computer hardware
Computer hardware includes the physical parts of a computer, such as the central processing unit (CPU), random-access memory (RAM), motherboard, computer data storage, graphics card, sound card, and computer case. It includes external devices ...
and software
Software consists of computer programs that instruct the Execution (computing), execution of a computer. Software also includes design documents and specifications.
The history of software is closely tied to the development of digital comput ...
resources, and provides common services for computer program
A computer program is a sequence or set of instructions in a programming language for a computer to Execution (computing), execute. It is one component of software, which also includes software documentation, documentation and other intangibl ...
s.
Time-sharing
In computing, time-sharing is the Concurrency (computer science), concurrent sharing of a computing resource among many tasks or users by giving each Process (computing), task or User (computing), user a small slice of CPU time, processing time. ...
operating systems schedule tasks for efficient use of the system and may also include accounting software for cost allocation of processor time, mass storage
In computing, mass storage refers to the storage of large amounts of data in a persisting and machine-readable fashion. In general, the term ''mass'' in ''mass storage'' is used to mean ''large'' in relation to contemporaneous hard disk drive ...
, peripherals, and other resources.
For hardware functions such as input and output and memory allocation, the operating system acts as an intermediary between programs and the computer hardware, although the application code is usually executed directly by the hardware and frequently makes system call
In computing, a system call (syscall) is the programmatic way in which a computer program requests a service from the operating system on which it is executed. This may include hardware-related services (for example, accessing a hard disk drive ...
s to an OS function or is interrupt
In digital computers, an interrupt (sometimes referred to as a trap) is a request for the processor to ''interrupt'' currently executing code (when permitted), so that the event can be processed in a timely manner. If the request is accepted ...
ed by it. Operating systems are found on many devices that contain a computerfrom cellular phones and video game consoles to web server
A web server is computer software and underlying Computer hardware, hardware that accepts requests via Hypertext Transfer Protocol, HTTP (the network protocol created to distribute web content) or its secure variant HTTPS. A user agent, co ...
s and supercomputer
A supercomputer is a type of computer with a high level of performance as compared to a general-purpose computer. The performance of a supercomputer is commonly measured in floating-point operations per second (FLOPS) instead of million instruc ...
s.
, Android is the most popular operating system with a 46% market share, followed by Microsoft Windows
Windows is a Product lining, product line of Proprietary software, proprietary graphical user interface, graphical operating systems developed and marketed by Microsoft. It is grouped into families and subfamilies that cater to particular sec ...
at 26%, iOS and iPadOS at 18%, macOS
macOS, previously OS X and originally Mac OS X, is a Unix, Unix-based operating system developed and marketed by Apple Inc., Apple since 2001. It is the current operating system for Apple's Mac (computer), Mac computers. With ...
at 5%, and Linux
Linux ( ) is a family of open source Unix-like operating systems based on the Linux kernel, an kernel (operating system), operating system kernel first released on September 17, 1991, by Linus Torvalds. Linux is typically package manager, pac ...
at 1%. Android, iOS, and iPadOS are mobile operating systems, while Windows, macOS, and Linux are desktop operating systems. Linux distribution
A Linux distribution, often abbreviated as distro, is an operating system that includes the Linux kernel for its kernel functionality. Although the name does not imply product distribution per se, a distro—if distributed on its own—is oft ...
s are dominant in the server and supercomputing sectors. Other specialized classes of operating systems (special-purpose operating systems), such as embedded and real-time systems, exist for many applications. Security-focused operating system
This is a list of operating systems specifically focused on computer security, security. Similar concepts include security-evaluated operating systems that have achieved certification from an code audit, auditing organization, and trusted operati ...
s also exist. Some operating systems have low system requirements (e.g. light-weight Linux distribution). Others may have higher system requirements.
Some operating systems require installation or may come pre-installed with purchased computers ( OEM-installation), whereas others may run directly from media (i.e. live CD) or flash memory (i.e. a LiveUSB from a USB
Universal Serial Bus (USB) is an industry standard, developed by USB Implementers Forum (USB-IF), for digital data transmission and power delivery between many types of electronics. It specifies the architecture, in particular the physical ...
stick).
Definition and purpose
An operating system is difficult to define, but has been called "the layer of software that manages a computer's resources for its users and their applications". Operating systems include the software that is always running, called a kernel—but can include other software as well. The two other types of programs that can run on a computer are system programs—which are associated with the operating system, but may not be part of the kernel—and applications—all other software. There are three main purposes that an operating system fulfills: *Operating systems allocate resources between different applications, deciding when they will receivecentral processing unit
A central processing unit (CPU), also called a central processor, main processor, or just processor, is the primary Processor (computing), processor in a given computer. Its electronic circuitry executes Instruction (computing), instructions ...
(CPU) time or space in memory
Memory is the faculty of the mind by which data or information is encoded, stored, and retrieved when needed. It is the retention of information over time for the purpose of influencing future action. If past events could not be remembe ...
. On modern personal computer
A personal computer, commonly referred to as PC or computer, is a computer designed for individual use. It is typically used for tasks such as Word processor, word processing, web browser, internet browsing, email, multimedia playback, and PC ...
s, users often want to run several applications at once. In order to ensure that one program cannot monopolize the computer's limited hardware resources, the operating system gives each application a share of the resource, either in time (CPU) or space (memory). The operating system also must isolate applications from each other to protect them from errors and security vulnerabilities in another application's code, but enable communications between different applications.
*Operating systems provide an interface that abstracts the details of accessing hardware details (such as physical memory) to make things easier for programmers. Virtualization
In computing, virtualization (abbreviated v12n) is a series of technologies that allows dividing of physical computing resources into a series of virtual machines, operating systems, processes or containers.
Virtualization began in the 1960s wit ...
also enables the operating system to mask limited hardware resources; for example, virtual memory
In computing, virtual memory, or virtual storage, is a memory management technique that provides an "idealized abstraction of the storage resources that are actually available on a given machine" which "creates the illusion to users of a ver ...
can provide a program with the illusion of nearly unlimited memory that exceeds the computer's actual memory.
*Operating systems provide common services, such as an interface for accessing network and disk devices. This enables an application to be run on different hardware without needing to be rewritten. Which services to include in an operating system varies greatly, and this functionality makes up the great majority of code for most operating systems.
Types of operating systems
Multicomputer operating systems
With multiprocessors multiple CPUs share memory. A multicomputer or cluster computer has multiple CPUs, each of which has its own memory. Multicomputers were developed because large multiprocessors are difficult to engineer and prohibitively expensive; they are universal incloud computing
Cloud computing is "a paradigm for enabling network access to a scalable and elastic pool of shareable physical or virtual resources with self-service provisioning and administration on-demand," according to International Organization for ...
because of the size of the machine needed. The different CPUs often need to send and receive messages to each other; to ensure good performance, the operating systems for these machines need to minimize this copying of packets. Newer systems are often multiqueue—separating groups of users into separate queues—to reduce the need for packet copying and support more concurrent users. Another technique is remote direct memory access, which enables each CPU to access memory belonging to other CPUs. Multicomputer operating systems often support remote procedure call
In distributed computing, a remote procedure call (RPC) is when a computer program causes a procedure (subroutine) to execute in a different address space (commonly on another computer on a shared computer network), which is written as if it were a ...
s where a CPU can call a procedure on another CPU, or distributed shared memory, in which the operating system uses virtualization
In computing, virtualization (abbreviated v12n) is a series of technologies that allows dividing of physical computing resources into a series of virtual machines, operating systems, processes or containers.
Virtualization began in the 1960s wit ...
to generate shared memory that does not physically exist.
Distributed systems
A distributed system is a group of distinct, networked computers—each of which might have their own operating system and file system. Unlike multicomputers, they may be dispersed anywhere in the world. Middleware, an additional software layer between the operating system and applications, is often used to improve consistency. Although it functions similarly to an operating system, it is not a true operating system.Embedded
Embedded operating systems are designed to be used in embedded computer systems, whether they areinternet of things
Internet of things (IoT) describes devices with sensors, processing ability, software and other technologies that connect and exchange data with other devices and systems over the Internet or other communication networks. The IoT encompasse ...
objects or not connected to a network. Embedded systems include many household appliances. The distinguishing factor is that they do not load user-installed software. Consequently, they do not need protection between different applications, enabling simpler designs. Very small operating systems might run in less than 10 kilobytes, and the smallest are for smart cards
A smart card (SC), chip card, or integrated circuit card (ICC or IC card), is a card used to control access to a resource. It is typically a plastic credit card-sized card with an Embedded system, embedded integrated circuit (IC) chip. Many smart ...
. Examples include Embedded Linux, QNX, VxWorks
VxWorks is a real-time operating system (or RTOS) developed as proprietary software by Wind River Systems, a subsidiary of Aptiv. First released in 1987, VxWorks is designed for use in embedded systems requiring real-time, Deterministic system, ...
, and the extra-small systems RIOT
A riot or mob violence is a form of civil disorder commonly characterized by a group lashing out in a violent public disturbance against authority, property, or people.
Riots typically involve destruction of property, public or private. The p ...
and TinyOS.
Real-time
Areal-time operating system
A real-time operating system (RTOS) is an operating system (OS) for real-time computing applications that processes data and events that have critically defined time constraints. A RTOS is distinct from a time-sharing operating system, such as Unix ...
is an operating system that guarantees to process events or data by or at a specific moment in time. Hard real-time systems require exact timing and are common in manufacturing
Manufacturing is the creation or production of goods with the help of equipment, labor, machines, tools, and chemical or biological processing or formulation. It is the essence of the
secondary sector of the economy. The term may refer ...
, avionics
Avionics (a portmanteau of ''aviation'' and ''electronics'') are the Electronics, electronic systems used on aircraft. Avionic systems include communications, Air navigation, navigation, the display and management of multiple systems, and the ...
, military, and other similar uses. With soft real-time systems, the occasional missed event is acceptable; this category often includes audio or multimedia systems, as well as smartphones. In order for hard real-time systems be sufficiently exact in their timing, often they are just a library with no protection between applications, such as eCos.
Hypervisor
A hypervisor is an operating system that runs avirtual machine
In computing, a virtual machine (VM) is the virtualization or emulator, emulation of a computer system. Virtual machines are based on computer architectures and provide the functionality of a physical computer. Their implementations may involve ...
. The virtual machine is unaware that it is an application and operates as if it had its own hardware. Virtual machines can be paused, saved, and resumed, making them useful for operating systems research, development, and debugging. They also enhance portability by enabling applications to be run on a computer even if they are not compatible with the base operating system.
Library
A ''library operating system'' (libOS) is one in which the services that a typical operating system provides, such as networking, are provided in the form oflibraries
A library is a collection of Book, books, and possibly other Document, materials and Media (communication), media, that is accessible for use by its members and members of allied institutions. Libraries provide physical (hard copies) or electron ...
and composed with a single application and configuration code to construct a unikernel:
a specialized (only the absolute necessary pieces of code are extracted from libraries and bound together
), single address space, machine image that can be deployed to cloud or embedded environments.
The operating system code and application code are not executed in separated protection domains (there is only a single application running, at least conceptually, so there is no need to prevent interference between applications) and OS services are accessed via simple library calls (potentially inlining them based on compiler thresholds), without the usual overhead of context switches,
in a way similarly to embedded and real-time OSes. Note that this overhead is not negligible: to the direct cost of mode switching it's necessary to add the indirect pollution of important processor structures (like CPU cache
A CPU cache is a hardware cache used by the central processing unit (CPU) of a computer to reduce the average cost (time or energy) to access data from the main memory. A cache is a smaller, faster memory, located closer to a processor core, whi ...
s, the instruction pipeline
In computer engineering, instruction pipelining is a technique for implementing instruction-level parallelism within a single processor. Pipelining attempts to keep every part of the processor busy with some instruction by dividing incoming Mac ...
, and so on) which affects both user-mode and kernel-mode performance.
History
 The first computers in the late 1940s and 1950s were directly programmed either with plugboards or with
The first computers in the late 1940s and 1950s were directly programmed either with plugboards or with machine code
In computer programming, machine code is computer code consisting of machine language instructions, which are used to control a computer's central processing unit (CPU). For conventional binary computers, machine code is the binaryOn nonb ...
inputted on media such as punch card
A punched card (also punch card or punched-card) is a stiff paper-based medium used to store digital information via the presence or absence of holes in predefined positions. Developed over the 18th to 20th centuries, punched cards were wide ...
s, without programming language
A programming language is a system of notation for writing computer programs.
Programming languages are described in terms of their Syntax (programming languages), syntax (form) and semantics (computer science), semantics (meaning), usually def ...
s or operating systems. After the introduction of the transistor
A transistor is a semiconductor device used to Electronic amplifier, amplify or electronic switch, switch electrical signals and electric power, power. It is one of the basic building blocks of modern electronics. It is composed of semicondu ...
in the mid-1950s, mainframe
A mainframe computer, informally called a mainframe or big iron, is a computer used primarily by large organizations for critical applications like bulk data processing for tasks such as censuses, industry and consumer statistics, enterpris ...
s began to be built. These still needed professional operators who manually do what a modern operating system would do, such as scheduling programs to run, but mainframes still had rudimentary operating systems such as Fortran Monitor System (FMS) and IBSYS. In the 1960s, IBM
International Business Machines Corporation (using the trademark IBM), nicknamed Big Blue, is an American Multinational corporation, multinational technology company headquartered in Armonk, New York, and present in over 175 countries. It is ...
introduced the first series of intercompatible computers (System/360
The IBM System/360 (S/360) is a family of mainframe computer systems announced by IBM on April 7, 1964, and delivered between 1965 and 1978. System/360 was the first family of computers designed to cover both commercial and scientific applicati ...
). All of them ran the same operating system— OS/360—which consisted of millions of lines of assembly language
In computing, assembly language (alternatively assembler language or symbolic machine code), often referred to simply as assembly and commonly abbreviated as ASM or asm, is any low-level programming language with a very strong correspondence bet ...
that had thousands of bugs. The OS/360 also was the first popular operating system to support multiprogramming, such that the CPU could be put to use on one job while another was waiting on input/output
In computing, input/output (I/O, i/o, or informally io or IO) is the communication between an information processing system, such as a computer, and the outside world, such as another computer system, peripherals, or a human operator. Inputs a ...
(I/O). Holding multiple jobs in memory
Memory is the faculty of the mind by which data or information is encoded, stored, and retrieved when needed. It is the retention of information over time for the purpose of influencing future action. If past events could not be remembe ...
necessitated memory partitioning and safeguards against one job accessing the memory allocated to a different one.
Around the same time, teleprinter
A teleprinter (teletypewriter, teletype or TTY) is an electromechanical device that can be used to send and receive typed messages through various communications channels, in both point-to-point (telecommunications), point-to-point and point- ...
s began to be used as terminals so multiple users could access the computer simultaneously. The operating system MULTICS
Multics ("MULTiplexed Information and Computing Service") is an influential early time-sharing operating system based on the concept of a single-level memory.Dennis M. Ritchie, "The Evolution of the Unix Time-sharing System", Communications of t ...
was intended to allow hundreds of users to access a large computer. Despite its limited adoption, it can be considered the precursor to cloud computing
Cloud computing is "a paradigm for enabling network access to a scalable and elastic pool of shareable physical or virtual resources with self-service provisioning and administration on-demand," according to International Organization for ...
. The UNIX
Unix (, ; trademarked as UNIX) is a family of multitasking, multi-user computer operating systems that derive from the original AT&T Unix, whose development started in 1969 at the Bell Labs research center by Ken Thompson, Dennis Ritchie, a ...
operating system originated as a development of MULTICS for a single user. Because UNIX's source code
In computing, source code, or simply code or source, is a plain text computer program written in a programming language. A programmer writes the human readable source code to control the behavior of a computer.
Since a computer, at base, only ...
was available, it became the basis of other, incompatible operating systems, of which the most successful were AT&T
AT&T Inc., an abbreviation for its predecessor's former name, the American Telephone and Telegraph Company, is an American multinational telecommunications holding company headquartered at Whitacre Tower in Downtown Dallas, Texas. It is the w ...
's System V and the University of California
The University of California (UC) is a public university, public Land-grant university, land-grant research university, research university system in the U.S. state of California. Headquartered in Oakland, California, Oakland, the system is co ...
's Berkeley Software Distribution
The Berkeley Software Distribution (BSD), also known as Berkeley Unix or BSD Unix, is a discontinued Unix operating system developed and distributed by the Computer Systems Research Group (CSRG) at the University of California, Berkeley, beginn ...
(BSD). To increase compatibility, the IEEE
The Institute of Electrical and Electronics Engineers (IEEE) is an American 501(c)(3) organization, 501(c)(3) public charity professional organization for electrical engineering, electronics engineering, and other related disciplines.
The IEEE ...
released the POSIX
The Portable Operating System Interface (POSIX; ) is a family of standards specified by the IEEE Computer Society for maintaining compatibility between operating systems. POSIX defines application programming interfaces (APIs), along with comm ...
standard for operating system application programming interface
An application programming interface (API) is a connection between computers or between computer programs. It is a type of software Interface (computing), interface, offering a service to other pieces of software. A document or standard that des ...
s (APIs), which is supported by most UNIX systems. MINIX was a stripped-down version of UNIX, developed in 1987 for educational uses, that inspired the commercially available, free software
Free software, libre software, libreware sometimes known as freedom-respecting software is computer software distributed open-source license, under terms that allow users to run the software for any purpose as well as to study, change, distribut ...
Linux
Linux ( ) is a family of open source Unix-like operating systems based on the Linux kernel, an kernel (operating system), operating system kernel first released on September 17, 1991, by Linus Torvalds. Linux is typically package manager, pac ...
. Since 2008, MINIX is used in controllers of most Intel
Intel Corporation is an American multinational corporation and technology company headquartered in Santa Clara, California, and Delaware General Corporation Law, incorporated in Delaware. Intel designs, manufactures, and sells computer compo ...
microchips, while Linux is widespread in data centers and Android smartphones.
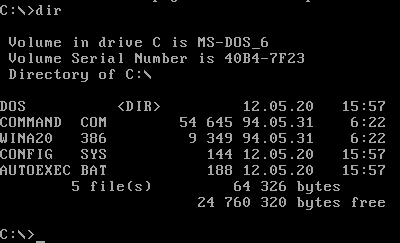
Microcomputers
 The invention of large scale integration enabled the production of
The invention of large scale integration enabled the production of personal computer
A personal computer, commonly referred to as PC or computer, is a computer designed for individual use. It is typically used for tasks such as Word processor, word processing, web browser, internet browsing, email, multimedia playback, and PC ...
s (initially called microcomputers) from around 1980. For around five years, the CP/M
CP/M, originally standing for Control Program/Monitor and later Control Program for Microcomputers, is a mass-market operating system created in 1974 for Intel 8080/Intel 8085, 85-based microcomputers by Gary Kildall of Digital Research, Dig ...
(Control Program for Microcomputers) was the most popular operating system for microcomputers. Later, IBM bought the DOS (Disk Operating System) from Microsoft
Microsoft Corporation is an American multinational corporation and technology company, technology conglomerate headquartered in Redmond, Washington. Founded in 1975, the company became influential in the History of personal computers#The ear ...
. After modifications requested by IBM, the resulting system was called MS-DOS
MS-DOS ( ; acronym for Microsoft Disk Operating System, also known as Microsoft DOS) is an operating system for x86-based personal computers mostly developed by Microsoft. Collectively, MS-DOS, its rebranding as IBM PC DOS, and a few op ...
( Disk Operating System) and was widely used on IBM microcomputers. Later versions increased their sophistication, in part by borrowing features from UNIX.
Apple
An apple is a round, edible fruit produced by an apple tree (''Malus'' spp.). Fruit trees of the orchard or domestic apple (''Malus domestica''), the most widely grown in the genus, are agriculture, cultivated worldwide. The tree originated ...
's Macintosh
Mac is a brand of personal computers designed and marketed by Apple Inc., Apple since 1984. The name is short for Macintosh (its official name until 1999), a reference to the McIntosh (apple), McIntosh apple. The current product lineup inclu ...
was the first popular computer to use a graphical user interface
A graphical user interface, or GUI, is a form of user interface that allows user (computing), users to human–computer interaction, interact with electronic devices through Graphics, graphical icon (computing), icons and visual indicators such ...
(GUI). The GUI proved much more user friendly
''User Friendly'' was a webcomic written by J. D. Frazer, also known by his pen name Illiad. Starting in 1997, the strip was one of the earliest webcomics to make its creator a living. The comic is set in a fictional internet service provider a ...
than the text-only command-line interface
A command-line interface (CLI) is a means of interacting with software via command (computing), commands each formatted as a line of text. Command-line interfaces emerged in the mid-1960s, on computer terminals, as an interactive and more user ...
earlier operating systems had used. Following the success of Macintosh, MS-DOS was updated with a GUI overlay called Windows
Windows is a Product lining, product line of Proprietary software, proprietary graphical user interface, graphical operating systems developed and marketed by Microsoft. It is grouped into families and subfamilies that cater to particular sec ...
. Windows later was rewritten as a stand-alone operating system, borrowing so many features from another ( VAX VMS) that a large legal settlement was paid. In the twenty-first century, Windows continues to be popular on personal computers but has less market share
Market share is the percentage of the total revenue or sales in a Market (economics), market that a company's business makes up. For example, if there are 50,000 units sold per year in a given industry, a company whose sales were 5,000 of those ...
of servers. UNIX operating systems, especially Linux, are the most popular on enterprise systems and servers but are also used on mobile device
A mobile device or handheld device is a computer small enough to hold and operate in hand. Mobile devices are typically battery-powered and possess a flat-panel display and one or more built-in input devices, such as a touchscreen or keypad. ...
s and many other computer systems.
On mobile devices, Symbian OS was dominant at first, being usurped by BlackBerry OS (introduced 2002) and iOS for iPhones (from 2007). Later on, the open-source Android operating system (introduced 2008), with a Linux kernel and a C library (Bionic (software), Bionic) partially based on BSD code, became most popular.
Components
The components of an operating system are designed to ensure that various parts of a computer function cohesively. With the de facto obsoletion of Disk Operating System, DOS, all usersoftware
Software consists of computer programs that instruct the Execution (computing), execution of a computer. Software also includes design documents and specifications.
The history of software is closely tied to the development of digital comput ...
must interact with the operating system to access hardware.
Kernel
input/output
In computing, input/output (I/O, i/o, or informally io or IO) is the communication between an information processing system, such as a computer, and the outside world, such as another computer system, peripherals, or a human operator. Inputs a ...
devices.
Program execution
The operating system provides an interface between an application program and the computer hardware, so that an application program can interact with the hardware only by obeying rules and procedures programmed into the operating system. The operating system is also a set of services which simplify development and execution of application programs. Executing an application program typically involves the creation of a Process (computing), process by the operating system kernel (operating system), kernel, which assigns memory space and other resources, establishes a priority for the process in multi-tasking systems, loads program binary code into memory, and initiates execution of the application program, which then interacts with the user and with hardware devices. However, in some systems an application can request that the operating system execute another application within the same process, either as a subroutine or in a separate thread, e.g., the LINK and ATTACH facilities of OS/360 and successors.Interrupts
Aninterrupt
In digital computers, an interrupt (sometimes referred to as a trap) is a request for the processor to ''interrupt'' currently executing code (when permitted), so that the event can be processed in a timely manner. If the request is accepted ...
(also known as an Abort (computing), abort, Exception handling, exception, ''fault'', Signal (IPC), signal, or ''trap'') provides an efficient way for most operating systems to react to the environment. Interrupts cause the central processing unit
A central processing unit (CPU), also called a central processor, main processor, or just processor, is the primary Processor (computing), processor in a given computer. Its electronic circuitry executes Instruction (computing), instructions ...
(CPU) to have a control flow change away from the currently running program to an interrupt handler, also known as an interrupt service routine (ISR). An interrupt service routine may cause the central processing unit
A central processing unit (CPU), also called a central processor, main processor, or just processor, is the primary Processor (computing), processor in a given computer. Its electronic circuitry executes Instruction (computing), instructions ...
(CPU) to have a context switch. The details of how a computer processes an interrupt vary from architecture to architecture, and the details of how interrupt service routines behave vary from operating system to operating system. However, several interrupt functions are common. The architecture and operating system must:
# transfer control to an interrupt service routine.
# save the state of the currently running process.
# restore the state after the interrupt is serviced.
=Software interrupt
= A software interrupt is a message to a Process (computing), process that an event has occurred. This contrasts with a ''hardware interrupt'' — which is a message to thecentral processing unit
A central processing unit (CPU), also called a central processor, main processor, or just processor, is the primary Processor (computing), processor in a given computer. Its electronic circuitry executes Instruction (computing), instructions ...
(CPU) that an event has occurred. Software interrupts are similar to hardware interrupts — there is a change away from the currently running process. Similarly, both hardware and software interrupts execute an Interrupt handler, interrupt service routine.
Software interrupts may be normally occurring events. It is expected that a Preemption (computing)#Time slice, time slice will occur, so the kernel will have to perform a context switch. A computer program
A computer program is a sequence or set of instructions in a programming language for a computer to Execution (computing), execute. It is one component of software, which also includes software documentation, documentation and other intangibl ...
may set a timer to go off after a few seconds in case too much data causes an algorithm to take too long.
Software interrupts may be error conditions, such as a malformed machine code, machine instruction. However, the most common error conditions are division by zero and segmentation fault, accessing an invalid memory address.
User (computing), Users can send messages to the kernel to modify the behavior of a currently running process. For example, in the Command-line interface, command-line environment, pressing the ''interrupt character'' (usually Control-C) might terminate the currently running process.
To generate ''software interrupts'' for x86 CPUs, the INT (x86 instruction), INT assembly language
In computing, assembly language (alternatively assembler language or symbolic machine code), often referred to simply as assembly and commonly abbreviated as ASM or asm, is any low-level programming language with a very strong correspondence bet ...
instruction is available. The syntax is INT X, where X is the offset number (in hexadecimal format) to the interrupt vector table.
=Signal
= To generate ''software interrupts'' in Unix-like operating systems, thekill(pid,signum) system call
In computing, a system call (syscall) is the programmatic way in which a computer program requests a service from the operating system on which it is executed. This may include hardware-related services (for example, accessing a hard disk drive ...
will send a Signal (IPC), signal to another process. pid is the process identifier of the receiving process. signum is the signal number (in mnemonic format) to be sent. (The abrasive name of kill was chosen because early implementations only terminated the process.)
In Unix-like operating systems, ''signals'' inform processes of the occurrence of asynchronous events. To communicate asynchronously, interrupts are required. One reason a process needs to asynchronously communicate to another process solves a variation of the classic Readers–writers problem, reader/writer problem. The writer receives a pipe from the Shell (computing), shell for its output to be sent to the reader's input stream. The Command-line interface, command-line syntax is alpha , bravo. alpha will write to the pipe when its computation is ready and then sleep in the wait queue. bravo will then be moved to the Multilevel feedback queue, ready queue and soon will read from its input stream. The kernel will generate ''software interrupts'' to coordinate the piping.
''Signals'' may be classified into 7 categories. The categories are:
# when a process finishes normally.
# when a process has an error exception.
# when a process runs out of a system resource.
# when a process executes an illegal instruction.
# when a process sets an alarm event.
# when a process is aborted from the keyboard.
# when a process has a tracing alert for debugging.
=Hardware interrupt
= Input/output (I/O) Peripheral, devices are slower than the CPU. Therefore, it would slow down the computer if the CPU had to Busy waiting, wait for each I/O to finish. Instead, a computer may implement interrupts for I/O completion, avoiding the need for Polling (computer science), polling or busy waiting. Some computers require an interrupt for each character or word, costing a significant amount of CPU time. Direct memory access (DMA) is an architecture feature to allow devices to bypass the CPU and access random-access memory, main memory directly. (Separate from the architecture, a device may perform direct memory access to and from main memory either directly or via a bus.)Input/output
=Interrupt-driven I/O
= When a user (computing), computer user types a key on the keyboard, typically the character appears immediately on the screen. Likewise, when a user moves a computer mouse, mouse, the Cursor (user interface), cursor immediately moves across the screen. Each keystroke and mouse movement generates an ''interrupt'' called ''Interrupt-driven I/O''. An interrupt-driven I/O occurs when a process causes an interrupt for every character or word transmitted.=Direct memory access
= Devices such as hard disk drives, solid-state drives, and magnetic tape drives can transfer data at a rate high enough that interrupting the CPU for every byte or word transferred, and having the CPU transfer the byte or word between the device and memory, would require too much CPU time. Data is, instead, transferred between the device and memory independently of the CPU by hardware such as a channel I/O, channel or a direct memory access controller; an interrupt is delivered only when all the data is transferred. If acomputer program
A computer program is a sequence or set of instructions in a programming language for a computer to Execution (computing), execute. It is one component of software, which also includes software documentation, documentation and other intangibl ...
executes a system call
In computing, a system call (syscall) is the programmatic way in which a computer program requests a service from the operating system on which it is executed. This may include hardware-related services (for example, accessing a hard disk drive ...
to perform a block I/O ''write'' operation, then the system call might execute the following instructions:
* Set the contents of the CPU's Processor register, registers (including the program counter) into the process control block.
* Create an entry in the device-status table. The operating system maintains this table to keep track of which processes are waiting for which devices. One field in the table is the memory address of the process control block.
* Place all the characters to be sent to the device into a random-access memory, memory buffer.
* Set the memory address of the memory buffer to a predetermined device register.
* Set the buffer size (an integer) to another predetermined register.
* Execute the machine code, machine instruction to begin the writing.
* Perform a context switch to the next process in the multilevel feedback queue, ready queue.
While the writing takes place, the operating system will context switch to other processes as normal. When the device finishes writing, the device will ''interrupt'' the currently running process by ''asserting'' an Interrupt request (PC architecture), interrupt request. The device will also place an integer onto the data bus. Upon accepting the interrupt request, the operating system will:
* Push the contents of the program counter (a register) followed by the status register onto the call stack.
* Push the contents of the other registers onto the call stack. (Alternatively, the contents of the registers may be placed in a system table.)
* Read the integer from the data bus. The integer is an offset to the interrupt vector table. The vector table's instructions will then:
:* Access the device-status table.
:* Extract the process control block.
:* Perform a context switch back to the writing process.
When the writing process has its Preemption (computing)#time slice, time slice expired, the operating system will:
* Pop from the call stack the registers other than the status register and program counter.
* Pop from the call stack the status register.
* Pop from the call stack the address of the next instruction, and set it back into the program counter.
With the program counter now reset, the interrupted process will resume its time slice.
Memory management
Among other things, a multiprogramming operating system kernel (operating system), kernel must be responsible for managing all system memory which is currently in use by the programs. This ensures that a program does not interfere with memory already in use by another program. Since programs time share, each program must have independent access to memory. Cooperative memory management, used by many early operating systems, assumes that all programs make voluntary use of the kernel (operating system), kernel's memory manager, and do not exceed their allocated memory. This system of memory management is almost never seen anymore, since programs often contain bugs which can cause them to exceed their allocated memory. If a program fails, it may cause memory used by one or more other programs to be affected or overwritten. Malicious programs or viruses may purposefully alter another program's memory, or may affect the operation of the operating system itself. With cooperative memory management, it takes only one misbehaved program to Crash (computing), crash the system. Memory protection enables the kernel (operating system), kernel to limit a process' access to the computer's memory. Various methods of memory protection exist, including memory segmentation and paging. All methods require some level of hardware support (such as the 80286 MMU), which does not exist in all computers. In both segmentation and paging, certain protected mode registers specify to the CPU what memory address it should allow a running program to access. Attempts to access other addresses trigger an interrupt, which causes the CPU to re-enter supervisor mode, placing the kernel (operating system), kernel in charge. This is called a segmentation violation or Seg-V for short, and since it is both difficult to assign a meaningful result to such an operation, and because it is usually a sign of a misbehaving program, the kernel (operating system), kernel generally resorts to terminating the offending program, and reports the error. Windows versions 3.1 through ME had some level of memory protection, but programs could easily circumvent the need to use it. A general protection fault would be produced, indicating a segmentation violation had occurred; however, the system would often crash anyway.Virtual memory
Concurrency
Concurrency (computer science), Concurrency refers to the operating system's ability to carry out multiple tasks simultaneously. Virtually all modern operating systems support concurrency. Thread (computing), Threads enable splitting a process' work into multiple parts that can run simultaneously. The number of threads is not limited by the number of processors available. If there are more threads than processors, the operating system kernel (operating system), kernel schedules, suspends, and resumes threads, controlling when each thread runs and how much CPU time it receives. During a context switch a running thread is suspended, its state is saved into the thread control block and stack, and the state of the new thread is loaded in. Historically, on many systems a thread could run until it relinquished control (cooperative multitasking). Because this model can allow a single thread to monopolize the processor, most operating systems now caninterrupt
In digital computers, an interrupt (sometimes referred to as a trap) is a request for the processor to ''interrupt'' currently executing code (when permitted), so that the event can be processed in a timely manner. If the request is accepted ...
a thread (preemptive multitasking).
Threads have their own thread ID, program counter (PC), a Processor register, register set, and a Stack-based memory allocation, stack, but share code, heap memory, heap data, and other resources with other threads of the same process. Thus, there is less overhead to create a thread than a new process. On single-CPU systems, concurrency is switching between processes. Many computers have multiple CPUs. Parallel computing, Parallelism with multiple threads running on different CPUs can speed up a program, depending on how much of it can be executed concurrently.
File system
 Permanent storage devices used in twenty-first century computers, unlike volatile memory, volatile dynamic random-access memory (DRAM), are still accessible after a Crash (computing), crash or power failure. Permanent (non-volatile memory, non-volatile) storage is much cheaper per byte, but takes several orders of magnitude longer to access, read, and write. The two main technologies are a hard drive consisting of magnetic disks, and flash memory (a solid-state drive that stores data in electrical circuits). The latter is more expensive but faster and more durable.
File systems are an abstraction used by the operating system to simplify access to permanent storage. They provide human-readable filenames and other metadata, increase performance via Amortization (computer science), amortization of accesses, prevent multiple threads from accessing the same section of memory, and include checksums to identify Data corruption, corruption. File systems are composed of files (named collections of data, of an arbitrary size) and Directory (computing), directories (also called folders) that list human-readable filenames and other directories. An absolute file path begins at the root directory and lists subdirectories divided by punctuation, while a relative path defines the location of a file from a directory.
System calls (which are sometimes Wrapper function, wrapped by libraries) enable applications to create, delete, open, and close files, as well as link, read, and write to them. All these operations are carried out by the operating system on behalf of the application. The operating system's efforts to reduce latency include storing recently requested blocks of memory in a Cache (computing), cache and prefetching data that the application has not asked for, but might need next. Device drivers are software specific to each
Permanent storage devices used in twenty-first century computers, unlike volatile memory, volatile dynamic random-access memory (DRAM), are still accessible after a Crash (computing), crash or power failure. Permanent (non-volatile memory, non-volatile) storage is much cheaper per byte, but takes several orders of magnitude longer to access, read, and write. The two main technologies are a hard drive consisting of magnetic disks, and flash memory (a solid-state drive that stores data in electrical circuits). The latter is more expensive but faster and more durable.
File systems are an abstraction used by the operating system to simplify access to permanent storage. They provide human-readable filenames and other metadata, increase performance via Amortization (computer science), amortization of accesses, prevent multiple threads from accessing the same section of memory, and include checksums to identify Data corruption, corruption. File systems are composed of files (named collections of data, of an arbitrary size) and Directory (computing), directories (also called folders) that list human-readable filenames and other directories. An absolute file path begins at the root directory and lists subdirectories divided by punctuation, while a relative path defines the location of a file from a directory.
System calls (which are sometimes Wrapper function, wrapped by libraries) enable applications to create, delete, open, and close files, as well as link, read, and write to them. All these operations are carried out by the operating system on behalf of the application. The operating system's efforts to reduce latency include storing recently requested blocks of memory in a Cache (computing), cache and prefetching data that the application has not asked for, but might need next. Device drivers are software specific to each input/output
In computing, input/output (I/O, i/o, or informally io or IO) is the communication between an information processing system, such as a computer, and the outside world, such as another computer system, peripherals, or a human operator. Inputs a ...
(I/O) device that enables the operating system to work without modification over different hardware.
Another component of file systems is a Associative array, dictionary that maps a file's name and metadata to the data block where its contents are stored. Most file systems use directories to convert file names to file numbers. To find the block number, the operating system uses an Database index, index (often implemented as a tree (data structure), tree). Separately, there is a free space map (data structure), map to track free blocks, commonly implemented as a bitmap. Although any free block can be used to store a new file, many operating systems try to group together files in the same directory to maximize performance, or periodically reorganize files to reduce file system fragmentation, fragmentation.
Maintaining data reliability in the face of a computer crash or hardware failure is another concern. File writing protocols are designed with atomic operations so as not to leave permanent storage in a partially written, inconsistent state in the event of a crash at any point during writing. Data corruption is addressed by redundant storage (for example, RAID—redundant array of inexpensive disks) and checksums to detect when data has been corrupted. With multiple layers of checksums and backups of a file, a system can recover from multiple hardware failures. Background processes are often used to detect and recover from data corruption.
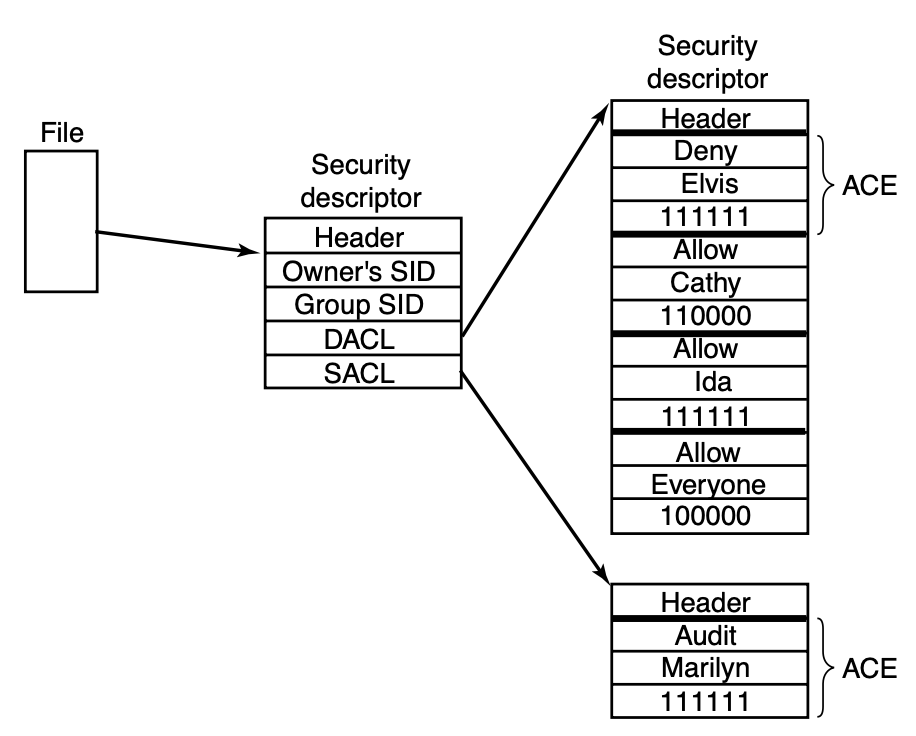
Security
Security means protecting users from other users of the same computer, as well as from those who seeking remote access to it over a network. Operating systems security rests on achieving the CIA triad: confidentiality (unauthorized users cannot access data), integrity (unauthorized users cannot modify data), and availability (ensuring that the system remains available to authorized users, even in the event of a denial of service attack). As with other computer systems, isolating security domains—in the case of operating systems, the kernel, processes, andvirtual machine
In computing, a virtual machine (VM) is the virtualization or emulator, emulation of a computer system. Virtual machines are based on computer architectures and provide the functionality of a physical computer. Their implementations may involve ...
s—is key to achieving security. Other ways to increase security include simplicity to minimize the attack surface, locking access to resources by default, checking all requests for authorization, principle of least authority (granting the minimum privilege essential for performing a task), privilege separation, and reducing shared data.
Some operating system designs are more secure than others. Those with no isolation between the kernel and applications are least secure, while those with a monolithic kernel like most general-purpose operating systems are still vulnerable if any part of the kernel is compromised. A more secure design features microkernels that separate the kernel's privileges into many separate security domains and reduce the consequences of a single kernel breach. Unikernels are another approach that improves security by minimizing the kernel and separating out other operating systems functionality by application.
Most operating systems are written in C (programming language), C or C++, which create potential vulnerabilities for exploitation. Despite attempts to protect against them, vulnerabilities are caused by buffer overflow attacks, which are enabled by the lack of bounds checking. Hardware vulnerabilities, some of them Speculative execution CPU vulnerabilities, caused by CPU optimizations, can also be used to compromise the operating system. There are known instances of operating system programmers deliberately implanting vulnerabilities, such as Backdoor (computing), back doors.
Operating systems security is hampered by their increasing complexity and the resulting inevitability of bugs. Because formal verification of operating systems may not be feasible, developers use operating system Hardening (computing), hardening to reduce vulnerabilities, e.g. address space layout randomization, control-flow integrity, Access-control list, access restrictions, and other techniques. There are no restrictions on who can contribute code to open source operating systems; such operating systems have transparent change histories and distributed governance structures. Open source developers strive to work collaboratively to find and eliminate security vulnerabilities, using code review and type checking to expunge malicious code. Andrew S. Tanenbaum advises releasing the source code
In computing, source code, or simply code or source, is a plain text computer program written in a programming language. A programmer writes the human readable source code to control the behavior of a computer.
Since a computer, at base, only ...
of all operating systems, arguing that it prevents developers from placing trust in secrecy and thus relying on the unreliable practice of security by obscurity.
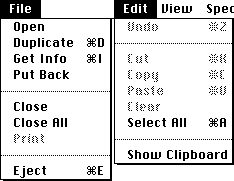
User interface
A user interface (UI) is essential to support human interaction with a computer. The two most common user interface types for any computer are *command-line interface
A command-line interface (CLI) is a means of interacting with software via command (computing), commands each formatted as a line of text. Command-line interfaces emerged in the mid-1960s, on computer terminals, as an interactive and more user ...
, where computer commands are typed, line-by-line,
*graphical user interface
A graphical user interface, or GUI, is a form of user interface that allows user (computing), users to human–computer interaction, interact with electronic devices through Graphics, graphical icon (computing), icons and visual indicators such ...
(GUI) using a visual environment, most commonly a combination of the window, icon, menu, and pointer elements, also known as WIMP (computing), WIMP.
For personal computers, including smartphones and tablet computers, and for workstations, user input is typically from a combination of Keyboard technology, keyboard, mouse (computing), mouse, and trackpad or touchscreen, all of which are connected to the operating system with specialized software. Personal computer users who are not software developers or coders often prefer GUIs for both input and output; GUIs are supported by most personal computers. The software to support GUIs is more complex than a command line for input and plain text output. Plain text output is often preferred by programmers, and is easy to support.
Operating system development as a hobby
A hobby operating system may be classified as one whose code has not been directly derived from an existing operating system, and has few users and active developers. In some cases, hobby development is in support of a "Homebrew Computer Club, homebrew" computing device, for example, a simple single-board computer powered by a MOS Technology 6502, 6502 microprocessor. Or, development may be for an architecture already in widespread use. Operating system development may come from entirely new concepts, or may commence by modeling an existing operating system. In either case, the hobbyist is her/his own developer, or may interact with a small and sometimes unstructured group of individuals who have like interests. Examples of hobby operating systems include Syllable Desktop, Syllable and TempleOS.Diversity of operating systems and portability
If an application is written for use on a specific operating system, and is ported to another OS, the functionality required by that application may be implemented differently by that OS (the names of functions, meaning of arguments, etc.) requiring the application to be adapted, changed, or otherwise software maintenance, maintained. This cost in supporting operating systems diversity can be avoided by instead writing applications against software platforms such as Java (software platform), Java or Qt (software), Qt. These abstractions have already borne the cost of adaptation to specific operating systems and their system library, system libraries. Another approach is for operating system vendors to adopt standards. For example,POSIX
The Portable Operating System Interface (POSIX; ) is a family of standards specified by the IEEE Computer Society for maintaining compatibility between operating systems. POSIX defines application programming interfaces (APIs), along with comm ...
and operating system abstraction layer, OS abstraction layers provide commonalities that reduce porting costs.
Popular operating systems
, Android (based on the Linux kernel) is the most popular operating system with a 46% market share, followed byMicrosoft Windows
Windows is a Product lining, product line of Proprietary software, proprietary graphical user interface, graphical operating systems developed and marketed by Microsoft. It is grouped into families and subfamilies that cater to particular sec ...
at 26%, iOS and iPadOS at 18%, macOS
macOS, previously OS X and originally Mac OS X, is a Unix, Unix-based operating system developed and marketed by Apple Inc., Apple since 2001. It is the current operating system for Apple's Mac (computer), Mac computers. With ...
at 5%, and Linux
Linux ( ) is a family of open source Unix-like operating systems based on the Linux kernel, an kernel (operating system), operating system kernel first released on September 17, 1991, by Linus Torvalds. Linux is typically package manager, pac ...
at 1%. Android, iOS, and iPadOS are mobile operating systems, while Windows, macOS, and Linux are desktop operating systems.
Linux

Linux
Linux ( ) is a family of open source Unix-like operating systems based on the Linux kernel, an kernel (operating system), operating system kernel first released on September 17, 1991, by Linus Torvalds. Linux is typically package manager, pac ...
is a free software
Free software, libre software, libreware sometimes known as freedom-respecting software is computer software distributed open-source license, under terms that allow users to run the software for any purpose as well as to study, change, distribut ...
distributed under the GNU General Public License (GPL), which means that all of its derivatives are legally required to release their source code
In computing, source code, or simply code or source, is a plain text computer program written in a programming language. A programmer writes the human readable source code to control the behavior of a computer.
Since a computer, at base, only ...
. Linux was designed by programmers for their own use, thus emphasizing simplicity and consistency, with a small number of basic elements that can be combined in nearly unlimited ways, and avoiding redundancy.
Its design is similar to other UNIX systems not using a microkernel. It is written in C (programming language), C and uses UNIX System V syntax, but also supports BSD syntax. Linux supports standard UNIX networking features, as well as the full suite of UNIX tools, while multiuser, supporting multiple users and employing preemptive multitasking. Initially of a minimalist design, Linux is a flexible system that can work in under 16 megabytes, MB of RAM, but still is used on large multiprocessor systems. Similar to other UNIX systems, Linux Linux distribution, distributions are composed of a Linux kernel, kernel, system library, system libraries, and system utilities. Linux has a graphical user interface
A graphical user interface, or GUI, is a form of user interface that allows user (computing), users to human–computer interaction, interact with electronic devices through Graphics, graphical icon (computing), icons and visual indicators such ...
(GUI) with a desktop, folder and file icons, as well as the option to access the operating system via a command line.
Android is a partially open-source operating system closely based on Linux and has become the most widely used operating system by users, due to its popularity on smartphones and, to a lesser extent, embedded systems needing a GUI, such as "smart watches, Android Automotive, automotive dashboards, airplane seatbacks, medical devices, and home appliances". Unlike Linux, much of Android is written in Java (programming language), Java and uses object-oriented design.
Microsoft Windows
 Windows is a proprietary operating system that is widely used on desktop computers, laptops, tablets, phones, workstations, enterprise servers, and Xbox consoles. The operating system was designed for "security, reliability, compatibility, high performance, extensibility, portability, and international support"—later on, Energy efficiency in operating systems, energy efficiency and support for dynamic devices also became priorities.
Windows Executive works via Object Manager (Windows), kernel-mode objects for important data structures like processes, threads, and sections (memory objects, for example files). The operating system supports demand paging of
Windows is a proprietary operating system that is widely used on desktop computers, laptops, tablets, phones, workstations, enterprise servers, and Xbox consoles. The operating system was designed for "security, reliability, compatibility, high performance, extensibility, portability, and international support"—later on, Energy efficiency in operating systems, energy efficiency and support for dynamic devices also became priorities.
Windows Executive works via Object Manager (Windows), kernel-mode objects for important data structures like processes, threads, and sections (memory objects, for example files). The operating system supports demand paging of virtual memory
In computing, virtual memory, or virtual storage, is a memory management technique that provides an "idealized abstraction of the storage resources that are actually available on a given machine" which "creates the illusion to users of a ver ...
, which speeds up I/O for many applications. I/O device drivers use the Windows Driver Model. The NTFS file system has a master table and each file is represented as a Record (computer science), record with metadata. The scheduling includes preemptive multitasking. Windows has many security features; especially important are the use of access-control lists and safety integrity level, integrity levels. Every process has an authentication token and each object is given a security descriptor. Later releases have added even more security features.
See also
* Comparison of operating systems * DBOS * Interruptible operating system * List of operating systems * List of pioneers in computer science * Glossary of operating systems terms * Microcontroller * Network operating system * Object-oriented operating system * Lisp machine * Operating System Projects * System Commander * System image * Timeline of operating systemsNotes
References
Further reading
* * * * * * * O'Brien, J. A., & Marakas, G. M.(2011). ''Management Information Systems''. 10e. McGraw-Hill Irwin. * * * *External links
Multics History
and the history of operating systems {{Authority control Operating systems,