KeeLoq on:
[Wikipedia]
[Google]
[Amazon]
KeeLoq is a proprietary hardware-dedicated
 KeeLoq "code hopping" encoders encrypt a 0-filled 32-bit block with KeeLoq cipher to produce a 32-bit "
KeeLoq "code hopping" encoders encrypt a 0-filled 32-bit block with KeeLoq cipher to produce a 32-bit "
 KeeLoq was first cryptanalyzed by Andrey Bogdanov using sliding techniques and efficient
KeeLoq was first cryptanalyzed by Andrey Bogdanov using sliding techniques and efficient
A complete break of the KeeLoq access control system
/ref> Their attack works on all known car and building access control systems that rely on the KeeLoq cipher. The attack by the Bochum team allows recovering the secret cryptographic
Microchip KeeLoq siteIntroduction to Ultimate KeeLoq TechnologyHCSXXX Encoder Family - Product InformationUltimate KeeLoq Technology,the Next Generation of Security - Featuring MCS3142 Dual KeeLoq Encoder
* *
C source code by Ruptor
N.T. Courtois and G.V. Bard, 'Algebraic and Slide Attacks on KeeLoq'
*
Physical Cryptanalysis of KeeLoq code-hopping applications
{{Cryptography navbox , block Block ciphers Broken block ciphers Automotive technology tradenames Radio electronics Vehicle security systems Microchip Technology hardware Garage door openers
block cipher
In cryptography, a block cipher is a deterministic algorithm operating on fixed-length groups of bits, called ''blocks''. Block ciphers are specified cryptographic primitive, elementary components in the design of many cryptographic protocols and ...
that uses a non-linear feedback shift register (NLFSR). The uni-directional command transfer protocol was designed by Frederick Bruwer of Nanoteq (Pty) Ltd., the cryptographic algorithm was created by Gideon Kuhn at the University of Pretoria, and the silicon implementation was by Willem Smit at Nanoteq Pty Ltd (South Africa
South Africa, officially the Republic of South Africa (RSA), is the southernmost country in Africa. It is bounded to the south by of coastline that stretch along the South Atlantic and Indian Oceans; to the north by the neighbouring countri ...
) in the mid-1980s. KeeLoq was sold to Microchip Technology Inc
Microchip Technology Inc. is a publicly-listed American corporation that manufactures microcontroller, mixed-signal, analog and Flash-IP integrated circuits. Its products include microcontrollers ( PIC, dsPIC, AVR and SAM), Serial EEPROM ...
in 1995 for $10 million. It is used in " code hopping" encoders and decoders such as NTQ105/106/115/125D/129D, HCS101/2XX/3XX/4XX/5XX and MCS31X2. KeeLoq is or was used in many remote keyless entry systems by such companies as Chrysler
Stellantis North America (officially FCA US and formerly Chrysler ()) is one of the " Big Three" automobile manufacturers in the United States, headquartered in Auburn Hills, Michigan. It is the American subsidiary of the multinational automoti ...
, Daewoo
Daewoo ( ; Hangul: , Hanja: , ; literally "great universe" and a portmanteau of "dae" meaning great, and the given name of founder and chairman Kim Woo-choong) also known as the Daewoo Group, was a major South Korean chaebol (type of conglomerat ...
, Fiat
Fiat Automobiles S.p.A. (, , ; originally FIAT, it, Fabbrica Italiana Automobili di Torino, lit=Italian Automobiles Factory of Turin) is an Italian automobile manufacturer, formerly part of Fiat Chrysler Automobiles, and since 2021 a subsidiary ...
, GM, Honda
is a Japanese public multinational conglomerate manufacturer of automobiles, motorcycles, and power equipment, headquartered in Minato, Tokyo, Japan.
Honda has been the world's largest motorcycle manufacturer since 1959, reaching a product ...
, Toyota
is a Japanese multinational automotive manufacturer headquartered in Toyota City, Aichi, Japan. It was founded by Kiichiro Toyoda and incorporated on . Toyota is one of the largest automobile manufacturers in the world, producing about 10 ...
, Volvo
The Volvo Group ( sv, Volvokoncernen; legally Aktiebolaget Volvo, shortened to AB Volvo, stylized as VOLVO) is a Swedish multinational manufacturing corporation headquartered in Gothenburg. While its core activity is the production, distributio ...
, Volkswagen Group
Volkswagen AG (), known internationally as the Volkswagen Group, is a German multinational automotive manufacturer headquartered in Wolfsburg, Lower Saxony, Germany. The company designs, manufactures and distributes passenger and commercial ...
, Clifford, Shurlok, and Jaguar
The jaguar (''Panthera onca'') is a large cat species and the only living member of the genus '' Panthera'' native to the Americas. With a body length of up to and a weight of up to , it is the largest cat species in the Americas and the th ...
.
Description
 KeeLoq "code hopping" encoders encrypt a 0-filled 32-bit block with KeeLoq cipher to produce a 32-bit "
KeeLoq "code hopping" encoders encrypt a 0-filled 32-bit block with KeeLoq cipher to produce a 32-bit "hopping code
A rolling code (or sometimes called a hopping code) is used in keyless entry systems to prevent replay attacks, where an eavesdropper records the transmission and replays it at a later time to cause the receiver to 'unlock'. Such systems are typic ...
". A 32-bit initialization vector
In cryptography, an initialization vector (IV) or starting variable (SV) is an input to a cryptographic primitive being used to provide the initial state. The IV is typically required to be random or pseudorandom, but sometimes an IV only needs to ...
is linearly added (XOR
Exclusive or or exclusive disjunction is a logical operation that is true if and only if its arguments differ (one is true, the other is false).
It is symbolized by the prefix operator J and by the infix operators XOR ( or ), EOR, EXOR, , ...
ed) to the 32 least significant bit
In computing, bit numbering is the convention used to identify the bit positions in a binary number.
Bit significance and indexing
In computing, the least significant bit (LSB) is the bit position in a binary integer representing the binary 1 ...
s of the key
Key or The Key may refer to:
Common meanings
* Key (cryptography), a piece of information that controls the operation of a cryptography algorithm
* Key (lock), device used to control access to places or facilities restricted by a lock
* Key (map ...
prior to encryption
In cryptography, encryption is the process of encoding information. This process converts the original representation of the information, known as plaintext, into an alternative form known as ciphertext. Ideally, only authorized parties can decip ...
and after decryption
In cryptography, encryption is the process of encoding information. This process converts the original representation of the information, known as plaintext, into an alternative form known as ciphertext. Ideally, only authorized parties can decip ...
.
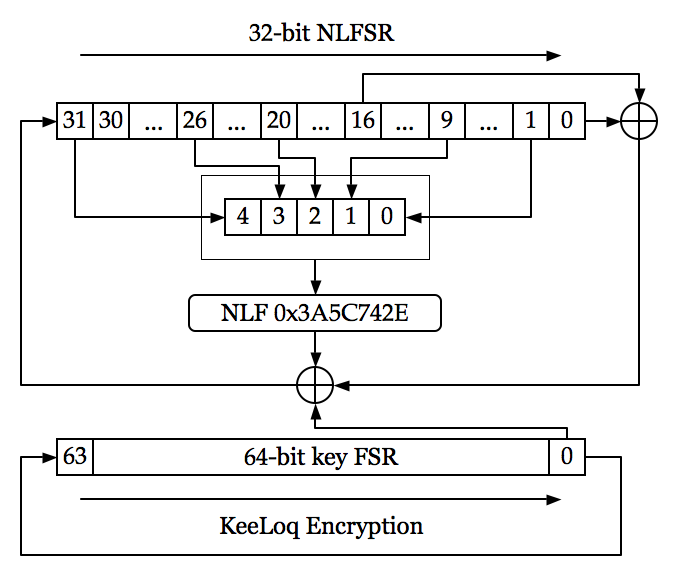
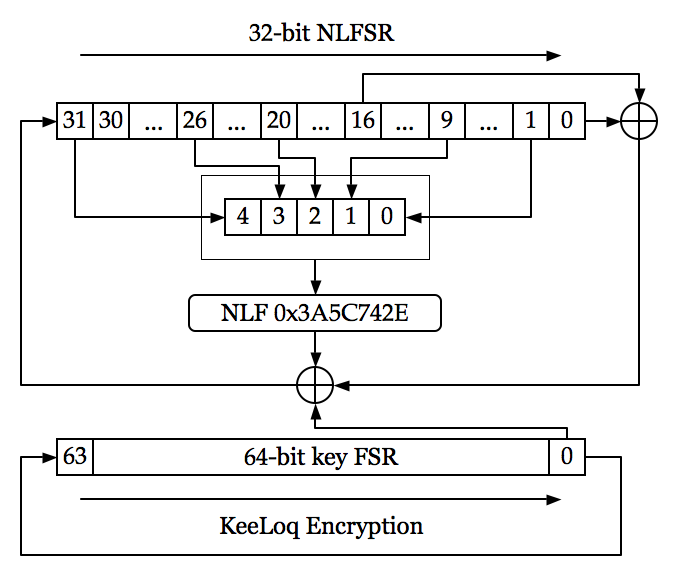
KeeLoq cipher accepts 64-bit keys and encrypts 32-bit blocks by executing its single-bit NLFSR for 528 rounds. The NLFSR feedback function is 0x3A5C742E or
:
KeeLoq uses bits 1, 9, 20, 26 and 31 of the NLFSR state as its inputs during encryption and bits 0, 8, 19, 25 and 30 during decryption. Its output is linearly combined (XORed) with two of the bits of the NLFSR state (bits 0 and 16 on encryption and bits 31 and 15 on decryption) and with a key bit (bit 0 of the key state on encryption and bit 15 of the key state on decryption) and is fed back into the NLFSR state on every round.
Versions
This article describes the Classic KeyLoq protocol, but newer versions has been developed. The Dual KeeLoq system is a timer-based algorithm enhancing the Classic KeeLoq system. The goal of this newer version is to have a timer-driven counter which continuously increments, which is the opposite of the Classic KeeLoq where the counter increments based on the events it received. This provides protection against capture and replay attack, known as RollJam for Samy Kamkar's work.Attacks
Replay attack
For simplicity, individual "code hopping" implementations typically do not usecryptographic nonce
In cryptography, a nonce is an arbitrary number that can be used just once in a cryptographic communication. It is often a random or pseudo-random number issued in an authentication protocol to ensure that old communications cannot be reused in ...
s or timestamping
A timestamp is a sequence of characters or encoded information identifying when a certain event occurred, usually giving date and time of day, sometimes accurate to a small fraction of a second. Timestamps do not have to be based on some absolut ...
. This makes the protocol inherently vulnerable to replay attack
A replay attack (also known as a repeat attack or playback attack) is a form of network attack in which valid data transmission is maliciously or fraudulently repeated or delayed. This is carried out either by the originator or by an adversary wh ...
s: For example, by jamming the channel while intercepting the code, a thief can obtain a code that may still be usable at a later stage. This sort of "code grabber," while theoretically interesting, does not appear to be widely used by car thieves.
A detailed description of an inexpensive prototype device designed and built by Samy Kamkar Samy may refer to:
*Samy (director) (active from 2006), Tamil film director
*Samy (XSS), a computer worm
*Samy (Mobile Marketing)
*
*Sami (disambiguation)
Acronyms
* SAMI, ''Synchronized Accessible Media Interchange'', a closed-captioning forma ...
to exploit this technique appeared in 2015. The device about the size of a wallet could be concealed on or near a locked vehicle to capture a single keyless entry code to be used at a later time to unlock the vehicle. The device transmits a jamming signal to block the vehicle's reception of rolling code signals from the owner's fob, while recording these signals from both of his two attempts needed to unlock the vehicle. The recorded first code is forwarded to the vehicle only when the owner makes the second attempt, while the recorded second code is retained for future use. A demonstration was announced for DEF CON
DEF CON (also written as DEFCON, Defcon or DC) is a hacker convention held annually in Las Vegas, Nevada. The first DEF CON took place in June 1993 and today many attendees at DEF CON include computer security professionals, journalists, lawyer ...
23.
Cryptanalysis
 KeeLoq was first cryptanalyzed by Andrey Bogdanov using sliding techniques and efficient
KeeLoq was first cryptanalyzed by Andrey Bogdanov using sliding techniques and efficient linear approximation
In mathematics, a linear approximation is an approximation of a general function using a linear function (more precisely, an affine function). They are widely used in the method of finite differences to produce first order methods for solving or a ...
s. Nicolas Courtois
Nicolas Tadeusz Courtois (born 14 November 1971) is a cryptographer and senior lecturer in computer science at University College London.
Courtois was one of the co-authors of both the XSL attack against block ciphers, such as the Advanced Encry ...
attacked KeeLoq using sliding and algebraic methods. The attacks by Bogdanov and Courtois do not pose any threat to the actual implementations that seem to be much more vulnerable to simple brute-force of the key space that is reduced in all the code-hopping implementations of the cipher
In cryptography, a cipher (or cypher) is an algorithm for performing encryption or decryption—a series of well-defined steps that can be followed as a procedure. An alternative, less common term is ''encipherment''. To encipher or encode i ...
known to date. Some KeeLoq "code grabbers" use FPGA
A field-programmable gate array (FPGA) is an integrated circuit designed to be configured by a customer or a designer after manufacturinghence the term '' field-programmable''. The FPGA configuration is generally specified using a hardware de ...
-based devices to break KeeLoq-based keys by brute force within about two weeks due to the reduced key length in the real world implementations.
In 2007, researchers in the COSIC
The Computer Security and Industrial Cryptography research group, commonly called COSIC, is a research group at the Department of Electrical Engineering of KU Leuven, which is headed by Bart Preneel.
Research
Research and expertise in digital s ...
group at the university at Leuven
Leuven (, ) or Louvain (, , ; german: link=no, Löwen ) is the capital and largest city of the province of Flemish Brabant in the Flemish Region of Belgium. It is located about east of Brussels. The municipality itself comprises the historic ...
, Belgium
Belgium, ; french: Belgique ; german: Belgien officially the Kingdom of Belgium, is a country in Northwestern Europe. The country is bordered by the Netherlands to the north, Germany to the east, Luxembourg to the southeast, France to th ...
, (K.U.Leuven) in cooperation with colleagues from Israel
Israel (; he, יִשְׂרָאֵל, ; ar, إِسْرَائِيل, ), officially the State of Israel ( he, מְדִינַת יִשְׂרָאֵל, label=none, translit=Medīnat Yīsrāʾēl; ), is a country in Western Asia. It is situated ...
found a new attack against the system.
Using the details of the algorithm that were leaked in 2006, the researchers started to analyze the weaknesses. After determining the part of the key common to cars of a specific model, the unique bits of the key can be cracked with only sniffed communication between the key and the car.
Microchip introduced in 1996 a version of KeeLoq ICs which use a 60-bit seed. If a 60-bit seed is being used, an attacker would require approximately 1011 days of processing on a dedicated parallel brute force attack
In cryptography, a brute-force attack consists of an attacker submitting many passwords or passphrases with the hope of eventually guessing correctly. The attacker systematically checks all possible passwords and passphrases until the correct ...
ing machine before the system is broken.
Side-channel attacks
In March 2008, researchers from the Chair for Embedded Security ofRuhr University Bochum
The Ruhr University Bochum (, ) is a public research university located in the southern hills of the central Ruhr area, Bochum, Germany. It was founded in 1962 as the first new public university in Germany after World War II. Instruction began in ...
, Germany, presented a complete break of remote keyless entry systems based on the KeeLoq RFID technology./ref> Their attack works on all known car and building access control systems that rely on the KeeLoq cipher. The attack by the Bochum team allows recovering the secret cryptographic
key
Key or The Key may refer to:
Common meanings
* Key (cryptography), a piece of information that controls the operation of a cryptography algorithm
* Key (lock), device used to control access to places or facilities restricted by a lock
* Key (map ...
s embedded in both the receiver and the remote control. It is based on measuring the electric power consumption of a device during an encryption. Applying what is called side-channel analysis methods to the power traces, the researchers can extract the manufacturer key from the receivers, which can be regarded as a master key for generating valid keys for the remote controls of one particular manufacturer. Unlike the cryptanalytic attack described above which requires about 65536 chosen plaintext-ciphertext pairs and days of calculation on a PC to recover the key, the side-channel attack can also be applied to the so-called KeeLoq Code Hopping mode of operation (a.k.a. rolling code
A rolling code (or sometimes called a hopping code) is used in keyless entry systems to prevent replay attacks, where an eavesdropper records the transmission and replays it at a later time to cause the receiver to 'unlock'. Such systems are typic ...
) that is widely used for keyless entry systems (cars, garages, buildings, etc.).
The most devastating practical consequence of the side-channel analysis is an attack in which an attacker, having previously learned the system's master key, can clone any legitimate encoder by intercepting only two messages from this encoder from a distance of up to . Another attack allows one to reset the internal counter of the receiver (garage door, car door, etc.), which makes it impossible for a legitimate user to open the door.
References
External links
Microchip KeeLoq site
* *
C source code by Ruptor
N.T. Courtois and G.V. Bard, 'Algebraic and Slide Attacks on KeeLoq'
*
Physical Cryptanalysis of KeeLoq code-hopping applications
{{Cryptography navbox , block Block ciphers Broken block ciphers Automotive technology tradenames Radio electronics Vehicle security systems Microchip Technology hardware Garage door openers