|
Ciphertext-only Attack
In cryptography, a ciphertext-only attack (COA) or known ciphertext attack is an attack model for cryptanalysis where the attacker is assumed to have access only to a set of ciphertexts. While the attacker has no channel providing access to the plaintext prior to encryption, in all practical ciphertext-only attacks, the attacker still has some knowledge of the plaintext. For instance, the attacker might know the language in which the plaintext is written or the expected statistical distribution of characters in the plaintext. Standard protocol data and messages are commonly part of the plaintext in many deployed systems, and can usually be guessed or known efficiently as part of a ciphertext-only attack on these systems. Attack The attack is completely successful if the corresponding plaintexts can be deduced, or even better, the key. The ability to obtain any information at all about the underlying plaintext beyond what was pre-known to the attacker is still considered a succ ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |
Cryptography
Cryptography, or cryptology (from "hidden, secret"; and ''graphein'', "to write", or ''-logy, -logia'', "study", respectively), is the practice and study of techniques for secure communication in the presence of Adversary (cryptography), adversarial behavior. More generally, cryptography is about constructing and analyzing Communication protocol, protocols that prevent third parties or the public from reading private messages. Modern cryptography exists at the intersection of the disciplines of mathematics, computer science, information security, electrical engineering, digital signal processing, physics, and others. Core concepts related to information security (confidentiality, data confidentiality, data integrity, authentication, and non-repudiation) are also central to cryptography. Practical applications of cryptography include electronic commerce, Smart card#EMV, chip-based payment cards, digital currencies, password, computer passwords, and military communications. ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |
Mimic Function
A mimic function changes a file A so it assumes the statistical properties of another file B. That is, if p(t,A) is the probability of some substring t occurring in A, then a mimic function f, recodes A so that p(t,f(A)) approximates p(t,B) for all strings t of length less than some n. It is commonly considered to be one of the basic techniques for hiding information, often called steganography. The simplest mimic functions use simple statistical models to pick the symbols in the output. If the statistical model says that item x occurs with probability p(x,A) and item y occurs with probability p(y,A), then a random number is used to choose between outputting x or y with probability p(x,A) or p(y,A) respectively. Even more sophisticated models use reversible Turing machine A Turing machine is a mathematical model of computation describing an abstract machine that manipulates symbols on a strip of tape according to a table of rules. Despite the model's simplicity, it is capa ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |
Advanced Encryption Standard
The Advanced Encryption Standard (AES), also known by its original name Rijndael (), is a specification for the encryption of electronic data established by the U.S. National Institute of Standards and Technology (NIST) in 2001. AES is a variant of the Rijndael block cipher developed by two Belgium, Belgian cryptographers, Joan Daemen and Vincent Rijmen, who submitted a proposal to NIST during the Advanced Encryption Standard process, AES selection process. Rijndael is a family of ciphers with different key size, key and Block size (cryptography), block sizes. For AES, NIST selected three members of the Rijndael family, each with a block size of 128 bits, but three different key lengths: 128, 192 and 256 bits. AES has been adopted by the Federal government of the United States, U.S. government. It supersedes the Data Encryption Standard (DES), which was published in 1977. The algorithm described by AES is a symmetric-key algorithm, meaning the same key is used for both encrypting ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |
Data Encryption Standard
The Data Encryption Standard (DES ) is a symmetric-key algorithm for the encryption of digital data. Although its short key length of 56 bits makes it too insecure for modern applications, it has been highly influential in the advancement of cryptography. Developed in the early 1970s at IBM and based on an earlier design by Horst Feistel, the algorithm was submitted to the National Bureau of Standards (NBS) following the agency's invitation to propose a candidate for the protection of sensitive, unclassified electronic government data. In 1976, after consultation with the National Security Agency (NSA), the NBS selected a slightly modified version (strengthened against differential cryptanalysis, but weakened against brute-force attacks), which was published as an official Federal Information Processing Standard (FIPS) for the United States in 1977. The publication of an NSA-approved encryption standard led to its quick international adoption and widespread academic scrutiny. C ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |
Unicity Distance
In cryptography, unicity distance is the length of an original ciphertext needed to break the cipher by reducing the number of possible spurious keys to zero in a brute force attack. That is, after trying every possible key, there should be just one decipherment that makes sense, i.e. expected amount of ciphertext needed to determine the key completely, assuming the underlying message has redundancy. Claude Shannon defined the unicity distance in his 1949 paper " Communication Theory of Secrecy Systems". Consider an attack on the ciphertext string "WNAIW" encrypted using a Vigenère cipher with a five letter key. Conceivably, this string could be deciphered into any other string—RIVER and WATER are both possibilities for certain keys. This is a general rule of cryptanalysis: with no additional information it is impossible to decode this message. Of course, even in this case, only a certain number of five letter keys will result in English words. Trying all possible keys w ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |
Brute Force Attack
In cryptography, a brute-force attack or exhaustive key search is a cryptanalytic attack that consists of an attacker submitting many possible Key (cryptography), keys or passwords with the hope of eventually guessing correctly. This strategy can theoretically be used to break any form of encryption that is not information-theoretically secure. However, in a properly designed cryptosystem the chance of successfully guessing the key is negligible. When Password cracking, cracking passwords, this method is very fast when used to check all short passwords, but for longer passwords other methods such as the dictionary attack are used because a brute-force search takes too long. Longer passwords, passphrases and keys have more possible values, making them exponentially more difficult to crack than shorter ones due to diversity of characters. Brute-force attacks can be made less effective by Obfuscation (software), obfuscating the data to be encoded making it more difficult for an att ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |
Akelarre (cipher)
Akelarre is a block cipher proposed in 1996, combining the basic design of IDEA (cipher), IDEA with ideas from RC5. It was shown to be susceptible to a ciphertext-only attack in 1997. Akelarre is a 128-bit block cipher with a variable key-length which must be some multiple of 64 bits. The number of rounds is variable, but four are suggested. The round function of Akelarre is similar to IDEA in structure. After the successful cryptanalysis of Akelarre, its designers responded with an updated variant called Ake98. This cipher differs from the original Akelarre in the new ''AR-box'' (addition–rotation box), the swapping of words at the end of a round, and the addition of subkeys at the beginning of each round. In 2004, Jorge Nakahara, Jr. and Daniel Santana de Freitas found large classes of weak keys for Ake98. These weak keys allow a cryptanalysis faster than exhaustive search using only 71 known plaintexts, for up to 11.5 rounds of Ake98. References * * * * * {{Cry ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |
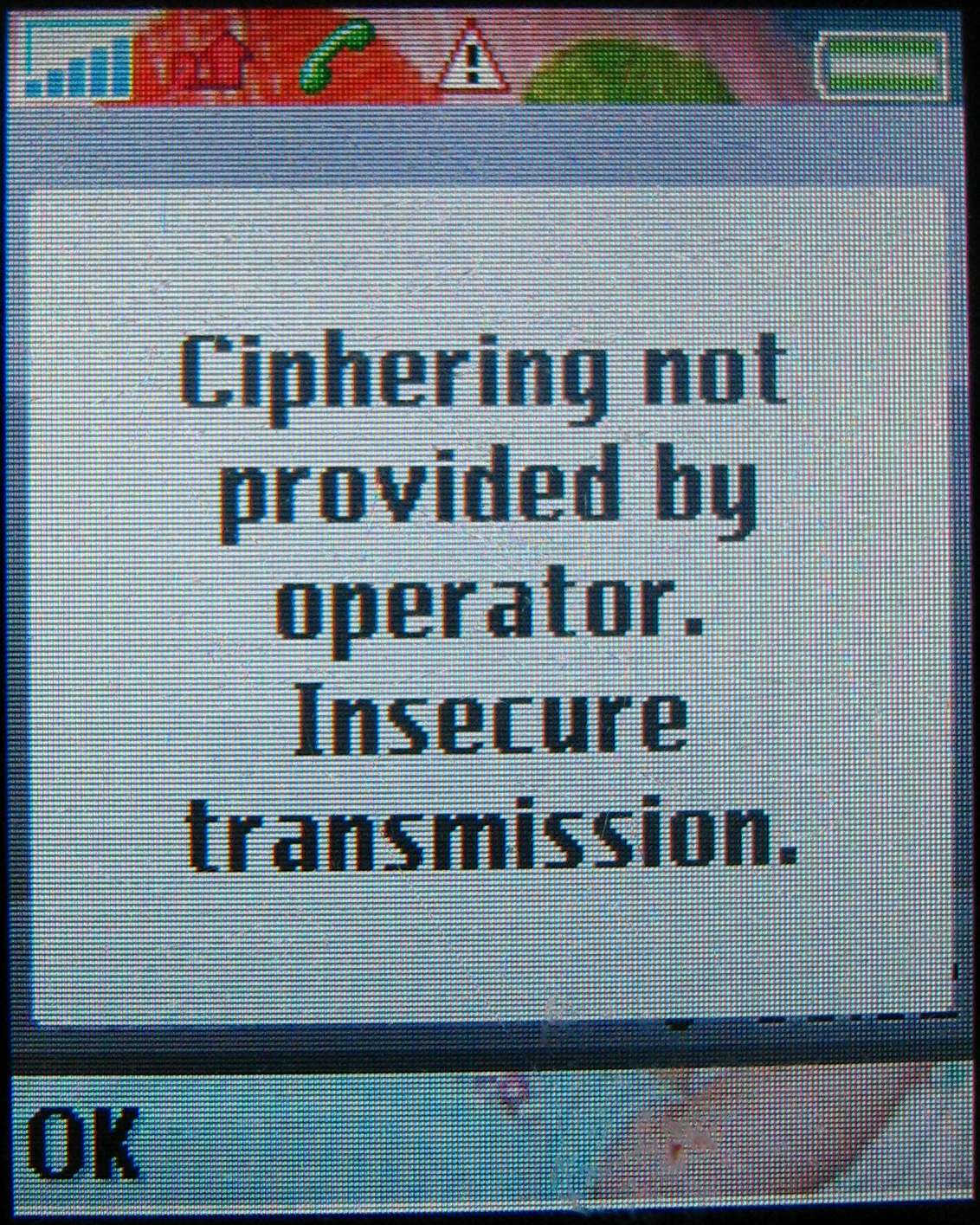
A5/2
A5/2 is a stream cipher used to provide voice privacy in the GSM cellular telephone protocol. It was designed in 1992-1993 (finished March 1993) as a replacement for the relatively stronger (but still weak) A5/1, to allow the GSM standard to be exported to countries "with restrictions on the import of products with cryptographic security features". The cipher is based on a combination of four linear-feedback shift registers with irregular clocking and a non-linear combiner. In 1999, Ian Goldberg and David A. Wagner cryptanalyzed A5/2 in the same month it was reverse engineered, and showed that it was extremely weak – so much so that low end equipment can probably break it in real time. In 2003, Elad Barkan, Eli Biham and Nathan Keller presented a ciphertext-only attack based on the error correcting codes used in GSM communication. They also demonstrated a vulnerability in the GSM protocols that allows a man-in-the-middle attack to work whenever the mobile phone supports A5/2 ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |
A5/1
A5/1 is a stream cipher used to provide over-the-air communication privacy in the Global System for Mobile Communications, GSM Cell phone, cellular telephone standard. It is one of several implementations of the A5 security protocol. It was initially kept secret, but became public knowledge through leaks and reverse engineering. A number of serious weaknesses in the cipher have been identified. History and usage A5/1 is used in Europe and the United States. A5/2 was a deliberate weakening of the algorithm for certain export regions. A5/1 was developed in 1987, when GSM was not yet considered for use outside Europe, and A5/2 was developed in 1989. Though both were initially kept secret, the general design was leaked in 1994 and the algorithms were entirely reverse engineered in 1999 by Marc Briceno from a GSM telephone. In 2000, around 130 million GSM customers relied on A5/1 to protect the confidentiality of their voice communications. Security researcher Ross J. Anderson, Ross And ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |
Wi-Fi
Wi-Fi () is a family of wireless network protocols based on the IEEE 802.11 family of standards, which are commonly used for Wireless LAN, local area networking of devices and Internet access, allowing nearby digital devices to exchange data by radio waves. These are the most widely used computer networks, used globally in small office/home office, home and small office networks to link devices and to provide Internet access with wireless routers and wireless access points in public places such as coffee shops, restaurants, hotels, libraries, and airports. ''Wi-Fi'' is a trademark of the Wi-Fi Alliance, which restricts the use of the term "''Wi-Fi Certified''" to products that successfully complete Interoperability Solutions for European Public Administrations, interoperability certification testing. Non-compliant hardware is simply referred to as WLAN, and it may or may not work with "''Wi-Fi Certified''" devices. the Wi-Fi Alliance consisted of more than 800 companies from ar ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |
Wired Equivalent Privacy
Wired Equivalent Privacy (WEP) is an obsolete, and insecure security algorithm for 802.11 wireless networks. It was introduced as part of the original IEEE 802.11 standard ratified in 1997. The intention was to provide a level of security and privacy comparable to that of a traditional wired network. WEP, recognizable by its key of 10 or 26 hexadecimal digits (40 or 104 bits), was at one time widely used, and was often the first security choice presented to users by router configuration tools. After a severe design flaw in the algorithm was disclosed in 2001, WEP was no longer considered a secure method of wireless connection; however, in the vast majority of cases, Wi-Fi hardware devices relying on WEP security could not be upgraded to secure operation. Some of WEP's design flaws were addressed in WEP2, but it also proved insecure, and never saw wide adoption or standardization. In 2003, the Wi-Fi Alliance announced that WEP and WEP2 had been superseded by Wi-Fi Protected Acc ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |
Stream Cipher Attack
Stream ciphers, where plaintext bits are combined with a cipher bit stream by an exclusive-or operation (xor), can be very secure if used properly. However, they are vulnerable to attacks if certain precautions are not followed: *keys must never be used twice *valid decryption should never be relied on to indicate authenticity Reused key attack Stream ciphers are vulnerable to attack if the same key is used twice (depth of two) or more. Say we send messages ''A'' and ''B'' of the same length, both encrypted using same key, ''K''. The stream cipher produces a string of bits ''C(K)'' the same length as the messages. The encrypted versions of the messages then are: :''E(A) = A xor C'' :''E(B) = B xor C'' where ''xor'' is performed bit by bit. Say an adversary has intercepted ''E(A)'' and ''E(B)''. They can easily compute: :''E(A) xor E(B)'' However, ''xor'' is commutative and has the property that ''X xor X = 0'' (self-inverse) so: :''E(A) xor E(B) = (A xor C) xor (B xor C ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] [Amazon] |