines. Installation of the screens began in late 2015. The city government plans to implement more than seven thousand kiosks over time, eventually making LinkNYC the largest and fastest public, government-operated Wi-Fi network in the world.
The
UK has planned a similar project across major cities of the country, with the project's first implementation in the
Camden borough of
London
London is the capital and List of urban areas in the United Kingdom, largest city of England and the United Kingdom, with a population of just under 9 million. It stands on the River Thames in south-east England at the head of a estuary dow ...
.
Officials in South Korea's capital
Seoul
Seoul (; ; ), officially known as the Seoul Special City, is the Capital city, capital and largest metropolis of South Korea.Before 1972, Seoul was the ''de jure'' capital of the North Korea, Democratic People's Republic of Korea (North Korea ...
are moving to provide free Internet access at more than 10,000 locations around the city, including outdoor public spaces, major streets, and densely populated residential areas. Seoul will grant leases to KT,
LG Telecom, and SK Telecom. The companies will invest $44 million in the project, which was to be completed in 2015.
Geolocation
Wi-Fi positioning systems use the positions of Wi-Fi hotspots to identify a device's location.
Motion detection
Wi-Fi sensing
WiFi Sensing (also referred to as WLAN Sensing) uses existing Wi-Fi signals to detect events or changes such as motion, gesture recognition, and biometric measurement (e.g. breathing). WiFi Sensing is the combination of Wi-Fi and RADAR sensing te ...
is used in applications such as
motion detection
Motion detection is the process of detecting a change in the position of an object relative to its surroundings or a change in the surroundings relative to an object. It can be achieved by either mechanical or electronic methods. When it is done b ...
and
gesture recognition
Gesture recognition is a topic in computer science and language technology with the goal of interpreting human gestures via mathematical algorithms. It is a subdiscipline of computer vision. Gestures can originate from any bodily motion or sta ...
.
Operational principles
Wi-Fi stations communicate by sending each other
data packet
In telecommunications and computer networking, a network packet is a formatted unit of data carried by a packet-switched network. A packet consists of control information and user data; the latter is also known as the ''payload''. Control info ...
s: blocks of data individually sent and delivered over radio. As with all radio, this is done by the
modulation and demodulation of
carrier wave
In telecommunications, a carrier wave, carrier signal, or just carrier, is a waveform (usually sinusoidal) that is modulated (modified) with an information-bearing signal for the purpose of conveying information. This carrier wave usually has ...
s. Different versions of Wi-Fi use different techniques, 802.11b uses
DSSS
In telecommunications, direct-sequence spread spectrum (DSSS) is a spread-spectrum modulation technique primarily used to reduce overall signal interference. The direct-sequence modulation makes the transmitted signal wider in bandwidth than t ...
on a single carrier, whereas 802.11a, Wi-Fi 4, 5 and 6 use multiple carriers on slightly different frequencies within the channel (
OFDM
In telecommunications, orthogonal frequency-division multiplexing (OFDM) is a type of digital transmission and a method of encoding digital data on multiple carrier frequencies. OFDM has developed into a popular scheme for wideband digital commu ...
).
As with other IEEE 802 LANs, stations come programmed with a globally unique 48-bit MAC address (often printed on the equipment) so that each Wi-Fi station has a unique address. The MAC addresses are used to specify both the destination and the source of each data packet. Wi-Fi establishes link-level connections, which can be defined using both the destination and source addresses. On the reception of a transmission, the receiver uses the destination address to determine whether the transmission is relevant to the station or should be ignored. A network interface normally does not accept packets addressed to other Wi-Fi stations.
Channels are used
half duplex
A duplex communication system is a point-to-point system composed of two or more connected parties or devices that can communicate with one another in both directions. Duplex systems are employed in many communications networks, either to allow ...
and can be
time-shared by multiple networks. When communication happens on the same channel, any information sent by one computer is locally received by all, even if that information is intended for just one destination. The network interface card interrupts the
CPU
A central processing unit (CPU), also called a central processor, main processor or just processor, is the electronic circuitry that executes instructions comprising a computer program. The CPU performs basic arithmetic, logic, controlling, a ...
only when applicable packets are received: the card ignores information not addressed to it. The use of the same channel also means that the data bandwidth is shared, such that, for example, available data bandwidth to each device is halved when two stations are actively transmitting.
A scheme known as
carrier sense multiple access with collision avoidance (CSMA/CA) governs the way stations share channels. With CSMA/CA stations attempt to avoid collisions by beginning transmission only after the channel is sensed to be "idle",
but then transmit their packet data in its entirety. However, for geometric reasons, it cannot completely prevent collisions. A collision happens when a station receives multiple signals on a channel at the same time. This corrupts the transmitted data and can require stations to re-transmit. The lost data and re-transmission reduces throughput, in some cases severely.
Waveband
The 802.11 standard provides several distinct
radio frequency
Radio frequency (RF) is the oscillation rate of an alternating electric current or voltage or of a magnetic, electric or electromagnetic field or mechanical system in the frequency range from around to around . This is roughly between the up ...
ranges for use in Wi-Fi communications: 900
MHz, 2.4 GHz, 3.6 GHz, 4.9 GHz, 5 GHz, 5.9 GHz and 60 GHz
bands. Each range is divided into a multitude of
channels
Channel, channels, channeling, etc., may refer to:
Geography
* Channel (geography), in physical geography, a landform consisting of the outline (banks) of the path of a narrow body of water.
Australia
* Channel Country, region of outback Austral ...
. In the standards, channels are numbered at 5 MHz spacing within a band (except in the 60 GHz band, where they are 2.16 GHz apart), and the number refers to the centre frequency of the channel. Although channels are numbered at 5 MHz spacing, transmitters generally occupy at least 20 MHz, and standards allow for channels to be bonded together to form wider channels for higher throughput.
Countries apply their own regulations to the allowable channels, allowed users and maximum power levels within these frequency ranges. 802.11b/g/n can use the 2.4 GHz band, operating in the United States under FCC
Part 15
Code of Federal Regulations, 'Title 47, Part 15(47 CFR 15) is an oft-quoted part of Federal Communications Commission (FCC) rules and regulations regarding unlicensed transmissions. It is a part of Title 47 of the Code of Federal Regulations ( ...
Rules and Regulations. In this frequency band equipment may occasionally suffer
interference from microwave ovens,
cordless telephone
A cordless telephone or portable telephone has a portable telephone handset that connects by radio to a base station connected to the public telephone network. The operational range is limited, usually to the same building or within some short ...
s,
USB 3.0
USB 3.0, released in November 2008, is the third major version of the Universal Serial Bus (USB) standard for interfacing computers and electronic devices. Among other improvements, USB 3.0 adds the new transfer rate referred to as '' ...
hubs, and
Bluetooth
Bluetooth is a short-range wireless technology standard that is used for exchanging data between fixed and mobile devices over short distances and building personal area networks (PANs). In the most widely used mode, transmission power is limi ...
devices.
Spectrum assignments and operational limitations are not consistent worldwide: Australia and Europe allow for an additional two channels (12, 13) beyond the 11 permitted in the United States for the 2.4 GHz band, while Japan has three more (12–14). In the US and other countries, 802.11a and 802.11g devices may be operated without a licence, as allowed in Part 15 of the FCC Rules and Regulations.
802.11a/h/j/n/ac/ax can use the
5 GHz U-NII band, which, for much of the world, offers at least 23 non-overlapping 20 MHz channels rather than the 2.4 GHz frequency band, where the channels are only 5 MHz wide. In general, lower frequencies have longer range but have less capacity. The 5 GHz bands are absorbed to a greater degree by common building materials than the 2.4 GHz bands and usually give a shorter range.
As 802.11 specifications evolved to support higher throughput, the protocols have become much more efficient in their use of bandwidth. Additionally, they have gained the ability to
aggregate
Aggregate or aggregates may refer to:
Computing and mathematics
* collection of objects that are bound together by a root entity, otherwise known as an aggregate root. The aggregate root guarantees the consistency of changes being made within the ...
(or 'bond') channels together to gain still more throughput where the bandwidth is available. 802.11n allows for double radio spectrum/bandwidth (40 MHz- 8 channels) compared to
802.11a
IEEE 802.11a-1999 or 802.11a was an amendment to the IEEE 802.11 wireless local network specifications that defined requirements for an orthogonal frequency-division multiplexing (OFDM) communication system. It was originally designed to support ...
or 802.11g (20 MHz). 802.11n can also be set to limit itself to 20 MHz bandwidth to prevent interference in dense communities. In the 5 GHz band, 20 MHz, 40 MHz, 80 MHz, and 160 MHz bandwidth signals are permitted with some restrictions, giving much faster connections.
Communication stack
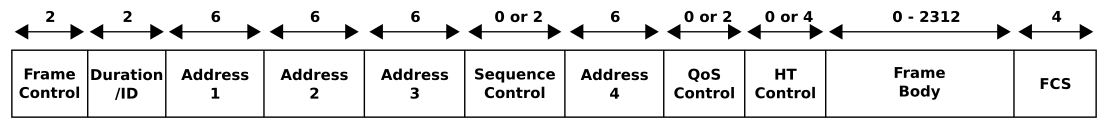
Wi-Fi is part of the IEEE 802 protocol family. The data is organized into
802.11 frames that are very similar to
Ethernet frame
In computer networking, an Ethernet frame is a data link layer protocol data unit and uses the underlying Ethernet physical layer transport mechanisms. In other words, a data unit on an Ethernet link transports an Ethernet frame as its payload ...
s at the data link layer, but with extra address fields. MAC addresses are used as
network address
A network address is an identifier for a node or host on a telecommunications network. Network addresses are designed to be unique identifiers across the network, although some networks allow for local, private addresses, or locally admini ...
es for routing over the LAN.
Wi-Fi's MAC and
physical layer
In the seven-layer OSI model of computer networking, the physical layer or layer 1 is the first and lowest layer; The layer most closely associated with the physical connection between devices. This layer may be implemented by a PHY chip.
The ...
(PHY) specifications are defined by IEEE 802.11 for modulating and receiving one or more carrier waves to transmit the data in the infrared, and 2.4,
3.6, 5, 6, or
60 GHz frequency bands. They are created and maintained by the IEEE LAN/
MAN
A man is an adult male human. Prior to adulthood, a male human is referred to as a boy (a male child or adolescent). Like most other male mammals, a man's genome usually inherits an X chromosome from the mother and a Y chromo ...
Standards Committee (
IEEE 802
IEEE 802 is a family of Institute of Electrical and Electronics Engineers (IEEE) standards for local area networks (LAN), personal area network (PAN), and metropolitan area networks (MAN). The IEEE 802 LAN/MAN Standards Committee (LMSC) maintai ...
). The base version of the standard was released in 1997 and has had many subsequent amendments. The standard and amendments provide the basis for wireless network products using the Wi-Fi brand. While each amendment is officially revoked when it is incorporated in the latest version of the standard, the corporate world tends to market to the revisions because they concisely denote capabilities of their products. As a result, in the market place, each revision tends to become its own standard.
In addition to 802.11 the IEEE 802 protocol family has specific provisions for Wi-Fi. These are required because Ethernet's cable-based media are not usually shared, whereas with wireless all transmissions are received by all stations within the range that employ that radio channel. While Ethernet has essentially negligible error rates, wireless communication media are subject to significant interference. Therefore, the accurate transmission is not guaranteed so delivery is, therefore, a
best-effort delivery
Best-effort delivery describes a network service in which the network does ''not'' provide any guarantee that data is delivered or that delivery meets any quality of service. In a best-effort network, all users obtain best-effort service. Under b ...
mechanism. Because of this, for Wi-Fi, the
Logical Link Control
In the IEEE 802 reference model of computer networking, the logical link control (LLC) data communication protocol layer is the upper sublayer of the data link layer (layer 2) of the seven-layer OSI model. The LLC sublayer acts as an interface ...
(LLC) specified by
IEEE 802.2 employs Wi-Fi's
media access control
In IEEE 802 LAN/MAN standards, the medium access control (MAC, also called media access control) sublayer is the layer that controls the hardware responsible for interaction with the wired, optical or wireless transmission medium. The MAC sublay ...
(MAC) protocols to manage retries without relying on higher levels of the protocol stack.
For internetworking purposes, Wi-Fi is usually
layered as a
link layer (equivalent to the physical and data link layers of the
OSI model
The Open Systems Interconnection model (OSI model) is a conceptual model that 'provides a common basis for the coordination of SOstandards development for the purpose of systems interconnection'. In the OSI reference model, the communications ...
) below the
internet layer
The internet layer is a group of internetworking methods, protocols, and specifications in the Internet protocol suite that are used to transport network packets from the originating host across network boundaries; if necessary, to the destinat ...
of the
Internet Protocol
The Internet Protocol (IP) is the network layer communications protocol in the Internet protocol suite for relaying datagrams across network boundaries. Its routing function enables internetworking, and essentially establishes the Internet.
...
. This means that nodes have an associated
internet address
An Internet Protocol address (IP address) is a numerical label such as that is connected to a computer network that uses the Internet Protocol for communication.. Updated by . An IP address serves two main functions: network interface identi ...
and, with suitable connectivity, this allows full Internet access.
Modes
Infrastructure

In infrastructure mode, which is the most common mode used, all communications go through a base station. For communications within the network, this introduces an extra use of the airwaves but has the advantage that any two stations that can communicate with the base station can also communicate through the base station, which enormously simplifies the protocols.
Ad hoc and Wi-Fi direct
Wi-Fi also allows communications directly from one computer to another without an access point intermediary. This is called
''ad hoc'' Wi-Fi transmission. Different types of ad hoc networks exist. In the simplest case network nodes must talk directly to each other. In more complex protocols nodes may forward packets, and nodes keep track of how to reach other nodes, even if they move around.
Ad hoc mode was first described by
Chai Keong Toh
Chai Keong Toh is a Singaporean computer scientist, engineer and professor. He is currently an Expert Consultant to the Gerson Lehrman Group. He has performed research on wireless ad hoc networks, mobile computing, Internet Protocols, and mu ...
in his 1996 patent of wireless ad hoc routing, implemented on Lucent WaveLAN 802.11a wireless on IBM
ThinkPad
ThinkPad is a line of business-oriented laptop computers and tablets designed, developed and marketed by Lenovo, and formerly by IBM until 2005, when IBM's PC business was acquired by Lenovo. ThinkPads have a distinct black, boxy design la ...
s over a size nodes scenario spanning a region of over a mile. The success was recorded in ''Mobile Computing'' magazine (1999) and later published formally in ''
IEEE Transactions on Wireless Communications'', 2002 and ''ACM SIGMETRICS Performance Evaluation Review'', 2001.
This wireless ad hoc network mode has proven popular with
multiplayer
A multiplayer video game is a video game in which more than one person can play in the same game environment at the same time, either locally on the same computing system ( couch co-op), on different computing systems via a local area network, or ...
handheld game console
A handheld game console, or simply handheld console, is a small, portable self-contained video game console with a built-in screen, game controls and speakers. Handheld game consoles are smaller than home video game consoles and contain the co ...
s, such as the
Nintendo DS
The is a handheld game console produced by Nintendo, released globally across 2004 and 2005. The DS, an initialism for "Developers' System" or "Dual Screen", introduced distinctive new features to handheld games: two LCD screens working in t ...
,
PlayStation Portable
The PlayStation Portable (PSP) is a handheld game console developed and marketed by Sony Computer Entertainment. It was first released in Japan on December 12, 2004, in North America on March 24, 2005, and in PAL regions on September 1, 200 ...
,
digital camera
A digital camera is a camera that captures photographs in digital memory. Most cameras produced today are digital, largely replacing those that capture images on photographic film. Digital cameras are now widely incorporated into mobile devices ...
s, and other
consumer electronics
Consumer electronics or home electronics are electronic ( analog or digital) equipment intended for everyday use, typically in private homes. Consumer electronics include devices used for entertainment, communications and recreation. Usuall ...
devices. Some devices can also share their Internet connection using ad hoc, becoming hotspots or "virtual routers".
Similarly, the Wi-Fi Alliance promotes the specification
Wi-Fi Direct
Wi-Fi Direct (formerly Wi-Fi Peer-to-Peer) is a Wi-Fi standard for peer-to-peer wireless connections that allows two devices to establish a direct Wi-Fi connection without an intermediary wireless access point, router, or Internet connection. W ...
for file transfers and media sharing through a new discovery- and security-methodology. Wi-Fi Direct launched in October 2010.
Another mode of direct communication over Wi-Fi is Tunneled Direct-Link Setup (
TDLS
TDLS, shortened from Tunneled Direct Link Setup, is "a seamless way to stream media and other data faster between devices already on the same Wi-Fi network." Devices using it communicate directly with one another, without involving the wireless n ...
), which enables two devices on the same Wi-Fi network to communicate directly, instead of via the access point.
Multiple access points

An
Extended Service Set
In IEEE 802.11 wireless local area networking standards (including Wi-Fi), a service set is a group of wireless network devices which share a ''service set identifier'' (''SSID'')—typically the natural language label that users see as a network ...
may be formed by deploying multiple access points that are configured with the same SSID and security settings. Wi-Fi client devices typically connect to the access point that can provide the strongest signal within that service set.
Increasing the number of Wi-Fi access points for a network provides
redundancy, better range, support for fast roaming, and increased overall network-capacity by using more channels or by defining smaller
cells
Cell most often refers to:
* Cell (biology), the functional basic unit of life
Cell may also refer to:
Locations
* Monastic cell, a small room, hut, or cave in which a religious recluse lives, alternatively the small precursor of a monastery w ...
. Except for the smallest implementations (such as home or small office networks), Wi-Fi implementations have moved toward "thin" access points, with more of the
network intelligence housed in a centralized network appliance, relegating individual access points to the role of "dumb" transceivers. Outdoor applications may use
mesh
A mesh is a barrier made of connected strands of metal, fiber, or other flexible or ductile materials. A mesh is similar to a web or a net in that it has many attached or woven strands.
Types
* A plastic mesh may be extruded, oriented, exp ...
topologies.
Performance
Wi-Fi operational range depends on factors such as the frequency band,
radio power output, receiver sensitivity, antenna gain, and antenna type as well as the modulation technique. Also, the propagation characteristics of the signals can have a big impact.
At longer distances, and with greater signal absorption, speed is usually reduced.
Transmitter power
Compared to cell phones and similar technology, Wi-Fi transmitters are low-power devices. In general, the maximum amount of power that a Wi-Fi device can transmit is limited by local regulations, such as
FCC Part 15 in the US.
Equivalent isotropically radiated power (EIRP) in the
European Union
The European Union (EU) is a supranational union, supranational political union, political and economic union of Member state of the European Union, member states that are located primarily in Europe, Europe. The union has a total area of ...
is limited to 20
dBm (100 mW).
To reach requirements for wireless LAN applications, Wi-Fi has higher power consumption compared to some other standards designed to support wireless personal area network (PAN) applications. For example, Bluetooth provides a much shorter
propagation
Propagation can refer to:
*Chain propagation in a chemical reaction mechanism
*Crack propagation, the growth of a crack during the fracture of materials
* Propaganda, non-objective information used to further an agenda
* Reproduction, and other for ...
range between 1 and 100 metres (1 and 100 yards) and so in general has a lower power consumption. Other low-power technologies such as
ZigBee
Zigbee is an IEEE 802.15.4-based specification for a suite of high-level communication protocols used to create personal area networks with small, low-power digital radios, such as for home automation, medical device data collection, and oth ...
have fairly long range, but much lower data rate. The high power consumption of Wi-Fi makes battery life in some mobile devices a concern.
Antenna
An access point compliant with either
802.11b or 802.11g, using the stock
omnidirectional antenna
In radio communication, an omnidirectional antenna is a class of antenna which radiates equal radio power in all directions perpendicular to an axis (azimuthal directions), with power varying with angle to the axis ( elevation angle), declining ...
might have a range of . The same radio with an external semi parabolic antenna (15 dB gain) with a similarly equipped receiver at the far end might have a range over 20 miles.
Higher gain rating (dBi) indicates further deviation (generally toward the horizontal) from a theoretical, perfect
isotropic radiator
An isotropic radiator is a theoretical point source of electromagnetic or sound waves which radiates the same intensity of radiation in all directions. It has no preferred direction of radiation. It radiates uniformly in all directions over ...
, and therefore the antenna can project or accept a usable signal further in particular directions, as compared to a similar output power on a more isotropic antenna. For example, an 8 dBi antenna used with a 100 mW driver has a similar horizontal range to a 6 dBi antenna being driven at 500 mW. Note that this assumes that radiation in the vertical is lost; this may not be the case in some situations, especially in large buildings or within a
waveguide
A waveguide is a structure that guides waves, such as electromagnetic waves or sound, with minimal loss of energy by restricting the transmission of energy to one direction. Without the physical constraint of a waveguide, wave intensities de ...
. In the above example, a directional waveguide could cause the low-power 6 dBi antenna to project much further in a single direction than the 8 dBi antenna, which is not in a waveguide, even if they are both driven at 100 mW.
On wireless routers with detachable antennas, it is possible to improve range by fitting upgraded antennas that provide a higher gain in particular directions. Outdoor ranges can be improved to many kilometres (miles) through the use of high gain
directional antenna
A directional antenna or beam antenna is an antenna which radiates or receives greater power in specific directions allowing increased performance and reduced interference from unwanted sources. Directional antennas provide increased performanc ...
s at the router and remote device(s).
MIMO (multiple-input and multiple-output)
Wi-Fi 4 and higher standards allow devices to have multiple antennas on transmitters and receivers. Multiple antennas enable the equipment to exploit
multipath propagation
In radio communication, multipath is the propagation phenomenon that results in radio signals reaching the receiving antenna by two or more paths. Causes of multipath include atmospheric ducting, ionospheric reflection and refraction, and refle ...
on the same frequency bands giving much higher speeds and longer range.
Wi-Fi 4 can more than double the range over previous standards.
The Wi-Fi 5 standard uses the 5 GHz band exclusively, and is capable of multi-station WLAN throughput of at least 1 gigabit per second, and a single station throughput of at least 500 Mbit/s. As of the first quarter of 2016, The Wi-Fi Alliance certifies devices compliant with the 802.11ac standard as "Wi-Fi CERTIFIED ac". This standard uses several signal processing techniques such as multi-user MIMO and 4X4 Spatial Multiplexing streams, and wide channel bandwidth (160 MHz) to achieve its gigabit throughput. According to a study by IHS Technology, 70% of all access point sales revenue in the first quarter of 2016 came from 802.11ac devices.
Radio propagation
With Wi-Fi signals
line-of-sight usually works best, but signals can transmit, absorb, reflect,
refract
In physics, refraction is the redirection of a wave as it passes from one medium to another. The redirection can be caused by the wave's change in speed or by a change in the medium. Refraction of light is the most commonly observed phenomeno ...
,
diffract
Diffraction is defined as the interference or bending of waves around the corners of an obstacle or through an aperture into the region of geometrical shadow of the obstacle/aperture. The diffracting object or aperture effectively becomes a s ...
and
up and down fade through and around structures, both man-made and natural. Wi-Fi signals are very strongly affected by metallic structures (including
rebar
Rebar (short for reinforcing bar), known when massed as reinforcing steel or reinforcement steel, is a steel bar used as a tension device in reinforced concrete and reinforced masonry structures to strengthen and aid the concrete under tension. ...
in concrete,
low-e coatings in glazing) and water (such as found in vegetation.)
Due to the complex nature of radio propagation at typical Wi-Fi frequencies, particularly around trees and buildings, algorithms can only approximately predict Wi-Fi signal strength for any given area in relation to a transmitter. This effect does not apply equally to
long-range Wi-Fi
Long-range Wi-Fi is used for low-cost, unregulated point-to-point computer network connections, as an alternative to other fixed wireless, cellular networks or satellite Internet access.
Wi-Fi networks have a range that's limited by the freque ...
, since longer links typically operate from towers that transmit above the surrounding foliage.
Mobile use of Wi-Fi over wider ranges is limited, for instance, to uses such as in an automobile moving from one hotspot to another. Other wireless technologies are more suitable for communicating with moving vehicles.
Distance records
Distance records (using non-standard devices) include in June 2007, held by Ermanno Pietrosemoli and EsLaRed of Venezuela, transferring about 3 MB of data between the mountain-tops of
El Águila and Platillon. The
Swedish Space Agency transferred data , using 6 watt amplifiers to reach an overhead
stratospheric balloon.
Interference

Wi-Fi connections can be blocked or the Internet speed lowered by having other devices in the same area. Wi-Fi protocols are designed to share the wavebands reasonably fairly, and this often works with little to no disruption. To minimize collisions with Wi-Fi and non-Wi-Fi devices, Wi-Fi employs
Carrier-sense multiple access with collision avoidance
Carrier-sense multiple access with collision avoidance (CSMA/CA) in computer networking, is a network multiple access method in which carrier sensing is used, but nodes attempt to avoid collisions by beginning transmission only after the channe ...
(CSMA/CA), where transmitters listen before transmitting and delay transmission of packets if they detect that other devices are active on the channel, or if noise is detected from adjacent channels or non-Wi-Fi sources. Nevertheless, Wi-Fi networks are still susceptible to the
hidden node and
exposed node problem
In wireless networks, the exposed node problem occurs when a node is prevented from sending packets to other nodes because of co-channel interference with a neighboring transmitter. Consider an example of four nodes labeled R1, S1, S2, and R2, whe ...
.
A standard speed Wi-Fi signal occupies five channels in the 2.4 GHz band. Interference can be caused by overlapping channels. Any two channel numbers that differ by five or more, such as 2 and 7, do not overlap (no
adjacent-channel interference
Adjacent-channel interference (ACI) is interference caused by extraneous power from a signal in an adjacent channel. ACI may be caused by inadequate filtering (such as incomplete filtering of unwanted modulation products in FM systems), improp ...
). The oft-repeated adage that channels 1, 6, and 11 are the ''only'' non-overlapping channels is, therefore, not accurate. Channels 1, 6, and 11 are the only ''group of three'' non-overlapping channels in North America. However, whether the overlap is significant depends on physical spacing. Channels that are four apart interfere a negligible amountmuch less than reusing channels (which causes
co-channel interference
Co-channel interference or CCI is crosstalk from two different radio transmitters using the same channel. Co-channel interference can be caused by many factors from weather conditions to administrative and design issues. Co-channel interferen ...
)if transmitters are at least a few metres apart.
In Europe and Japan where channel 13 is available, using Channels 1, 5, 9, and 13 for
802.11g and
802.11n is viable and
recommended.
However, many 2.4 GHz 802.11b and 802.11g access-points default to the same channel on initial startup, contributing to congestion on certain channels. Wi-Fi pollution, or an excessive number of access points in the area, can prevent access and interfere with other devices' use of other access points as well as with decreased
signal-to-noise ratio
Signal-to-noise ratio (SNR or S/N) is a measure used in science and engineering that compares the level of a desired signal to the level of background noise. SNR is defined as the ratio of signal power to the noise power, often expressed in de ...
(SNR) between access points. These issues can become a problem in high-density areas, such as large apartment complexes or office buildings with many Wi-Fi access points.
Other devices use the 2.4 GHz band:
microwave ovens, ISM band devices,
security camera
A closed-circuit television camera can produce images or recordings for surveillance or other private purposes. Cameras can be either video cameras, or digital stills cameras. Walter Bruch was the inventor of the CCTV camera. The main purpose o ...
s, ZigBee devices, Bluetooth devices,
video senders, cordless phones,
baby monitor
A baby monitor, also known as a baby alarm, is a radio system used to remotely listen to sounds made by an infant. An audio monitor consists of a transmitter unit, equipped with a microphone, placed near to the child. It transmits the sounds by ...
s, and, in some countries,
amateur radio
Amateur radio, also known as ham radio, is the use of the radio frequency spectrum for purposes of non-commercial exchange of messages, wireless experimentation, self-training, private recreation, radiosport, contesting, and emergency commu ...
, all of which can cause significant additional interference. It is also an issue when municipalities or other large entities (such as universities) seek to provide large area coverage. On some 5 GHz bands interference from radar systems can occur in some places. For base stations that support those bands they employ Dynamic Frequency Selection which listens for radar, and if it is found, it will not permit a network on that band.
These bands can be used by low power transmitters without a licence, and with few restrictions. However, while unintended interference is common, users that have been found to cause deliberate interference (particularly for attempting to locally monopolize these bands for commercial purposes) have been issued large fines.
Throughput
Various layer-2 variants of IEEE 802.11 have different characteristics. Across all flavours of 802.11, maximum achievable throughputs are either given based on measurements under ideal conditions or in the layer-2 data rates. This, however, does not apply to typical deployments in which data are transferred between two endpoints of which at least one is typically connected to a wired infrastructure, and the other is connected to an infrastructure via a wireless link.
This means that typically data frames pass an 802.11 (WLAN) medium and are being converted to 802.3 (Ethernet) or vice versa.
Due to the difference in the frame (header) lengths of these two media, the packet size of an application determines the speed of the data transfer. This means that an application that uses small packets (e.g. VoIP) creates a data flow with high overhead traffic (low
goodput
In computer networks, goodput (a portmanteau of good and throughput) is the application-level throughput of a communication; i.e. the number of useful information bits delivered by the network to a certain destination per unit of time. The amoun ...
).
Other factors that contribute to the overall application data rate are the speed with which the application transmits the packets (i.e. the data rate) and the energy with which the wireless signal is received. The latter is determined by distance and by the configured output power of the communicating devices.
The same references apply to the attached throughput graphs, which show measurements of
UDP throughput measurements. Each represents an average throughput of 25 measurements (the error bars are there, but barely visible due to the small variation), is with specific packet size (small or large), and with a specific data rate (10 kbit/s – 100 Mbit/s). Markers for traffic profiles of common applications are included as well. This text and measurements do not cover packet errors but information about this can be found at the above references. The table below shows the maximum achievable (application-specific) UDP throughput in the same scenarios (same references again) with various WLAN (802.11) flavours. The measurement hosts have been 25 metres (yards) apart from each other; loss is again ignored.
Hardware

Wi-Fi allows wireless deployment of local area networks (LANs). Also, spaces where cables cannot be run, such as outdoor areas and historical buildings, can host wireless LANs. However, building walls of certain materials, such as stone with high metal content, can block Wi-Fi signals.
A Wi-Fi device is a
short-range wireless
Wireless communication (or just wireless, when the context allows) is the transfer of information between two or more points without the use of an electrical conductor, optical fiber or other continuous guided medium for the transfer. The most ...
device. Wi-Fi devices are
fabricated on
RF CMOS integrated circuit
An integrated circuit or monolithic integrated circuit (also referred to as an IC, a chip, or a microchip) is a set of electronic circuits on one small flat piece (or "chip") of semiconductor material, usually silicon. Large numbers of tiny ...
(
RF circuit
Radio-frequency (RF) engineering is a subset of electronic engineering involving the application of transmission line, waveguide, antenna and electromagnetic field principles to the design and application of devices that produce or use signals w ...
) chips.
Since the early 2000s, manufacturers are building wireless network adapters into most laptops. The price of
chipset
In a computer system, a chipset is a set of electronic components in one or more integrated circuits known as a "Data Flow Management System" that manages the data flow between the processor, memory and peripherals. It is usually found on the mo ...
s for Wi-Fi continues to drop, making it an economical networking option included in ever more devices.
Different competitive brands of access points and client network-interfaces can inter-operate at a basic level of service. Products designated as "Wi-Fi Certified" by the Wi-Fi Alliance are
backward compatible
Backward compatibility (sometimes known as backwards compatibility) is a property of an operating system, product, or technology that allows for interoperability with an older legacy system, or with input designed for such a system, especially in ...
. Unlike
mobile phone
A mobile phone, cellular phone, cell phone, cellphone, handphone, hand phone or pocket phone, sometimes shortened to simply mobile, cell, or just phone, is a portable telephone that can make and receive calls over a radio frequency link whi ...
s, any standard Wi-Fi device works anywhere in the world.
Access point

A wireless access point (WAP) connects a group of wireless devices to an adjacent wired LAN. An access point resembles a
network hub, relaying
data
In the pursuit of knowledge, data (; ) is a collection of discrete values that convey information, describing quantity, quality, fact, statistics, other basic units of meaning, or simply sequences of symbols that may be further interpret ...
between connected wireless devices in addition to a (usually) single connected wired device, most often an Ethernet hub or switch, allowing wireless devices to communicate with other wired devices.
Wireless adapter

Wireless adapters allow devices to connect to a wireless network. These adapters connect to devices using various external or internal interconnects such as PCI, miniPCI, USB,
ExpressCard, Cardbus, and
PC Card
In computing, PC Card is a configuration for computer parallel communication peripheral interface, designed for laptop computers. Originally introduced as PCMCIA, the PC Card standard as well as its successors like CardBus were defined and devel ...
. As of 2010, most newer laptop computers come equipped with built-in internal adapters.
Router
Wireless router
A wireless router is a device that performs the functions of a router and also includes the functions of a wireless access point. It is used to provide access to the Internet or a private computer network. Depending on the manufacturer and mode ...
s integrate a Wireless Access Point, Ethernet
switch
In electrical engineering, a switch is an electrical component that can disconnect or connect the conducting path in an electrical circuit, interrupting the electric current or diverting it from one conductor to another. The most common type of ...
, and internal router firmware application that provides
IP routing
Routing is the process of selecting a path for traffic in a network or between or across multiple networks. Broadly, routing is performed in many types of networks, including circuit-switched networks, such as the public switched telephone netw ...
,
NAT
Nat or NAT may refer to:
Computing
* Network address translation (NAT), in computer networking
Organizations
* National Actors Theatre, New York City, U.S.
* National AIDS trust, a British charity
* National Archives of Thailand
* National A ...
, and
DNS forwarding through an integrated WAN-interface. A wireless router allows wired and wireless Ethernet LAN devices to connect to a (usually) single WAN device such as a cable modem,
DSL modem, or
optical modem. A wireless router allows all three devices, mainly the access point and router, to be configured through one central utility. This utility is usually an integrated
web server
A web server is computer software and underlying hardware that accepts requests via HTTP (the network protocol created to distribute web content) or its secure variant HTTPS. A user agent, commonly a web browser or web crawler, initia ...
that is accessible to wired and wireless LAN clients and often optionally to WAN clients. This utility may also be an application that is run on a computer, as is the case with as Apple's AirPort, which is managed with the
AirPort Utility on
macOS
macOS (; previously OS X and originally Mac OS X) is a Unix operating system developed and marketed by Apple Inc. since 2001. It is the primary operating system for Apple's Mac computers. Within the market of desktop and la ...
and iOS.
Bridge
Wireless
network bridge
A network bridge is a computer networking device that creates a single, aggregate network from multiple communication networks or network segments. This function is called network bridging. Bridging is distinct from routing. Routing allows ...
s can act to connect two networks to form a single network at the
data-link layer
The data link layer, or layer 2, is the second layer of the seven-layer OSI model of computer networking. This layer is the protocol layer that transfers data between nodes on a network segment across the physical layer. The data link layer pr ...
over Wi-Fi. The main standard is the
wireless distribution system
A wireless distribution system (WDS) is a system enabling the wireless interconnection of access points in an IEEE 802.11 network. It allows a wireless network to be expanded using multiple access points without the traditional requirement for a ...
(WDS).
Wireless bridging can connect a wired network to a wireless network. A bridge differs from an access point: an access point typically connects wireless devices to one wired network. Two wireless bridge devices may be used to connect two wired networks over a wireless link, useful in situations where a wired connection may be unavailable, such as between two separate homes or for devices that have no wireless networking capability (but have wired networking capability), such as
consumer entertainment devices; alternatively, a wireless bridge can be used to enable a device that supports a wired connection to operate at a wireless networking standard that is faster than supported by the wireless network connectivity feature (external dongle or inbuilt) supported by the device (e.g., enabling Wireless-N speeds (up to the maximum supported speed on the wired Ethernet port on both the bridge and connected devices including the wireless access point) for a device that only supports Wireless-G).
A dual-band wireless bridge can also be used to enable 5 GHz wireless network operation on a device that only supports 2.4 GHz wireless and has a wired Ethernet port.
Repeater
Wireless range-extenders or
wireless repeater
A wireless repeater (also called wireless range extender or wifi extender) is a device that takes an existing signal from a wireless router or wireless access point and rebroadcasts it to create a second network. When two or more hosts have to ...
s can extend the range of an existing wireless network. Strategically placed range-extenders can elongate a signal area or allow for the signal area to reach around barriers such as those pertaining in L-shaped corridors. Wireless devices connected through repeaters suffer from an increased latency for each hop, and there may be a reduction in the maximum available data throughput. Besides, the effect of additional users using a network employing wireless range-extenders is to consume the available bandwidth faster than would be the case whereby a single user migrates around a network employing extenders. For this reason, wireless range-extenders work best in networks supporting low traffic throughput requirements, such as for cases whereby a single user with a Wi-Fi-equipped tablet migrates around the combined extended and non-extended portions of the total connected network. Also, a wireless device connected to any of the repeaters in the chain has data throughput limited by the "weakest link" in the chain between the connection origin and connection end. Networks using wireless extenders are more prone to degradation from interference from neighbouring access points that border portions of the extended network and that happen to occupy the same channel as the extended network.
Embedded systems
The security standard,
Wi-Fi Protected Setup
Wi-Fi Protected Setup (WPS; originally, Wi-Fi Simple Config) is a network security standard to create a secure wireless home network.
Created by Cisco and introduced in 2006, the point of the protocol is to allow home users who know little of w ...
, allows embedded devices with a limited graphical user interface to connect to the Internet with ease. Wi-Fi Protected Setup has 2 configurations: The Push Button configuration and the PIN configuration. These embedded devices are also called The
Internet of Things
The Internet of things (IoT) describes physical objects (or groups of such objects) with sensors, processing ability, software and other technologies that connect and exchange data with other devices and systems over the Internet or other com ...
and are low-power, battery-operated embedded systems. Several Wi-Fi manufacturers design chips and modules for embedded Wi-Fi, such as GainSpan.
Increasingly in the last few years (particularly ), embedded Wi-Fi modules have become available that incorporate a real-time operating system and provide a simple means of wirelessly enabling any device that can communicate via a serial port. This allows the design of simple monitoring devices. An example is a portable ECG device monitoring a patient at home. This Wi-Fi-enabled device can communicate via the Internet.
These Wi-Fi modules are designed by
OEMs so that implementers need only minimal Wi-Fi knowledge to provide Wi-Fi connectivity for their products.
In June 2014,
Texas Instruments
Texas Instruments Incorporated (TI) is an American technology company headquartered in Dallas, Texas, that designs and manufactures semiconductors and various integrated circuits, which it sells to electronics designers and manufacturers globa ...
introduced the first ARM Cortex-M4 microcontroller with an onboard dedicated Wi-Fi MCU, the SimpleLink CC3200. It makes embedded systems with Wi-Fi connectivity possible to build as single-chip devices, which reduces their cost and minimum size, making it more practical to build wireless-networked controllers into inexpensive ordinary objects.
Network security
The main issue with wireless
network security
Network security consists of the policies, processes and practices adopted to prevent, detect and monitor unauthorized access, misuse, modification, or denial of a computer network and network-accessible resources. Network security involves th ...
is its simplified access to the network compared to traditional wired networks such as Ethernet. With wired networking, one must either gain access to a building (physically connecting into the internal network), or break through an external
firewall
Firewall may refer to:
* Firewall (computing), a technological barrier designed to prevent unauthorized or unwanted communications between computer networks or hosts
* Firewall (construction), a barrier inside a building, designed to limit the spre ...
. To access Wi-Fi, one must merely be within the range of the Wi-Fi network. Most business networks protect sensitive data and systems by attempting to disallow external access. Enabling wireless connectivity reduces security if the network uses inadequate or no encryption.
An attacker who has gained access to a Wi-Fi network router can initiate a DNS spoofing attack against any other user of the network by forging a response before the queried DNS server has a chance to reply.
Securing methods
A common measure to deter unauthorized users involves hiding the access point's name by disabling the SSID broadcast. While effective against the casual user, it is ineffective as a security method because the SSID is broadcast in the clear in response to a client SSID query. Another method is to only allow computers with known MAC addresses to join the network, but determined eavesdroppers may be able to join the network by
spoofing an authorized address.
Wired Equivalent Privacy
Wired Equivalent Privacy (WEP) was a security algorithm for 802.11 wireless networks. Introduced as part of the original IEEE 802.11 standard ratified in 1997, its intention was to provide data confidentiality comparable to that of a traditional ...
(WEP) encryption was designed to protect against casual snooping but it is no longer considered secure. Tools such as
AirSnort or
Aircrack-ng
Aircrack-ng is a network software suite consisting of a detector, packet sniffer, WEP and WPA/WPA2-PSK cracker and analysis tool for 802.11 wireless LANs. It works with any wireless network interface controller whose driver supports raw moni ...
can quickly recover WEP encryption keys. Because of WEP's weakness the Wi-Fi Alliance approved Wi-Fi Protected Access (WPA) which uses
TKIP. WPA was specifically designed to work with older equipment usually through a firmware upgrade. Though more secure than WEP, WPA has known vulnerabilities.
The more secure
WPA2 using
Advanced Encryption Standard
The Advanced Encryption Standard (AES), also known by its original name Rijndael (), is a specification for the encryption of electronic data established by the U.S. National Institute of Standards and Technology (NIST) in 2001.
AES is a variant ...
was introduced in 2004 and is supported by most new Wi-Fi devices. WPA2 is fully compatible with WPA.
In 2017, a flaw in the WPA2 protocol was discovered, allowing a key replay attack, known as
KRACK
KRACK ("Key Reinstallation Attack") is a replay attack (a type of exploitable flaw) on the Wi-Fi Protected Access protocol that secures Wi-Fi connections. It was discovered in 2016 by the Belgian researchers Mathy Vanhoef and Frank Piessens o ...
.

A flaw in a feature added to Wi-Fi in 2007, called
Wi-Fi Protected Setup
Wi-Fi Protected Setup (WPS; originally, Wi-Fi Simple Config) is a network security standard to create a secure wireless home network.
Created by Cisco and introduced in 2006, the point of the protocol is to allow home users who know little of w ...
(WPS), let WPA and WPA2 security be bypassed, and effectively broken in many situations. The only remedy as of late 2011 was to turn off Wi-Fi Protected Setup, which is not always possible.
Virtual Private Network
A virtual private network (VPN) extends a private network across a public network and enables users to send and receive data across shared or public networks as if their computing devices were directly connected to the private network. The b ...
s can be used to improve the confidentiality of data carried through Wi-Fi networks, especially public Wi-Fi networks.
A
URI using the WIFI scheme can specify the SSID, encryption type, password/passphrase, and if the SSID is hidden or not, so users can follow links from
QR code
A QR code (an initialism for quick response code) is a type of matrix barcode (or two-dimensional barcode) invented in 1994 by the Japanese company Denso Wave. A barcode is a machine-readable optical label that can contain information about t ...
s, for instance, to join networks without having to manually enter the data. A MECARD-like format is supported by Android and iOS 11+.
* Common format:
WIFI:S:;T:;P:;H:;
* Sample
WIFI:S:MySSID;T:WPA;P:MyPassW0rd;;
Data security risks
The older wireless
encryption
In cryptography, encryption is the process of encoding information. This process converts the original representation of the information, known as plaintext, into an alternative form known as ciphertext. Ideally, only authorized parties can d ...
-standard, Wired Equivalent Privacy (WEP), has been
shown easily breakable even when correctly configured. Wi-Fi Protected Access (WPA and WPA2) encryption, which became available in devices in 2003, aimed to solve this problem. Wi-Fi access points typically default to an encryption-free (''open'') mode. Novice users benefit from a zero-configuration device that works out-of-the-box, but this default does not enable any
wireless security
Wireless security is the prevention of unauthorized access or damage to computers or data using wireless networks, which include Wi-Fi networks. The term may also refer to the protection of the wireless network itself from adversaries seeking to ...
, providing open wireless access to a LAN. To turn security on requires the user to configure the device, usually via a software
graphical user interface
The GUI ( "UI" by itself is still usually pronounced . or ), graphical user interface, is a form of user interface that allows users to interact with electronic devices through graphical icons and audio indicator such as primary notation, ins ...
(GUI). On unencrypted Wi-Fi networks connecting devices can monitor and record data (including personal information). Such networks can only be secured by using other means of protection, such as a
VPN
A virtual private network (VPN) extends a private network across a public network and enables users to send and receive data across shared or public networks as if their computing devices were directly connected to the private network. The be ...
or secure
Hypertext Transfer Protocol
The Hypertext Transfer Protocol (HTTP) is an application layer protocol in the Internet protocol suite model for distributed, collaborative, hypermedia information systems. HTTP is the foundation of data communication for the World Wide We ...
over
Transport Layer Security
Transport Layer Security (TLS) is a cryptographic protocol designed to provide communications security over a computer network. The protocol is widely used in applications such as email, instant messaging, and voice over IP, but its use in securi ...
(
HTTPS
Hypertext Transfer Protocol Secure (HTTPS) is an extension of the Hypertext Transfer Protocol (HTTP). It is used for secure communication over a computer network, and is widely used on the Internet. In HTTPS, the communication protocol is enc ...
).
Wi-Fi Protected Access encryption (WPA2) is considered secure, provided a strong
passphrase
A passphrase is a sequence of words or other text used to control access to a computer system, program or data. It is similar to a password in usage, but a passphrase is generally longer for added security. Passphrases are often used to control ...
is used. In 2018,
WPA3 was announced as a replacement for WPA2, increasing security; it rolled out on June 26.
Piggybacking
Piggybacking refers to access to a wireless Internet connection by bringing one's computer within the range of another's wireless connection, and using that service without the subscriber's explicit permission or knowledge.
During the early popular adoption of
802.11
IEEE 802.11 is part of the IEEE 802 set of local area network (LAN) technical standards, and specifies the set of media access control (MAC) and physical layer (PHY) protocols for implementing wireless local area network (WLAN) computer com ...
, providing open access points for anyone within range to use was encouraged to cultivate
wireless community network
Wireless community networks (WCNs) or wireless community projects or simply community networks, are non-centralized, self-managed and collaborative networks organized in a grassroots fashion by communities, NGO's and cooperatives in order to provi ...
s, particularly since people on average use only a fraction of their downstream bandwidth at any given time.
Recreational logging and mapping of other people's access points have become known as
wardriving
Wardriving is the act of searching for Wi-Fi wireless networks, usually from a moving vehicle, using a laptop or smartphone. Software for wardriving is freely available on the internet.
Warbiking, warcycling, warwalking and similar use the sam ...
. Indeed, many access points are intentionally installed without security turned on so that they can be used as a free service. Providing access to one's Internet connection in this fashion may breach the Terms of Service or contract with the
ISP
An Internet service provider (ISP) is an organization that provides services for accessing, using, or participating in the Internet. ISPs can be organized in various forms, such as commercial, community-owned, non-profit, or otherwise private ...
. These activities do not result in sanctions in most jurisdictions; however, legislation and
case law
Case law, also used interchangeably with common law, is law that is based on precedents, that is the judicial decisions from previous cases, rather than law based on constitutions, statutes, or regulations. Case law uses the detailed facts of ...
differ considerably across the world. A proposal to leave
graffiti
Graffiti (plural; singular ''graffiti'' or ''graffito'', the latter rarely used except in archeology) is art that is written, painted or drawn on a wall or other surface, usually without permission and within public view. Graffiti ranges from s ...
describing available services was called
warchalking
Warchalking is the drawing of symbols in public places to advertise an open Wi-Fi network.
Inspired by hobo symbols, the warchalking marks were conceived by a group of friends in June 2002 and publicised by Matt Jones who designed the set of ico ...
.
Piggybacking often occurs unintentionally – a technically unfamiliar user might not change the default "unsecured" settings to their access point and operating systems can be configured to connect automatically to any available wireless network. A user who happens to start up a laptop in the vicinity of an access point may find the computer has joined the network without any visible indication. Moreover, a user intending to join one network may instead end up on another one if the latter has a stronger signal. In combination with automatic discovery of other network resources (see
DHCP
The Dynamic Host Configuration Protocol (DHCP) is a network management protocol used on Internet Protocol (IP) networks for automatically assigning IP addresses and other communication parameters to devices connected to the network using a cli ...
and
Zeroconf
Zero-configuration networking (zeroconf) is a set of technologies that automatically creates a usable computer network based on the Internet Protocol Suite (TCP/IP) when computers or network peripherals are interconnected. It does not require ma ...
) this could lead wireless users to send sensitive data to the wrong middle-man when seeking a destination (see
man-in-the-middle attack
In cryptography and computer security, a man-in-the-middle, monster-in-the-middle, machine-in-the-middle, monkey-in-the-middle, meddler-in-the-middle, manipulator-in-the-middle (MITM), person-in-the-middle (PITM) or adversary-in-the-middle (AiTM) ...
). For example, a user could inadvertently use an unsecured network to log into a
website
A website (also written as a web site) is a collection of web pages and related content that is identified by a common domain name and published on at least one web server. Examples of notable websites are Google, Facebook, Amazon, and W ...
, thereby making the login credentials available to anyone listening, if the website uses an insecure protocol such as plain
HTTP
The Hypertext Transfer Protocol (HTTP) is an application layer protocol in the Internet protocol suite model for distributed, collaborative, hypermedia information systems. HTTP is the foundation of data communication for the World Wide We ...
without
TLS
TLS may refer to:
Computing
* Transport Layer Security, a cryptographic protocol for secure computer network communication
* Thread level speculation, an optimisation on multiprocessor CPUs
* Thread-local storage, a mechanism for allocating vari ...
.
On an unsecured access point, an unauthorized user can obtain security information (factory preset passphrase and/or Wi-Fi Protected Setup PIN) from a label on a wireless access point and use this information (or connect by the Wi-Fi Protected Setup pushbutton method) to commit unauthorized and/or unlawful activities.
Societal aspects
Wireless internet access has become much more embedded in society. It has thus changed how the society functions in many ways.
Influence on developing countries
Over half the world does not have access to the internet,
prominently rural areas in developing nations. Technology that has been implemented in more developed nations is often costly and low energy efficient. This has led to developing nations using more low-tech networks, frequently implementing renewable power sources that can solely be maintained through
solar power
Solar power is the conversion of energy from sunlight into electricity, either directly using photovoltaics (PV) or indirectly using concentrated solar power. Photovoltaic cells convert light into an electric current using the photovolta ...
, creating a network that is resistant to disruptions such as power outages. For instance, in 2007 a 450 km (280 mile) network between Cabo Pantoja and
Iquitos
Iquitos (; ) is the capital city of Peru's Maynas Province and Loreto Region. It is the largest metropolis in the Peruvian Amazon, east of the Andes, as well as the ninth-most populous city of Peru. Iquitos is the largest city in the world t ...
in
Peru
, image_flag = Flag of Peru.svg
, image_coat = Escudo nacional del Perú.svg
, other_symbol = Great Seal of the State
, other_symbol_type = National seal
, national_motto = "Firm and Happy f ...
was erected in which all equipment is powered only by
solar panel
A solar cell panel, solar electric panel, photo-voltaic (PV) module, PV panel or solar panel is an assembly of photovoltaic solar cells mounted in a (usually rectangular) frame, and a neatly organised collection of PV panels is called a photo ...
s.
These long-range Wi-Fi networks have two main uses: offer internet access to populations in isolated villages, and to provide healthcare to isolated communities. In the case of the aforementioned example, it connects the central hospital in Iquitos to 15 medical outposts which are intended for remote diagnosis.
Work habits
Access to Wi-Fi in public spaces such as cafes or parks allows people, in particular freelancers, to work remotely. While the accessibility of Wi-Fi is the strongest factor when choosing a place to work (75% of people would choose a place that provides Wi-Fi over one that does not),
other factors influence the choice of specific
hotspots
Hotspot, Hot Spot or Hot spot may refer to:
Places
* Hot Spot, Kentucky, a community in the United States
Arts, entertainment, and media Fictional entities
* Hot Spot (comics), a name for the DC Comics character Isaiah Crockett
* Hot Spot (Tra ...
. These vary from the accessibility of other resources, like books, the location of the workplace, and the social aspect of meeting other people in the same place. Moreover, the increase of people working from public places results in more customers for local businesses thus providing an economic stimulus to the area.
Additionally, in the same study it has been noted that wireless connection provides more freedom of movement while working. Both when working at home or from the office it allows the displacement between different rooms or areas. In some offices (notably Cisco offices in New York) the employees do not have assigned desks but can work from any office connecting their laptop to Wi-Fi
hotspot.
Housing
The internet has become an integral part of living. 81.9% of American households have internet access. Additionally, 89% of American households with broadband connect via wireless technologies. 72.9% of American households have Wi-Fi.
Wi-Fi networks have also affected how the interior of homes and hotels are arranged. For instance, architects have described that their clients no longer wanted only one room as their home office, but would like to work near the fireplace or have the possibility to work in different rooms. This contradicts architect's pre-existing ideas of the use of rooms that they designed. Additionally, some hotels have noted that guests prefer to stay in certain rooms since they receive a stronger Wi-Fi signal.
Health concerns
The
World Health Organization
The World Health Organization (WHO) is a specialized agency of the United Nations responsible for international public health. The WHO Constitution states its main objective as "the attainment by all peoples of the highest possible level o ...
(WHO) says, "no health effects are expected from exposure to RF fields from base stations and wireless networks", but notes that they promote research into effects from other RF sources. (a category used when "a causal association is considered credible, but when chance, bias or confounding cannot be ruled out with reasonable confidence"), this classification was based on risks associated with wireless phone use rather than Wi-Fi networks.
The United Kingdom's
Health Protection Agency
The Health Protection Agency (HPA) was a non-departmental public body in the United Kingdom. It was an organisation that was set up by the UK government in 2003 to protect the public from threats to their health from infectious diseases and envi ...
reported in 2007 that exposure to Wi-Fi for a year results in the "same amount of radiation from a 20-minute mobile phone call".
A review of studies involving 725 people who claimed
electromagnetic hypersensitivity
Electromagnetic hypersensitivity (EHS) is a claimed sensitivity to electromagnetic fields, to which negative symptoms are attributed. EHS has no scientific basis and is not a recognised medical diagnosis. Claims are characterized by a "variet ...
, "...suggests that 'electromagnetic hypersensitivity' is unrelated to the presence of an EMF, although more research into this phenomenon is required."
Alternatives
Several other wireless technologies provide alternatives to Wi-Fi for different use cases:
*
Bluetooth
Bluetooth is a short-range wireless technology standard that is used for exchanging data between fixed and mobile devices over short distances and building personal area networks (PANs). In the most widely used mode, transmission power is limi ...
, a short-distance network
*
Bluetooth Low Energy
Bluetooth Low Energy (Bluetooth LE, colloquially BLE, formerly marketed as Bluetooth Smart) is a wireless personal area network technology designed and marketed by the Bluetooth Special Interest Group (Bluetooth SIG) aimed at novel applications i ...
, a low-power variant of Bluetooth
*
Zigbee
Zigbee is an IEEE 802.15.4-based specification for a suite of high-level communication protocols used to create personal area networks with small, low-power digital radios, such as for home automation, medical device data collection, and oth ...
, a low-power, low data rate, short-distance communication protocol
*
Cellular network
A cellular network or mobile network is a communication network where the link to and from end nodes is wireless. The network is distributed over land areas called "cells", each served by at least one fixed-location transceiver (typically th ...
s, used by smartphones
*
WiMAX
Worldwide Interoperability for Microwave Access (WiMAX) is a family of wireless broadband communication standards based on the IEEE 802.16 set of standards, which provide physical layer (PHY) and media access control (MAC) options.
The WiMAX ...
, for providing long range wireless internet connectivity
*
LoRa
Lora is a female given name and family name in the Spanish language of French origin meaning from Lorraine, a region in Northeastern France.
As a given name, Lora may also be a variant of Laura or derived from an Italian hypocoristic of either E ...
, for long range wireless with low data rate
Some alternatives are "no new wires", re-using existing cable:
*
G.hn
G.hn is a specification for home networking with data rates up to 2 Gbit/s and operation over four types of legacy wires: telephone wiring, coaxial cables, power lines and plastic optical fiber. A single G.hn semiconductor device is able to n ...
, which uses existing home wiring, such as phone and
power lines
Electric power transmission is the bulk movement of electrical energy from a generating site, such as a power plant, to an electrical substation. The interconnected lines that facilitate this movement form a ''transmission network''. This is d ...
Several ''wired'' technologies for computer networking, which provide viable alternatives to Wi-Fi:
*
Ethernet over twisted pair
Ethernet over twisted-pair technologies use twisted-pair cables for the physical layer of an Ethernet computer network. They are a subset of all Ethernet physical layers.
Early Ethernet used various grades of coaxial cable, but in 1984, Sta ...
See also
*
Gi-Fi Gi-Fi or gigabit wireless refers to a wireless communication at a data rate of more than one billion bits (gigabit) per second.
By 2004 some trade press used the term "Gi-Fi" to refer to faster versions of the IEEE 802.11 standards marketed unde ...
a term used by some trade press to refer to faster versions of the IEEE 802.11 standards
*
HiperLAN
HiperLAN (High Performance Radio LAN) is a wireless LAN standard. It is a European alternative for the IEEE 802.11 standards (the IEEE is an international organization). It is defined by the European Telecommunications Standards Institute (ETSI) ...
*
Indoor positioning system
An indoor positioning system (IPS) is a network of devices used to locate people or objects where GPS and other satellite technologies lack precision or fail entirely, such as inside multistory buildings, airports, alleys, parking garages, and und ...
*
Li-Fi
*
List of WLAN channels
Wireless LAN (WLAN) channels are frequently accessed using IEEE 802.11 protocols, and equipment that does so is sold mostly under the trademark Wi-Fi. Other equipment also accesses the same channels, such as Bluetooth. The radio frequency (RF) spec ...
*
Operating system Wi-Fi support
*
Power-line communication
Power-line communication (also known as power-line carrier or PLC) carries data on a conductor that is also used simultaneously for AC electric power transmission or electric power distribution to consumers.
A wide range of power-line communicat ...
*
San Francisco Digital Inclusion Strategy
*
WiGig
WiGig, alternatively known as 60 GHz Wi-Fi, refers to a set of 60 GHz wireless network protocols. It includes the current IEEE 802.11ad standard and also the IEEE 802.11ay standard.
The WiGig specification allows devices to communicate wi ...
*
Wireless Broadband Alliance
*
Wi-Fi Direct
Wi-Fi Direct (formerly Wi-Fi Peer-to-Peer) is a Wi-Fi standard for peer-to-peer wireless connections that allows two devices to establish a direct Wi-Fi connection without an intermediary wireless access point, router, or Internet connection. W ...
*
Hotspot (Wi-Fi)
A hotspot is a physical location where people can obtain Internet access, typically using Wi-Fi technology, via a wireless local-area network (WLAN) using a router connected to an Internet service provider.
Public hotspots may be created by ...
*
Bluetooth
Bluetooth is a short-range wireless technology standard that is used for exchanging data between fixed and mobile devices over short distances and building personal area networks (PANs). In the most widely used mode, transmission power is limi ...
Explanatory notes
References
Further reading
*
{{Telecommunications
Australian inventions
Computer-related introductions in 1999
Networking standards
Wireless communication systems
 Wi-Fi's radio bands have relatively high absorption and work best for line-of-sight use. Many common obstructions such as walls, pillars, home appliances, etc. may greatly reduce range, but this also helps minimize interference between different networks in crowded environments. An access point range of about indoors while some access points claim up to a range outdoors. Hotspot coverage can be as small as a single room with walls that block radio waves, or as large as many square kilometres using many overlapping access points with
Wi-Fi's radio bands have relatively high absorption and work best for line-of-sight use. Many common obstructions such as walls, pillars, home appliances, etc. may greatly reduce range, but this also helps minimize interference between different networks in crowded environments. An access point range of about indoors while some access points claim up to a range outdoors. Hotspot coverage can be as small as a single room with walls that block radio waves, or as large as many square kilometres using many overlapping access points with  The
The  In the early 2000s, many cities around the world announced plans to construct citywide Wi-Fi networks. There are many successful examples; in 2004,
In the early 2000s, many cities around the world announced plans to construct citywide Wi-Fi networks. There are many successful examples; in 2004, 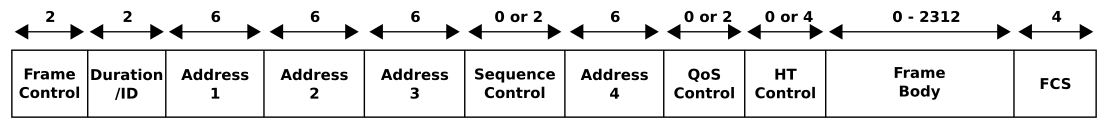 Wi-Fi is part of the IEEE 802 protocol family. The data is organized into 802.11 frames that are very similar to
Wi-Fi is part of the IEEE 802 protocol family. The data is organized into 802.11 frames that are very similar to  In infrastructure mode, which is the most common mode used, all communications go through a base station. For communications within the network, this introduces an extra use of the airwaves but has the advantage that any two stations that can communicate with the base station can also communicate through the base station, which enormously simplifies the protocols.
In infrastructure mode, which is the most common mode used, all communications go through a base station. For communications within the network, this introduces an extra use of the airwaves but has the advantage that any two stations that can communicate with the base station can also communicate through the base station, which enormously simplifies the protocols.
 Wi-Fi connections can be blocked or the Internet speed lowered by having other devices in the same area. Wi-Fi protocols are designed to share the wavebands reasonably fairly, and this often works with little to no disruption. To minimize collisions with Wi-Fi and non-Wi-Fi devices, Wi-Fi employs
Wi-Fi connections can be blocked or the Internet speed lowered by having other devices in the same area. Wi-Fi protocols are designed to share the wavebands reasonably fairly, and this often works with little to no disruption. To minimize collisions with Wi-Fi and non-Wi-Fi devices, Wi-Fi employs  Wi-Fi allows wireless deployment of local area networks (LANs). Also, spaces where cables cannot be run, such as outdoor areas and historical buildings, can host wireless LANs. However, building walls of certain materials, such as stone with high metal content, can block Wi-Fi signals.
A Wi-Fi device is a short-range
Wi-Fi allows wireless deployment of local area networks (LANs). Also, spaces where cables cannot be run, such as outdoor areas and historical buildings, can host wireless LANs. However, building walls of certain materials, such as stone with high metal content, can block Wi-Fi signals.
A Wi-Fi device is a short-range  A wireless access point (WAP) connects a group of wireless devices to an adjacent wired LAN. An access point resembles a network hub, relaying
A wireless access point (WAP) connects a group of wireless devices to an adjacent wired LAN. An access point resembles a network hub, relaying  Wireless adapters allow devices to connect to a wireless network. These adapters connect to devices using various external or internal interconnects such as PCI, miniPCI, USB, ExpressCard, Cardbus, and
Wireless adapters allow devices to connect to a wireless network. These adapters connect to devices using various external or internal interconnects such as PCI, miniPCI, USB, ExpressCard, Cardbus, and  A flaw in a feature added to Wi-Fi in 2007, called
A flaw in a feature added to Wi-Fi in 2007, called