|
Matrix App
Matrix was an instant messaging (IM) and communications network that was shut down by cooperation between Dutch and French police in December 2024. It was also known by the names Mactrix, Totalsec, X-Quantum and Q-Safe. History Dutch police discovered the network while investigating the murder of Peter de Vries in 2021. A mobile phone was found in the getaway car. The phone was found to be connected to the Matrix network. A joint task force involving Dutch and French police was formed, with 2.3 million messages in 33 languages intercepted. Police forces in Italy, Lithuania, Spain and Germany were also involved. Europol and Eurojust coordinated the investigation. Infrastructure The service operated on around 40 servers throughout Europe and had about 8000 users. Users paid between $1350 and $1700 in cryptocurrency for a Google Pixel handset and six months subscription to the service. Seizures and arrests Simultaneous raids and searches took place on 3 December 2024 in four countri ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Instant Messaging
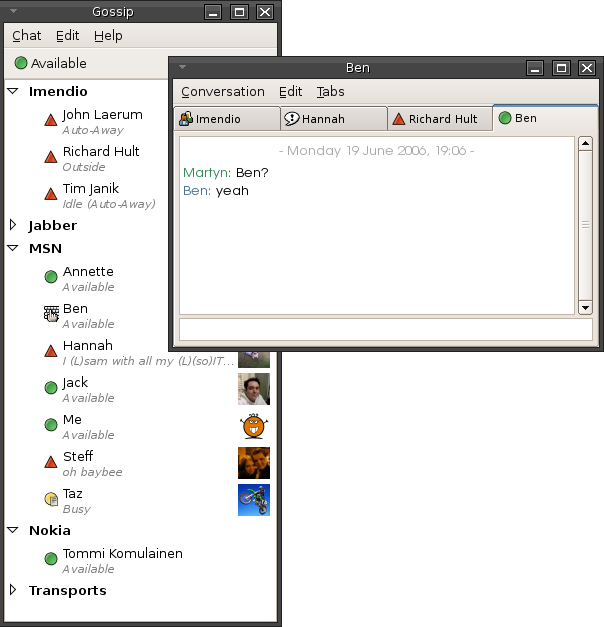
Instant messaging (IM) technology is a type of synchronous computer-mediated communication involving the immediate ( real-time) transmission of messages between two or more parties over the Internet or another computer network. Originally involving simple text message exchanges, modern IM applications and services (also called "social messengers", "messaging apps", "chat apps" or "chat clients") tend to also feature the exchange of multimedia, emojis, file transfer, VoIP (voice calling), and video chat capabilities. Instant messaging systems facilitate connections between specified known users (often using a contact list also known as a "buddy list" or "friend list") or in chat rooms, and can be standalone apps or integrated into a wider social media platform, or in a website where it can, for instance, be used for conversational commerce. Originally the term "instant messaging" was distinguished from " text messaging" by being run on a computer network instead of a cellula ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Ennetcom
Ennetcom was a Netherlands based communications network and service provider. Company The company was based in the Netherlands as were most of its customers, but most of the company servers were based in Canada. Danny Manupassa, the company owner, was arrested in 2016 amid allegations that the phones were largely used by criminals. The company had about 19,000 users. The phones sold for €1,500 each and used company servers for traffic. The devices had been altered so they could not make calls or use the Internet normally. Canadian authorities seized the servers and passed messages to Dutch authorities. The latter had managed to decrypt 3.6 million messages by 2017, apparently because the key to the messages had been stored on the same servers the messages were on. These messages have led to arrests, including that of Naoufal Fassih. Fassih has been convicted of one charge of murder and one of attempted murder in relation to the murder of Ali Motamed. See also * ANOM * E ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Network Architecture
Network architecture is the design of a computer network. It is a framework for the specification of a network's physical components and their functional organization and configuration, its operational principles and procedures, as well as communication protocols used. In telecommunications, the specification of a network architecture may also include a detailed description of products and services delivered via a communications network, as well as detailed rate and billing structures under which services are compensated. The network architecture of the Internet is predominantly expressed by its use of the Internet protocol suite, rather than a specific model for interconnecting networks or nodes in the network, or the usage of specific types of hardware links. OSI model The Open Systems Interconnection model (OSI model) defines and codifies the concept of layered network architecture. Abstraction layers are used to subdivide a communications system further into smaller man ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Internet Culture
Internet culture refers to culture developed and maintained among frequent and active users of the Internet (also known as netizens) who primarily communicate with one another as members of online communities; that is, a culture whose influence is "mediated by computer screens" and information communication technology, specifically the Internet. Internet culture arises from the frequent interactions between members within various online communities and the use of these communities for communication, entertainment, business, and recreation. Studied aspects of Internet culture include anonymity/pseudonymity, social media, gaming and specific communities, such as fandoms. History The Internet developed in parallel with rapid and sustained technological advances in computing and data communication. Widespread access to the Internet emerged as the cost of infrastructure dropped by several orders of magnitude with consecutive technological improvements. Though Internet cultur ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Internet Architecture
World Wide Web topology is distinct from Internet topology. While the former focuses on how web pages are interconnected through hyperlinks, the latter refers to the layout of network infrastructure like routers, ISPs, and backbone connections. The Jellyfish model of the World Wide Web topology represents the web as a core of highly connected nodes (web pages) surrounded by layers of less connected nodes. The Bow Tie model, on the other hand, divides the web into distinct zones: a strongly connected core, an 'IN' group leading into the core, an 'OUT' group leading out, and disconnected components. This model emphasizes the flow of hyperlinks between different parts of the web.. Models of web page topology Jellyfish Model The simplistic Jellyfish model of the World Wide Web centers around a large strongly connected core of high- degree web pages A web page (or webpage) is a World Wide Web, Web document that is accessed in a web browser. A website typically consists of many w ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
File Sharing
File sharing is the practice of distributing or providing access to digital media, such as computer programs, multimedia (audio, images and video), documents or electronic books. Common methods of storage, transmission and dispersion include removable media, centralized servers on computer networks, Internet-based hyperlinked documents, and the use of distributed peer-to-peer networking. File sharing technologies, such as BitTorrent, are integral to modern media piracy, as well as the sharing of scientific data and other free content. History Files were first exchanged on removable media. Computers were able to access remote files using filesystem mounting, bulletin board systems (1978), Usenet (1979), and FTP servers (1970's). Internet Relay Chat (1988) and Hotline (1997) enabled users to communicate remotely through chat and to exchange files. The mp3 encoding, which was standardized in 1991 and substantially reduced the size of audio files, grew to widespread use ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
End-to-end Encryption
End-to-end encryption (E2EE) is a method of implementing a secure communication system where only communicating users can participate. No one else, including the system provider, telecom providers, Internet providers or malicious actors, can access the cryptographic keys needed to read or send messages. End-to-end encryption prevents data from being read or secretly modified, except by the true sender and intended recipients. Frequently, the messages are relayed from the sender to the recipients by a service provider. However, messages are encrypted by the sender and no third party, including the service provider, has the means to decrypt them. The recipients retrieve the encrypted messages and decrypt them independently. Since third parties cannot decrypt the data being communicated or stored, services that provide end-to-end encryption are better at protecting user data when they are affected by data breaches. Such services are also unable to share user data with governm ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Distributed Computing Architecture
Distributed computing is a field of computer science that studies distributed systems, defined as computer systems whose inter-communicating components are located on different networked computers. The components of a distributed system communicate and coordinate their actions by passing messages to one another in order to achieve a common goal. Three significant challenges of distributed systems are: maintaining concurrency of components, overcoming the lack of a global clock, and managing the independent failure of components. When a component of one system fails, the entire system does not fail. Examples of distributed systems vary from SOA-based systems to microservices to massively multiplayer online games to peer-to-peer applications. Distributed systems cost significantly more than monolithic architectures, primarily due to increased needs for additional hardware, servers, gateways, firewalls, new subnets, proxies, and so on. Also, distributed systems are prone to ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Defunct Darknet Markets
{{Disambiguation ...
Defunct may refer to: * ''Defunct'' (video game), 2014 * Zombie process or defunct process, in Unix-like operating systems See also * * :Former entities * End-of-life product * Obsolescence Obsolescence is the process of becoming antiquated, out of date, old-fashioned, no longer in general use, or no longer useful, or the condition of being in such a state. When used in a biological sense, it means imperfect or rudimentary when comp ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Dark Web
The dark web is the World Wide Web content that exists on darknets ( overlay networks) that use the Internet but require specific software, configurations, or authorization to access. Through the dark web, private computer networks can communicate and conduct business anonymously without divulging identifying information, such as a user's location. The dark web forms a small part of the deep web, the part of the web not indexed by web search engines, although sometimes the term ''deep web'' is mistakenly used to refer specifically to the dark web. The darknets which constitute the dark web include small, friend-to-friend networks, as well as large, popular networks such as Tor, Hyphanet, I2P, and Riffle operated by public organizations and individuals. Users of the dark web refer to the regular web as clearnet due to its unencrypted nature. The Tor dark web or onionland uses the traffic anonymization technique of onion routing under the network's top-level domain suffi ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Cyberspace
Cyberspace is an interconnected digital environment. It is a type of virtual world popularized with the rise of the Internet. The term entered popular culture from science fiction and the arts but is now used by technology strategists, security professionals, governments, military and industry leaders and entrepreneurs to describe the domain of the global technology environment, commonly defined as standing for the global network of interdependent information technology infrastructures, telecommunications networks and computer processing systems. Others consider cyberspace to be just a notional environment in which communication over computer networks occurs. The word became popular in the 1990s when the use of the Internet, networking, and digital communication were all growing dramatically; the term ''cyberspace'' was able to represent the many new ideas and phenomena that were emerging. As a social experience, individuals can interact, exchange ideas, share information, provi ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Anonymity Networks
Anonymity describes situations where the acting person's identity is unknown. Anonymity may be created unintentionally through the loss of identifying information due to the passage of time or a destructive event, or intentionally if a person chooses to withhold their identity. There are various situations in which a person might choose to remain anonymous. Acts of charity have been performed anonymously when benefactors do not wish to be acknowledged. A person who feels threatened might attempt to mitigate that threat through anonymity. A witness to a crime might seek to avoid retribution, for example, by anonymously calling a crime tipline. In many other situations (like conversation between strangers, or buying some product or service in a shop), anonymity is traditionally accepted as natural. Some writers have argued that the term "namelessness", though technically correct, does not capture what is more centrally at stake in contexts of anonymity. The important idea here is t ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |