Secret of the Tomb on:
[Wikipedia]
[Google]
[Amazon]

 Secrecy is the practice of hiding information from certain individuals or groups who do not have the "need to know", perhaps while sharing it with other individuals. That which is kept hidden is known as the secret.
Secrecy is often controversial, depending on the content or nature of the secret, the group or people keeping the secret, and the motivation for secrecy.
Secrecy is the practice of hiding information from certain individuals or groups who do not have the "need to know", perhaps while sharing it with other individuals. That which is kept hidden is known as the secret.
Secrecy is often controversial, depending on the content or nature of the secret, the group or people keeping the secret, and the motivation for secrecy.
 Secrecy by government entities is often decried as excessive or in promotion of poor operation; excessive revelation of information on individuals can conflict with virtues of privacy and
Secrecy by government entities is often decried as excessive or in promotion of poor operation; excessive revelation of information on individuals can conflict with virtues of privacy and 
 Secrecy can exist in a number of different ways: encoding or
Secrecy can exist in a number of different ways: encoding or
 Secrets are sometimes kept to provide the pleasure of surprise. This includes keeping secret about a surprise party, not telling
Secrets are sometimes kept to provide the pleasure of surprise. This includes keeping secret about a surprise party, not telling
security clearance
for access and other protection methods, such as keeping documents in a safe, are stipulated. Few people dispute the desirability of keeping
competitive advantage
to meet legal requirements, or, in some cases, to conceal nefarious behavior. New products under development, unique manufacturing techniques, or simply lists of customers are types of information protected by
Commercial-in-confidence
(or secrecy) clauses in contracts between government and private providers further limits public accountability of governments and prevents proper public scrutiny of the performance and probity of the private companies. Concerns have been raised that 'commercial-in-confidence' is open to abuse because it can be deliberately used to hide corporate or government maladministration and even corruption.
 Preservation of secrets is one of the goals of
Preservation of secrets is one of the goals of
cryptographic keys
Many believe that security technology can be more effective if it itself is not kept secret.
Information hiding
is a design principle in much
 Military secrecy is the concealing of information about martial affairs that is purposely not made available to the general public and hence to any enemy, in order to gain an advantage or to not reveal a weakness, to avoid
Military secrecy is the concealing of information about martial affairs that is purposely not made available to the general public and hence to any enemy, in order to gain an advantage or to not reveal a weakness, to avoid
Preview.
An Open Source Collection of Readings on Secrecy
Secrecy News
from the Federation of American Scientists {{Authority control Classified information

 Secrecy is the practice of hiding information from certain individuals or groups who do not have the "need to know", perhaps while sharing it with other individuals. That which is kept hidden is known as the secret.
Secrecy is often controversial, depending on the content or nature of the secret, the group or people keeping the secret, and the motivation for secrecy.
Secrecy is the practice of hiding information from certain individuals or groups who do not have the "need to know", perhaps while sharing it with other individuals. That which is kept hidden is known as the secret.
Secrecy is often controversial, depending on the content or nature of the secret, the group or people keeping the secret, and the motivation for secrecy.
 Secrecy by government entities is often decried as excessive or in promotion of poor operation; excessive revelation of information on individuals can conflict with virtues of privacy and
Secrecy by government entities is often decried as excessive or in promotion of poor operation; excessive revelation of information on individuals can conflict with virtues of privacy and confidentiality
Confidentiality involves a set of rules or a promise usually executed through confidentiality agreements that limits the access or places restrictions on certain types of information.
Legal confidentiality
By law, lawyers are often required ...
. It is often contrasted with social transparency.

 Secrecy can exist in a number of different ways: encoding or
Secrecy can exist in a number of different ways: encoding or encryption
In cryptography, encryption is the process of encoding information. This process converts the original representation of the information, known as plaintext, into an alternative form known as ciphertext. Ideally, only authorized parties can de ...
(where mathematical and technical strategies are used to hide messages), true secrecy (where restrictions are put upon those who take part of the message, such as through government security classification) and obfuscation, where secrets are hidden in plain sight behind complex idiosyncratic language (jargon
Jargon is the specialized terminology associated with a particular field or area of activity. Jargon is normally employed in a particular communicative context and may not be well understood outside that context. The context is usually a partic ...
) or steganography
Steganography ( ) is the practice of representing information within another message or physical object, in such a manner that the presence of the information is not evident to human inspection. In computing/electronic contexts, a computer file, ...
.
Another classification proposed by Claude Shannon in 1948 reads there are three systems of secrecy within communication:
# concealment systems, including such methods as invisible ink, concealing a message in an innocent text, or in a fake covering cryptogram, or other methods in which the existence of the message is concealed from the enemy
# privacy systems, for example, voice inversion
Voice inversion scrambling is an analog method of obscuring the content of a transmission. It is sometimes used in public service radio, automobile racing, cordless telephones and the Family Radio Service. Without a descrambler, the transmission ma ...
, in which special equipment is required to recover the message
# "true" secrecy systems where the meaning of the message is concealed by the cypher, code, etc., although its existence is not hidden, and the enemy is assumed to have any special equipment necessary to intercept and record the transmitted signal
Sociology
Animal
Animals are multicellular, eukaryotic organisms in the Kingdom (biology), biological kingdom Animalia. With few exceptions, animals Heterotroph, consume organic material, Cellular respiration#Aerobic respiration, breathe oxygen, are Motilit ...
s conceal the location of their den or nest
A nest is a structure built for certain animals to hold eggs or young. Although nests are most closely associated with birds, members of all classes of vertebrates and some invertebrates construct nests. They may be composed of organic materi ...
from predators
Predation is a biological interaction where one organism, the predator, kills and eats another organism, its prey. It is one of a family of common feeding behaviours that includes parasitism and micropredation (which usually do not kill th ...
. Squirrels bury nuts, hiding them, and they try to remember their locations later.
Human
Humans (''Homo sapiens'') are the most abundant and widespread species of primate, characterized by bipedalism and exceptional cognitive skills due to a large and complex brain. This has enabled the development of advanced tools, cultu ...
s attempt to consciously conceal aspects of themselves from others due to shame
Shame is an unpleasant self-conscious emotion often associated with negative self-evaluation; motivation to quit; and feelings of pain, exposure, distrust, powerlessness, and worthlessness.
Definition
Shame is a discrete, basic emotion, d ...
, or from fear
Fear is an intensely unpleasant emotion in response to perceiving or recognizing a danger or threat. Fear causes physiological changes that may produce behavioral reactions such as mounting an aggressive response or fleeing the threat. Fear ...
of violence, rejection, harassment, loss of acceptance, or loss of employment. Humans may also attempt to conceal aspects of their own self
The self is an individual as the object of that individual’s own reflective consciousness. Since the ''self'' is a reference by a subject to the same subject, this reference is necessarily subjective. The sense of having a self—or ''selfhoo ...
which they are not capable of incorporating psychologically into their conscious
Consciousness, at its simplest, is sentience and awareness of internal and external existence. However, the lack of definitions has led to millennia of analyses, explanations and debates by philosophers, theologians, linguisticians, and scien ...
being. Families
Family (from la, familia) is a group of people related either by consanguinity (by recognized birth) or affinity (by marriage or other relationship). The purpose of the family is to maintain the well-being of its members and of society. Ideal ...
sometimes maintain "family secret
A family secret is a secret kept within a family. Most families have secrets, but the kind and importance vary. Family secrets can be shared by the whole family, by some family members or kept by an individual member of the family. The secret can r ...
s", obliging family members never to discuss disagreeable issues concerning the family with outsiders or sometimes even within the family. Many "family secrets" are maintained by using a mutually agreed-upon construct (an official family story) when speaking with outside members. Agreement to maintain the secret is often coerced through "shaming" and reference to family honor
Honour (British English) or honor (American English; see spelling differences) is the idea of a bond between an individual and a society as a quality of a person that is both of social teaching and of personal ethos, that manifests itself as a ...
. The information may even be something as trivial as a recipe.
 Secrets are sometimes kept to provide the pleasure of surprise. This includes keeping secret about a surprise party, not telling
Secrets are sometimes kept to provide the pleasure of surprise. This includes keeping secret about a surprise party, not telling spoiler
Spoiler is a security vulnerability on modern computer central processing units that use speculative execution. It exploits side-effects of speculative execution to improve the efficiency of Rowhammer and other related memory and cache attacks. Ac ...
s of a story, and avoiding exposure of a magic trick.
Keeping one's strategy secret is important in many aspects of game theory.
In anthropology
Anthropology is the scientific study of humanity, concerned with human behavior, human biology, cultures, societies, and linguistics, in both the present and past, including past human species. Social anthropology studies patterns of be ...
secret sharing is one way for people to establish traditional relations with other people. A commonly used narrative that describes this kind of behavior is Joseph Conrad's short story " The Secret Sharer".
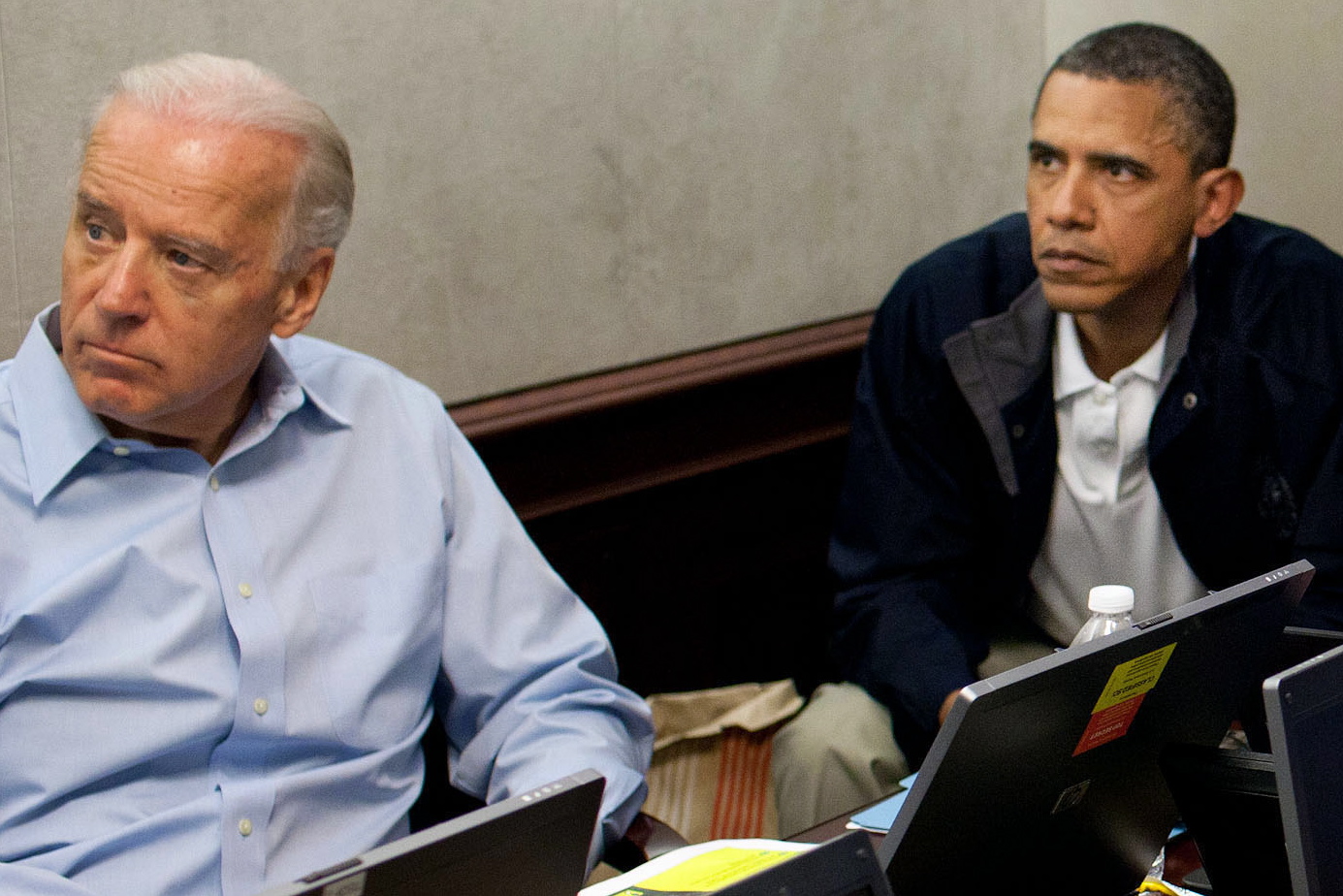
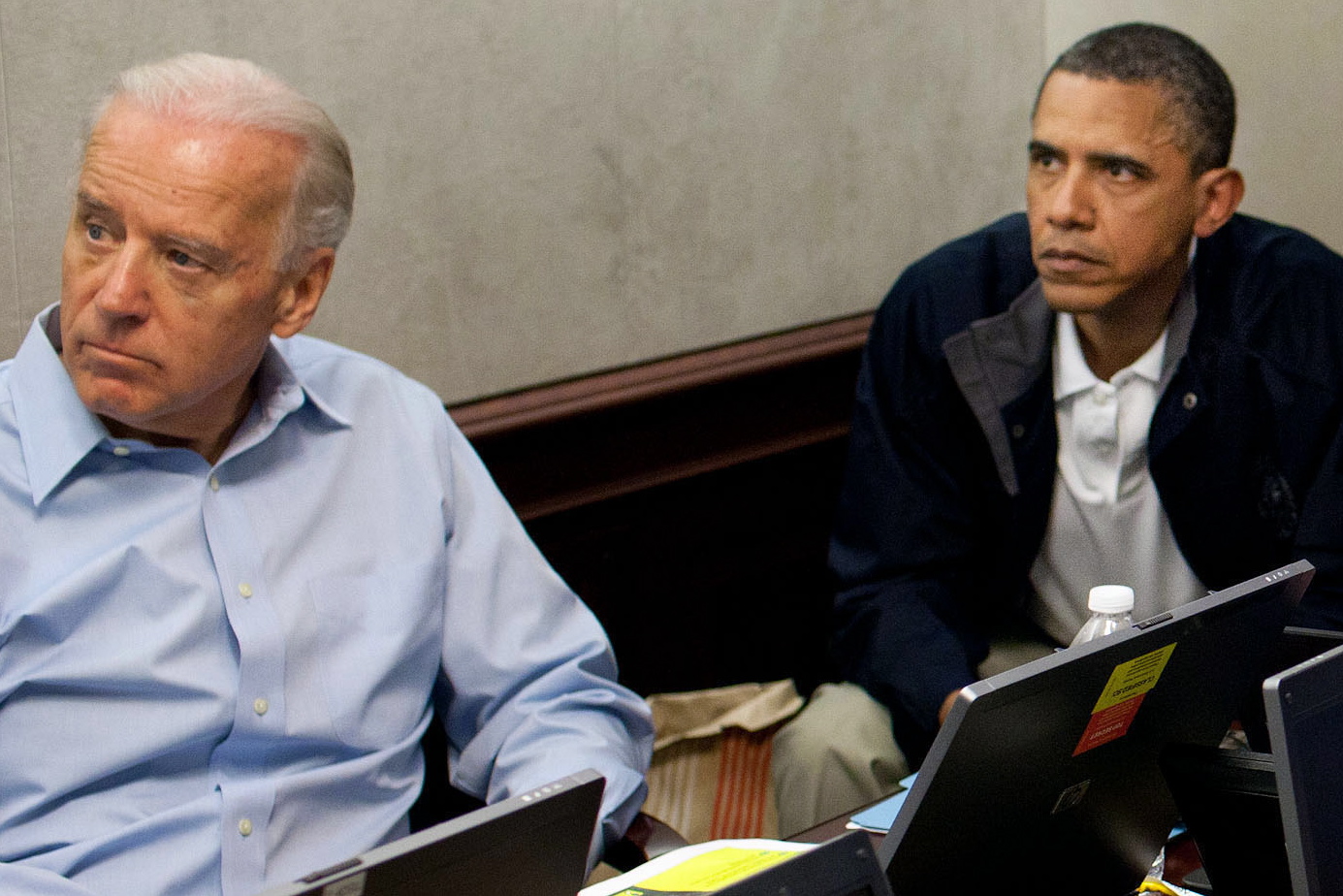
Government
Government
A government is the system or group of people governing an organized community, generally a state.
In the case of its broad associative definition, government normally consists of legislature, executive, and judiciary. Government is ...
s often attempt to conceal information from other governments and the public. These state secrets can include weapon
A weapon, arm or armament is any implement or device that can be used to deter, threaten, inflict physical damage, harm, or kill. Weapons are used to increase the efficacy and efficiency of activities such as hunting, crime, law enforcement, ...
designs, military plans, diplomatic negotiation
Negotiation is a dialogue between two or more people or parties to reach the desired outcome regarding one or more issues of conflict. It is an interaction between entities who aspire to agree on matters of mutual interest. The agreement c ...
tactics, and secrets obtained illicitly from others ("intelligence
Intelligence has been defined in many ways: the capacity for abstraction, logic, understanding, self-awareness, learning, emotional knowledge, reasoning, planning, creativity, critical thinking, and problem-solving. More generally, it can be des ...
"). Most nations have some form of Official Secrets Act (the Espionage Act
The Espionage Act of 1917 is a United States federal law enacted on June 15, 1917, shortly after the United States entered World War I. It has been amended numerous times over the years. It was originally found in Title 50 of the U.S. Code (War ...
in the U.S.) and classify material according to the level of protection needed (hence the term "classified information
Classified information is material that a government body deems to be sensitive information that must be protected. Access is restricted by law or regulation to particular groups of people with the necessary security clearance and need to kn ...
"). An individual needs security clearance
for access and other protection methods, such as keeping documents in a safe, are stipulated. Few people dispute the desirability of keeping
Critical Nuclear Weapon Design Information {{Short description, Category of U.S. top secret classified data
Critical Nuclear Weapon Design Information (CNWDI, often pronounced ''SIN-widdy'' or ''SIN-wuh-dee'') is a U.S. Department of Defense (DoD) category of Top Secret Restricted Data or ...
secret, but many believe government secrecy to be excessive and too often employed for political purposes. Many countries have laws that attempt to limit government secrecy, such as the U.S. Freedom of Information Act Freedom of Information Act may refer to the following legislations in different jurisdictions which mandate the national government to disclose certain data to the general public upon request:
* Freedom of Information Act 1982, the Australian act
* ...
and sunshine laws. Government officials sometimes leak
A leak is a way (usually an opening) for fluid to escape a container or fluid-containing system, such as a tank or a ship's hull, through which the contents of the container can escape or outside matter can enter the container. Leaks are usually ...
information they are supposed to keep secret. (''For a recent (2005) example, see Plame affair
The Plame affair (also known as the CIA leak scandal and Plamegate) was a political scandal that revolved around journalist Robert Novak's public identification of Valerie Plame as a covert Central Intelligence Agency officer in 2003.
In 2002, ...
.'')
Secrecy in elections is a growing issue, particularly secrecy of vote counts on computerized vote counting machines. While voting, citizens are acting in a unique sovereign or "owner" capacity (instead of being a subject of the laws, as is true outside of elections) in selecting their government servants. It is argued that secrecy is impermissible as against the public in the area of elections where the government gets all of its power and taxing authority. In any event, permissible secrecy varies significantly with the context involved.
Corporations
Organizations, ranging from multi-national for profitcorporation
A corporation is an organization—usually a group of people or a company—authorized by the state to act as a single entity (a legal entity recognized by private and public law "born out of statute"; a legal person in legal context) and ...
s to nonprofit charities, keep secrets focompetitive advantage
to meet legal requirements, or, in some cases, to conceal nefarious behavior. New products under development, unique manufacturing techniques, or simply lists of customers are types of information protected by
trade secret
Trade secrets are a type of intellectual property that includes formulas, practices, processes, designs, instruments, patterns, or compilations of information that have inherent economic value because they are not generally known or readily ...
laws.
Research on corporate secrecy has studied the factors supporting secret organizations. In particular, scholars in economics and management have paid attention to the way firms participating in cartels work together to maintain secrecy and conceal their activities from antitrust authorities. The diversity of the participants (in terms of age and size of the firms) influences their ability to coordinate to avoid being detected.
The patent
A patent is a type of intellectual property that gives its owner the legal right to exclude others from making, using, or selling an invention for a limited period of time in exchange for publishing an enabling disclosure of the invention."A ...
system encourages inventors to publish information in exchange for a limited time monopoly
A monopoly (from Greek el, μόνος, mónos, single, alone, label=none and el, πωλεῖν, pōleîn, to sell, label=none), as described by Irving Fisher, is a market with the "absence of competition", creating a situation where a speci ...
on its use, though patent applications are initially secret. Secret societies
A secret society is a club or an organization whose activities, events, inner functioning, or membership are concealed. The society may or may not attempt to conceal its existence. The term usually excludes covert groups, such as intelligence a ...
use secrecy as a way to attract members by creating a sense of importance.
Shell companies
A shell corporation is a company or corporation that exists only on paper and has no office and no employees, but may have a bank account or may hold passive investments or be the registered owner of assets, such as intellectual property, or ...
may be used to launder money from criminal activity, to finance terrorism, or to evade taxes. Registers of beneficial ownership
In domestic and international commercial law, a beneficial owner is a natural person or persons who ultimately owns or controls an interest in a legal entity or arrangement, such as a company, a trust, or a foundation. Legal owners (i.e. the own ...
aim at fighting corporate secrecy in that sense.
Other laws ''require'' organizations to keep certain information secret, such as medical record
The terms medical record, health record and medical chart are used somewhat interchangeably to describe the systematic documentation of a single patient's medical history and care across time within one particular health care provider's jurisdic ...
s (HIPAA
The Health Insurance Portability and Accountability Act of 1996 (HIPAA or the Kennedy– Kassebaum Act) is a United States Act of Congress enacted by the 104th United States Congress and signed into law by President Bill Clinton on August 21, 1 ...
in the U.S.), or financial reports that are under preparation (to limit insider trading). Europe has particularly strict laws about database
In computing, a database is an organized collection of data stored and accessed electronically. Small databases can be stored on a file system, while large databases are hosted on computer clusters or cloud storage. The design of databases s ...
privacy.
In many countries, neoliberal reforms of government have included expanding the outsourcing of government tasks and functions to private businesses with the aim of improving efficiency and effectiveness in government administration. However, among the criticisms of these reforms is the claim that the pervasive use ofCommercial-in-confidence
(or secrecy) clauses in contracts between government and private providers further limits public accountability of governments and prevents proper public scrutiny of the performance and probity of the private companies. Concerns have been raised that 'commercial-in-confidence' is open to abuse because it can be deliberately used to hide corporate or government maladministration and even corruption.
Computing
 Preservation of secrets is one of the goals of
Preservation of secrets is one of the goals of information security
Information security, sometimes shortened to InfoSec, is the practice of protecting information by mitigating information risks. It is part of information risk management. It typically involves preventing or reducing the probability of unauthorize ...
. Techniques used include physical security
Physical security describes security measures that are designed to deny unauthorized access to facilities, equipment and resources and to protect personnel and property from damage or harm (such as espionage, theft, or terrorist attacks). Physica ...
and cryptography
Cryptography, or cryptology (from grc, , translit=kryptós "hidden, secret"; and ''graphein'', "to write", or ''-logia'', "study", respectively), is the practice and study of techniques for secure communication in the presence of adver ...
. The latter depends on the secrecy ocryptographic keys
Many believe that security technology can be more effective if it itself is not kept secret.
Information hiding
is a design principle in much
software engineering
Software engineering is a systematic engineering approach to software development.
A software engineer is a person who applies the principles of software engineering to design, develop, maintain, test, and evaluate computer software. The term '' ...
. It is considered easier to verify software reliability if one can be sure that different parts of the program can only access (and therefore depend on) a known limited amount of information.
Military
 Military secrecy is the concealing of information about martial affairs that is purposely not made available to the general public and hence to any enemy, in order to gain an advantage or to not reveal a weakness, to avoid
Military secrecy is the concealing of information about martial affairs that is purposely not made available to the general public and hence to any enemy, in order to gain an advantage or to not reveal a weakness, to avoid embarrassment
Embarrassment or awkwardness is an emotional state that is associated with mild to severe levels of discomfort, and which is usually experienced when someone commits (or thinks of) a socially unacceptable or frowned-upon act that is witnessed ...
, or to help in propaganda efforts. Most military secrets are tactical in nature, such as the strengths and weaknesses of weapon systems, tactics
Tactic(s) or Tactical may refer to:
* Tactic (method), a conceptual action implemented as one or more specific tasks
** Military tactics, the disposition and maneuver of units on a particular sea or battlefield
** Chess tactics
** Political tact ...
, training methods, plans, and the number and location of specific weapons. Some secrets involve information in broader areas, such as secure communications, cryptography
Cryptography, or cryptology (from grc, , translit=kryptós "hidden, secret"; and ''graphein'', "to write", or ''-logia'', "study", respectively), is the practice and study of techniques for secure communication in the presence of adver ...
, intelligence operations, and cooperation with third parties.
Views
Excessive secrecy is often citedLightfoot, Geoffrey, and Tomasz Piotr Wisniewski. "Information asymmetry and power in a surveillance society." Information and Organization 24.4 (2014): 214-235. as a source of much human conflict. One may have to lie in order to hold a secret, which might lead to psychological repercussions. The alternative, declining to answer when asked something, may suggest the answer and may therefore not always be suitable for keeping a secret. Also, the other may insist that one answer the question. Nearly 2500 years ago,Sophocles
Sophocles (; grc, Σοφοκλῆς, , Sophoklễs; 497/6 – winter 406/5 BC)Sommerstein (2002), p. 41. is one of three ancient Greek tragedians, at least one of whose plays has survived in full. His first plays were written later than, or c ...
wrote, "Do nothing secretly; for Time sees and hears all things, and discloses all." Gautama Siddhartha
Siddhartha Gautama, most commonly referred to as the Buddha, was a wandering ascetic and religious teacher who lived in South Asia during the 6th or 5th century BCE and founded Buddhism.
According to Buddhist tradition, he was born in Lu ...
, the Buddha
Siddhartha Gautama, most commonly referred to as the Buddha, was a wandering ascetic and religious teacher who lived in South Asia during the 6th or 5th century BCE and founded Buddhism.
According to Buddhist tradition, he was born in L ...
, once said "Three things cannot long stay hidden: the sun
The Sun is the star at the center of the Solar System. It is a nearly perfect ball of hot plasma, heated to incandescence by nuclear fusion reactions in its core. The Sun radiates this energy mainly as light, ultraviolet, and infrared radi ...
, the moon
The Moon is Earth's only natural satellite. It is the fifth largest satellite in the Solar System and the largest and most massive relative to its parent planet, with a diameter about one-quarter that of Earth (comparable to the width of ...
and the truth
Truth is the property of being in accord with fact or reality.Merriam-Webster's Online Dictionarytruth 2005 In everyday language, truth is typically ascribed to things that aim to represent reality or otherwise correspond to it, such as belie ...
".
See also
* Ambiguity *Banking secrecy
Banking secrecy, alternately known as financial privacy, banking discretion, or bank safety,Guex (2000), p. 240 is a conditional agreement between a bank and its clients that all foregoing activities remain secure, confidential, and private. Mos ...
* Classified information
Classified information is material that a government body deems to be sensitive information that must be protected. Access is restricted by law or regulation to particular groups of people with the necessary security clearance and need to kn ...
* Concealment device
Concealment devices or diversion safes are used to hide things for the purpose of secrecy or security. They are made from an ordinary household object such as a book, a soda can, a candle, a can, or something as small as a coin. The idea is tha ...
* Confidentiality
Confidentiality involves a set of rules or a promise usually executed through confidentiality agreements that limits the access or places restrictions on certain types of information.
Legal confidentiality
By law, lawyers are often required ...
* Conspiracy theory
* Covert operation
* Cover-up
A cover-up is an attempt, whether successful or not, to conceal evidence of wrongdoing, error, incompetence, or other embarrassing information. Research has distinguished personal cover-ups (covering up one's own misdeeds) from relational co ...
* Deception
* Don't ask, don't tell
"Don't ask, don't tell" (DADT) was the official United States policy on military service of non-heterosexual people, instituted during the Clinton administration. The policy was issued under Department of Defense Directive 1304.26 on Decemb ...
* Espionage
Espionage, spying, or intelligence gathering is the act of obtaining secret or confidential information (intelligence) from non-disclosed sources or divulging of the same without the permission of the holder of the information for a tangib ...
* Freedom of information legislation
Freedom of information laws allow access by the general public to data held by national governments and, where applicable, by state and local governments. The emergence of freedom of information legislation was a response to increasing dissatisfa ...
* Media transparency
Media transparency (or transparent media), also referred to as Media Opacity, is a concept that explores how and why information subsidies are being produced, distributed and handled by media professionals, including journalists, editors, public r ...
* Need to know
The term "need to know", when used by government and other organizations (particularly those related to the military or espionage), describes the restriction of data which is considered very sensitive. Under need-to-know restrictions, even if one ...
* Open secret
An open secret is a concept or idea that is "officially" (''de jure'') secret or restricted in knowledge, but in practice (''de facto'') is widely known; or it refers to something that is widely known to be true but which none of the people most i ...
* Secrecy (sociology)
* Secret passage
Secret passages, also commonly referred to as hidden passages or secret tunnels, are hidden routes used for stealthy travel, escape, or movement of people and goods. They are sometimes inside buildings leading to secret rooms. Others allow peop ...
* Secret sharing
Secret sharing (also called secret splitting) refers to methods for distributing a secret among a group, in such a way that no individual holds any intelligible information about the secret, but when a sufficient number of individuals combine t ...
* Self-concealment
Self-concealment is a psychological construct defined as "a predisposition to actively conceal from others personal information that one perceives as distressing or negative".. Its opposite is self-disclosure..
The concealed personal information ...
* Somebody Else's Problem
* Smuggling
* State Secrets Privilege
* ''Sub rosa
''Sub rosa'' (New Latin for "under the rose") denotes secrecy or confidentiality. The rose has an ancient history as a symbol of secrecy.
History
In Hellenistic and later Roman mythology, roses were associated with secrecy because Cupid ga ...
''
* WikiLeaks
WikiLeaks () is an international non-profit organisation that published news leaks and classified media provided by anonymous sources. Julian Assange, an Australian Internet activist, is generally described as its founder and director and ...
References
* * * * * * * * * * * * * * ::Also available as:Preview.
Further reading
*External links
An Open Source Collection of Readings on Secrecy
Secrecy News
from the Federation of American Scientists {{Authority control Classified information