|
Telnet
Telnet (sometimes stylized TELNET) is a client-server application protocol that provides access to virtual terminals of remote systems on local area networks or the Internet. It is a protocol for bidirectional 8-bit communications. Its main goal was to connect terminal devices and terminal-oriented processes. The name "Telnet" refers to two things: a protocol itself specifying how two parties are to communicate and a software application that implements the protocol as a service. User data is interspersed in-band with Telnet control information in an 8-bit byte oriented data connection over the Transmission Control Protocol (TCP). Telnet transmits all information including usernames and passwords in plaintext so it is not recommended for security-sensitive applications such as remote management of routers. Telnet's use for this purpose has waned significantly in favor of SSH. Some extensions to Telnet which would provide encryption have been proposed. Description The ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Secure Shell
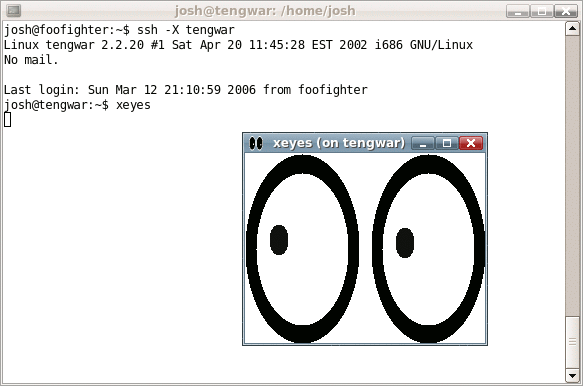
The Secure Shell Protocol (SSH Protocol) is a cryptographic network protocol for operating network services securely over an unsecured network. Its most notable applications are remote login and command-line execution. SSH was designed for Unix-like operating systems as a replacement for Telnet and unsecured remote Unix shell protocols, such as the Berkeley Remote Shell (rsh) and the related rlogin and rexec protocols, which all use insecure, plaintext methods of authentication, like passwords. Since mechanisms like Telnet and Remote Shell are designed to access and operate remote computers, sending the authentication tokens (e.g. username and password) for this access to these computers across a public network in an unsecured way poses a great risk of 3rd parties obtaining the password and achieving the same level of access to the remote system as the telnet user. Secure Shell mitigates this risk through the use of encryption mechanisms that are intended to hide th ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Port (computer Networking)
In computer networking, a port is a communication endpoint. At the software level within an operating system, a port is a logical construct that identifies a specific process or a type of network service. A port is uniquely identified by a number, the port number, associated with the combination of a transport protocol and the network IP address. Port numbers are 16-bit unsigned integers. The most common transport protocols that use port numbers are the Transmission Control Protocol (TCP) and the User Datagram Protocol (UDP). The port completes the destination and origination addresses of a message within a host to point to an operating system process. Specific port numbers are reserved to identify specific services so that an arriving packet can be easily forwarded to a running application. For this purpose, port numbers lower than 1024 identify the historically most commonly used services and are called the well-known port numbers. Higher-numbered ports are available for g ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Computer Terminal
A computer terminal is an electronic or electromechanical hardware device that can be used for entering data into, and transcribing data from, a computer or a computing system. Most early computers only had a front panel to input or display bits and had to be connected to a terminal to print or input text through a keyboard. Teleprinters were used as early-day hard-copy terminals and predated the use of a computer screen by decades. The computer would typically transmit a line of data which would be printed on paper, and accept a line of data from a keyboard over a serial or other interface. Starting in the mid-1970s with microcomputers such as the Sphere 1, Sol-20, and Apple I, display circuitry and keyboards began to be integrated into personal and workstation computer systems, with the computer handling character generation and outputting to a CRT display such as a computer monitor or, sometimes, a consumer TV, but most larger computers continued to require terminal ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
ARPANET
The Advanced Research Projects Agency Network (ARPANET) was the first wide-area packet-switched network with distributed control and one of the first computer networks to implement the TCP/IP protocol suite. Both technologies became the technical foundation of the Internet. The ARPANET was established by the Advanced Research Projects Agency (now DARPA) of the United States Department of Defense. Building on the ideas of J. C. R. Licklider, Robert Taylor (computer scientist), Bob Taylor initiated the ARPANET project in 1966 to enable resource sharing between remote computers. Taylor appointed Lawrence Roberts (scientist), Larry Roberts as program manager. Roberts made the key decisions about the request for proposal to build the network. He incorporated Donald Davies' concepts and designs for packet switching, and sought input from Paul Baran on dynamic routing. In 1969, ARPA awarded the contract to build the Interface Message Processors (IMPs) for the network to Bolt Berane ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Remote System
Remote administration refers to any method of controlling a computer or other Internet-connected device, such as a smartphone, from a remote location. There are many commercially available and free-to-use software that make remote administration easy to set up and use. Remote administration is often used when it's difficult or impractical to be physically near a system in order to use it or troubleshoot it. Many server administrators also use remote administration to control the servers around the world at remote locations. It is also used by companies and corporations to improve overall productivity as well as promote remote work. It may also refer to both legal and illegal (i.e. hacking) remote administration (see Owned and Trojan). Requirements Internet connection Any computer with an Internet connection or on a local area network can be remotely administered. For non-malicious administration, the user must install or enable server software on the host system in order ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Local Area Network
A local area network (LAN) is a computer network that interconnects computers within a limited area such as a residence, campus, or building, and has its network equipment and interconnects locally managed. LANs facilitate the distribution of data and sharing network devices, such as printers. The LAN contrasts the wide area network (WAN), which not only covers a larger geographic distance, but also generally involves Leased line, leased telecommunication circuits or Internet links. An even greater contrast is the Internet, which is a system of globally connected business and personal computers. Ethernet and Wi-Fi are the two most common technologies used for local area networks; historical network technologies include ARCNET, Token Ring, and LocalTalk. Cabling Most wired network infrastructures utilize Category 5 cable, Category 5 or Category 6 cable, Category 6 twisted pair cabling with RJ45 (telecommunications), RJ45 compatible terminations. This medium provides physical ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Stephen Crocker
Stephen D. Crocker (born October 15, 1944) is an American Internet pioneer. In 1969, he created the ARPA "Network Working Group" and the Request for Comments series. He served as chair of the board of the Internet Corporation for Assigned Names and Numbers (ICANN) from 2011 through 2017. Education Steve Crocker attended Van Nuys High School, as did Vint Cerf and Jon Postel. Crocker received his bachelor's degree (1968) and PhD (1977) from the University of California, Los Angeles. Career As a graduate student at the University of California Los Angeles (UCLA) in the 1960s, he was part of the team that developed the protocols for the ARPANET which were the foundation for today's Internet. He said "While much of the development proceeded according to a grand plan, the design of the protocols and the creation of the RFCs was largely accidental." He was instrumental in forming a Network Working Group (NWG) in 1969 and was the instigator of the Request for Comment (RFC) s ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Application Layer
An application layer is an abstraction layer that specifies the shared communication protocols and interface methods used by hosts in a communications network. An ''application layer'' abstraction is specified in both the Internet Protocol Suite (TCP/IP) and the OSI model. Although both models use the same term for their respective highest-level layer, the detailed definitions and purposes are different. Internet protocol suite In the Internet protocol suite, the application layer contains the communications protocols and interface methods used in process-to-process communications across an Internet Protocol (IP) computer network. The application layer only standardizes communication and depends upon the underlying transport layer protocols to establish host-to-host data transfer channels and manage the data exchange in a client–server or peer-to-peer networking model. Though the TCP/IP application layer does not describe specific rules or data formats that applications m ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Internet Standard
In computer network engineering, an Internet Standard is a normative specification of a technology or methodology applicable to the Internet. Internet Standards are created and published by the Internet Engineering Task Force (IETF). They allow interoperation of hardware and software from different sources which allows internets to function. As the Internet became global, Internet Standards became the lingua franca of worldwide communications. Engineering contributions to the IETF start as an Internet Draft, may be promoted to a Request for Comments, and may eventually become an Internet Standard. An Internet Standard is characterized by technical maturity and usefulness. The IETF also defines a Proposed Standard as a less mature but stable and well-reviewed specification. A Draft Standard was an intermediate level, discontinued in 2011. A Draft Standard was an intermediary step that occurred after a Proposed Standard but prior to an Internet Standard. As put in RFC 2026: In ge ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Packet Sniffing
A packet analyzer (also packet sniffer or network analyzer) is a computer program or computer hardware such as a packet capture appliance that can analyze and log traffic that passes over a computer network or part of a network. Packet capture is the process of intercepting and logging traffic. As data streams flow across the network, the analyzer captures each packet and, if needed, decodes the packet's raw data, showing the values of various fields in the packet, and analyzes its content according to the appropriate RFC or other specifications. A packet analyzer used for intercepting traffic on wireless networks is known as a wireless analyzer - those designed specifically for Wi-Fi networks are Wi-Fi analyzers. While a packet analyzer can also be referred to as a network analyzer or protocol analyzer these terms can also have other meanings. Protocol analyzer can technically be a broader, more general class that includes packet analyzers/sniffers. However, the terms ar ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Cyberattack
A cyberattack (or cyber attack) occurs when there is an unauthorized action against computer infrastructure that compromises the confidentiality, integrity, or availability of its content. The rising dependence on increasingly complex and interconnected computer systems in most domains of life is the main factor that causes vulnerability to cyberattacks, since virtually all computer systems have bugs that can be exploited by attackers. Although it is impossible or impractical to create a perfectly secure system, there are many defense mechanisms that can make a system more difficult to attack, making information security a field of rapidly increasing importance in the world today. Perpetrators of a cyberattack can be criminals, hacktivists, or states. They attempt to find weaknesses in a system, exploit them and create malware to carry out their goals, and deliver it to the targeted system. Once installed, the malware can have a variety of effects depending on its purpose. ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Client–server Model
The client–server model is a distributed application structure that partitions tasks or workloads between the providers of a resource or service, called servers, and service requesters, called clients. Often clients and servers communicate over a computer network on separate hardware, but both client and server may be on the same device. A server host runs one or more server programs, which share their resources with clients. A client usually does not share its computing resources, but it requests content or service from a server and may share its own content as part of the request. Clients, therefore, initiate communication sessions with servers, which await incoming requests. Examples of computer applications that use the client–server model are email, network printing, and the World Wide Web. Client and server role The server component provides a function or service to one or many clients, which initiate requests for such services. Servers are classified by the servic ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |