|
Password
A password, sometimes called a passcode (for example in Apple devices), is secret data, typically a string of characters, usually used to confirm a user's identity. Traditionally, passwords were expected to be memorized, but the large number of password-protected services that a typical individual accesses can make memorization of unique passwords for each service impractical. Using the terminology of the NIST Digital Identity Guidelines, the secret is held by a party called the ''claimant'' while the party verifying the identity of the claimant is called the ''verifier''. When the claimant successfully demonstrates knowledge of the password to the verifier through an established authentication protocol, the verifier is able to infer the claimant's identity. In general, a password is an arbitrary string of characters including letters, digits, or other symbols. If the permissible characters are constrained to be numeric, the corresponding secret is sometimes called a personal ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Salt (cryptography)
In cryptography, a salt is random data that is used as an additional input to a one-way function that hashes data, a password or passphrase. Salts are used to safeguard passwords in storage. Historically, only the output from an invocation of a cryptographic hash function on the password was stored on a system, but, over time, additional safeguards were developed to protect against duplicate or common passwords being identifiable (as their hashes are identical). Salting is one such protection. A new salt is randomly generated for each password. Typically, the salt and the password (or its version after key stretching) are concatenated and fed to a cryptographic hash function, and the output hash value (but not the original password) is stored with the salt in a database. Hashing allows later authentication without keeping and therefore risking exposure of the plaintext password if the authentication data store is compromised. Salts don't need to be encrypted or stored separat ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Passphrase
A passphrase is a sequence of words or other text used to control access to a computer system, program or data. It is similar to a password in usage, but a passphrase is generally longer for added security. Passphrases are often used to control both access to, and the operation of, cryptographic programs and systems, especially those that derive an encryption key from a passphrase. The origin of the term is by analogy with ''password''. The modern concept of passphrases is believed to have been invented by Sigmund N. Porter in 1982. Security Considering that the entropy of written English is less than 1.1 bits per character, passphrases can be relatively weak. NIST has estimated that the 23-character passphrase "IamtheCapitanofthePina4" contains a 45-bit strength. The equation employed here is: : 4 bits (1st character) + 14 bits (characters 2–8) + 18 bits (characters 9–20) + 3 bits (characters 21–23) + 6 bits (bonus for upper case, lower case, and alphanumeri ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Dictionary Attack
In cryptanalysis and computer security, a dictionary attack is an attack using a restricted subset of a keyspace to defeat a cipher or authentication mechanism by trying to determine its decryption key or passphrase, sometimes trying thousands or millions of likely possibilities often obtained from lists of past security breaches. Technique A dictionary attack is based on trying all the strings in a pre-arranged listing. Such attacks originally used words found in a dictionary (hence the phrase ''dictionary attack''); however, now there are much larger lists available on the open Internet containing hundreds of millions of passwords recovered from past data breaches. There is also cracking software that can use such lists and produce common variations, such as substituting numbers for similar-looking letters. A dictionary attack tries only those possibilities which are deemed most likely to succeed. Dictionary attacks often succeed because many people have a tendency to choose sh ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Hacker (computer Security)
A security hacker is someone who explores methods for breaching defenses and exploiting weaknesses in a computer system or network. Hackers may be motivated by a multitude of reasons, such as profit, protest, information gathering, challenge, recreation, or evaluation of a system weaknesses to assist in formulating defenses against potential hackers. The subculture that has evolved around hackers is often referred to as the "computer underground". Longstanding controversy surrounds the meaning of the term " hacker." In this controversy, computer programmers reclaim the term ''hacker'', arguing that it refers simply to someone with an advanced understanding of computers and computer networks and that ''cracker'' is the more appropriate term for those who break into computers, whether computer criminals ( black hats) or computer security experts ( white hats). A 2014 article noted that "the black-hat meaning still prevails among the general public". History Birth of subc ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Authentication Protocol
An authentication protocol is a type of computer communications protocol or cryptographic protocol specifically designed for transfer of authentication data between two entities. It allows the receiving entity to authenticate the connecting entity (e.g. Client connecting to a Server) as well as authenticate itself to the connecting entity (Server to a client) by declaring the type of information needed for authentication as well as syntax. It is the most important layer of protection needed for secure communication within computer networks. Purpose With the increasing amount of trustworthy information being accessible over the network, the need for keeping unauthorized persons from access to this data emerged. Stealing someone's identity is easy in the computing world - special verification methods had to be invented to find out whether the person/computer requesting data is really who he says he is. The task of the authentication protocol is to specify the exact series of steps n ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Computer User
A user is a person who utilizes a computer or network service. A user often has a user account and is identified to the system by a username (or user name). Other terms for username include login name, screenname (or screen name), account name, nickname (or nick) and handle, which is derived from the identical citizens band radio term. Some software products provide services to other systems and have no direct end users. End user End users are the ultimate human users (also referred to as operators) of a software product. The end user stands in contrast to users who support or maintain the product such as sysops, database administrators and computer technicians. The term is used to abstract and distinguish those who only use the software from the developers of the system, who enhance the software for end users. In user-centered design, it also distinguishes the software operator from the client who pays for its development and other stakeholders who may not directly us ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
User (computing)
A user is a person who utilizes a computer or network service. A user often has a user account and is identified to the system by a username (or user name). Other terms for username include login name, screenname (or screen name), account name, nickname (or nick) and handle, which is derived from the identical citizens band radio term. Some software products provide services to other systems and have no direct end users. End user End users are the ultimate human users (also referred to as operators) of a software product. The end user stands in contrast to users who support or maintain the product such as sysops, database administrators and computer technicians. The term is used to abstract and distinguish those who only use the software from the developers of the system, who enhance the software for end users. In user-centered design, it also distinguishes the software operator from the client who pays for its development and other stakeholders who may not direc ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Access Control
In the fields of physical security and information security, access control (AC) is the selective restriction of access to a place or other resource, while access management describes the process. The act of ''accessing'' may mean consuming, entering, or using. Permission to access a resource is called ''authorization''. Locks and login credentials are two analogous mechanisms of access control. Physical security Geographical access control may be enforced by personnel (e.g. border guard, bouncer, ticket checker), or with a device such as a turnstile. There may be fences to avoid circumventing this access control. An alternative of access control in the strict sense (physically controlling access itself) is a system of checking authorized presence, see e.g. Ticket controller (transportation). A variant is exit control, e.g. of a shop (checkout) or a country. The term access control refers to the practice of restricting entrance to a property, a building, or a room ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Crypt (Unix)
In Unix computing, crypt or enigma is a utility program used for encryption. Due to the ease of breaking it, it is considered to be obsolete. The program is usually used as a filter, and it has traditionally been implemented using a "rotor machine" algorithm based on the Enigma machine. It is considered to be cryptographically far too weak to provide any security against brute-force attacks by modern, commodity personal computers. Some versions of Unix shipped with an even weaker version of the ''crypt(1)'' command in order to comply with contemporaneous laws and regulations that limited the exportation of cryptographic software. Some of these were simply implementations of the Caesar cipher (effectively no more secure than ROT13, which is implemented as a Caesar cipher with a well-known key). History Cryptographer Robert Morris wrote a M-209-based , which first appeared in Version 3 Unix, to encourage codebreaking experiments; Morris managed to break by hand. Dennis Ri ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Apple Inc
Apple Inc. is an American multinational technology company headquartered in Cupertino, California, United States. Apple is the largest technology company by revenue (totaling in 2021) and, as of June 2022, is the world's biggest company by market capitalization, the fourth-largest personal computer vendor by unit sales and second-largest mobile phone manufacturer. It is one of the Big Five American information technology companies, alongside Alphabet, Amazon, Meta, and Microsoft. Apple was founded as Apple Computer Company on April 1, 1976, by Steve Wozniak, Steve Jobs and Ronald Wayne to develop and sell Wozniak's Apple I personal computer. It was incorporated by Jobs and Wozniak as Apple Computer, Inc. in 1977 and the company's next computer, the Apple II, became a best seller and one of the first mass-produced microcomputers. Apple went public in 1980 to instant financial success. The company developed computers featuring innovative graphical user inte ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
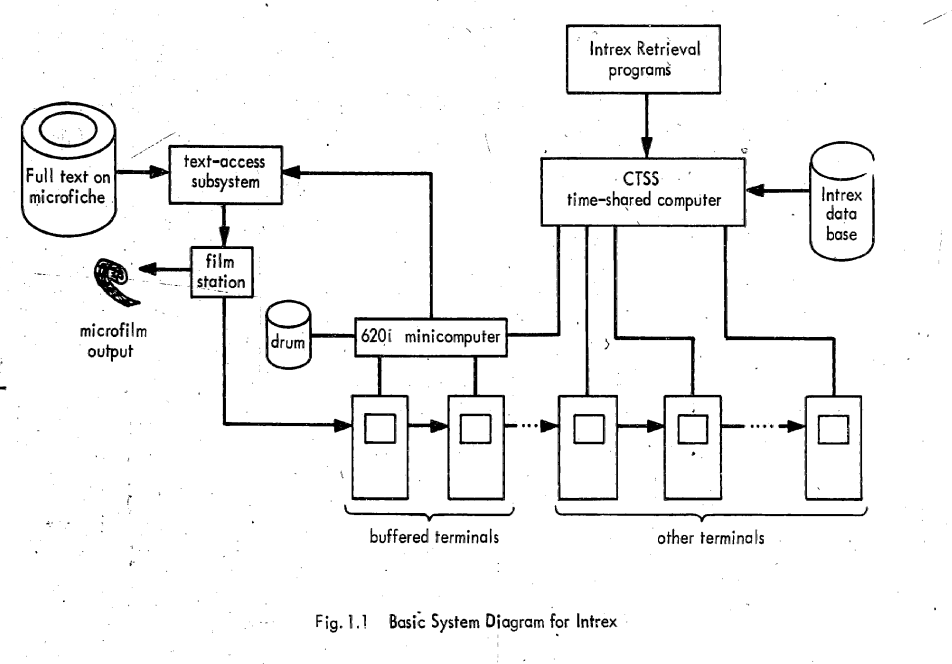
Compatible Time-Sharing System
The Compatible Time-Sharing System (CTSS) was the first general purpose time-sharing operating system. Compatible Time Sharing referred to time sharing which was compatible with batch processing; it could offer both time sharing and batch processing concurrently. CTSS was developed at the MIT Computation Center ("Comp Center"). CTSS was first demonstrated on MIT's modified IBM 709 in November 1961. The hardware was replaced with a modified IBM 7090 in 1962 and later a modified IBM 7094 called the "blue machine" to distinguish it from the Project MAC CTSS IBM 7094. Routine service to MIT Comp Center users began in the summer of 1963 and was operated there until 1968. A second deployment of CTSS on a separate IBM 7094 that was received in October 1963 (the "red machine") was used early on in Project MAC until 1969 when the red machine was moved to the Information Processing Center and operated until July 20, 1973. CTSS ran on only those two machines however there were remote CT ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Logging (computer Security)
In computer security, logging in (or logging on, signing in, or signing on) is the process by which an individual gains access to a computer system by identifying and authenticating themselves. The user credentials are typically some form of username and a matching password, and these credentials themselves are sometimes referred to as ''a'' login (or logon, sign-in, sign-on).Oxford Dictionaries definition of ''login''. detail and definition of ''login'' and ''logging in''. In practice, modern secure systems often require a second factor such as |