|
Cyberweapon
Cyberweapons are commonly defined as malware agents employed for military, paramilitary, or intelligence objectives as part of a cyberattack. This includes computer viruses, trojans, spyware, and worms that can introduce malicious code into existing software, causing a computer to perform actions or processes unintended by its operator. Characteristics A cyberweapon is usually sponsored or employed by a state or non-state actor, meets an objective that would otherwise require espionage or the use of force, and is employed against specific targets. A cyberweapon performs an action that would normally require a soldier or spy, and which would be considered either illegal or an act of war if performed directly by a human agent of the sponsor during peacetime. Legal issues include violating the privacy of the target and the sovereignty of its host nation. Example of such actions are surveillance, data theft and electronic or physical destruction. While a cyberweapon almost ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
WannaCry Ransomware Attack
The WannaCry ransomware attack was a worldwide cyberattack in May 2017 by the WannaCry ransomware cryptoworm, which targeted computers running the Microsoft Windows operating system by encrypting data and demanding ransom payments in the form of Bitcoin cryptocurrency. It was propagated using EternalBlue, an exploit developed by the United States National Security Agency (NSA) for Microsoft Windows systems. EternalBlue was stolen and leaked by a group called The Shadow Brokers (TSB) a month prior to the attack. While Microsoft had released patches previously to close the exploit, much of WannaCry's spread was from organizations that had not applied these patches, or were using older Windows systems that were past their end of life. These patches were imperative to cyber security, but many organizations did not apply them, citing a need for 24/7 operation, the risk of formerly working applications breaking because of the changes, lack of personnel or time to install them, or ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Duqu
Duqu is a collection of computer malware discovered on 1 September 2011, thought by Kaspersky Labs to be related to the Stuxnet worm and to have been created by Unit 8200. The Laboratory of Cryptography and System Security ( CrySyS Lab) of the Budapest University of Technology and Economics in Hungary discovered the threat, analysed the malware, and wrote a 60-page report naming the threat Duqu. Duqu got its name from the prefix "~DQ" it gives to the names of files it creates. Nomenclature The term Duqu is used in a variety of ways: * Duqu malware is a variety of software components that together provide services to the attackers. Currently this includes information stealing capabilities and in the background, kernel drivers and injection tools. Part of this malware is written in unknown high-level programming language, dubbed "Duqu framework". It is not C++, Python, Ada, Lua and many other checked languages. However, it is suggested that Duqu may have been written in C with ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Zero-day (computing)
A zero-day (also known as a 0-day) is a vulnerability or security hole in a computer system unknown to its developers or anyone capable of mitigating it. Until the vulnerability is remedied, threat actors can exploit it in a zero-day exploit, or zero-day attack. The term "zero-day" originally referred to the number of days since a new piece of software was released to the public, so "zero-day software" was obtained by hacking into a developer's computer before release. Eventually the term was applied to the vulnerabilities that allowed this hacking, and to the number of days that the vendor has had to fix them. Vendors who discover the vulnerability may create patches or advise workarounds to mitigate it – though users need to deploy that mitigation to eliminate the vulnerability in their systems. Zero-day attacks are severe threats. Definition Despite developers' goal of delivering a product that works entirely as intended, virtually all software and hardware contain bugs. ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Malware
Malware (a portmanteau of ''malicious software'')Tahir, R. (2018)A study on malware and malware detection techniques . ''International Journal of Education and Management Engineering'', ''8''(2), 20. is any software intentionally designed to cause disruption to a computer, server (computing), server, Client (computing), client, or computer network, leak private information, gain unauthorized access to information or systems, deprive access to information, or which unknowingly interferes with the user's computer security and privacy. Researchers tend to classify malware into one or more sub-types (i.e. computer viruses, Computer worm, worms, Trojan horse (computing), Trojan horses, logic bombs, ransomware, spyware, adware, rogue software, Wiper (malware), wipers and keyloggers). Malware poses serious problems to individuals and businesses on the Internet. According to NortonLifeLock, Symantec's 2018 Internet Security Threat Report (ISTR), malware variants number has increased to 66 ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Surveillance
Surveillance is the monitoring of behavior, many activities, or information for the purpose of information gathering, influencing, managing, or directing. This can include observation from a distance by means of electronic equipment, such as closed-circuit television (CCTV), or interception of electronically transmitted information like Internet traffic. Increasingly, Government, governments may also obtain Customer data, consumer data through the purchase of online information, effectively expanding surveillance capabilities through commercially available digital records. It can also include simple technical methods, such as Human intelligence (intelligence gathering), human intelligence gathering and postal interception. Surveillance is used by citizens, for instance for protecting their neighborhoods. It is widely used by governments for intelligence gathering, including espionage, prevention of crime, the protection of a process, person, group or object, or the investigat ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Stuxnet
Stuxnet is a Malware, malicious computer worm first uncovered on June 17, 2010, and thought to have been in development since at least 2005. Stuxnet targets supervisory control and data acquisition (SCADA) systems and is believed to be responsible for causing substantial damage to the nuclear program of Iran, Iran nuclear program. Although neither the United States nor Israel has openly admitted responsibility, multiple independent news organizations claim Stuxnet to be a cyberweapon built jointly by the two countries in a collaborative effort known as Operation Olympic Games. The program, started during the Presidency of George W. Bush, Bush administration, was rapidly expanded within the first months of Barack Obama's presidency. Stuxnet specifically targets programmable logic controllers (PLCs), which allow the automation of electromechanical processes such as those used to control machinery and industrial processes including gas centrifuges for separating nuclear material. Exp ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Mirai (malware)
Mirai (from the Japanese word for "future", 未来) is malware that turns networked devices running Linux into remotely controlled bots that can be used as part of a botnet in large-scale network attacks. It primarily targets online consumer devices such as IP cameras and home routers. The Mirai botnet was first found in August 2016 by MalwareMustDie, a white hat malware research group, and has been used in some of the largest and most disruptive distributed denial of service (DDoS) attacks, including an attack on 20 September 2016 on computer security journalist Brian Krebs' website, an attack on French web host OVH, and the October 2016 DDoS attacks on Dyn. According to a chat log between Anna-senpai (the malware's original author) and Robert Coelho, Mirai was named after the 2011 TV anime series '' Mirai Nikki''. The software was initially used by the creators to DDoS ''Minecraft'' servers and companies offering DDoS protection to ''Minecraft'' servers, with the author ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Great Cannon
The Great Cannon of China is an Internet attack tool that is used by the government of the People's Republic of China to launch distributed denial-of-service attacks on websites by performing a man-in-the-middle attack on large amounts of web traffic and injecting code which causes the end-user's web browsers to flood traffic to targeted websites. According to the researchers at the Citizen Lab, the International Computer Science Institute, and Princeton University's Center for Information Technology Policy, who coined the term, the Great Cannon hijacks foreign web traffic intended for Chinese websites and re-purposes them to flood targeted web servers with enormous amounts of traffic in an attempt to disrupt their operations. While it is co-located with the Great Firewall, the Great Cannon is "a separate offensive system, with different capabilities and design." Besides launching denial-of-service attacks, the tool is also capable of monitoring web traffic and distributing mal ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Flame (malware)
Flame, also known as Flamer, sKyWIper, and Skywiper, is modular computer malware discovered in 2012 that attacks computers running the Microsoft Windows operating system. The program is used for targeted cyber spying, cyber espionage in Middle Eastern countries. Its discovery was announced on 28 May 2012 by the MAHER Center of the Iranian National Computer Emergency Response Team (CERT), Kaspersky Lab and CrySyS Lab of the Budapest University of Technology and Economics. The last of these stated in its report that Flame "is certainly the most sophisticated malware we encountered during our practice; arguably, it is the most complex malware ever found." Flame can spread to other systems over a local area network (LAN). It can record audio, screenshots, Keystroke logging, keyboard activity and Packet capture, network traffic. The program also records Skype conversations and can turn infected computers into Bluetooth beacons which attempt to download contact information from near ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Petya And NotPetya
Petya is a family of encrypting malware that was first discovered in 2016. The malware targets Microsoft Windows–based systems, infecting the master boot record to execute a payload that encrypts a hard drive's file system table and prevents Windows from booting. It subsequently demands that the users make a payment in Bitcoin in order to regain access to the system. Variants of Petya were first seen in March 2016, which propagated via infected e-mail attachments. In June 2017, a new variant of Petya was used for a global cyberattack, primarily targeting Ukraine. The new variant propagates via the EternalBlue exploit, which is generally believed to have been developed by the U.S. National Security Agency (NSA), and was used earlier in the year by the WannaCry ransomware. Kaspersky Lab referred to this new version as ''NotPetya'' to distinguish it from the 2016 variants, due to these differences in operation. It looked like ransomware, but without functioning recovery featu ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Fraud
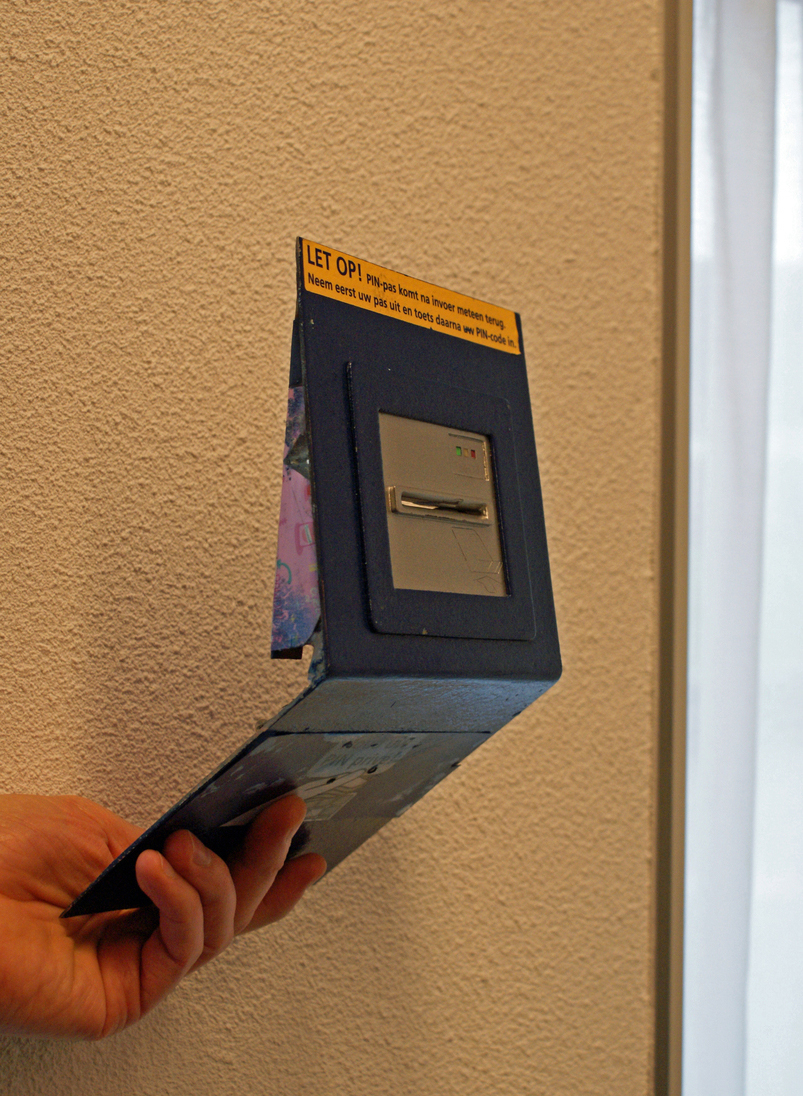
In law, fraud is intent (law), intentional deception to deprive a victim of a legal right or to gain from a victim unlawfully or unfairly. Fraud can violate Civil law (common law), civil law (e.g., a fraud victim may sue the fraud perpetrator to avoid the fraud or recover monetary compensation) or criminal law (e.g., a fraud perpetrator may be prosecuted and imprisoned by governmental authorities), or it may cause no loss of money, property, or legal right but still be an element of another civil or criminal wrong. The purpose of fraud may be monetary gain or other benefits, such as obtaining a passport, travel document, or driver's licence. In cases of mortgage fraud, the perpetrator may attempt to qualify for a mortgage by way of false statements. Terminology Fraud can be defined as either a civil wrong or a criminal act. For civil fraud, a government agency or person or entity harmed by fraud may bring litigation to stop the fraud, seek monetary damages, or both. For cr ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Selectivity
Selectivity may refer to: Psychology and behaviour * Choice, making a selection among options * Discrimination, the ability to recognize differences * Socioemotional selectivity theory, in social psychology Engineering * Selectivity (radio), a measure of the performance of a radio receiver to respond only to the radio signal it is tuned * Selectivity (circuit breakers), the coordination of overcurrent protection devices in an electrical installation Biology * Binding selectivity, in pharmacology * Functional selectivity, in pharmacology * Natural selection Natural selection is the differential survival and reproduction of individuals due to differences in phenotype. It is a key mechanism of evolution, the change in the Heredity, heritable traits characteristic of a population over generation ..., in biology Chemistry * Reactivity–selectivity principle, in general chemistry * Chemoselectivity, a term used in organic chemistry to describe reactivity of one funct ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |