|
Non-interactive Key Exchange
In cryptography, forward secrecy (FS), also known as perfect forward secrecy (PFS), is a feature of specific key-agreement protocols that gives assurances that session keys will not be compromised even if long-term secrets used in the session key exchange are compromised, limiting damage. For TLS, the long-term secret is typically the private key of the server. Forward secrecy protects past sessions against future compromises of keys or passwords. By generating a unique session key for every session a user initiates, the compromise of a single session key will not affect any data other than that exchanged in the specific session protected by that particular key. This by itself is not sufficient for forward secrecy which additionally requires that a long-term secret compromise does not affect the security of past session keys. Forward secrecy protects data on the transport layer of a network that uses common transport layer security protocols, including OpenSSL, when its long-ter ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
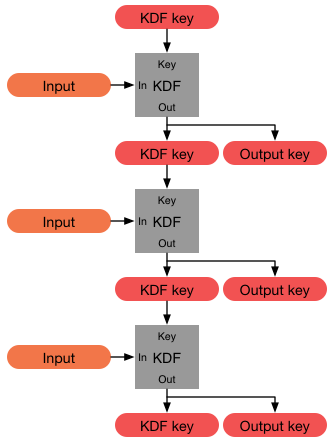
KDF Chain
KDF may refer to: Entertainment * K22JA-D, a TV station in Texas, US * Kentucky Derby Festival, Louisville, US * Klingon Defence Force, in ''Star Trek'' Organisations * Kerala Dalit Federation, an Indian political party * Kenya Defence Forces * KDF Energy, Romania * Kraft durch Freude (Strength Through Joy), a Nazi state leisure organization * Hitler's Chancellery, Kanzlei des Führers (Chancellory of the Führer), a Nazi office Sport * Kunst des fechtens, the German school of fencing Technologies * KDF9, a British computer * Key derivation function, in cryptography * Kinetic degradation fluxion media, for water filtration See also * KdF (other) {{Disambiguation, callsign ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
IEEE P1363
IEEE P1363 is an Institute of Electrical and Electronics Engineers (IEEE) standardization project for public-key cryptography. It includes specifications for: * Traditional public-key cryptography (IEEE Std 1363-2000 and 1363a-2004) * Lattice-based public-key cryptography (IEEE Std 1363.1-2008) * Password-based public-key cryptography (IEEE Std 1363.2-2008) * Identity-based public-key cryptography using pairings (IEEE Std 1363.3-2013) The chair of the working group as of October 2008 is William Whyte of NTRU Cryptosystems, Inc., who has served since August 2001. Former chairs were Ari Singer, also of NTRU (1999–2001), and Burt Kaliski of RSA Security (1994–1999). The IEEE Standard Association withdrew all of the 1363 standards except 1363.3-2013 on 7 November 2019. Traditional public-key cryptography (IEEE Std 1363-2000 and 1363a-2004) This specification includes key agreement, signature, and encryption schemes using several mathematical approaches: integer factorizati ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Replay Attacks
A replay attack (also known as a repeat attack or playback attack) is a form of network attack in which valid data transmission is maliciously or fraudulently repeated or delayed. This is carried out either by the originator or by an adversary who intercepts the data and re-transmits it, possibly as part of a spoofing attack by IP packet substitution. This is one of the lower-tier versions of a man-in-the-middle attack. Replay attacks are usually passive in nature. Another way of describing such an attack is: "an attack on a security protocol using a replay of messages from a different context into the intended (or original and expected) context, thereby fooling the honest participant(s) into thinking they have successfully completed the protocol run." Example Suppose Alice wants to prove her identity to Bob. Bob requests her password as proof of identity, which Alice dutifully provides (possibly after some transformation like hashing, or even salting, the password); meanwhile ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Store-and-forward
Store and forward is a telecommunications technique in which information is sent to an intermediate station where it is kept and sent at a later time to the final destination or to another intermediate station. The intermediate station, or node in a networking context, verifies the integrity of the message before forwarding it. In general, this technique is used in networks with intermittent connectivity, especially in the wilderness or environments requiring high mobility. It may also be preferable in situations when there are long delays in transmission and error rates are variable and high, or if a direct, end-to-end connection is not available. Modern store and forward networking * Store and forward originates with delay-tolerant networks. No real-time services are available for these kinds of networks. * Logistical Networking is a scalable form of store and forward networking that exposes network-embedded buffers on intermediate nodes and allows flexible creation of s ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Denial Of Service
In computing, a denial-of-service attack (DoS attack) is a cyberattack in which the perpetrator seeks to make a machine or network resource unavailable to its intended users by temporarily or indefinitely disrupting services of a host connected to a network. Denial of service is typically accomplished by flooding the targeted machine or resource with superfluous requests in an attempt to overload systems and prevent some or all legitimate requests from being fulfilled. The range of attacks varies widely, spanning from inundating a server with millions of requests to slow its performance, overwhelming a server with a substantial amount of invalid data, to submitting requests with an illegitimate IP address. In a distributed denial-of-service attack (DDoS attack), the incoming traffic flooding the victim originates from many different sources. More sophisticated strategies are required to mitigate this type of attack; simply attempting to block a single source is insuffic ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Harvest Now, Decrypt Later
Harvest now, decrypt later is a surveillance strategy that relies on the acquisition and long-term storage of currently unreadable encrypted data awaiting possible breakthroughs in decryption technology that would render it readable in the future – a hypothetical date referred to as Y2Q (a reference to Y2K) or Q-Day. The most common concern is the prospect of developments in quantum computing which would allow current strong encryption algorithms to be broken at some time in the future, making it possible to decrypt any stored material that had been encrypted using those algorithms. However, the improvement in decryption technology need not be due to a quantum-cryptographic advance; any other form of attack capable of enabling decryption would be sufficient. The existence of this strategy has led to concerns about the need to urgently deploy post-quantum cryptography, even though no practical quantum attacks yet exist, as some data stored now may still remain sensitive even de ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Discrete Logarithm Problem
In mathematics, for given real numbers a and b, the logarithm \log_b(a) is a number x such that b^x=a. Analogously, in any group G, powers b^k can be defined for all integers k, and the discrete logarithm \log_b(a) is an integer k such that b^k=a. In arithmetic modulo an integer m, the more commonly used term is index: One can write k=\mathbb_b a \pmod (read "the index of a to the base b modulo m") for b^k \equiv a \pmod if b is a primitive root of m and \gcd(a,m)=1. Discrete logarithms are quickly computable in a few special cases. However, no efficient method is known for computing them in general. In cryptography, the computational complexity of the discrete logarithm problem, along with its application, was first proposed in the Diffie–Hellman problem. Several important algorithms in public-key cryptography, such as ElGamal, base their security on the hardness assumption that the discrete logarithm problem (DLP) over carefully chosen groups has no efficient solution. ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Quantum Computers
A quantum computer is a computer that exploits quantum mechanical phenomena. On small scales, physical matter exhibits properties of both particles and waves, and quantum computing takes advantage of this behavior using specialized hardware. Classical physics cannot explain the operation of these quantum devices, and a scalable quantum computer could perform some calculations exponentially faster than any modern "classical" computer. Theoretically a large-scale quantum computer could break some widely used encryption schemes and aid physicists in performing physical simulations; however, the current state of the art is largely experimental and impractical, with several obstacles to useful applications. The basic unit of information in quantum computing, the qubit (or "quantum bit"), serves the same function as the bit in classical computing. However, unlike a classical bit, which can be in one of two states (a binary), a qubit can exist in a superposition of its two "basis" ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Public-key Cryptography
Public-key cryptography, or asymmetric cryptography, is the field of cryptographic systems that use pairs of related keys. Each key pair consists of a public key and a corresponding private key. Key pairs are generated with cryptographic algorithms based on mathematical problems termed one-way functions. Security of public-key cryptography depends on keeping the private key secret; the public key can be openly distributed without compromising security. There are many kinds of public-key cryptosystems, with different security goals, including digital signature, Diffie–Hellman key exchange, Key encapsulation mechanism, public-key key encapsulation, and public-key encryption. Public key algorithms are fundamental security primitives in modern cryptosystems, including applications and protocols that offer assurance of the confidentiality and authenticity of electronic communications and data storage. They underpin numerous Internet standards, such as Transport Layer Security, T ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Ciphers
In cryptography, a cipher (or cypher) is an algorithm for performing encryption or decryption—a series of well-defined steps that can be followed as a procedure. An alternative, less common term is ''encipherment''. To encipher or encode is to convert information into cipher or code. In common parlance, "cipher" is synonymous with "code (cryptography), code", as they are both a set of steps that encrypt a message; however, the concepts are distinct in cryptography, especially classical cryptography. Codes generally substitute different length strings of characters in the output, while ciphers generally substitute the same number of characters as are input. A code maps one meaning with another. Words and phrases can be coded as letters or numbers. Codes typically have direct meaning from input to key. Codes primarily function to save time. Ciphers are algorithmic. The given input must follow the cipher's process to be solved. Ciphers are commonly used to encrypt written info ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Cryptanalysis
Cryptanalysis (from the Greek ''kryptós'', "hidden", and ''analýein'', "to analyze") refers to the process of analyzing information systems in order to understand hidden aspects of the systems. Cryptanalysis is used to breach cryptographic security systems and gain access to the contents of encrypted messages, even if the cryptographic key is unknown. In addition to mathematical analysis of cryptographic algorithms, cryptanalysis includes the study of side-channel attacks that do not target weaknesses in the cryptographic algorithms themselves, but instead exploit weaknesses in their implementation. Even though the goal has been the same, the methods and techniques of cryptanalysis have changed drastically through the history of cryptography, adapting to increasing cryptographic complexity, ranging from the pen-and-paper methods of the past, through machines like the British Bombes and Colossus computers at Bletchley Park in World War II, to the mathematically advanced ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Symmetric Cipher
Symmetric-key algorithms are algorithms for cryptography that use the same cryptographic keys for both the encryption of plaintext and the decryption of ciphertext. The keys may be identical, or there may be a simple transformation to go between the two keys. The keys, in practice, represent a shared secret between two or more parties that can be used to maintain a private information link. The requirement that both parties have access to the secret key is one of the main drawbacks of symmetric-key encryption, in comparison to public-key encryption (also known as asymmetric-key encryption). However, symmetric-key encryption algorithms are usually better for bulk encryption. With exception of the one-time pad they have a smaller key size, which means less storage space and faster transmission. Due to this, asymmetric-key encryption is often used to exchange the secret key for symmetric-key encryption. Types Symmetric-key encryption can use either stream ciphers or block ciphers ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |